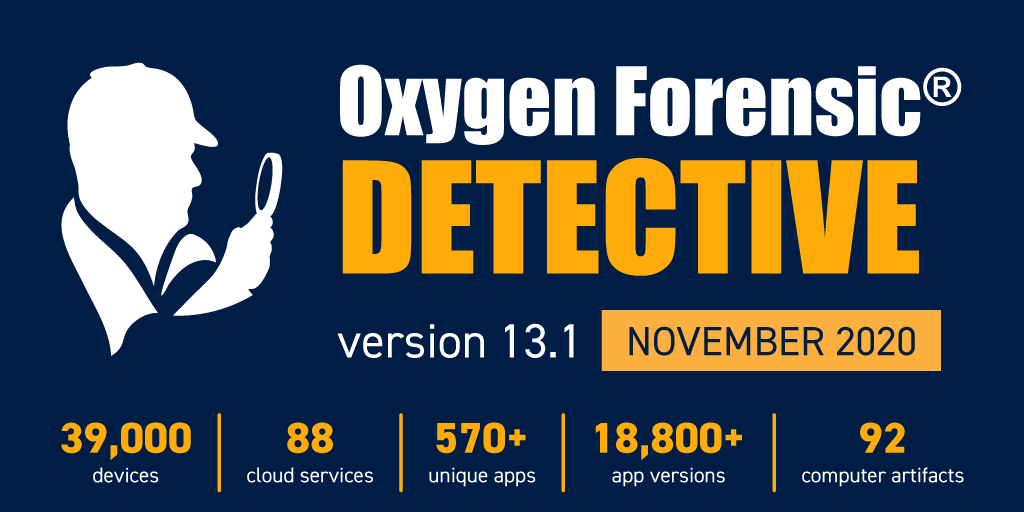
Today, Oxygen Forensics announced the release of the latest version of their flagship software, Oxygen Forensic® Detective v.13.1. The new version offers enhanced screen lock bypass methods for MTK and Qualcomm devices, Wire app decryption, a new method of Signal Messenger extraction, cloud access to SecMail, and many other features.
Signal Messenger extraction
Previous versions of Oxygen Forensic® Detective have allowed investigators to extract Signal Messenger from Apple iOS full file system, Android physical dumps and collect Signal data on Windows, macOS, and Linux computers.
However, Oxygen Forensic® Detective 13.1 introduces yet another method of Signal data extraction from Android devices; via our OxyAgent. To run this extraction, investigators simply install our OxyAgent to an unlocked Android device.
Select “Signal”, under the “Extract third-party applications data” option in OxyAgent, to extract existing backups. If there are no existing backups, you can choose to create a backup containing all the current Signal data. In either case, the evidence set will include account details, contacts, calls, and chats. Import the collected Signal data as an OxyAgent extraction to view it in Oxygen Forensic® Detective.
Support for MT6739 and МТ6580 chipsets
We’ve added the ability to bypass screen locks, perform physical acquisition, and decrypt physical dumps of Android devices based on Mediatek MT6739 and МТ6580 chipsets. While extracting a device, Oxygen Forensic® Detective also extracts hardware keys that are used to decrypt the collected binary image. In total, our MTK Android Physical method supports extraction and decryption for three chipsets: МТ6737, MT6739 and МТ6580. It should be noted, the built-in passcode brute force module is available at no additional charge.
Enhanced support for Qualcomm chipsets
Oxygen Forensic® Detective 13.1 offers an enhanced screen lock bypass method for Android devices based on Qualcomm MSM8917, MSM8937, MSM8940, and MSM8953 chipsets. We have improved the extraction of hardware keys that are used to decrypt the extracted binary images. Supported device models now include Xiaomi A2 Lite, Xiaomi Redmi Go, and Xiaomi Redmi Note 4X.
Acquisition of Android 10 devices
Oxygen Forensic® Detective 13.1 now allows investigators to perform a file system extraction of pre-rooted Android devices including those that run Android OS 10 and have File-based encryption. To extract a device, choose the “Android logical file system” option in Oxygen Forensic® Extractor and follow the instructions. When using this type of extraction users will have access to many parsed applications.
New cloud services
The updated Oxygen Forensic® Cloud Extractor adds support for 2 new cloud services, SecMail, and Firefox Browser. At 88 unique services, the built-in Cloud Extractor now supports even more services than any company in the industry.
- SecMail is a secure mail service. Investigators can gain access to the SecMail account via login and password. Extracted evidence will include the account information, contacts, and emails.
- FireFox Browser. Authorization in a browser can be done via login/password or token found in Apple iOS devices and on Windows computers. Evidence sets will include web history, saved logins, and passwords, bookmarks, opened tabs and installed add-ons.
New computer artifacts
With the updated Oxygen Forensic® KeyScout, investigators can now collect more new artifacts from computers. KeyScout now allows the extraction of all available user data from OneDrive, Slack, and Evernote apps running on Windows and macOS computers.
In addition to applications, KeyScout can now extract several new operating system artifacts to include:
- Recent Items showing which files have been recently opened on a Windows computer.
- Files and their detailed information from the Recycle Bin on Windows OS.
- The history of WinRAR operations on Windows OS.
We’ve also significantly improved the Settings menu interface where investigators can conveniently select applications for extraction, as well as set search criteria for files.
App support
We’ve updated data parsing from over 800 apps. The total amount of supported app versions exceeds 18,800. Here are some important highlights for this release:
- Wire App – data can now be fully extracted and decrypted from Apple iOS and Android devices. Apple iOS full file system and Android physical extractions are required
- Signal Messenger – decryption support for data extracted from Huawei devices running Kirin chipsets
- WhatsApp – parsing of messages from a new ChatSearchV5f database.
- Data parsing for three more new apps – Elyments, JioPages, and GroupMe
Smart analytics
We’ve added a Smart Filter button in the Timeline and Messages sections. This developing feature contains some of the most common scenarios that investigators may face in their day to day work. In this release, investigators have several options – to show all contacts or to filter contacts (including members of group chats) that have mentioned a certain word or phrase.
Including Oxygen Forensic Viewer to OFBX backup export
Now, when investigators save extracted data to the internal OFBX format, they can include the Oxygen Forensic® Viewer, which will be saved in the same folder. Choose “Include the Viewer” in the Export window and conveniently share extracted evidence and the corresponding Viewer with colleagues and other authorized personnel.
Export enhancements
With Oxygen Forensic® Detective 13.1 investigators can save their reports as RTF, a newly added file format. In addition, the OCR section now allows investigators to export recognized texts to a variety of external formats, including PDF, XML, XLS, Relativity, and others.
Wish to try Oxygen Forensic Detective? Ask for a fully-featured demo license.