Reviewed by Jade James
Passware Kit Forensic is an easy to use tool which provides a ‘complete electronic discovery solution’, reporting on all password-protected items on a system and decrypting them.Passware comes with many features, including the following.
• Password recovery for 280+ file types including Microsoft Office documents, PDFs, ZIP files, QuickBooks, Filemaker, Lotus notes, Bitcoin Wallets, Apple iTunes Backups, Mac OS X Keychain and so on.
• Cloud Data Acquisition – acquiring backups and data from cloud services such as Apple iCloud, MS OneDrive and Dropbox.
• Hardware Acceleration – Accelerated password recovery with multiple computers, NVIDIA and AMD GPUs, Tableau Password Recovery, and Rainbow Tables. It is possible to use up to 8 GPUs on a single system.
• Linux Agent ready – The Linux version can run a portable Passware Kit Agent from a bootable Linux USB drive on any system without installation.
• Mobile Forensics – Recovers passwords for Apple iPhone/iPad and Android backups as well as Android images and extracts data from images on Windows phones. Passware is integrated with Oxygen Forensic Suite.
• Intelligent Detection – Passware detects all encrypted files and hard disk images and reports the type of encryption and the level of complexity for the decryption of these files and images.
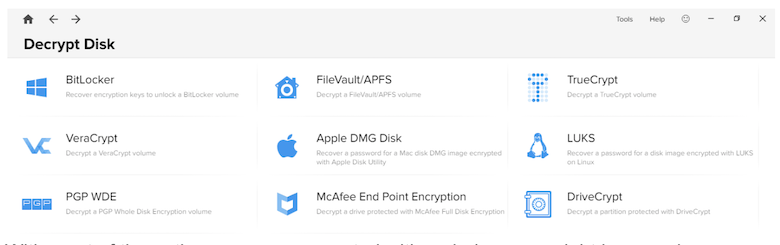
• Decryption of Full Disk Encryption – Passware decrypts or recovers passwords for BitLocker, FileVault2, TrueCrypt, VeraCrypt, LUKS, McAfee, APFS, Apple DMG, Symantec, and PGP disk images.
• Live Memory Analysis – Analyses live memory images and hibernation files and extracts encryption keys for hard disks, logins for Windows & Mac accounts, and passwords for files and websites, all in a single streamlined process.
Passware gives the following minimum system requirements in order to utilise the software in full:
• Microsoft Windows Vista, Server 2003/2008/2012/2016 or Windows 7/8/10 (64-bit) installed and configured on your system.
• 1 GHz processor (2.4 GHz recommended)
• 512MB of RAM (1GB recommended)
• 150MB of free hard disk space (more if you use custom dictionaries)
Passware supports PC platforms only. However, it can recover passwords for some files created on Macintosh, such as FileMaker. You can run Passware products on any virtual environment available (VirtualBox, Wine, Parallels Desktop, etc.) to unprotect your files.
Currently there is not a Linux Version of Passware, although it is possible to create a bootable Linux USB drive to run the Agent on any system without logging in and installing on the target computer.
This review was written for Passware Kit Forensic 2018 version 2.1 which had the following updates from previous versions:
• Resolved an issue with saving password recovery state
• Improved Passware Agent Hardware resources management
• Resolved Windows key ‘Incorrect Product Key’ error [SUP-868] • Minor GUI improvements
• Resolved minor issue with Passware Kit Forensic portable
Passware Kit uses five common password recovery attacks, four advanced file-type specific attacks, and two methods of grouping attacks together to form complex passwords.
The common password recovery attacks consist of Dictionary, Brute-force, Xieve, Known password or Part attack and Previous Password attacks.
A dictionary attack is a form of brute force attack for cracking a password by trying to determine its decryption key or passphrase using a considerable amount of likely possibilities, such as words in a dictionary.
The dictionary attack for Passware allows you to select the password length, has 9 built-in dictionaries (Arabic, Dutch, English, French, German, Italian, Portuguese, Russian, and Spanish) and allows you to add a Reverse Password Modifier to the Dictionary attack to check for reversed words from the dictionary.
A brute-force attack consists of submitting as many passwords or passphrases as possible with the hope of eventually guessing correctly. The brute force attack will systematically check all possible passwords and passphrases until the correct one is found.
In regards to Passware, this brute-force attack finds passwords by checking all possible combinations of characters from the specified symbol set and is the slowest, but most thorough method of cracking passwords.
The Xieve attack is another form of brute force which speeds up the password recovery process by skipping combinations which are nonsensical. Passware will only check the most common combinations of letters, skipping all the combinations that are not typical for the language selected.
If you know some of the password then you can specify what you know and then combine this with other attacks using the ‘Join Attacks’ option.
Previous Passwords attack checks passwords that were previously recovered by other attacks for other files. It automatically saves all found passwords. This is a useful feature as individuals tend to use the same password for most of their logins, and would save time in password cracking.
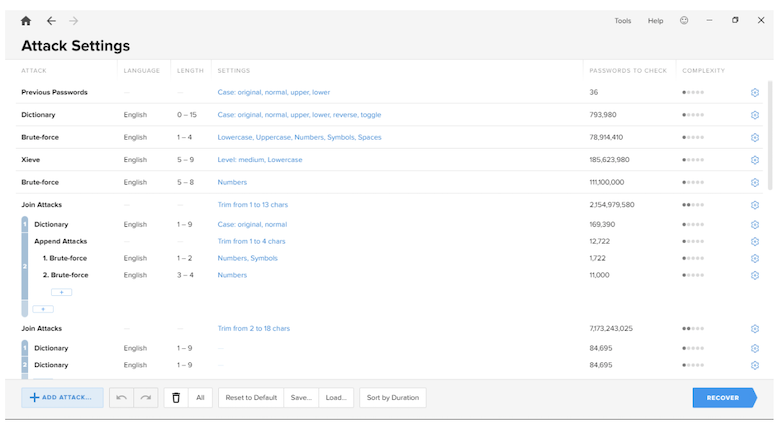
Modifiers allow for different variations of passwords:
• Change casing – you can choose to make certain characters upper/lowercase.
• Order – the order of the text can be reversed, for example ‘Password’ could become ‘drowssaP’.
• Substitution – this allows for the substitution of letters for numbers or symbols for when individuals use substitution to make passwords stronger, for example ‘Password’ could become ‘Pa$$w0rd’.
More information about the four advanced file-type specific attacks and two methods of grouping attacks can be found on the Passware website.
The installation of the software was simple. I was provided with a download link and product key. I was also provided with a quick start guide and samples which have been very helpful to test the different features of the software.
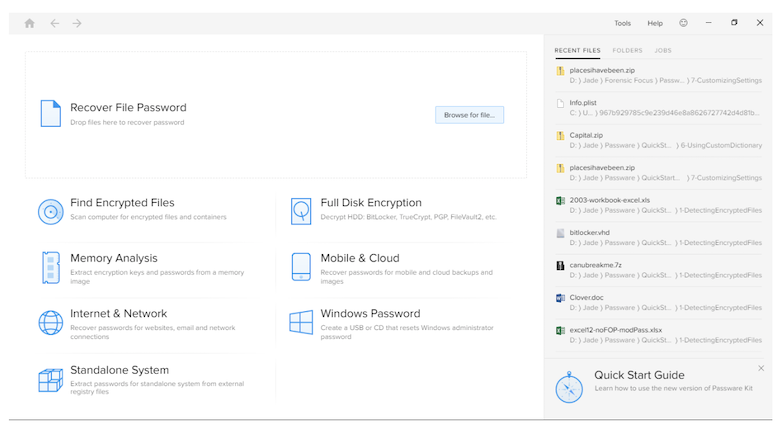
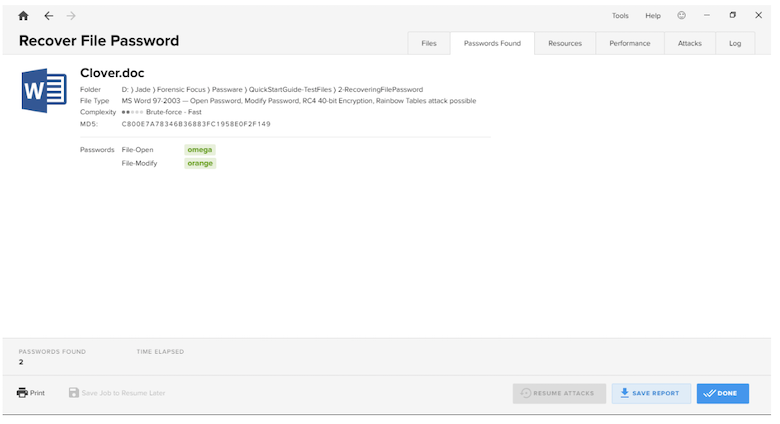
The first option allows you to navigate to a certain file and use the pre-defined settings to recover the password. The interface gives you a lot of information about the file such as the file path and what type of file it is; in this example it states that it is a MS Word 97-2003 file which uses the RC4 40-bit encryption to encrypt the password. The software is intuitive in that it states Rainbow Tables attacks are possible due to the file type.
There also several tabs which let you view the files you have selected to crack. Once the password for the file has been cracked, it will show you the password(s) in the ‘passwords found’ tab, which you can copy to the clipboard and paste elsewhere. This view also gives you the MD5 hash of the file.
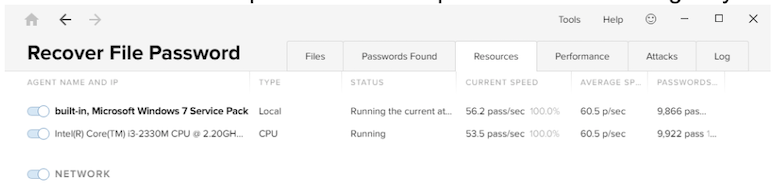
The ‘resources’ tab shows you what Passware has used to crack passwords, as in the CPU, RAM etc. and network and whilst the password cracking is running you can toggle the resources so you can use more/less as required.
The ‘performance’ tab gives you a visualisation of how many passwords have been submitted per second. The ‘attacks’ tab gives you a rundown of all the different types of attacks Passware is planning to conduct and the results of these. The ‘log’ tab gives you a breakdown of what attacks were performed, the time and date of these attacks, how many attempts were made with each attack, and the option to export the log.
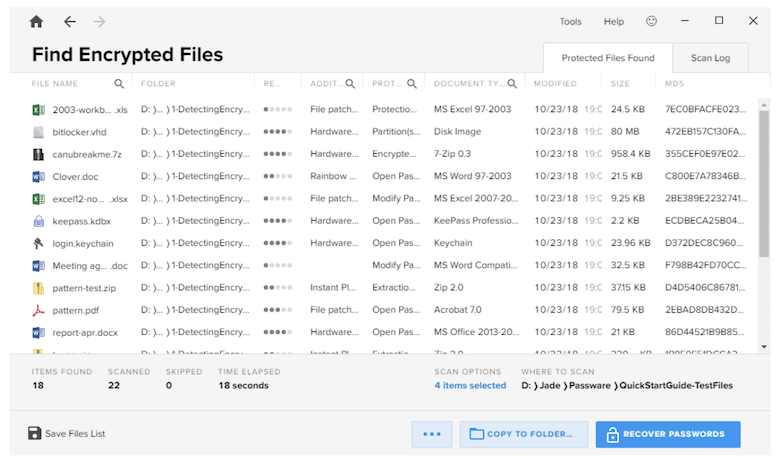
The ‘Find Encrypted Files’ option allows you to select different volumes on a system to scan for files which may be encrypted. You can search system folders, show file types, scan for encrypted containers and disk images, and compute the MD5 hash for these files.
You can choose to scan your local system, the local user’s My Documents folder, or other selected drives and folders.
After the initial scan you are given a list of files which have been found to be encrypted. You are then presented with the option to recover the passwords.
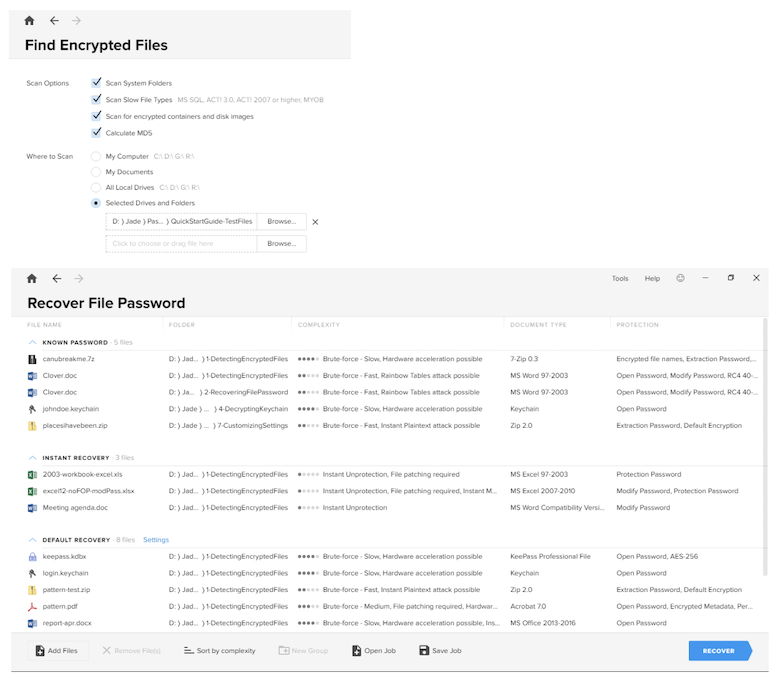
Passware will then put the files into three separate lists; known password, instant recovery, and default recovery. Once you begin the recovery process the known password and instant recovery files are cracked very quickly and you are given the passwords almost immediately. The default recovery files will take a lot longer to crack, depending on the specification of the system you are running Passware on.
Again you are presented with the files, password found, resources, performance and log tabs. You also have the option to skip an attack or skip a file. You also have the option to pause or stop an attack. If you stop an attack, you are able to resume attacks, save the job to resume attacks later, or save the report of the job.
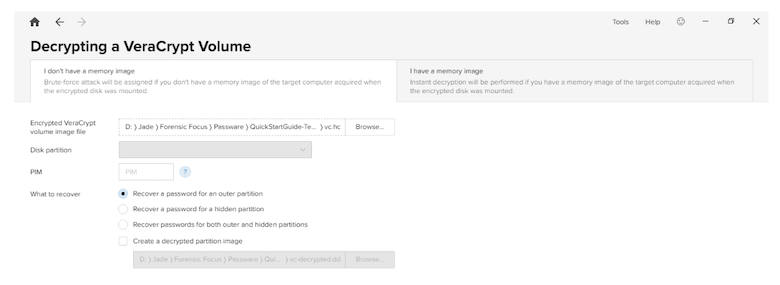
Selecting this option gives you a variety of different encryption types that you can decrypt. This is on the basis that you have already imaged an encrypted container, as you are not given the functionality to do this within the software.
With most of the options you are presented with a choice: you might have an image file, which means that instant decryption will be performed if you have a memory image of the target computer acquired when the encrypted disk was mounted.
Otherwise if you don’t have an image file, brute-force attack will be assigned. Using the encrypted volume image file and the physical memory image file, Passware creates an unprotected, decrypted version of the file. You can then use other software of your choosing to view the contents.
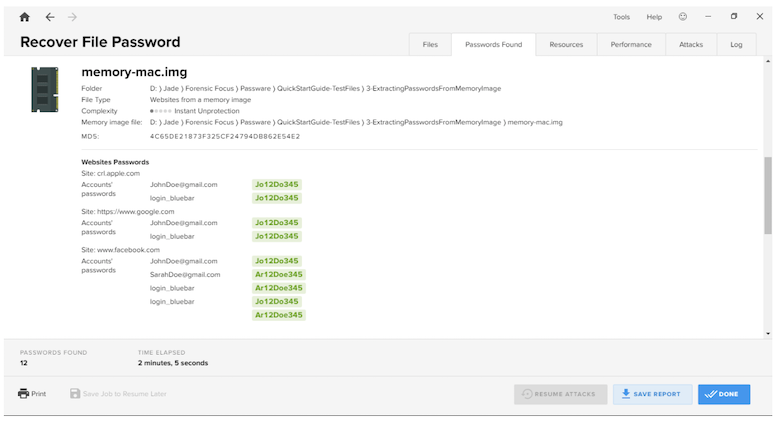
Conducting memory analysis is an option only available with Passware Kit Forensic. Again there is no functionality to capture a memory dump within Passware, therefore you would have to acquire this prior to the examination using other software.
Passware allows for the examination of DD, IMG or BIN memory image formats. Once you have a memory image, you simply navigate to where it is on the system and then choose to recover passwords for Windows or Mac users; extract passwords for Facebook and other websites; acquire data from Windows OneDrive; extract iCloud token from a memory image and download data from iCloud; or extract the master password for 1Password for keychain (standalone version – the option to extract passwords for a standalone system from external registry files) from a memory image.
From the memory image, Passware is able to extract the user accounts and passwords of the system and the websites which have been visited when the credentials were stored within the RAM of the system.
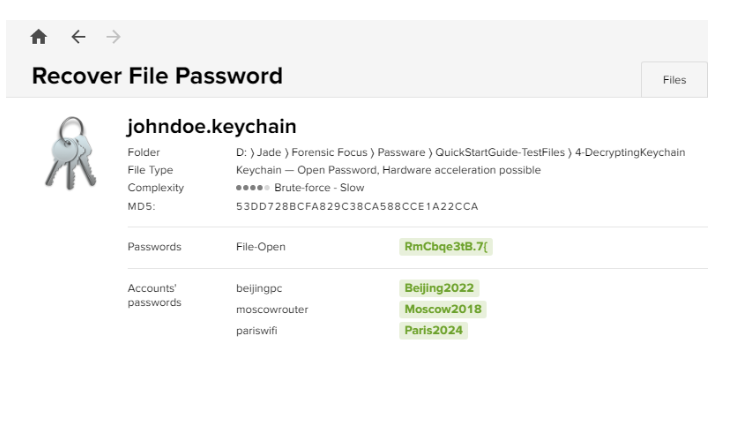
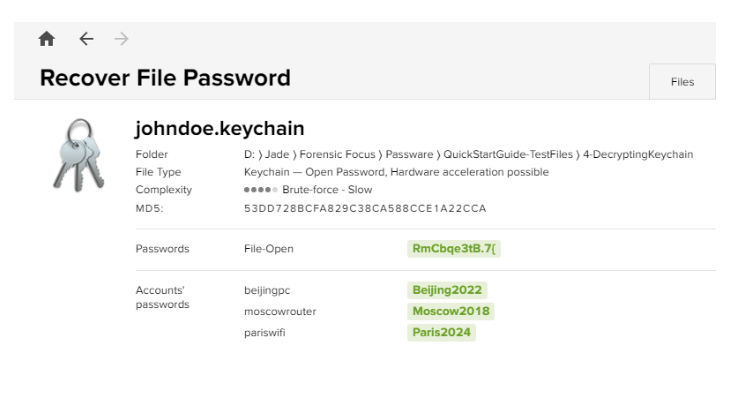
Again this is another feature which is only available for Passware Kit Forensic. Keychain Access is a MacOS app that stores your passwords and account information and reduces the number of passwords you have to remember and manage. By default, your keychain password is the same as your user password (the password you use to log in to the computer).
To decrypt a keychain password using Passware, you need to select the ‘recover file password’ option and navigate to where your keychain file is stored. You are then given the option to use the predefined settings or customise the settings (manually set up attacks). Using the sample data, the file-open password is recovered almost instantly and Passware extracts the login credentials from the keychain.
Passware provides an examiner with a lot of options to recover passwords from encrypted or password protected files, folders and volumes. The tool is easy to use and requires no previous training or experience.
Using the tool I found it to have a few small limitations; for example when recovering a password from an encrypted file, sometimes I was unable to choose to use the predefined settings or advanced settings as the software would completely skip this step. I was also unable to acquire data from iCloud even though I was using real credentials. Passware was also unable to detect Dropbox on the system that I was using even though it was present. These may be due to the fact that I was not using the current version of Passware. I was unable to use the Internet & Network and Mobile and Cloud options due to bugs with the software, which was disappointing because Passware is integrated with Oxygen and it would have been nice to see how they interact together.
I was also unable to send any bug reports through Passware itself and would have had to manually save the error report and send it to support. However there was an option (a smiley face at the top of the interface) to provide feedback and include a screenshot of the current screen, which would have been useful if the bug report stayed on the screen whilst you attempted to submit feedback.
Overall this is a good tool to have, but it is highly recommended to run the software on a system that is high spec (i5 minimum and a lot of RAM) as you will have to leave Passware running for weeks in order to crack files.
Passware have responded to the limitations described above:
Passware may skip the ‘choose settings’ step if a user has already finished the password recovery for this file and Passware Kit has saved this status. In order to start over, you can clear the state by clicking Tools | Clear History… | Recovery states.
Currently, Passware does not support acquisition for iOS version 12.1.
The new version of Passware Kit Forensic – 2019 v1 – has just been released. This will have increased Dropbox capabilities, and detailed logging will be available should any troubleshooting be required.
The bugs in the Internet & Network and Mobile and Cloud options have been fixed in the latest version of Passware, 2019 v1. This version also has increased support for sending bug reports, so as long as your mail client is set up as default in Windows, there should no longer be any issues submitting reports.
About The Reviewer
Jade James BSc (Hons) is currently a Digital Forensic Investigator at the Serious Fraud Office. She has previous professional Digital Forensic experience from working at IntaForensics, Home Office Centre for Applied Science and Technology and the City of London Police. Jade has gained experience from conducting Computer, Mobile devices examinations, Drone Forensics and has been involved with ISO 17025 & Quality Standards both as a Digital Forensic Practitioner and Quality Manager.
About Passware
Passware provide digital forensics solutions including Passware Kit Forensic, a complete electronic evidence discovery solution that reports all the password-protected items on a computer and decrypts them. Find out more on passware.com.