Reviewed by Jonathan Krause.
Introduction
You’re probably aware by now that peer-to-peer (P2P) networks are a pretty successful and popular method of distributing data over the internet. It’s easy to see why; the client software that the end user installs can be very small, simple to use, and more often than not works like a charm. It’ll usually download a file from multiple locations ensuring high download speeds, will immediately make the file available for upload to others, will deal with missing chunks of data and dropped connections and when it’s finished downloading every piece of the file it’ll make a contiguous usable file from all the data chunks, all without any centralised management system. Brilliant. Which makes me wonder why P2P appears to be used almost exclusively to distribute contraband material and hardly ever as way to distribute legitimate files.Due to the way they work, P2P clients by necessity create a lot of information about what they’ve been requested to download, where the download originated from and when. It’s a goldmine for forensic investigators and bad news for the subject of the investigation as in most legislatures distribution of contraband material is punished more severely than mere possession.
Findings
With the above in mind Alexander Kuiper through his company Kuiper Forensics developed an application that would quickly scan for P2P-applications, web disks and UseNet-clients and once the presence of such applications is detected can then evaluate the databases of the following:
· eMule (known.met)
· Kazaa (data256.dbb, data1024.dbb)
· Google Hello (*.chatlog, *.filmstrip)
· BitTorrent (*.torrent)
· LimeWire (library.dat, library5.dat, fileurns.cache)
Being a little old-fashioned in some respects I enjoyed receiving this product in a physical format through the post. Probably done through necessity as the software requires the presence of a USB dongle, it was still nice to get a disc with the software on it in a DVD case. The case design is quite plain and could be charitably described as minimalist while the Kuiper Forensics company logo is that old computer forensic favourite of a magnifying glass over a fingerprint/binary code.
Although I’m no fan of USB dongles – USB ports are limited, and it can be awkward to keep taking dongles out and putting them back in again – the dongle supplied with PeerLab is of the Human Interface Device (HID) variety, and so needs no installation routine or specialist drivers. Nice and easy.
The USB dongle in place, I inserted the CD and nothing; no auto-start routine which I think may suit some people. Clicking on the executable on the CD I began the install process. The install process is very basic and quick – choose install location, start install, close install. PeerLab is a 32-bit program and its installed size is an impressively tiny 718KB. No option is provided to install a desktop shortcut, or to open the program or open the read-me or manual which I think the application could benefit from and the developer should consider including in future releases. It didn’t appear in my Windows 7 Start List or in the ‘All Programs’ list so I needed to visit C:/Program Files (x86)/PeerLab/ to find the PeerLab executable and create a short cut to it on my desktop. I noted that there is no uninstaller; PeerLab does not appear as an item in the Windows 7 ‘Uninstall or change a program’ list and there is no specific uninstaller either. I imagine writing an uninstall routine is the least glamorous part of making software and the developer wouldn’t really want people to be removing their program, but still, it’s a necessary item that all applications should incorporate.
Next the PeerLab license agreement. Not something worth covering in a review you say? Think again. Apart from being unnecessarily written in all capitals, this particular license agreement was actually short enough to read in a minute or so, which makes a pleasant change – after all how many of us can hand-on-heart say we read the whole licensing agreement of EnCase or FTK before we dive in? Having said this, forensic investigators really should be familiar with the licensing agreements of the tools they use. I especially liked the last line of this license agreement ‘Never forget – PeerLab is a tool to assist you in your daily work. You are the professional!’ A great reminder.
The next screen is the configuration screen which is quite self-explanatory:

Figure 1: the PeerLab configuration screen
All straightforward so far. At this point, I should mention the PDF manual which is supplied on the CD is detailed, helpful and very clearly written, and serves as an excellent complement to the program. As you see from the screen-shots the application is laid out very well and it doesn’t take long at all for the user to become very familiar with it without needing to access the manual. Next, let’s create a case:
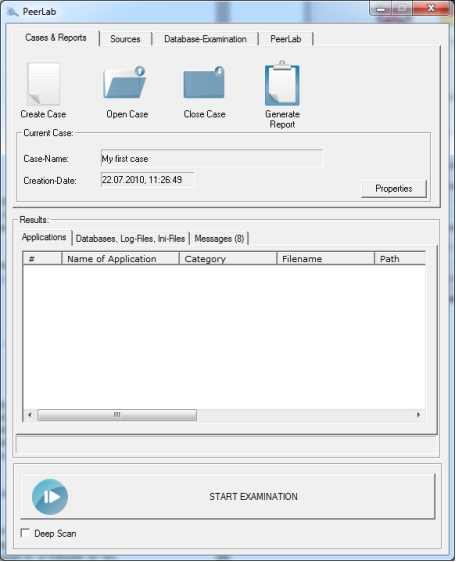
Figure 2: creating and opening a new case
And then fill in the case details:
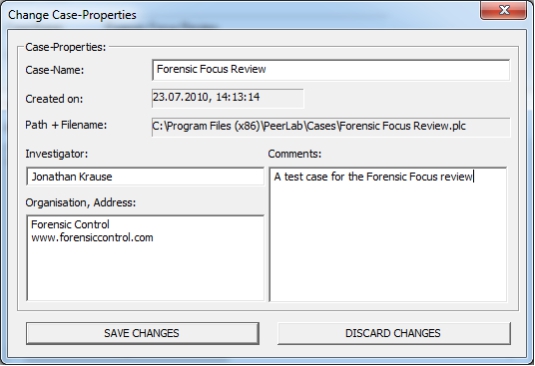
Figure 3: changing the case properties
And then select the source which we want to be examined:
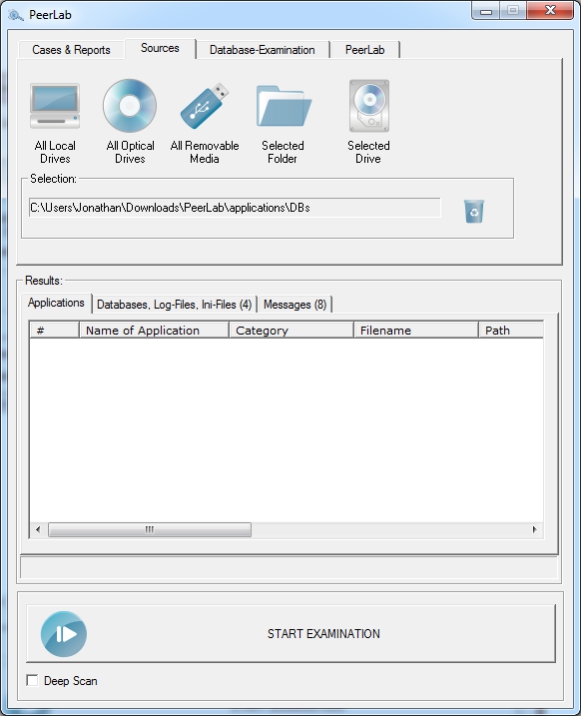
Figure 4: selecting source of data to be examined
At present PeerLab does not scan physical disks and can’t extract from unallocated space. This is something that Alexander tells me is due to be implemented which will be a great addition. I’d like to put in a feature request to Alexander here – if possible, I’d really like to be able to point PeerLab at E01 or dd files and for it to able to scan an entire image without the examiner needing to mount the image. This would be a real time and money saver.
Once the data source is selected PeerLab works like a virus scanner, detecting the presence of known versions of P2P applications, web disks and UseNet-clients (though hash values) and also ‘unknown’ versions of applications through searching for file names, doing this both with and without wildcard character substitutions. Currently PeerLab can detect 3229 versions of 267 different applications of interest. As such, PeerLab may also be used to show that the person under investigation did not have such applications installed.
As listed near the start of this review, PeerLab will automatically evaluate a number of databases from certain applications. On selecting the ‘Database-Examination’ tab from PeerLab’s main screen and clicking the ‘Investigation Wizard’ button you can examine the following found databases:
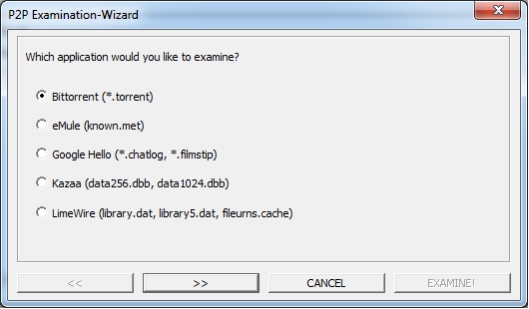
Figure 5: selection of database to be evaluated
In my example I examined LimeWire artefacts as supplied to me by Alexander Kuiper. The Wizard (confusingly called ‘Investigation Wizard’ in one place and ‘Examination Wizard’ in another) produced the following output:
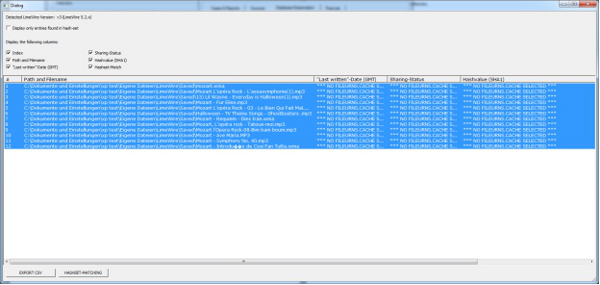
Figure 6: output after evaluating LimeWire artefacts (click to enlarge)
This output can then be exported in CSV format or you can run a hash-set check against the output helping identify notable files. Finally, PeerLab will create a customisable HTML report with the results of the applications it has found:
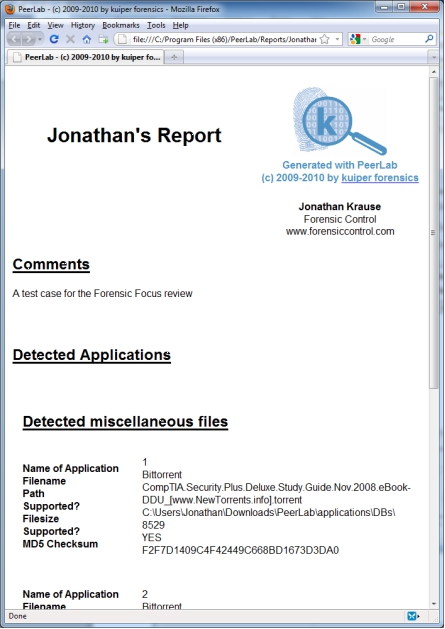
Figure 7: the HTML report produced by PeerLab (click to enlarge)
Conclusion
PeerLab is a great tool and a great addition to the forensic examiner’s tool kit. As I hope I’ve illustrated, it’s quick and very simple to operate, and does exactly what it says it will do. The manual is clear and comprehensive and the support I received from Alexander Kuiper was rapid, helpful and friendly. There are a couple of improvements in the pipeline that will further increase the usefulness of this tool, which I look forward to using in the future.
PeerLab can be used as a portable application which can be run from a USB disk. PeerLab runs on Windows XP and after and requires at least one free USB port.
PeerLab is available until the 31st of July 2010 at an introductory price of €79 from http://www.kuiper.de which provides a 1 user-license with updates for 1 year and includes: tax, postage, dongle, PeerLab-CD. PeerLab will not expire after the update-period ends. Volume licensing is available.
This review can be discussed here.
Jonathan Krause is an independent computer forensic investigator. You can follow him at http://twitter.com/jonathankrause







