In today’s world there are basically these types of digital evidence: text, image, video, audio recording and value such as geolocation or time-stamp data. A photo plays an important role among these types of evidence, bringing not only what we can see in the picture, but also a time and place the possible owner of a phone was present at. The reality is we live in a time of mobile phones with massive photographing and sharing, so knowing who took a photo is crucial information. This new technology is able to reliably verify, if a photo truly came from a specific camera. This applies for phone cameras, standalone cameras and any device with camera sensor. When you’ve found crucial photographic evidence, now you can verify its origin with accuracy of 99.9% and higher. Enter Camera Ballistics.
We have chosen the name Camera Ballistics for this product, because the concept is similar to firearms ballistics. We match a photo to a camera like a bullet to a gun. You’ve got a set of photos you want to verify, and you have a camera. With the camera you shoot test-shots, based on which a camera fingerprint is calculated. Camera Ballistics will compare the photos under investigation to the sensor fingerprint and determine if there is a match. And because we have been pioneers in this area for years, the name of the product has also become the name of the field; you can see it being used by other vendors.
What real-life case applications are there? There are innumerable possible case applications with Camera Ballistics. They key is to have your lab equipped with the right tools so when you need them. Imagine a person is suspected of producing child pornography. The suspect has many pictures saved to a hard drives, but denies that he took any of them, saying they were only downloaded from the internet. You also found a few digital cameras. Well now you can scientifically find the truth. Imagine another scenario – an explicit photo of a high school student has gone viral between classmates. The victim tells the investigator who it was that took the picture, but the suspect denies it. The investigator can quickly determine if the suspect’s phone was used to take the picture or not. Or, when an alibi is in question Camera Ballistics can also be used to solidify or disprove a suspect’s whereabouts if a photo is provided as ‘proof’. The suspect says they were at a certain location and can prove it with photos. With our photo verification tool, an investigator can determine if the camera took the photos, when they were taken and use GPS data to pinpoint location.
Camera Ballistics is not based on metadata such as EXIF, but it uses mathematics to analyze the physics of the sensor. Due to small differences in size and material composition, each pixel behaves differently, involving effects such as Photo Response Nonuniformity making each sensor unique. We can simplify the principle to say that it identifies anomalies of every pixel and uses this information to create a description of the camera sensor – the sensor fingerprint. This is true even between devices of the same make and model. It’s these differences that allow you to generate a sensor fingerprint and link an image to the specific camera that created it. Camera Ballistics will compare the photos under investigation to the sensor fingerprint to determine if there is a match.
How is a Camera Ballistics evidence accepted in courts? Well the technology is quite new, just as firearms ballistics or fingerprint authentication were in the past. Its acceptance depends on the country. The accuracy of this method is 99.9% or better, which is in line with the classical fingerprint test. Plus, there are two more advantages independent of the law. First, with this tool you get important information, which can further help to direct the investigation on the right path. Second, you can easily get a suspect’s conviction under the pressure of Camera Ballistics evidence.
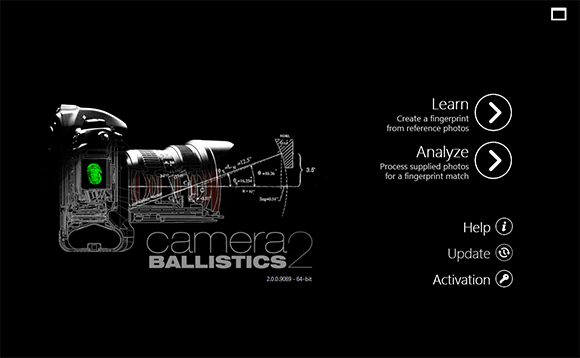
The power of Camera Ballistics is further amplified by its sleek and intuitive interface that guides you through processing in just a few clicks. Camera Ballistics takes its complex analysis method and turns it into a two-phase process. Simply create a few reference photos with the suspect camera for the program to learn about the device’s sensor and a sensor fingerprint will be generated. Camera Ballistics will use this fingerprint to analyze the photos you are investigating and match it to the ones taken by the suspected camera.
We’ve just released a second generation of this software, which is more accurate, much faster, more robust with 64-bits and works with resized photos.
Step 1 – Learn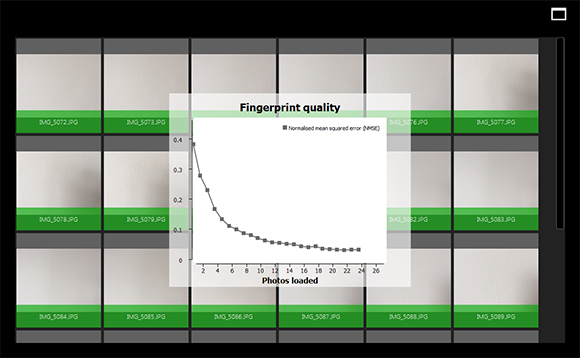
In this first step, you will supply reference photos from a camera in order to create its sensor fingerprint. The more photos you supply, the more precise your results will be. It is recommended to take at least 30 photos of white walls or clouds – images without sharp shapes and edges. Camera Ballistics will apply advanced algorithms to this folder in order to establish the sensor fingerprint.
Step 2 – Analyze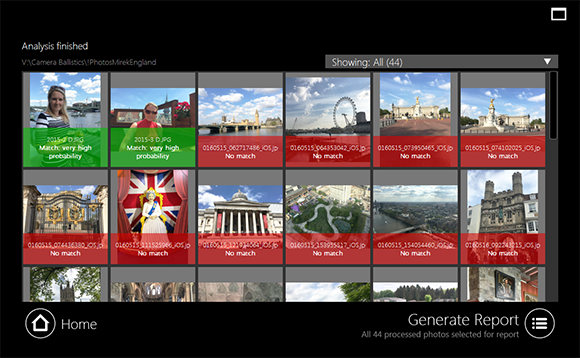
This step will match the fingerprint file created by the learn process to the photos under investigation. When you run the analysis, you can see the processing progress followed by the mathematical data and results as after analysis. Finally, a comprehensive and well-organized PDF report suitable for submission as evidence is generated. The report contains clickable thumbnails of all processed images, the camera device make and model, GPS data, camera settings, mean square error, fingerprint presence result, match probability and correlation.
Results should be interpreted like other typical ballistics tests: if traces of the device fingerprints are found, then there is an extremely high probability that a photo comes from the camera. If not found, it doesn’t necessarily mean that the particular camera has not been used to capture the image. This may happen when photos are resized too much or edited so the fingerprint information is damaged or lost.
When you use Camera Ballistics in combination with our premier mobile device forensic tool MOBILedit Forensic Express, you get not only all photos extracted from a phone, but each photo comes with information if it was taken by analyzed phone or not. This will clearly distinguish downloaded, shared or received photos from those that were actually taken by phone owner.
Forensic Express is a phone extractor, data analyzer and report generator in one solution. A powerful 64-bit application using both the physical and logical data acquisition methods, Forensic Express is excellent for its advanced application analyzer, UFED Data analyzer and generator, deleted data recovery, cloud analyzer, wide range of supported phones including most feature phones, fine-tuned reports, concurrent phone processing, and easy-to-use user interface. With the password and PIN breaker you can gain access to locked ADB or iTunes backups with GPU acceleration and multi-threaded operations for maximum speed. For more information go here.
This unique photo verification tool can be an important component of your lab. Camera Ballistics brings the state-of-the art technology that you need for high-quality and effective investigations. Please Contact Us Here with any questions about Camera Ballistics. To learn more or purchase a license please go here.
About COMPELSON Labs and the MOBILedit platform
Compelson Labs was founded in 1991 and is known for its pioneering products, such as MOBILedit, currently used by millions of users worldwide for many phone-related tasks including forensics. MOBILedit supports the vast majority of phones ever manufactured, offers physical and logical acquisition, advanced application analysis, cloud analysis, password breaker and more. Compelson has recently made a substantial investment into phone forensic products, watch for their massive development. Find more at www.mobiledit.com