This week, we’re combining Python and filtering for some forensic shenanigans on this week’s episode of FTK Feature Focus.
Welcome to FTK Feature Focus. I’m Justin Tolman, the director of training over North America here at Exterro. And this week we’re gonna take a look at using Python to create some filters for FTK.
The scenario is that we’ve been given a few hashes to find within our evidence, and we don’t wanna go through the work of creating a Known File Filter. Known File Filter is amazing for going through large datasets very quickly, looking for large amounts of hashes. But if we only have 4, 5, 10, then maybe it’s not worth the time investing in KFF.
We can use FTK’s powerful filter engine to do it, but we also don’t want to build the filter for that manually because that’s a lot of characters in an MD5 hash that we just frankly don’t want to type in.
So let’s write a Python script, not in this video, but let’s pretend that we would so that we can automatically create the filter based on a text list of hashes.
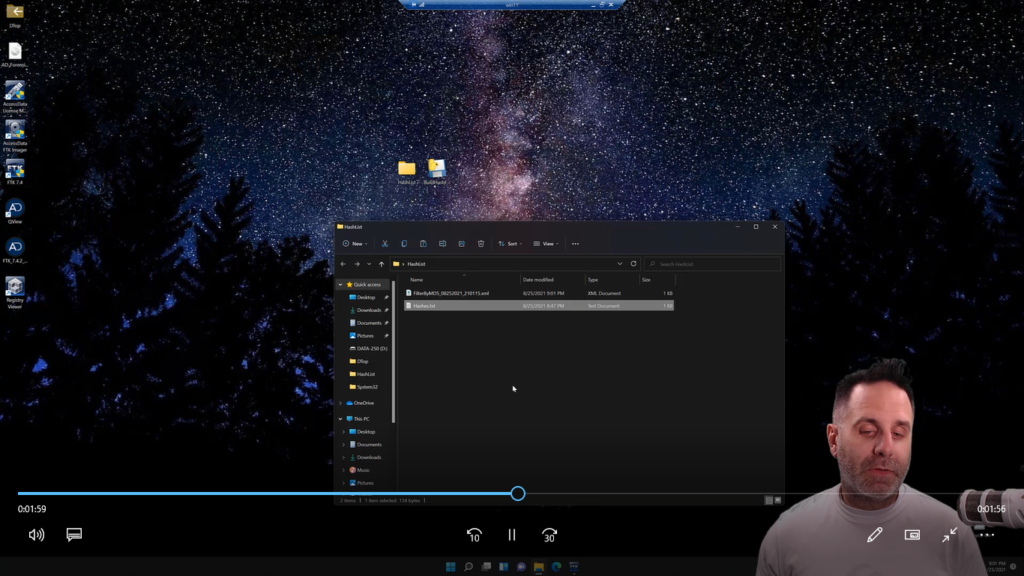
All right, let’s take a look at it. So we’re in FTK, but we’re gonna actually minimize FTK. And on our desktop, we have a directory called “hash list” and we have a Python script saved as an EXE, called BuildHashFilter.exe.
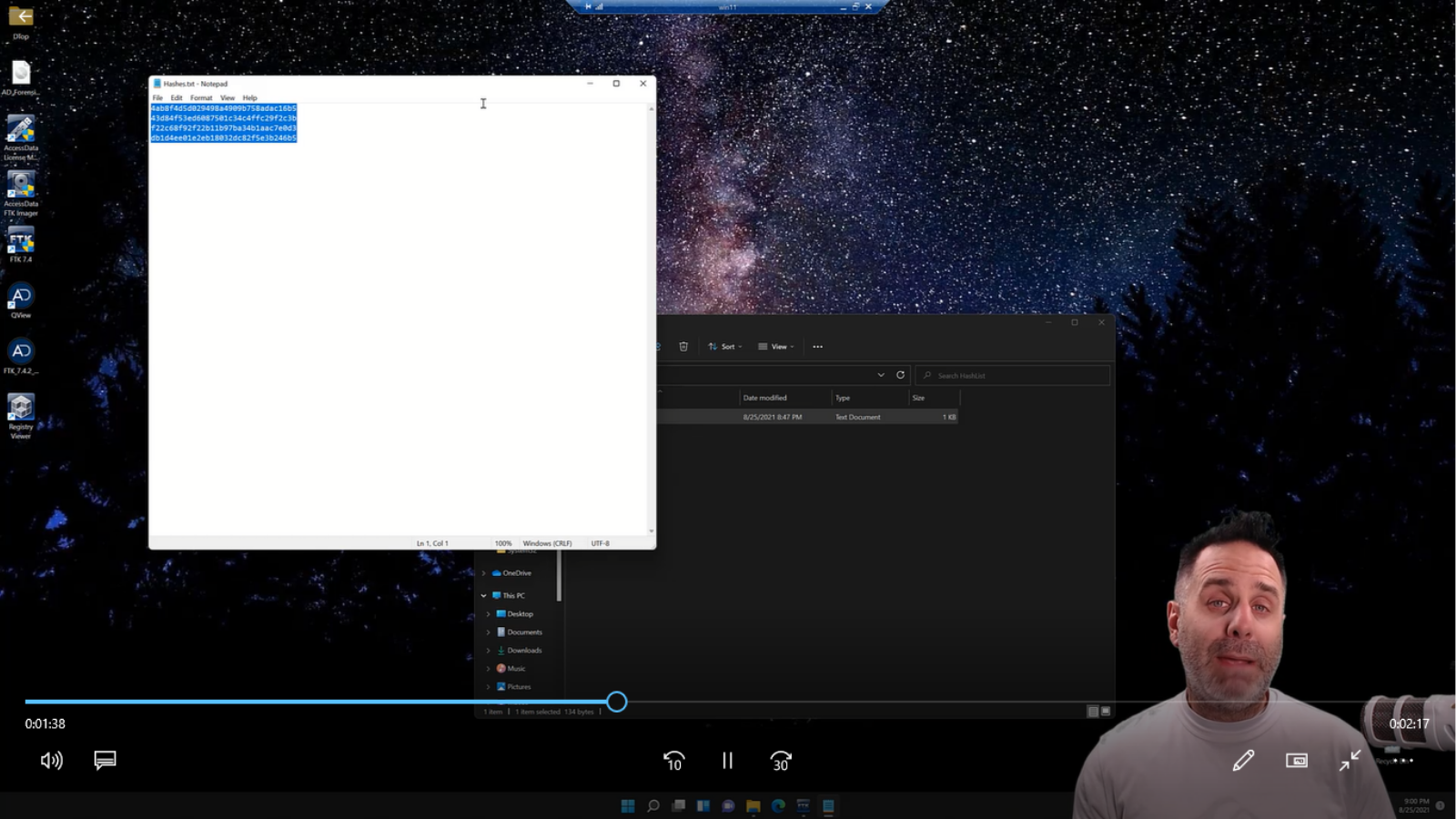
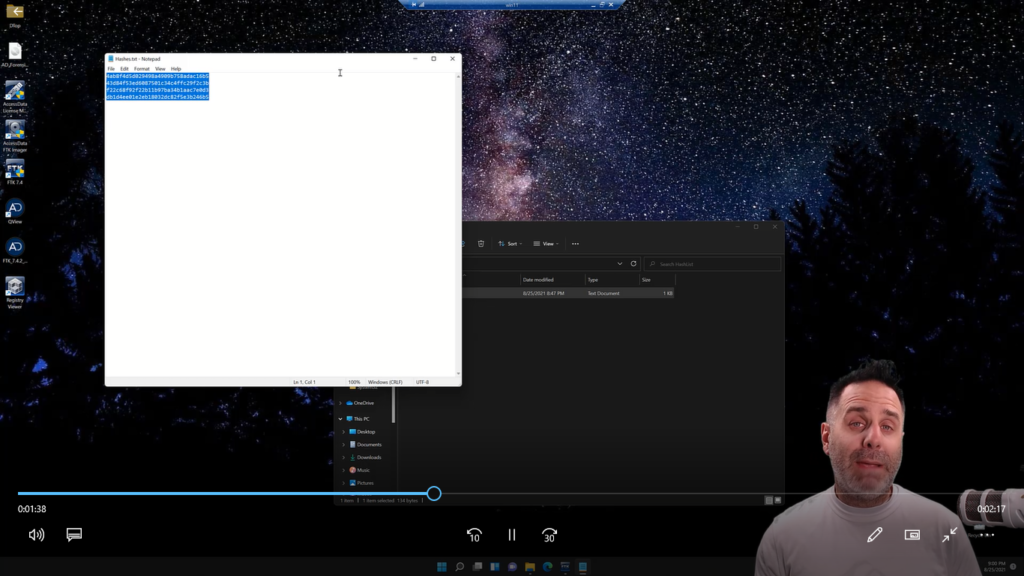
So we open up the hash list directory and we see hashes.txt. And we open that up and we see four hashes in here. Again, we could load this up into the Known File Filter and scan our evidence, but we only have four of them. Is it worth the time? Maybe if you’ve gotta run this over and over and over again, but this is also small enough that a filter will do just fine.
So we’re gonna go ahead and close that and come back over here. (We don’t wanna close the directory got ahead of myself.) So what we’re gonna do is we’ll simply grab our text file and we’ll drop it on our Python script and it will build us a filter easy as that.
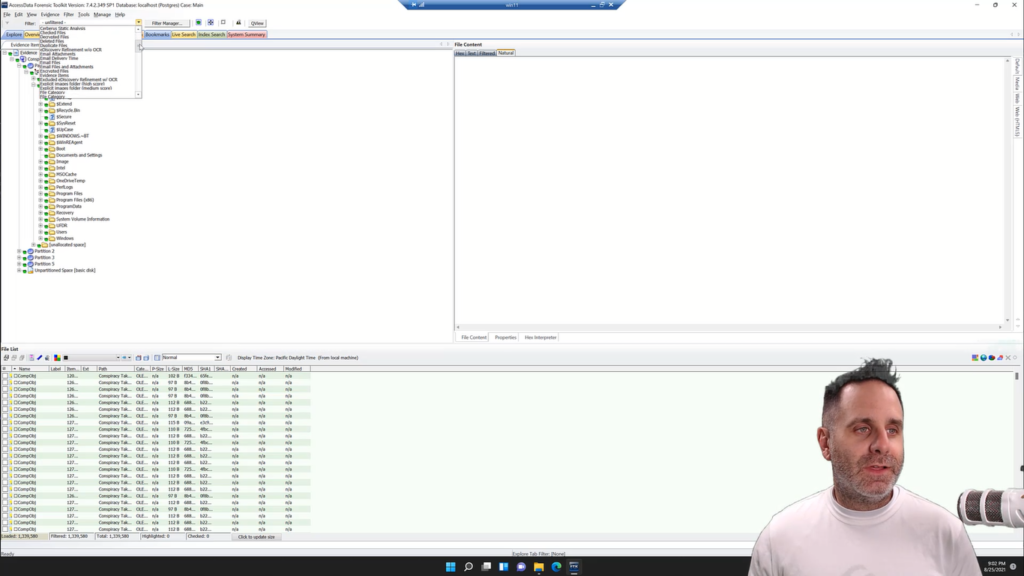
So we’ll go into FTK and gonna go up to filter and import. We’re gonna come out to hash list and we’re gonna grab “filter by MD5” with the date of when we created it. And that’s going to bring it in. Filter imported successfully.
We’ll jump over to the Explorer tab and we’re gonna quick pick all of our stuff, and just to make sure we have everything we’ll hit the little green button to load in all 1.3 million files. Doesn’t take long to load those remaining 300,000 files, but another one of those time saving things that FTK has added in the last little bit loading only a million items into your file list at a time.
So we have everything quick picked. We’ll come into the dropdown and to the chagrin of my instructors. I don’t name it with an underscore in front of it.
And so I have to go find it from the list, and we have it here: list of hash values, and we activate that. And here we go, we have our stuff based on the MD5 hashes that we had loaded up. So just that quick, we’re able to take a list of hashes, create a filter, drop it in.
The nice thing about the way FTK builds its filters into XML files is, it’s a consistent structure. So once you do open up any XML file, take a look at that, you can write a batch script, a Python script, or any frankly, any other language to automatically build a script for you that will go through and build a filter that you can load in just that quick.
So just a quick video on how you can leverage Python with FTK and its filtering engine to get you to your files quick. When you’re given a list of things to find, you could do this with any attribute. The easiest way to do it is to create a filter in FTK based on that attribute, then export it out, look at it in XML, and code your script to build it just like you see in your demo. So that’s this week’s episode of FTK Feature Focus. Thanks for watching. We’ll see you next week.