In the late nineties, IBM has adapted principle of heads parking outside platters, used in some older hard drives, on one of its new 2.5” models. Ramp – special plastic part located outside HDD platters was introduced.
Its purpose was reception of hard drive heads while device is turned off. This way, flat surfaces of head sliders and HDD platters don’t come in contact in any moment and stiction problem had become history.
Introduction of load/unload technology (ramp parking principle) was a huge step towards increase of capacity and lifetime of hard drives, as well as greater durability and data security as a result of enhanced shock tolerance. Also, great results were achieved in decreasing power consumption.

Ramp tool sets from HddSurgery
Advantages of load/unload technology over CSS parking principle resulted in fact that almost all modern hard drives are made with ramp. This technology change made a need for new solutions in data recovery. Known concept of head replacement were applicable only for hard drives with CSS parking principle. This was a new challenge for HddSurgery design engineers too.
HddSurgery R&D team started work on finding solution for safe & easy head swaps on hard drives with load/unload principle as soon as these have started to fail. Ramp set tools were presented to the market as a result of this work.
At first, set of head replacement tools for Western Digital hard drives was offered. It was a solution for both 2.5” and 3.5” hard drives and included 5 pairs (one tool for patient and the other one for donor HDD) of ramp tools, at the time.
Each tool pair is designed for different hard drive model, with certain number of heads and platters. Later, when new WD models appeared on the market, two new tool pairs were added to the set. Ramp sets for Seagate and Hitachi, both 2.5” and 3.5” hard drives, followed.
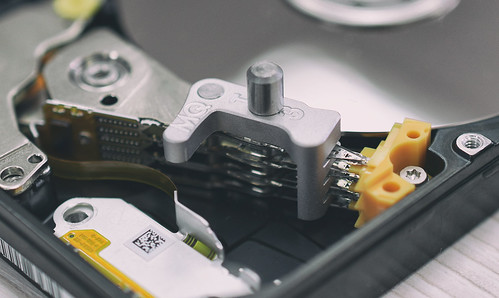
Use of HddSurgery ramp tools is simple. Tool is mounted by using one of the holes on the actuator arm. At least one technological hole is always available on all hard drive models, as manufacturers need it during the process of assembling. Rotation of the tool around axis of its central axle brings the tools snouts between read/write heads parked on a ramp.
After ramp tool is mounted on the head assembly, and its snouts are positioned between read/write heads, everything is ready for head replacement. Heads can be moved off the ramp as their mutual contact is prevented with the ramp tool snouts. After that entire head assembly can be dismounted from the donor hard drive.
Read/write heads position on the tools is secured by placing securing pin, either through the additional hole on the actuator arm or to the side of the heads if hole is not available. Securing pin is designed to prevent possible slipping of the heads from the ramp tool.
Tool from the upcoming Samsung & Toshiba 2.5'' Ramp Set
After mounting donor heads into patient hard drive, they can be safely moved to the patient ramp. Ramp tool snouts thickness is precisely engineered and produced so the heads remained separated by predefined dimension.
This enables moving the heads to the ramp without any unwanted contact which can lead to head damage. Sliding donor heads to the patient HDD ramp is last step in head replacement procedure and after that ramp tool can be dismounted from the heads.
Entire head swap process by using HddSurgery ramp tools is completely standardized and if it’s followed step by step there is no safer & easier way to perform it. There are no need for use of pieces of paper, cardboard, rubber, foil and similar soft and unreliable materials.
Standardized head swap procedure in combination with trustworthy and durable tools leads to increased efficiency and minimal chance for potential mistake. HddSurgery ramp tools are considered as real time and resource savers when it comes to solving mechanical defects of hard disk drives. Their additional advantage is possibility to train novices in the business more quickly.
Žarko Damjanović
Development engineer
Follow HddSurgery on Facebook, Twitter, Google +, You tube, Instagram and LinkedIn.






