Reviewed by Si Biles, Thinking Security
Sadly, at the time I put the finishing touches to the first part of this review at the start of 2015, Paris has been rocked by terrorist attacks resulting in the deaths of 17 not including the three perpetrators themselves. Subsequent investigations have revealed that at least 500 calls had been exchanged between the two groups of individuals involved – someone, somewhere in France, is most likely examining their mobile phones for even more intelligence right now.
That mobile devices are going to be used in any criminal activity is almost a given now – although post Snowden, at least the more intelligent crook might give some pause to consider the NSA or GCHQ before making their call. No surprise really when there are more phones in the UK than there are people – according to OFCOM
that’s 83.1 million subscriptions for a population estimated at 64.5 million
. 93% of adults have at least 1 mobile phone and 61% of those are so called “Smart Phones” (although if mine is anything to go by, “smart” is a bit of an exaggeration) – a Samsung S5 has a quad-core 2.5Ghz processor, 2GB of RAM and a 1920×1080 pixel display – you would be lucky to get somewhere close to this on the desktop 10 years ago. In 2005 an Apple PowerMac G5 would set you back £2,199 (inc VAT) – inflation adjusted that’s nearly £3k and it doesn’t include a display!The capabilities of these devices have advanced so far that some manufacturers have attempted to use them to replace laptops – look at the Motorola Atrix family of devices. And that’s not considering the whole arena of tablets, a majority of which run variations of the mobile phone operating systems – Android, iOS or Windows Mobile. These are definitely being touted as laptop replacements or if not that, accessories that replicate your laptop to the extent that they can be used everywhere a laptop cannot – trains, planes, buses and in the bath
.
Clearly this is a growing field, and to that end, it would be a foolhardy forensic software developer who didn’t produce a mobile phone tool. AccessData (henceforth AD) have survived long enough to prove that they aren’t foolhardy, and thus their tool Mobile Phone Examiner Plus (henceforth MPE+) is available to deal with that requirement for their clients.
MPE+ Starting Up
Let me say up-front that I’m actually a long term FTK fan, although strangely I own none of their products – my personal forensic tools include X-Ways Forensics for computers and Oxygen Forensics Suite for mobile devices. Somewhere I still have an early copy of FTK which somehow I managed to blag a “student” copy of – although since everyone since has told me that they don’t do this – including AccessData, I have no idea how ! (Incidentally AccessData, Guidance et al. – get ‘em while they are young and have no money with fully featured student editions and you’ll find that they’ll come back when they have budgets to spend – although I had a student version of FTK, I actually used WinHEX (free) more and thus it became my longer term choice…)
The ideal requirements of MPE+ are listed on the AD website
as:
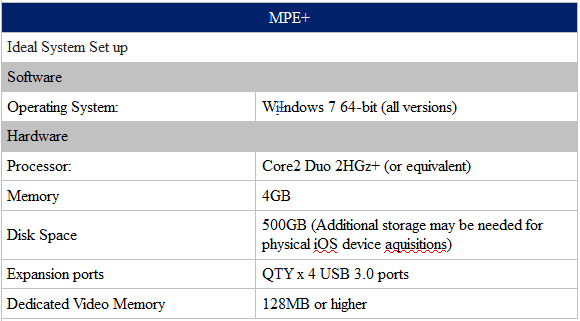
I personally ran it on two machines – one a VM under VMWare Fusion on a rather old, but very well loved, MacBook Pro (2.66Ghz i7, 8GB) and also my rather older, but very well loved Lenovo T61 (1.8Ghz Core 2 Duo, 8GB). Both scenarios performed more than adequately, with no issues at all in terms of performance – I imagine that newer hardware might accomplish the imaging faster given better USB ports but given I wasn’t overly time constrained, this was of no concern to me. On a laptop, 4 USB 3.0 ports will be a stretch I would think, bearing in mind that you need at least one spare port for the dongle itself
.
Installation was pretty straightforward I have to say. Rather than using the supplied CD-ROM, which was out of date by the time it arrived – it seems to me that in this day and age shipping optical media is somewhat an anachronistic throwback, especially given that AD are updating the product so often
– I downloaded the software from AD and had the latest version. [NOTE: The following sentences were written initially when I first reviewed the product – AD have changed their installation process to be “unattended” and the results of that update are documented in the second part of the review. I have chosen to leave the following information in place so that the reader can see the improvement for themselves and draw their own conclusions regarding the agility of AD to respond to feedback and update their products – screenshots and content in this part are from Version 5.5.5.118 and are still true, unless explicity caveated!] What I will say is that it isn’t an “unattended” installation – I’d kicked it off and gone away, making the assumption that it would just get on with it but I came back to a failure. A little confused, and being largely of the school of thought that if it doesn’t work the first time, just because it is a deterministic machine doesn’t mean it won’t work the second time I ran it again – this time, sitting around to try and figure out where it failed. It seems that there are a number of points during the installation where a quick click of a “Yes” or accepting a licensing agreement is required – failure to complete these within a certain amount of time results in a failed installation – no showstopper, just make a cup of tea before you start and be around to provide that element of human input required.
Conveniently for this review, I happened to receive a case with both an iPad and a Samsung S3 that gave me a chance to have a look at the software under “real-world” conditions (alongside Oxygen) – this also upped the number of test devices that I had to hand. MPE+ claims to support 7000+ devices across iOS, Android, Windows Mobile and Blackberry – I tested the following:
Samsung S2, S3, S3-mini, S4, S4-mini
iPhone 4, iPad, iPad Mini Retina
Sadly I couldn’t lay hands on Windows Mobile or Blackberry devices to test them directly, however, I see no logical reason to assume that they would differ significantly in performance or capability – given that Samsung and Apple between them account for about 35% of market share and that Android and iOS account for over 95% of market share, I think that this test selection should cover off a majority of the scenarios that are likely to be found in the real world.
AD are keen to emphasise the “user friendly” aspects of MPE+ and I have to say that it doesn’t disappoint. I get the impression that it is targeted toward the less experience mobile phone examiner – not that I consider this to be a bad thing. Detailed options are kept away from the outset and what is presented is a clean, unintimidating interface that it is obvious how to use. The learning curve is a gentle one enabling one to get to grips with it remarkably quickly.
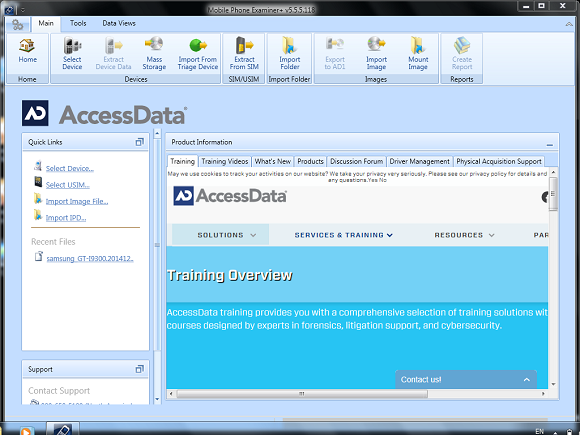
The MPE+ “Home Page”
First thing to note is that having installed the product, drivers for the device that you want to capture need to be installed separately. Again, this isn’t a show stopper and is simple to do. [Note: This was at time of writing, when AD asked me to review a newer release of the product, this now, mostly, happens automatically – bar the Apple drivers ] From the “Home” section it is simply a matter of selecting the “Driver Management” or the “Physical Acquisition Support” tabs and then installing the relevant drivers. Nothing to stop you from installing them all before you set off though – in fact, to that end, helpful “Download All” buttons have been provided, so it isn’t a matter of doing them one by one.
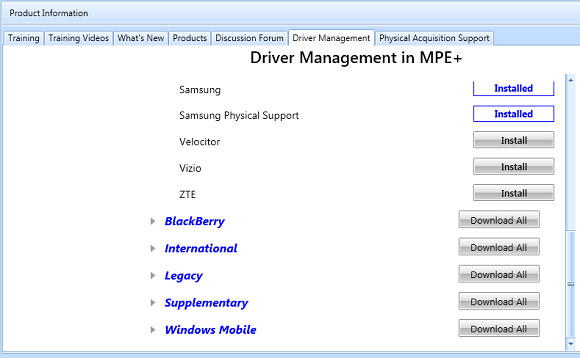
Installing Drivers
Across the top of the screen, in the current Microsoft favoured style of having a “ribbon”, are the main feature buttons. These buttons change depending upon the choice of high level tab – “Main”, “Tools” or “Data Views”. These segregate the workflow rather well with the “Main” tab being devoted to acquisition, product related features (such as drivers) and other product information (more of which later). The “Tools” tab containing analysis tools for parsing user data and file carving, and finally the “Data Views” tab giving you the results of your labours in various assorted shapes and forms.

The Home Ribbon
The “Devices” section contains all the functions required to acquire an image from a device, mass storage and SIM cards or to import a previously obtained image from disk or a triage device. Selecting to image a device presents you with a new dialog box – this allows you to choose the device manufacturer and the model from the drop down list, and if directly supported, will include a picture of your device to confirm that you’ve got the right thing.
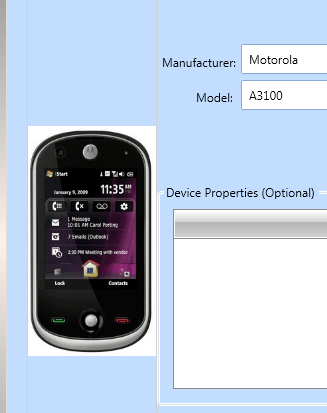
Selecting your device
Failing direct support, which I actually found to be not an uncommon occurrence – my Samsung Galaxy S4 (GT-i9505), a standard UK unlocked version from Carphone Warehouse, was notably missing – however, there is the “Android” option that allows for “dLogical” imaging. Whatever your choice, the subsequent instructions talk you through the process of configuring the phone to allow for imaging, complete with clear graphics demonstrating the required settings. Once the device has been detected, then it is a matter of selecting the data that you wish to extract and waiting…
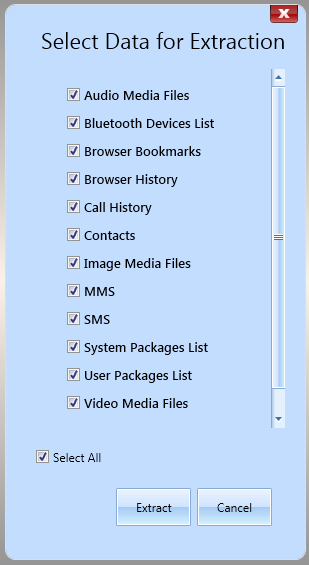
Choose what you want to get
It would be nice to have a time estimate, although I do appreciate that perhaps this is a little more complex to calculate than it might be in other scenarios. However it can be hard to tell if anything is actually happening, and until a degree of faith and experience are in place – wondering if you have crashed it is a real issue – the little blinking blob at the end of the progress bar doesn’t float my boat as evidence of “things happening”. However, as I said previously, time wasn’t a major consideration for me – but after the earlier installation crashes I wondered if I wouldn’t just come back later to find it in the same place.
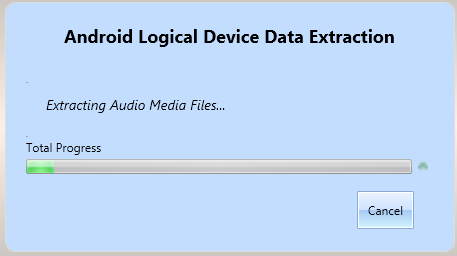
Magic happening… probably …
Extracting data from a live device isn’t the only way to get data in – you can also import previously obtained data, and this is simply a matter of selecting the correct file from the normal Windows dialog boxes. These can be saved AD1 files from MPE+ or a multitude of other formats, even those not collected using AD tools. Similarly, you can export the data to an AD1 file once you have it for future reference or for sharing with others. This isn’t a quick task in my experience, having said that – I wasn’t using the world’s fastest machines, nor was I in a hurry! It does work, and with the accuracy that you would expect. You are also able to mount an image locally in order to scan it for malware, and this is done through the “Mount Image” icon.
Note: Although MPE+ allows you to click onto other tabs when a task is in progress, I found, generally, that this resulted in a little instability of the program – be patient, let it get on with it and you’ll have no issues. Patience, in this regard, is definitely a virtue!
Anyhoo, I digress. Once you have finished your extraction, you are ready to move on. We will come back to the tools Tab next time, right now we are going over to the Data Views to find out what has been extracted by default. The Data Views tab has an alternate ribbon along the top.

Data Views Ribbon
Each of the data views has a number next to it indicating the items found. Clicking on each of these opens the respective sub-page. To a certain extent there is a lot of similarity between these sub-pages – you have similar displays and you can filter and sort columns in an intuitive way.
Starting at the left and working our way right. Device information contains all of the hardware type information from the device – if a SIM card is in the device, it includes the details of the SIM card, provider etc.
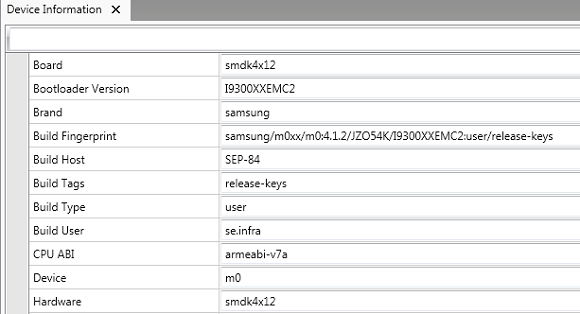
Device Information Sub-Page
(Please forgive the screenshots where they cut out information and have occasional redactions …Sections have been removed to protect the identity of the innocent!)
There is a good and useful selection of information summarised here – as well as the device hardware IMEI and SIM details – including the timezone of the device and the serial number.
One click to the right is the “Time Analysis” tab – this results in the most visually appealing of all of the sub-pages in my opinion. Graphing the communications against time…
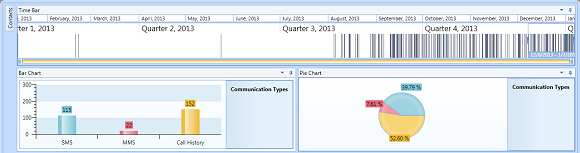
Timeline Sub-Page
Clicking on any particular section focuses the detail of the other windows to the period of interest – so, for example, above, when I select November 2013, the lower graphs change to reflect the statistics from that period. Clicking on the Call History bar in the chart changes the contents of the bottom pane to show the call log for the period, the MMS, the MMS log etc. It does make for a very quick triage of a period of interest, and even on my dinosaur machine this was very quick and responsive.
The next tab is the Social Analysis tab – I’m going to come back to that one in part 2 of this review. It’s a more powerful feature and I think deserves a little more coverage than the other things are going to get.
Next up – Call History – much what you would expect really – the call history.
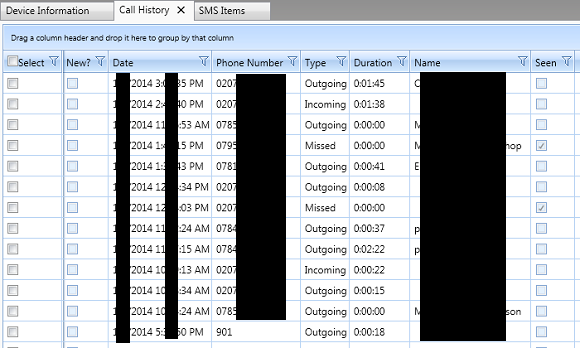
Calls Sub-page
As with other sub-pages, clicking on the filter icon at the top of the column allows you to create a search on the standard “Is equal to”, “Is less than”, “Is greater than” basis, as well as clicking on an individual column name to sort the data either ascending or descending.
This kind of interface persists across all of the other tabs. Where information can be cross referenced (e.g. numbers to names in the contacts) this seems to happen automagically and where images are available (e.g. as contacts pictures or as MMS contents) these are either displayed immediately or are a simple click away. On the MMS tab, the default view is the first part of the MMS message, not the “attached image” as it were, so you need to select the image before it displays – this isn’t a problem for me, although if going through a larger number of MMS’s a method to make the image show by default might be useful in future versions (if I’ve missed how to do this, I apologise, but I couldn’t see it …)
Contacts:
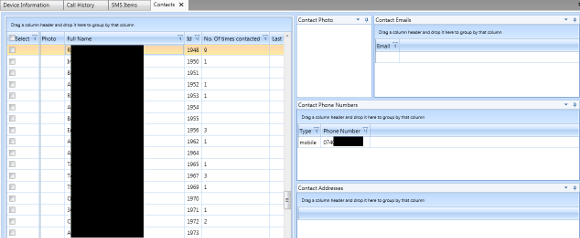
Contacts Sub-page
MMS/SMS:
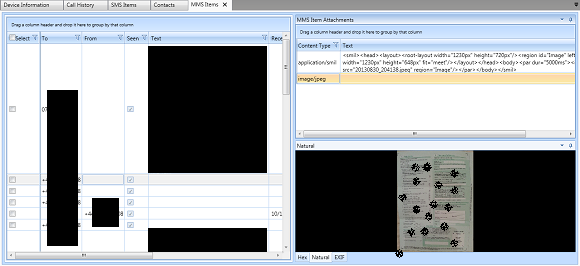
MMS Sub-page
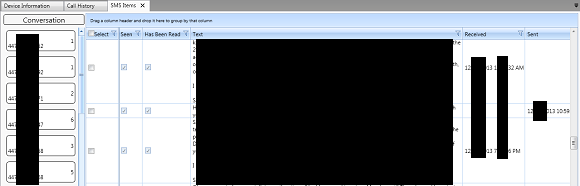
SMS Sub-page
Again, a visually pleasing, as well as very useful feature is the ability under the SMS sub-page to select SMSs by “Conversation” – on the left hand side of the SMS sub-page are a list of contacts, with a number beside them – this number is the count of the to-ing and fro-ing in the conversation in total. Clicking on a conversation brings up a simulated “speech bubble” visualisation, very similar to that you would expect to see on the phone itself.
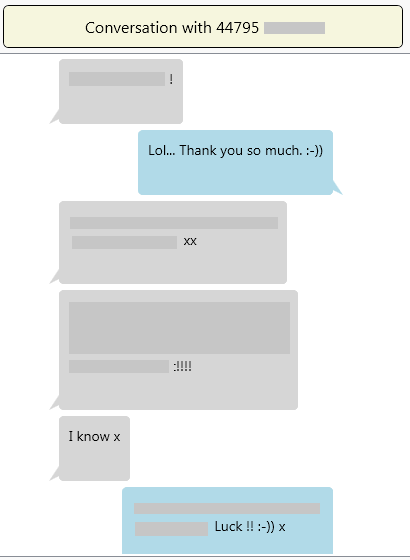
“Bubbles!”
Bluetooth devices is self explanatory, showing the devices which have been bonded to:
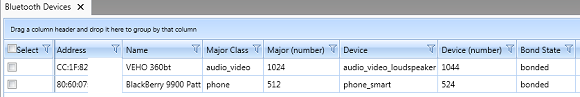
Bluetooth Sub-page
Similar is the WiFi Hotspots:
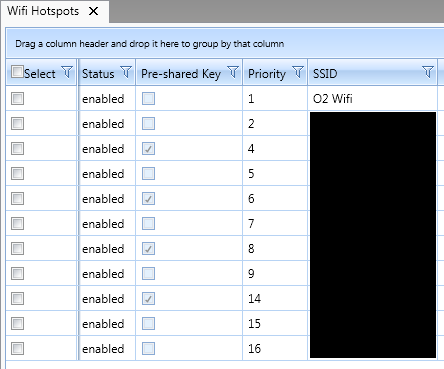
WiFi Sub-page
In the web department, there is both a browser history and the bookmarks list. The browser history includes information including the last visit time and the total number of visits. The bookmarks is just that, bookmarks and otherwise unremarkable.
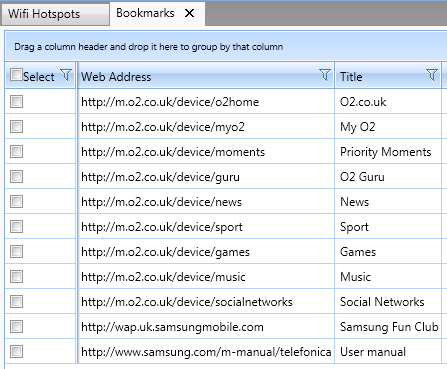
Bookmarks Sub-Page
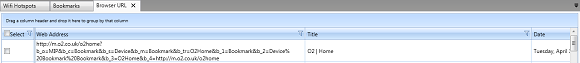
History Sub-Page
Finally, we are at the end of the Data Views and correspondingly the end of the first part of this review – coming soon will be the second part where we will look into the more Advanced Features (including scripting – something AD are justifiably proud of IMHO), imaging of SIM cards, creating reports and some of the support features that AD have built into the product.
So what we have left are the acquired Audio, Image and Video files. In all of these the player or previewer lives down in the bottom right of the screen. It represents itself as the “Natural” view – not sure if that is the term that I would necessarily use – viewing Natural to mean un-interpreted, but this is my pedantry, nothing more. As well as this view, there is a plain Hex view and, where applicable, the EXIF information as well. As far as I can tell the EXIF data is accurate and seems to include all that one might wish for. The video and sound played smoothly and clearly through the “Natural” embedded viewer and were easy to stop. However, the fact that they started playing automatically was a little annoying to me – I can easily imagine circumstances where I would want the opportunity to decide to play a clip or not – but again I apologise if there is a setting somewhere that I missed which makes it possible to turn this behaviour off. If not, it might be something for AD to consider for future versions.
So, the last screenshots of this part of the review:
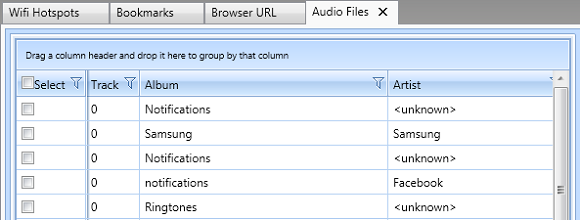
Audio Sub-page
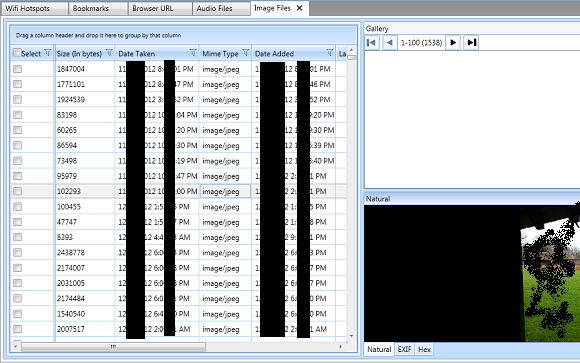
Images Sub-page
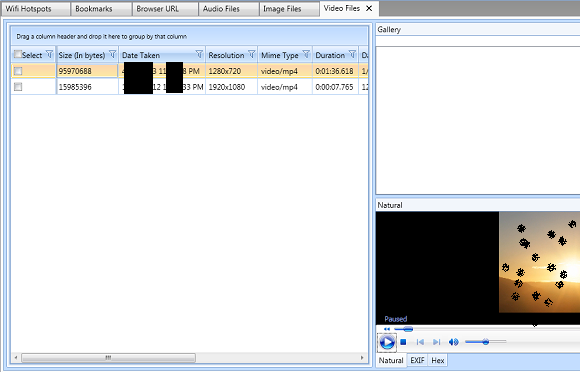
Video Sub-Page
I do sincerely hope that you’ll come back for the second part of this review. In the meantime, forensicate
well !
In Part 2: SIM Cards, Advanced Features, Reporting & Support
Learn more about MPE+ on the AccessData website or contact AccessData for further information.
Discuss this review here.
About the reviewer
Simon (Si) Biles is an Information Security and Digital Forensics Consultant. Starting as a UNIX and Linux SysAdmin more years ago that he cares to remember, he now specialises in "alternate" operating systems (which, it seems, is everything not made by Microsoft), both in Forensicating and in Security. As well as running the consulting company Thinking Security (www.thinking-security.co.uk), he also lectures for DeMontfort University in Leicester on both Forensics and Security to undergraduate and postgraduate students. If you enjoyed the review, and would be willing to spare a cup of coffee in exchange for the time it may have saved you in doing it yourself, Si would be grateful if you would consider making a donation to the charity WaterAid in support of his daughter who is currently training hard for a major fundraising event – http://my.wateraidfundraising.org.uk/dwkayaking
Si can be contacted by e-mail at: si@thinking-security.co.uk
LinkedIn : uk.linkedin.com/in/simonbiles/en
Twitter: @si_biles
Notes
1 http://media.ofcom.org.uk/facts/
2 http://www.ons.gov.uk/ons/rel/pop-estimate/population-estimates-for-uk–england-and-wales–scotland-and-northern-ireland/2013/index.html – scaled at an annual growth rate of 0.63% for one more year on the 2013 results…
3 http://www.sony.co.uk/electronics/xperia-tablet-z/sgp511-sgp512-sgp521 – other waterproof tablets are probably available – not recommending this one in any way!
4 http://accessdata.com/solutions/digital-forensics/mpe/technical
5 You can configure the dongle on another machine to run as a server – I did try this, although I tried it running as a server on the MacOS base operating system and using the Windows VM as the client so I didn’t gain any USB ports by it. It does work just fine though!
6 The version that I downloaded and tested in this part of the review was outdated by the time I got to the second part – owing largely to AD's request that I wait to test the new installer which was supposed to fix the “unattended” problem. See part two to find out how that works out …
7 At the beginning of the review period, I was fortunate to be given a run through of the interface by Kevin DeLong of AD. As a testament to the simplicity of this product, going through the whole thing only took about 45 minutes.
8 I’m trying to get “foreniscate” into publication enough to get it included in the Oxford English Dictionary as a legitimate alternative to “Perform a Forensic Analysis”, if only to save time typing it regularly!