Rapid growth of the usage of OS X has inspired forensic researchers to analyze devices such as the iPad, iPhone and Mac deeply. Therefore, OS X forensics, starting from Jonathan Zdziarski in 2008, became a very hot topic. However, most of the research and trainings are focused on file system analysis. Although there are some methods: eg Volatility, Volafox, Memoryze for Mac, Mac Memory Reader, MacLockPick and Rekall, able to analyze mac memory, mac memory analysis is relatively strange. This paper is to demonstrate a fast track of mac memory forensics via studying the evidence of a very popular social networking application ‘WeChat’.
INTRODUCTION
‘Memory Forensics is the art of analyzing computer memory (RAM) to solve digital crimes’defined by Michael Hale Ligh, Andrew Case and, Jamie Levy. Computer forensics science is not only a science but an art.
With the wide use of smart phones and the internet, most people communicate with their friends using mobile social networking applications ‘Facebook and Whatsapp’. Meanwhile, WeChat is the most famous chatting platform in China and the areas nearby, especially Hong Kong.
These applications provide not only the smart phone version but also the desktop version. Therefore, we could not ignore any possibility of evidence (either file system or memory) from a desktop machine.
As memory analysis would be an important intersection, this paper will perform this ‘Art’of science to examine the memory dump from a Mac machine, by acquisition, process analysis and data collection through an example of running WeChat on OS X.
ENVIRONMENT
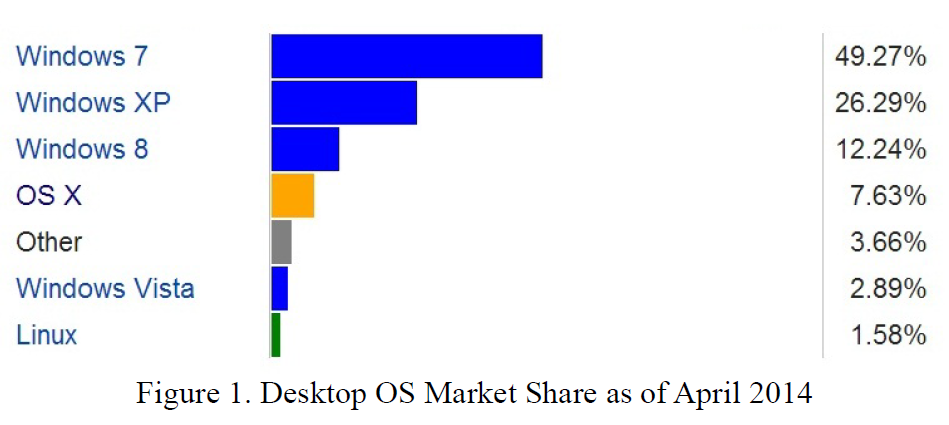
According to the research of Desktop Operation System from Net Application as of April 2014, the market share of Mac OS X is around 8% which is followed by the latest operation system Windows 8. With the effect from the ‘end-of-life’ of Windows XP, Mac OS X might occupy more market share afterwards. Now, it is a good time to study much more of the OS X attributes.
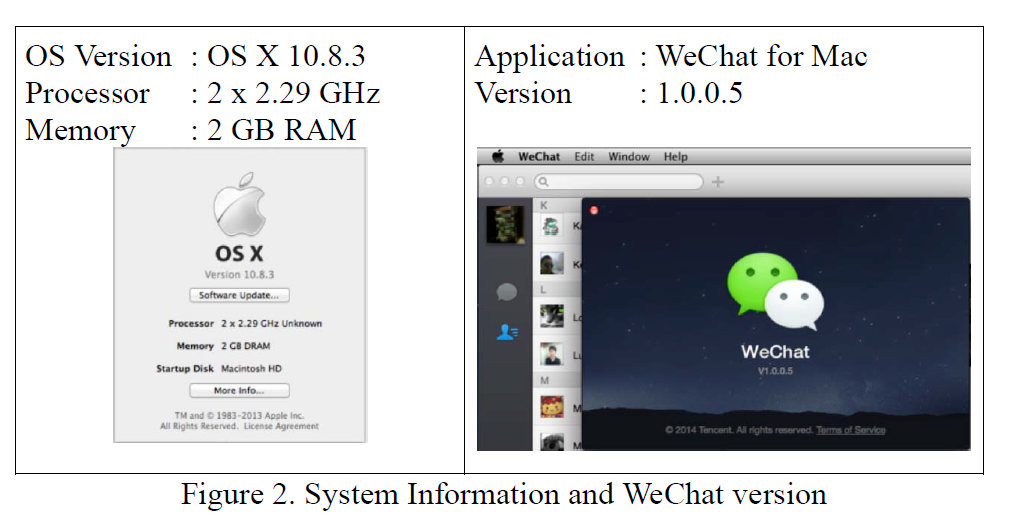
In this paper, a Mac machine with MountainLion OS X 10.8.3 installed was selected as a testing platform. The application ‘WeChat’ was downloaded from the official website of ‘Weixin’.
ACQUISITION
Two acquisition methods are suggested and preformed in this research. One is MacLockPick 3.0 from MacForensicsLab and the other is OSXPmem from Rekall Memory Forensics Framework.
MacLockPick 3.0
MacLockPick is a cross-platform forensics triage which could capture the live data such as system information and process in the field. It also supports gathering information from iPhone and iPad using Apple Mobile Sync application. LE version includes Apple Keychain Extractor.
Usage
The MacLockPick 3.0 is come with a USB Flash Drive with many of built-in Plugins. It could be configured in the MacLockPick Manager depended on the examiner’s preference.
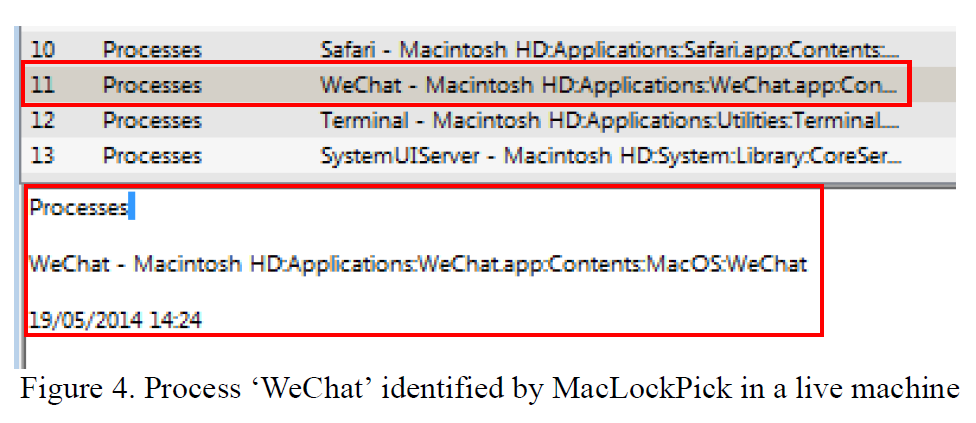
A process of ‘WeChat’ was identified by the MacLockPick. It executed
under the path /Application/WeChat.app/Contents/MacOS/WeChat on 2014-05-19.
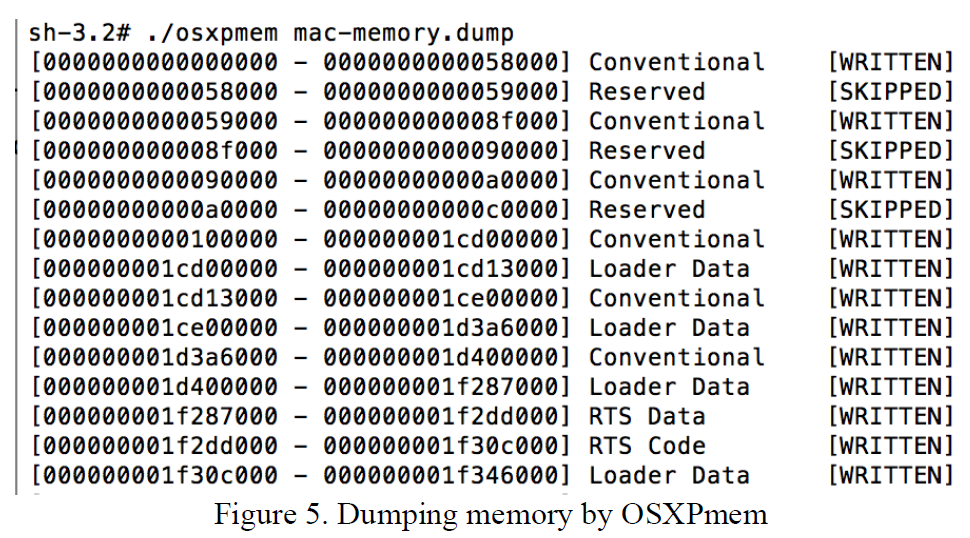
OSXPmem
Memory is volatile. All the data were gone if the machine is powered off. Although there is an alternative to recover the lost memory, for example ‘hibfil.sys’ in Windows OS, the best way is to acquire the memory dump as soon as possible.
The latest version of OSXPmem is RC3, developed by Rekall Memory Forensics Framework. It is an open source memory acquisition tool for Mac OS X which supports up to OS version 10.9. The default format is ELF
Usage
Super user privilege is required while dumping the memory.
$sudo su ./osxpmem mac-memory.dump
ANALYSIS
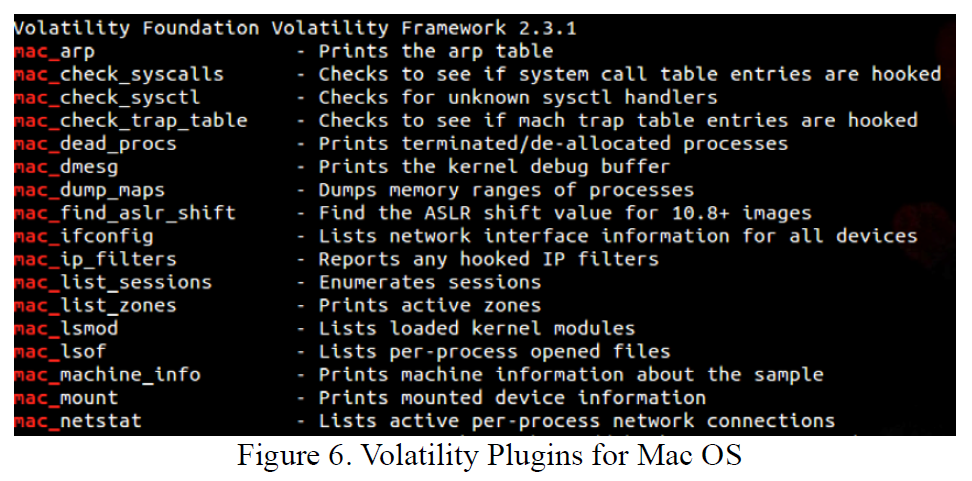
Volatility Forensics Framework
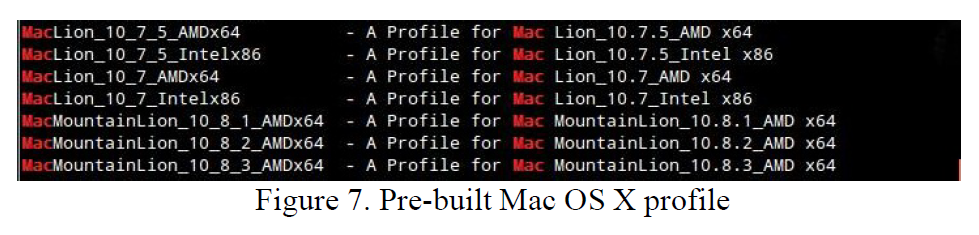
Once the process is identified, analysis progress is required. Volatility 2.3.1 is fully supporting the analysis on mac memory. It requires corresponding OS profiles while performing the process. The archive of the pre-built profiles up to version Mountain Lion 10.8.3 could be downloaded from its official website.
Usage
$ vol.py –f <mac-memory.dump> –profile=<MountainLion_Profile> <mac_pslist>
Volatility is a powerful memory forensics tool and delivers both Linux and Windows versions. It supports Windows, Linux and Mac memory. However, it builds in only 20 Windows operation system profiles. The user should know and select the correct profile when processing. Of course, a custom-profile for Linux or Mac OS might be created, if necessary.
Rekall Memory Forensics Framework
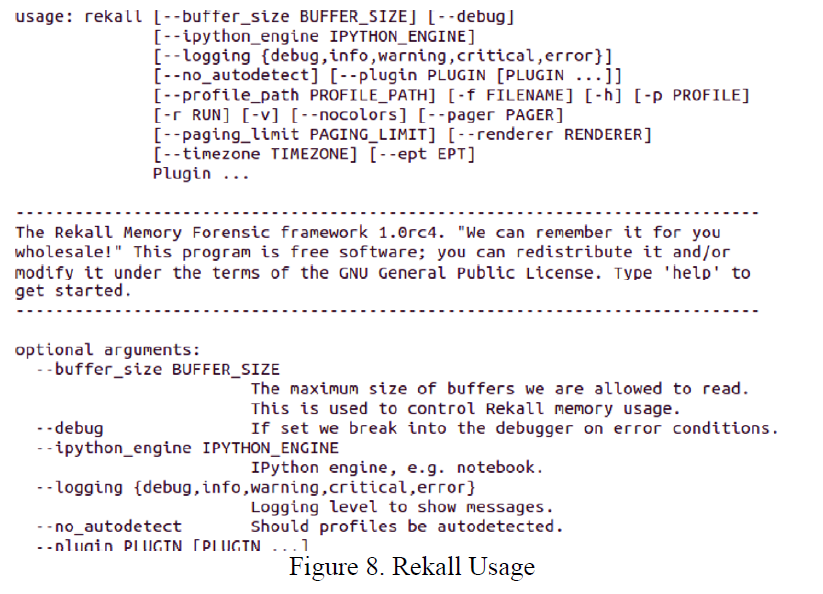
Another analysis tool is Rekall Memory Forensics Analysis Framework. The project is officially launched at the end of year 2013. The distribution is available from Internet. Likes Volatility, it processes with corresponding OS profile, but it could detect automatically. For OS X, it supports up to version 10.9.x. The profile repository contains over 300 different OS profiles. You could also create your favor profile for your own use.
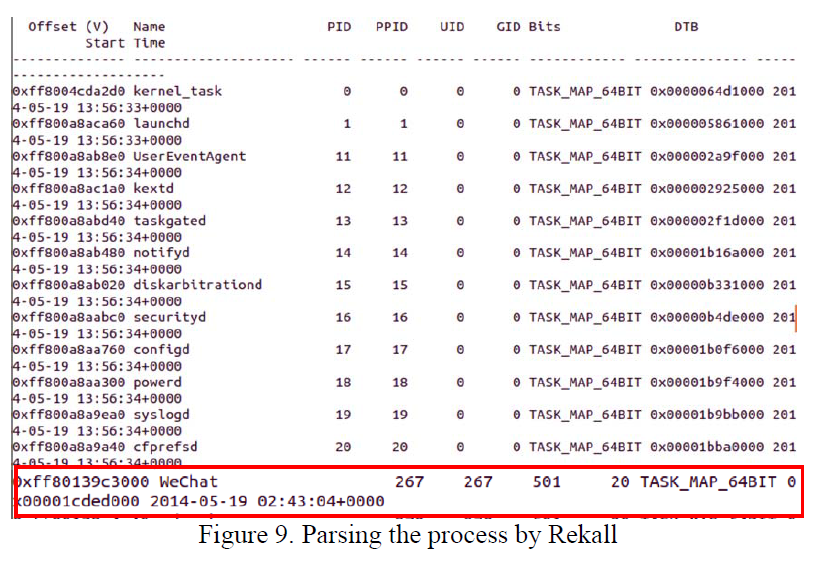
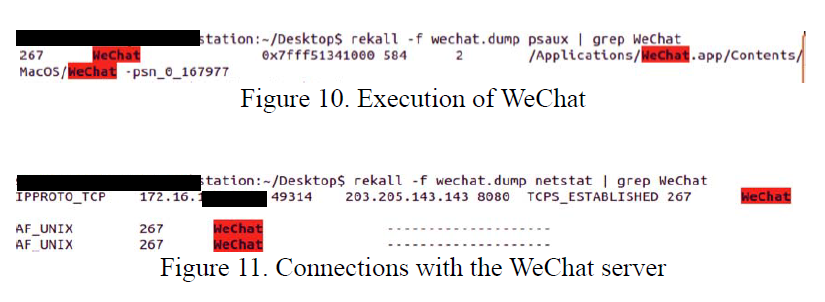
WeChat application has been identified by the MacLockPick at a live system as shown in Figure 4. It was executed from the path /Applcication/WeChat.app/Contents/MacOS/WeChat on 2014-05-19 as shown in Figure 4 & 9.
Rekall then parses the relevant information from the memory directly.
pslist shown that the PID of WeChat is 267 which connected to the IP Address 203.205.143.143:8080 as shown in Figure 9, 10 & 11.
Usage
$ rekall — help
$ rekall –f <mac-memory.dump> <pslist>
WeChat Analysis
User Account
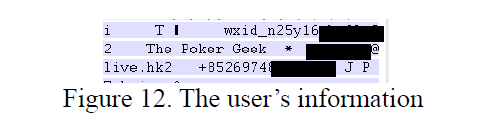
WeChat account has its Weixin ID, starting from “wxid_”(n25y16…..). The user nickname (The Poker Geek), registered email address (@live.hk) and phone number (+8526974) are now recovered from the memory.
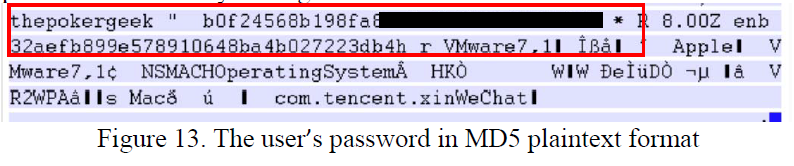
The interesting point is that the password of the user is a hashed MD5 plaintext followed by the login name.
Contact List
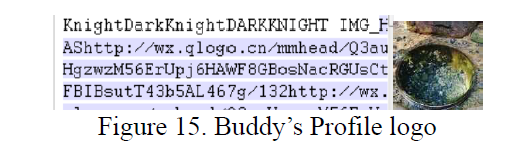
The contact list contains the Weixin ID (wxid), Nickname, the source of the buddy logo.
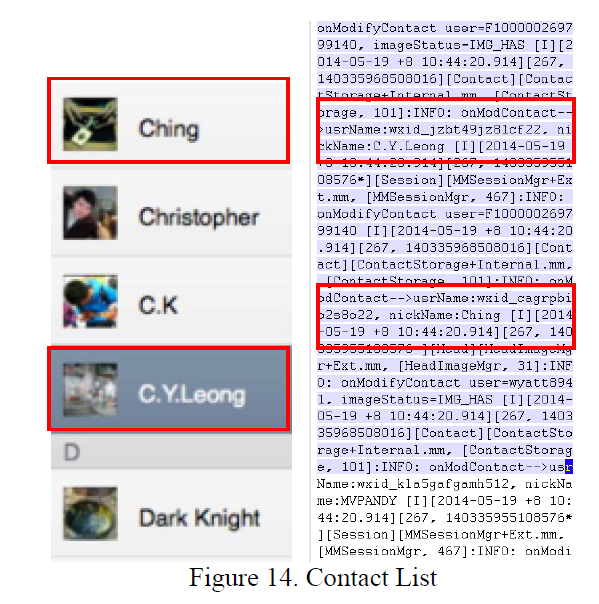
The logo of the user “Dark Knight”is located at the server.
Message
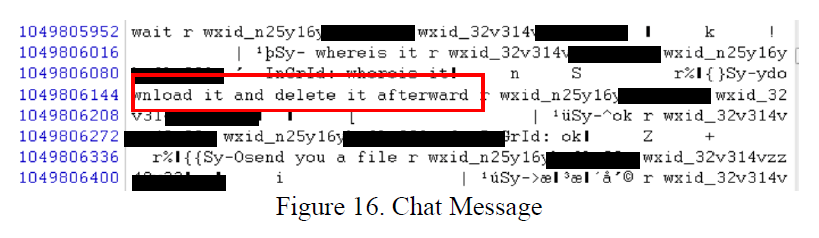
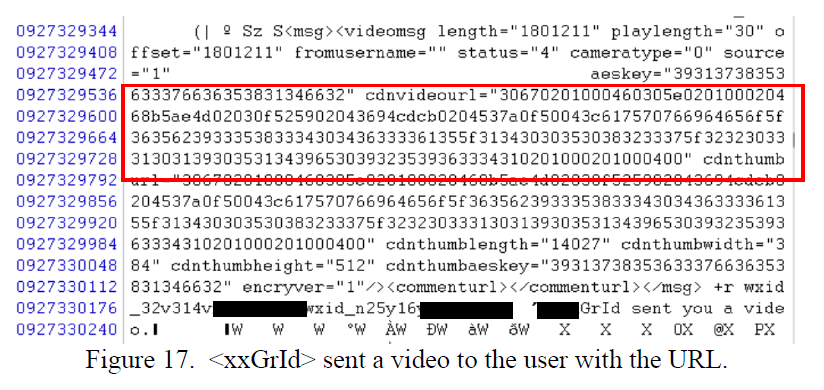
Upon searching, the conversation between the buddy (wxid_32v314…) and the user (wxid_n25y26y…) are recovered.
File Transfer
When a buddy wants to send out a file, eg video clip to the user, the file will be uploaded to the server. The user’s device will be notified by a message ‘<nickname> sent you a video’, together with a ‘cdnvidoeurl’(later known as a FileID).
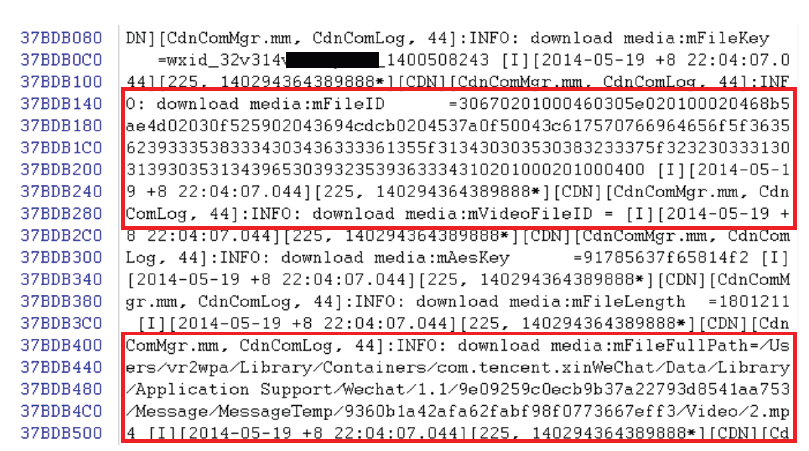
Figure 18. File (2.mp4) downloaded by the user
The user clicked on the icon and downloaded it from the server. The file will be eventually saved at the path /User/xxxxx/Library/Containers/com. tencent.xin/WeChat/Data/../../video/2.mp4, as a mpeg 4 format with a file name starting from a number, ie the second file is 2.mp4. Therefore, the file could be recovered from the physical Mac machine.
The file based on the “FileID”was downloaded by the user at 22:04:07 hrs +8 on 2014-05-19.
CONCLUSION
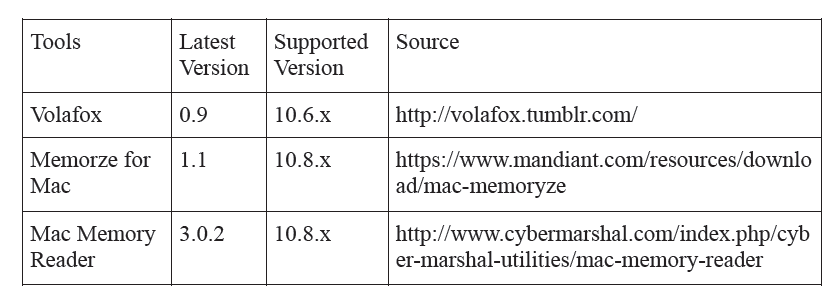
This demonstration showed you how to tackle the mac memory. Other than the above mentioned mac memory forensics tools, Volafox, Memorize for Mac and Mac Memory Reader are used for the mac memory acquisition and analysis.
Volatility and Rekall might not be the best memory forensics tools in the market but they provide the related effective and efficient solution to the forensics examiners or investigators. During the examination, we could understand much on the mac memory also reveal the security issue of the ‘WeChat’.
Kelvin, the author of this paper (also known as Forensics Ninja), has over 10 years experience in computer forensics and investigation for Law Enforcement. He has delivered speeches and workshops in DFRWS EU, DefCon, APWG and HTCIA (APAC).
References
[1] Michael Hale Ligh, Andrew Case, Jamie Levy, Aaron Walters, The Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and Mac Memory, 2014 [2] Johannes S. & Michael C., Robust Linux Memory Acquisition with Minimal Target Impact, 2014 [3] Feng Gao & Ying Zhang, Analysis of WeChat on IPhone, 2013 [4] Roberto Paleari , A look at WeChat security, 2013 [5] Andrew Case, Mac Memory Analysis with Volatility, 2012 [6] Kelvin WONG & VXRL, Facebook Forensics, 2011 [7] Yuhang Gao & Tianjie Cao, Memory Forensics for QQ from a Live System, 2010 [8] Joel Yonts, Mac OS X Malware Analysis, 2009 [9] Desktop Operating System Market Share, available at http://www.netmarketshare.com/ [10] Rekall Memory Forensics Framework, available at https://code.google.com/p/rekall/ [11] Volatility Memory Forensics Framework, available at https://code.google.com/p/volatility/ [12] MacLockPick 3.0, by MacForesicsLab, available at http://www.macforensicslab.com [13] OSXPmem, version RC3, available at https://code.google.com/p/rekall/source/browse/OSXPmem [14] Memorze for Mac, version 1.1, available at https://www.mandiant.com/resources/download/mac-memoryze [15] Volafox, version 0.9, available at http://volafox.tumblr.com [16] Mac Memory Reader, version 3.0.2, available at http://www.cybermarshal.com/index.php/cyber-marshal-utilities/mac-memory-reader














it is very impressive, be frank it is a good topic for further research.