Encryption, passwords, pass codes and other security measures are seemingly the ever-moving target in digital forensics. Whether your investigative focus is mobile devices and trying to bypass or obtain the pass code to collect valuable phone/tablet data; computer systems involved in your case that are potentially encrypted with Bitlocker, TrueCrypt or another method; or you simply have a password protected file that may be paramount in your case, the advent of advanced security measures in the digital world has presented us all with a problem. How do we work around these security measures?
Passware has been at the forefront of helping address this issue for years. Their latest version of Passware Kit Forensic 2020 brings together a great combination of ease of use and functionality.
System Requirements
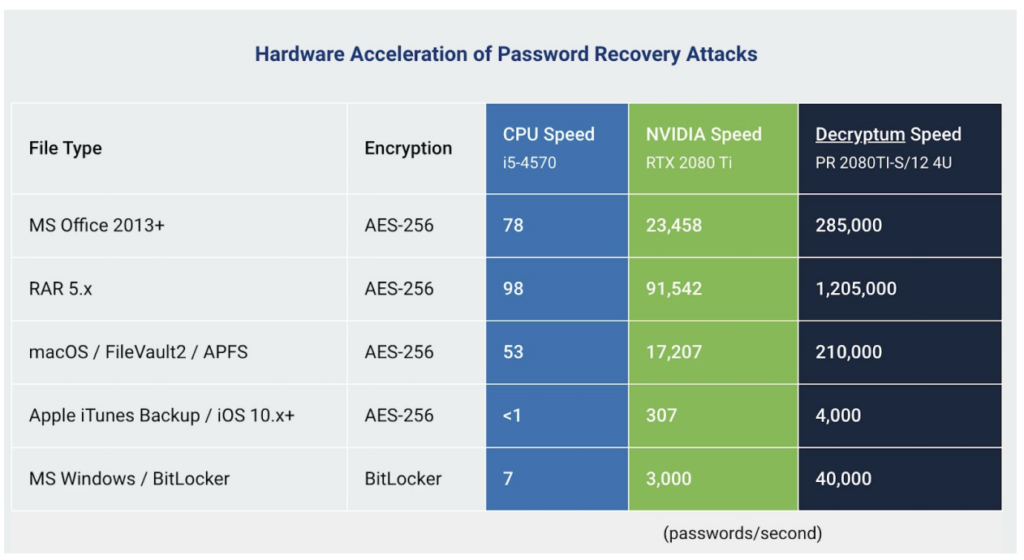
Those that have attempted password-cracking know very well how time- and resource-intensive the process can be. Essentially, the more main CPU and GPU resources you can dedicate to the process, the faster it will go and the higher the likelihood of obtaining the password, particularly in a brute-force attack. To be clear, brute-forcing a password with completely unknown parameters is not ideal, but Passware Kit Forensic 2020 has the full functionality to do this if this is what your case calls for. A word of warning, however: you’ll want to dedicate a very robust machine to this task. Brute forcing a password is not something you want running in the background while you’re conducting a system analysis or decoding a phone extraction.
Fortunately, Passware provides some guidance on their website with regard to what types of hardware specifications you may want to incorporate for better acceleration of the process and shorter turn-around times. See below from the Passware Kit Forensic web page:
Passware Kit Forensic Capabilities & Options
Passware Kit Forensic 2020 has a broad array of offerings for virtually any need with regard to password identifying and/or cracking. The main platform is (and has been) on MS Windows, but there is also a version for Mac OS, which is necessary when dealing with certain work-arounds in Mac forensics (discussed later).
With either operating system, the basic capabilities are essentially the same and offer a fairly extensive list of language variations for the requested attacks for those outside English-speaking countries or cases that may take on an international face. After initial setup and upon startup, the user is provided with a variety of options, depending on case need, as detailed below:
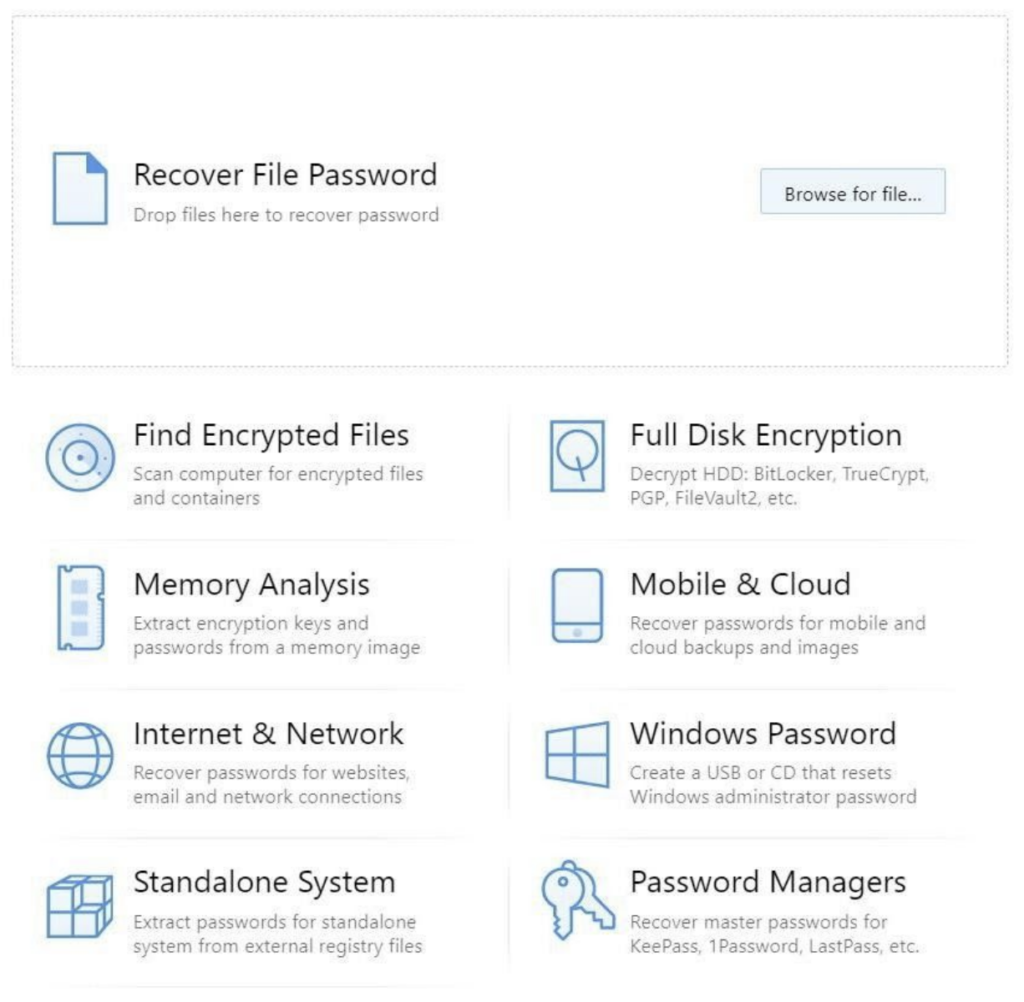
Locating Encrypted Files
Running through the highlights and likely most frequently used options, we started with finding encrypted files on our main forensic system. This process flowed along easily and quickly. There are options to scan the entire system or skip certain files, but generally speaking the workflow is intuitive and easy to understand. When it was completed, we were provided with a listing of all of the encrypted files located on the system:

One of the highlights about this function is not only the identification of encrypted files on the system, but with the existence of the Manifest.plist file, we’re automatically clued into the existence of an Apple iTunes (iPhone/iPad) device backup on the system, which would likely lead to further analysis. As a side note, we can also use Passware Kit Forensic 2020 to attack the Manifest.plist file to decrypt iTunes backup files and/or encrypted iPhone extractions in our mobile forensic tool of choice.
Memory Analysis
In recent years, the practice of digital forensics in the field has evolved to incorporate collection of volatile memory (or RAM) from suspect systems, whenever possible. This is because the volatile memory stores gigabytes of data on most modern systems, and that data can often contain passwords that are not stored in the allocated area of the drive or are otherwise obfuscated via hardware- or software-based encryption. Passware Kit Forensic has the ability to scan a dump of the volatile memory of your suspect Windows, Mac or Cloud system to attempt to locate any available passwords. Additionally, we can analyze the Pagefile.sys for similar data:
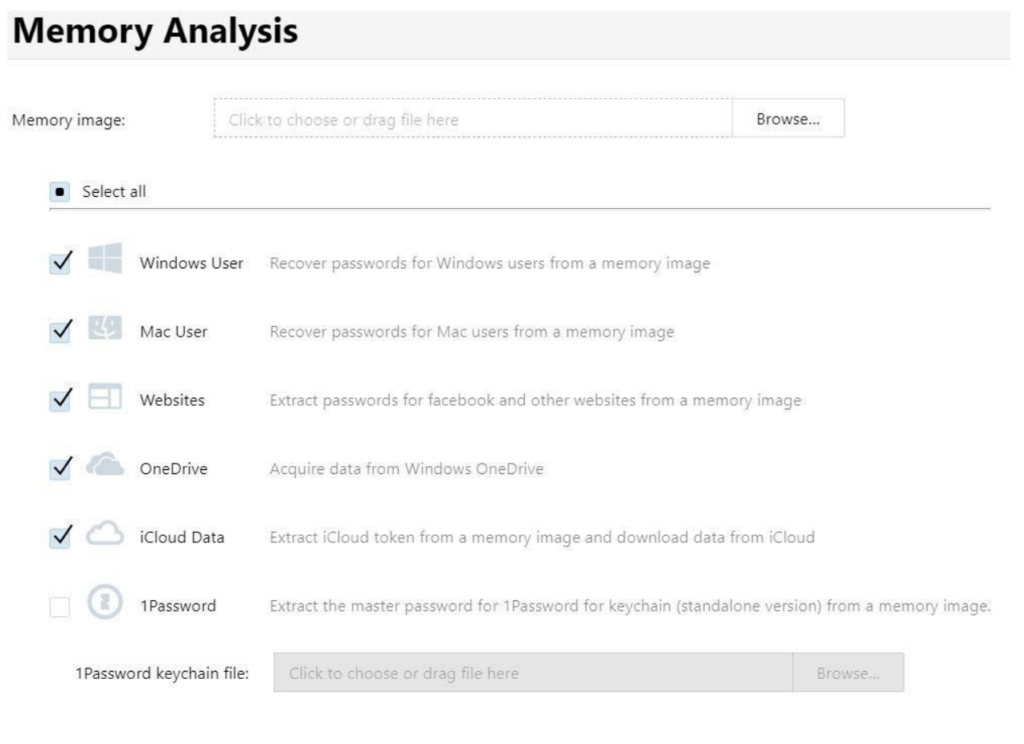
The appropriate collection and documentation of the volatile memory on the system is of vital importance, and there are many proprietary and open-source tools that can help facilitate this, but once it is accomplished, Passware Kit Forensic can assist with the crucial analysis that may mean the difference between accessing the full or partial system and sitting on a system that you can’t access because you don’t know the password.
Internet & Network
Among the functions that Passware Kit Forensic affords us is the ability to locate and render the passwords for a number of internet-based and network-based passwords. The interface is simple, self-explanatory and easy to navigate.
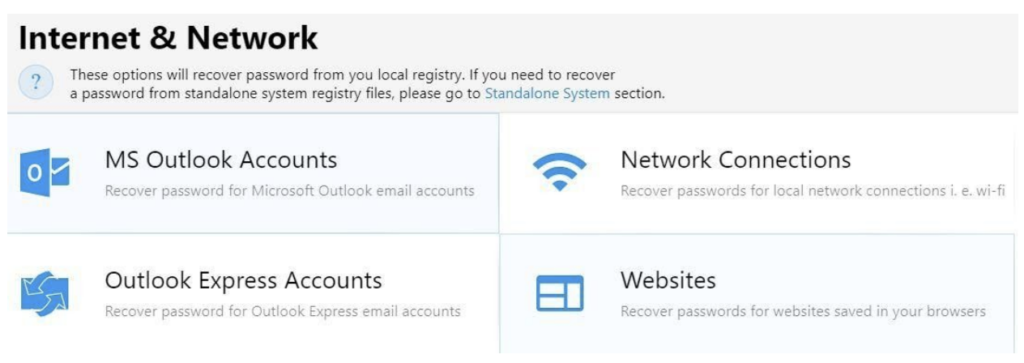
The artifacts returned on this function could potentially help confirm or refute that a suspect’s computer had such accounts, which websites they accessed and potentially the passwords for them, and which networks the system may have been connected to, with password recovery. It’s a great resource in any investigation.
Full Disk Functionality
Full disk encryption is a constant issue for digital forensic examiners. Whether we’re dealing with an operating system based encryption such as Bitlocker, FileVault or Linux-based encryption, or encryption from a third party like TrueCrypt or VeraCrypt, the developers at Passware Kit Forensic have worked hard to give us as many of the likely options for addressing these issues as possible:
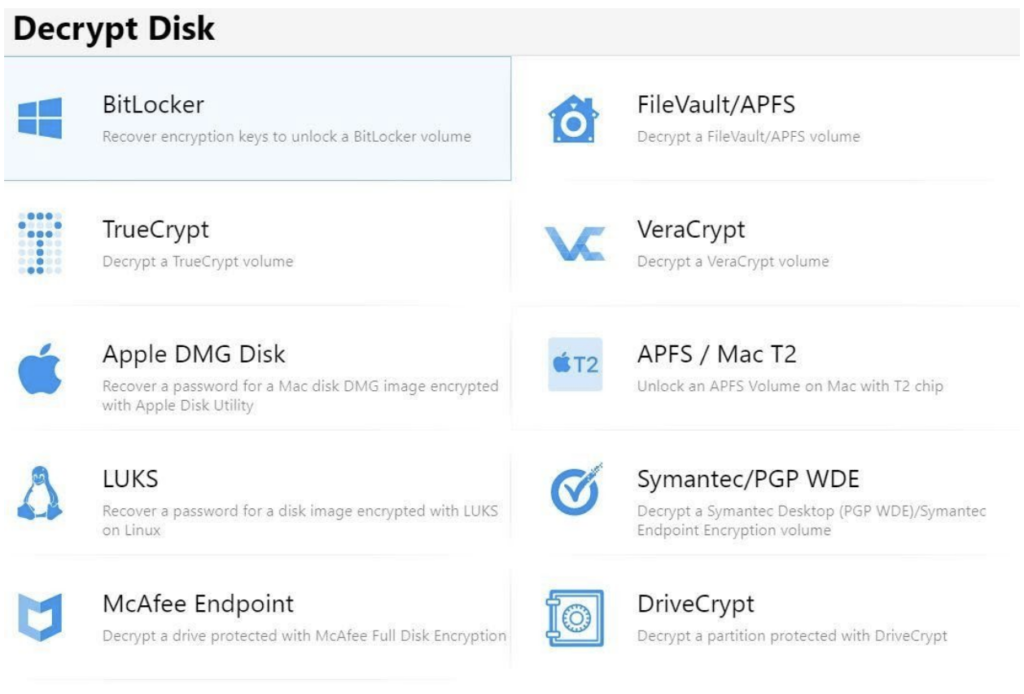
Of note is the ability to unlock an APFS Mac with the T2 chipset, a particular pest for examiners that has come about in recent years. Passware Kit Forensic provides this functionality with specific instructions that will require iCloud credentials or an iOS backup, your target Mac machine, a Thunderbolt 3 cable, and your Mac Forensic machine. This functionality is a great resource and only available using the Mac version of Passware Kit Forensic.
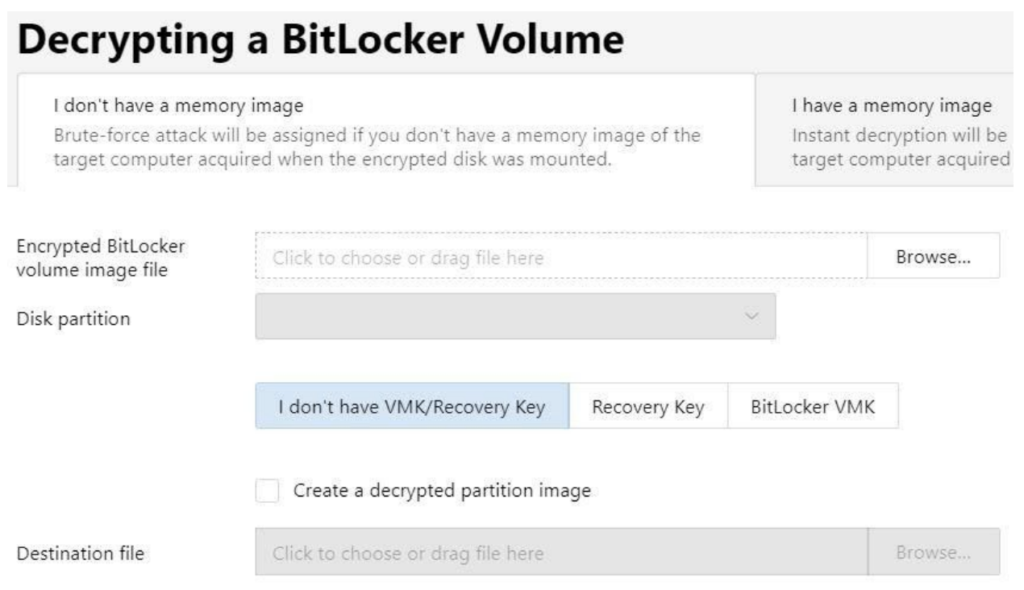
Because the majority of computer systems in use are MS Windows, we worked through the flow of decrypting a Bitlocker volume. The Passware Kit Forensic functionality of this tool is very simple. Just point Passware Kit Forensic at your forensic image of your Bitlocker drive, which can be in any of the standard (.dd, .img, .bin) formats or other types (.e01, .ex01, .l01, etc.) formats. A particular partition of your disk that may be of interest may also be selected. From there, simply tell Passware Kit Forensic what we know about the Bitlocker volume – do we have a Bitlocker, Recovery and/or VMK key – and then direct the tool where we want the decrypted volume to be placed and let Passware Kit Forensic work its magic.
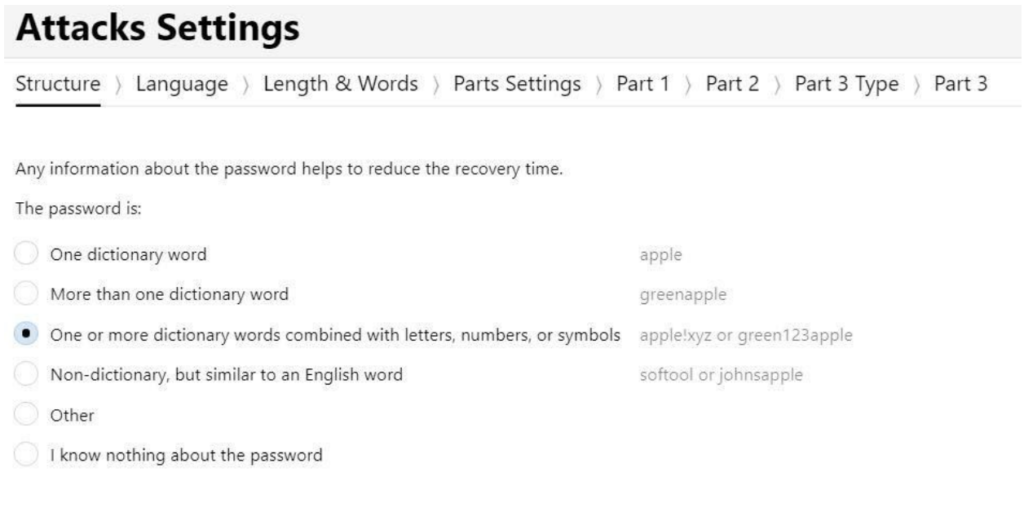
When conducting virtually all attacks on encrypted and/or password-protected disks, files, etc. in Passware Kit Forensic 2020, the options are simple. Naturally, the more you know about the password, the quicker your attack will be completed. These options (presented below) assist Passware Kit Forensic with customizing an attack on your data by constructing the quickest and most effective approach:
Mobile & Cloud Decryption
With the increasing ubiquity of out-of-the-box encryption on mobile devices and cloud-based data, the need for an approach to this challenge is ever-growing and certainly in demand. Passware Kit Forensic 2020 offers us many options with regard to this. The one we’ve used most is the iPhone (iTunes) backup. As mentioned earlier, selecting the Manifest.plist file from the iTunes backup, you can point Passware Kit Forensic at the file, set the password parameters (if known) and let ‘er rip! This is especially useful considering much of the good data isn’t currently available from a non encrypted iTunes backup.
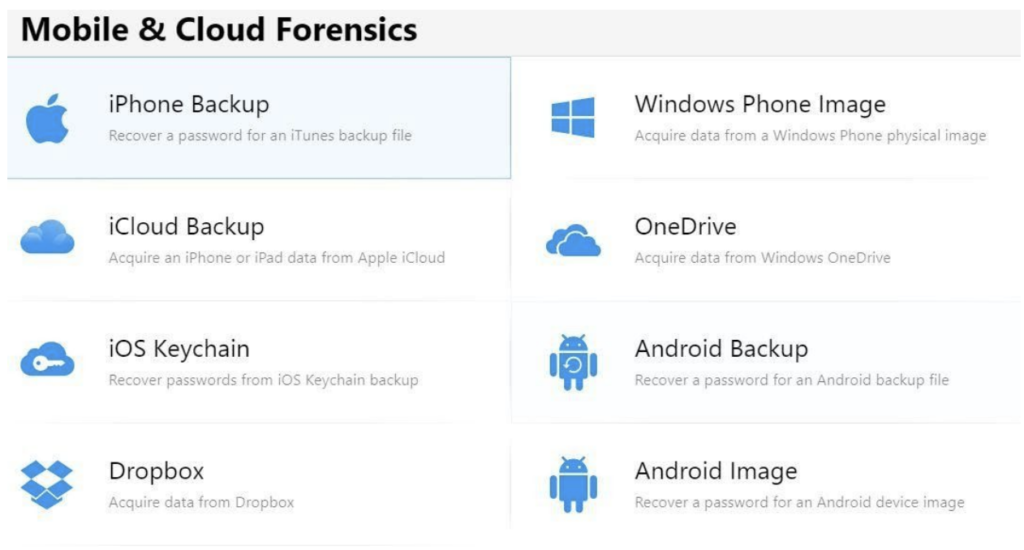
As we can see, Passware Kit Forensic also has the ability to address Android backup files, Android images, Windows phones, iOS Keychain backups and more. With the ever-increasing nature of data congruity between computer systems and their accompanying mobile devices, the usefulness of this functionality in Passware Kit Forensic 2020 is clear.
Conclusion
There are very few tools available to forensic examiners that address the sheer number of password-protected or encryption issues that Passware Kit Forensic 2020 does. Simply stated, it’s a virtually universal solution for addressing these issues and does so in a very intuitive and simple way and on multiple platforms. Naturally, the more “guts” your computer has and the more you know about any given password involved in your case, the more the efficiency of Passware Kit Forensic 2020 will be increased, but at a price point of $1,095.00 USD, it’s hard to pass up Passware Kit Forensic 2020 as a must-have tool in your forensic toolbox.















