Customers can quickly draw out relationships and hidden connections in digital forensic investigations and litigation
Nuix will make the Context user interface and other capabilities from Nuix Incident Response available with its Nuix Investigator and Nuix eDiscovery products. The new functionality will be included in the next minor release of the products, due early in October.“Many of our investigation and legal services customers have seen Nuix Incident Response and immediately thought of ways they could use its capabilities in their day-to-day work,” said Eddie Sheehy, CEO of Nuix. “We’re always looking for ways to deliver value to our customers and this was an obvious step.”
The Context interface is a fast and intuitive way to filter large numbers of items and allow the most interesting and relevant ones to float to the top. It applies built-in intelligence to group, show relationships between, and link the most relevant items for investigation or legal examination. This interface gives customers rapid access to the most relevant forensic artifacts including internet history, communication activity, file and operating system events, and USB device access.
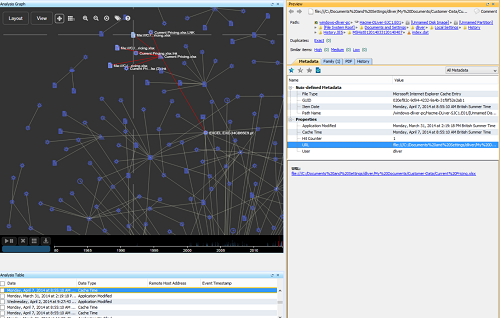
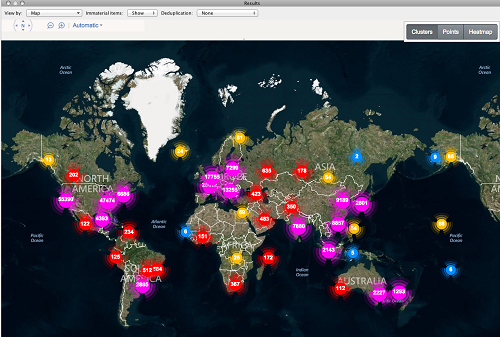
It enables users to build a chronology of activity across multiple evidence sources. It also extends Nuix’s mapping capabilities, making it possible to generate item-cluster and heat maps based on the locations of IP addresses as well as geographical data embedded in files.
eDiscovery and investigation customers will also gain the ability to ingest Logstash files and use worker-side scripting, a method for finely controlling the parameters for Nuix Workers during processing.
“Our investigation customers can rapidly find hidden connections and context between people, evidence sources, locations, and events—and comfortably cross the increasingly blurred line between traditional and cybersecurity investigations,” said Sheehy.
“Customers in litigation support, legal, and consulting firms will more easily be able to collaborate with security and incident response teams in the event of data breaches and in anticipation of post-breach lawsuits or regulatory action.”