Background
I have often heard RegRipper mentioned on forums and websites and how it was supposed to make examining event logs, registry files and other similar files a breeze (the event logs and the other files isn’t per say examined by RegRipper, but they will be used for creating timelines further on in this post with tools also developed by RegRippers author). RegRipper is developed and maintained by Harlan Carvey, who is the author of several blogs, numerous books and tools, and is also very active in the forensic community in general.
RegRipper is a tool that can be used to quickly extract values of interest from within the registry. It is NOT a registry browser. You do not get the option to browse through the registry. That can quickly overwhelm any analyst.
Instead it extracts only values of potential interest and presents it in a document for easier reading. This does not mean that you will be presented with the smoking gun right off the bat. You will still have to read a lot of material. But you will have significantly reduced what to look through.
RegRipper consists of a framework that executes plugins. Just select the plugins that extract the information you need and you are ready to go. If you need to extract something which there is no plug-in for, you can always write your own. I will not show you how to write your own plugins in this guide though. You will be presented with RegRipper and a program called auto_rip.exe, which is a program that has evolved from RegRipper and fires off a predefined number of plugins.
Once you are familiar with RegRipper and auto_rip, I will show you how to use additional programs to create timelines.
My RegRipper experience
I downloaded a copy of RegRipper in the past and tried it out. The learning curve is quite steep so I quickly found other things to focus my energy on. So instead I started writing EnScripts and C# programs that extracted the information for me.
The problem was that the programs I made, only took out the information I found important (and knew about). With RegRipper you have a whole community writing plugins, so chances are that someone, somewhere, has written a plugin that does what you want.
Still, although I planned to get around to use my spare time to finally figure out how it worked, something always came up. So I never got round to it. I just finished reading the book Windows Forensic Analysis Toolkit, Fourth Edition: Advanced Analysis Techniques for Windows 8 (worth a read for sure!), which is written by Harlan Carvey. Throughout the book he mentions the use of RegRipper. It’s not an advert for RegRipper, and you will still learn a lot if you don’t use the program, but it will sure make things a whole lot easier if you do. So I decided to try it out again, because I could see the potential gain I’d have in using RegRipper.
As I wrote earlier there is a huge community out there writing plugins for RegRipper. Be careful, though, to understand what the plugin does. The plugin may be flawed or the formats may have changed. I’m not saying there is a big risk of it being flawed, but the risk is still there. If you do not know what the program does it will be you who gets fried in court. You can’t just state that you pulled out the smoking gun without knowing how or where the program finds it. In my opinion tools like IEF should only be used as a big net that you cast in order to give you a rough idea of where to focus your investigation.
Often I see people take the evidence presented by various tools at face value and, for instance, say to themselves that there is nothing to be found if these tools doesn’t find anything. This is a recipe for disaster, since programs like that are limited by the fact that they look for specific artifacts. No matter how many artifacts a given piece of software holds, the program cannot figure out if some program changes its registry settings and decides to change the format in which they store chat and messages.
I will provide links and step-by-step instructions on the installation, use and how to incorporation of RegRipper into your own exams, without having to be able to program Perl, install Active Perl or use Linux, as these things may be distracting. I will point out the mistakes I have made, or mistakes I can see will be made frequently by others, in boxes throughout this guide.
The boxes will contain tips and will look like this one:
Luckily Harlan has also realized that not all people are familiar with perl, so he has provided most of the Perl programs as standalone .exe files (Compiled with perl2exe), that can be executed on Windows without any modification to your system whatsoever.
Tools exist, such as auto_rip, also an .exe file, which executes a whole series of plugins. This will make it a whole lot easier. But you’d need to be aware of these tools’ existence and how to use them in order to make use of them. This is what I feel is missing: a guide for the beginner. So this should take you through the whole process step by step. If you are used to RegRipper you might find this trivial, but as I stated earlier, this is aimed at those who wouldn’t otherwise get around to trying RegRipper. The following guide will focus on non XP systems since there are different versions of RegRipper for pre- and post XP. But if you need to use it on an XP system this guide should be useful as a starting point.
Prerequisite files
The following will include a number of downloads that you cannot download through Chrome, which categorizes them as potentially dangerous software. Firefox or another browser should be used to download the files. I will skip past Perl and Linux commands and assume that you will be using the compiled executable files on a Windows system. In order to start you should download several files, so let’s begin with that.
Downloads
- EDIT! The latest place where you can download RegRipper and the newest plugins is apparently https://github.com/keydet89/RegRipper2.8. Lets hope that this it stays in this place this time and new versions doesn’t start showing up other places. Thanks Jamie!
Download the latest RegRipper plugins available here (plugins20140414.zip). This will also contain a copy of RegRipper, so there is no need to download the RegRipper without the plugins. Take care to download them from the proper site; there are several websites posing as authentic.
RegRipper is in dire need of a central place where you can download it along with plugins and related tools. As it is now it’s RegRipper.wordpress.com, but there are also downloads on windowsir.blogspot.com, https://code.google.com/p/regripper/downloads/list and probably other places as well. As it is now, they often come in various dropbox links, which are placed in different posts that aren’t really searchable through Google, so you have to know where to look.- Download the wrapper script “autorip_08-26-13.zip” from this link. You’ll probably notice that the link also contains a version of RegRipper, but it doesn’t contain any plugins, so no need to download RegRipper from there. The auto_rip is developed by Corey Harrell of JourneyIntoIR.
EDIT! It turns out that auto_rips newest version can be downloaded from here. Unfortunately it is a perl script and hasn’t been compiled using Perl2Exe. And since Perl2Exe isn’t a part of this turorial you have to sort that one out yourself if you want the newest version.
- You will also need The Sleuth Kit®, since we will use some of the tools included later on. You can download it from here. Make sure you download the latest version (currently 4.1.3). The Sleuth Kit® is an open source digital investigation tool that is mostly command line based. From the same site you will also download Autopsy® which is a graphical interface to The Sleuth Kit and other tools. We will not use Autopsy® in this guide.
- On top of that you need to download some tools that greatly enhance the functionality of RegRipper and help to create timelines. I have been in contact with Harlan and he has given be permission to link to the materials he ships with his book, Windows Forensic Analysis Toolkit. Download here.
- Download the latest version of FTK® Imager from AccessData from here. FTK® Imager is a free data preview and imaging tool.
You should now have downloaded:
- rr_20140414.zip
- wfa4e.zip
- autorip_08-26-13.zip (Or higher version)
- sleuthkit-4.1.3-win32.zip (Or higher version)
- AccessData FTK Imager3-2-0.exe (Or higher version)
As you can see there is no central place where all the files are stored. On top of that most of the zip files contain several files we will be using. But don’t worry. You will be guided all the way.
I’ll walk you through the contents of the files. Many of the downloaded files contain several different tools, and we won’t be using all of them. In those cases I’ll only describe the files that are relevant to us in this tutorial.
I’ll describe all of the files in the first zip file though:
rr_20140414.zip
Let’s begin by unzipping rr_20140414.zip. This can be done using 7-zip (links to .exe file download). Unzip it to a place that you can remember.
Once extracted you’ll see something like this:
There are a lot Perl files (the .pl files). Just disregard those. rr.exe is the compiled version of rr.pl and so forth. Starting from the top (ignoring .pl files) you’ll see:
| Filename | Description |
|---|---|
| plugins | Which is a directory containing all the plugin files used by RegRipper. I will not describe each plugin within this directory, but you can see the description of each plugin if you use pb.exe (described later) |
| faq | Which is the frequently asked questions. Since there is no extension (a Linux thing) it will not open just by double clicking it. you’ll need to right click it and select “Open with”, and then select a text editor like notepad. |
| license.txt | The license terms. |
| p2x5124.dll | A dll file used when compiling perl scripts to executables. This file is required and needs to be in the same directory as the exe files. |
| pb.exe | The graphical plugin browser. Double click and point to the ‘plugins’ directory, and you will be able to see a very brief description of what the plugin does. This can also be used to create new plugins with. We will not be using it in this tutorial. |
| regrip.bat | A batch file that as far as I can tell isn’t used anymore. It used to be mentioned in Carvey’s books, but has since vanished (presumably because it has been deprecated due to auto_rip.exe, which we will discuss later on). Edit this to execute several of the exe files in one go. We will not be using this in this guide. |
| Regripper.pdf | A quick overview of RegRipper. You should use this later as it contains important information. But for the time being I would leave it be. It also gives an overview of some of the files included in the package, but not all. |
| rip.exe | A command line utility that is used, for instance, to run a single plugin against a hive file. We will discuss the use of this later. |
| rr.exe | This is RegRipper itself. It is a GUI (Graphical User Interface) based program that allows you to run a set number of plugins against a hive file. We will be discussing the use if this later. |
| updates.txt | A changelog. |
Note: Do not remove any of the files from the directory.
It is important that you unzip it to a place you can remember and not a temporary location, since we will be unzipping all other downloaded tools to this directory.
The folder you just specified is the folder we will be using for all the files in this tutorial and will hereafter be referred to as the Tools folder. You should also create a ‘Report‘ folder at this point.
You can run RegRipper and all the other files from separate directories, and most of the files can even be executed from a usb stick. But for the sake of simplicity we’ll extract all the files into the Tools folder.
wfa4e.zip
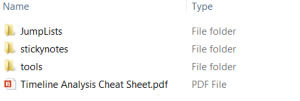
Double click the zip archive. Once opened you will see 7 folders all called starting with ‘ch’. The names are references to the book. We will be needing files from ch7, so open that folder. You will see something like that looks like the image below:
You will need to enter the ‘tools’ directory. The Jumplists and stickynotes directories contain tools designed to parse Jumplists and stickynotes, and the pdf is also self explanatory. We will not be using these files, so don’t worry about them.
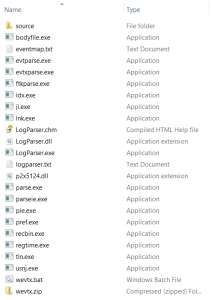
Open the ‘tools’ directory and you’ll be greeted by something that looks similar to the image below:
We will be using some of these files later on. So a detailed description of each will just add to the confusion. For now just unzip the files to the Tools folder.
Do NOT create sub directories but unzip/copy the files directly into the root of the folder. Overwrite any existing files and accept any prompts that require you to be administrator (User Account Control box).
autorip_08-26-13.zip (Or newer)
Auto_rip is a wrapper script for RegRipper and simplifies the use of RegRipper since it executes a number of preconfigured RegRipper scripts in one go. More on this later.
Unzip the contents of this archive into the Tools folder. Remember: No subfolders!.
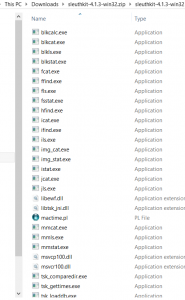
sleuthkit-4.1.3-win32.zip (Or higher version)
The Sleuth Kit is a full blown open source forensic tool like EnCase or X-Ways. We will not be using it in full. Instead we will be using two command line tools: mmls.exe and fls.exe. Double click the zip archive and navigate to the ‘sleuthkit-4.1.3-win32.zip\sleuthkit-4.1.3-win32\bin’ folder and you’ll see something like this:
The two executables we will be using rely on other dll files to function properly. So instead of just taking a few files, we will take all content of a directory. This will mean you will get a lot of files we have no use for. But for the sake of simplicity you should take the contents of the ‘bin’ directory and extract them into the Tools folder.
AccessData FTK Imager3-2-0.exe (or higher version)
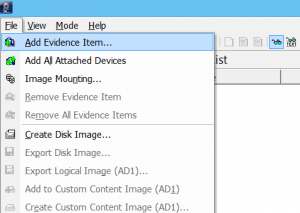
This tool must be installed on your computer. We will be using this to extract files and read image files. So double click the executable and follow the on-screen instructions to install it.
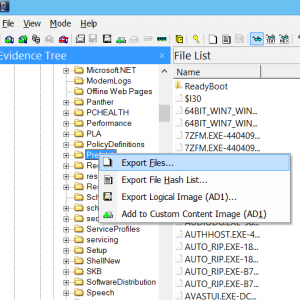
Start the program and you should see something similar to the below image:
You can close the program for now.
Got that? Great. If you followed at the steps I have described so far, you should now be ready to actually use the programs. We’ll look at this next.
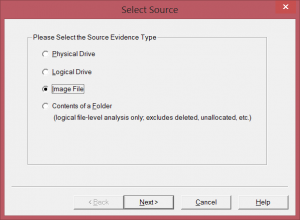
Exporting the files for use with RegRipper
I’ll start with showing you how to extract the files you’ll be needing from an image of a computer. You could opt to extract them from your own machine, but for this tutorial I’ll use an image of a Windows 7.
I will extract all the files we’ll need throughout the entire tutorial now. We will not be needing them all just yet, but I find that it is easier and brings less confusion to get all the files in one go instead of having to go back and repeat these steps each time you want to examine something new. The list of files we will extract is not complete. There are many more files you can extract and use in your examinations. I’ll just focus on the ones that best illustrate the principal of using RegRipper and give a quick result. Even though we will be extracting all the files in one go, I’ll be sure to let you know which files we will be using.
If you want to know how to create an image of a computer using FTK Imager you should check this.
Once you have the image you should complete the following steps:
That should give you all the files we will use in this tutorial. As I told you earlier, there are many more files you could use when examining a system. A few of these could be the Recent folder along with .lnk files and jumplist from a user, setupapi.dev.log, the webcachev01.dat, windows.edb, application log files and many more But this will do to begin with.
Have you followed the steps described?
You should now have extracted:
- The operating system registry hives: sam, security, system, software.
- The user registry hives NTuser.dat and UserClass.dat.
- The Windows\Prefetch\ folder
- The Windows Event files from: Windows\System32\winevt\logs\
As you can see, there are quite a lot of steps you need to take before you can actually get to use the program. But once you have done it a few times you should be able to do it quite quickly, as you do not have to download and install the programs each time you use it.
Granted: You could have gotten it over with quicker. You could have settled for downloading RegRipper and auto_rip and then only used those against the registry hives. But the extra tools and the timeline we will be building later will make your examination much more powerful and useful.
Using RegRipper
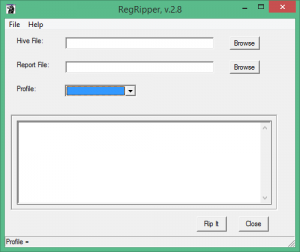
Navigate to the directory that contains the RegRipper executable, rr.exe, and start it. A GUI should now appear:
This is RegRipper. Let’s start by examining the files that you just extracted, containing information about the operating system.
Press the button labelled ‘Browse’ to the right of ‘Hive file’. In the dialog that appears, you should navigate to the directory containing the system file.
Specify where you want the output to be placed in Report file. You should make a folder for all your reports.
Select System from the drop-down menu labelled Profile.
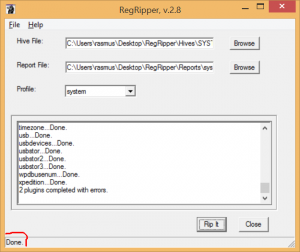
If you have completed the steps above, you should now be ready to press the button labelled ‘Rip it’.
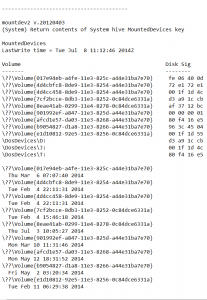
After this is done, you can view the extracted information in the text document that you specified in the Report file. Both a *.txt and *.log file will be present in the output directory. The *.log contains the log of what RegRipper has done and the *.txt contains the actual output. The output contains a lot of information that you will probably never need. But if you look through the report, you will find that there is much useful information to be seen:
The above screenshot shows an excerpt of the output. RegRipper lists all drives attached to the system and displays their disk signatures. It also shows the last time the drives were connected. (There can be several entries referring to the same volume).
Now it is just a matter of finding the information that you need.
Try and parse the extracted UserClass.dat.
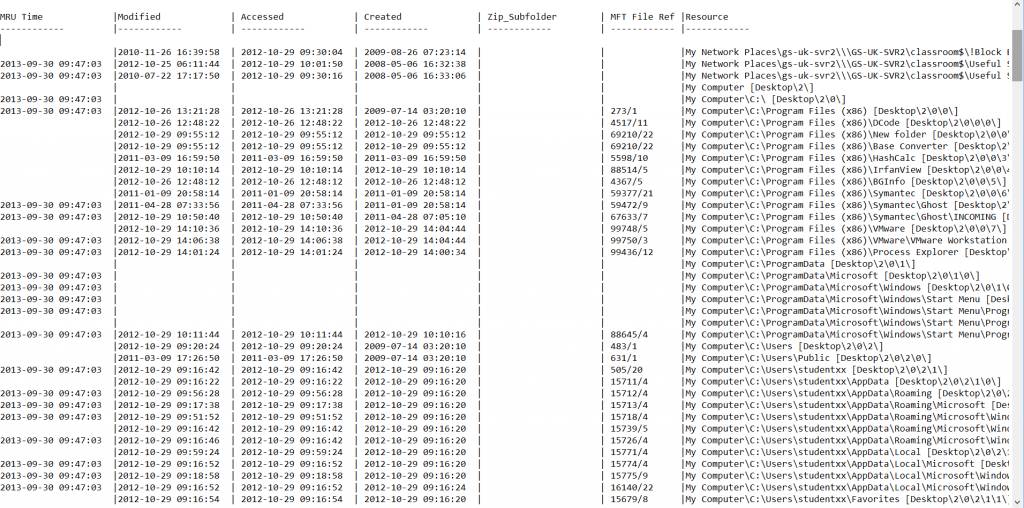
I would like to highlight a part of the UsrClass output, which is shown above. The image displays the ShellBag parsing, which contains folder names along with last access time. Very useful!
Now it is just a matter of doing the same thing for all the extracted registry files. This can be useful in many cases where you just want a specific plugin run, or you want information the next one doesn’t display.
Play around with RegRipper, examine the various profiles included, and get familiar with the output.
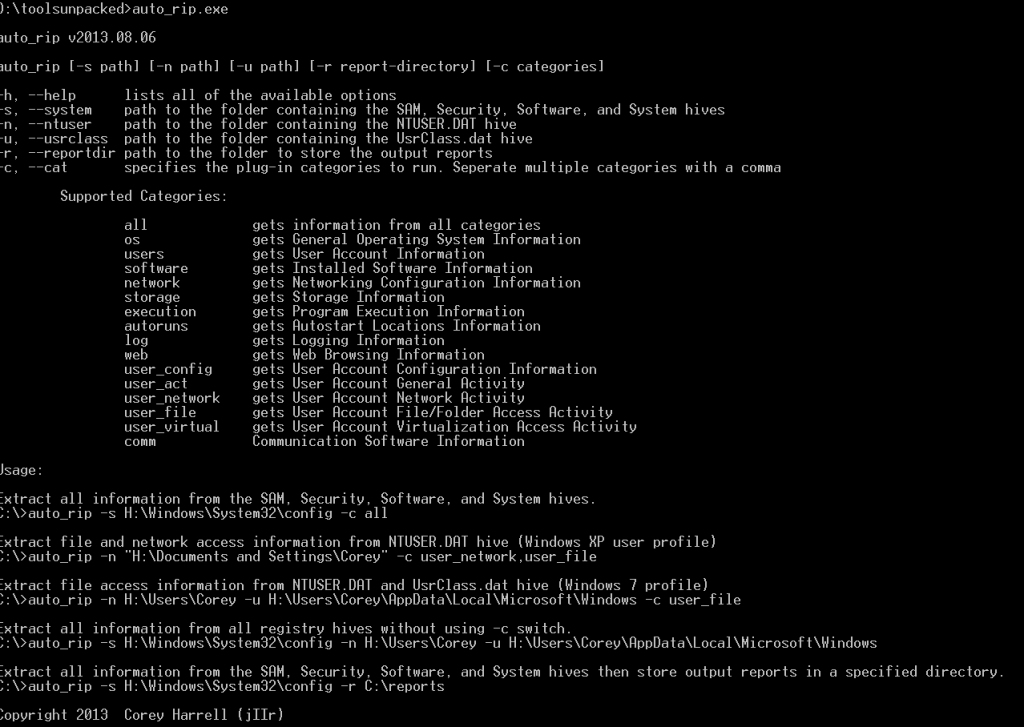
How to use the wrapper script: auto_rip
You have now used RegRipper and seen what information you can get using it. Pretty impressive, right? But if you are anything like me you feel that it is a bit repetitive to have to open RegRipper, select the input file, the report file and then select the profile.For a full examination you will have to do this quite a few times. Normally an incident response person will only want to look at a very specific part of the registry, and will use rr.exe for this. But if you would like to do a full examination of the computer, the above-mentioned procedure will involve a lot of repetitive steps.
This is where the wrapper script auto_rip comes to the rescue. Auto_rip is a wrapper script for RegRipper developed by Corey Harrell. It fires off a set number of plugins which will give you a quick overview of the system. It is command line based, but if you can get past this, it really speeds things up. Open your command prompt and navigate to the Tools folder. If you write auto_rip.exe you will be presented with a help text, where you can see several different options:
So. If you followed my instructions and copied all the hives, you should be able to run write:
auto_rip.exe -s [Full path to sam, software, security, system] -n [full path to ntuser.dat] -u [full path to UsrClass.dat] -r [full path to your output folder]
Example:
auto_rip.exe -s “C:\Users\rasmus\Google Drev\hives” -n “C:\Users\rasmus\Google Drive\hives” -u “C:\Users\rasmus\Google Drive\hives” -r C:\Users\rasmus\Desktop\RegRipper\Reports
When you are done, you should have 16 different report *.txt files in your Report folder which each contain a different category such as 14_user-account-file-access-activity.txt.
I will not explain the output in the reports or what the different values mean. This is beyond the scope of this guide. But look through the reports and see what can be discovered by just running a few commands.
The guide could stop here. But Harlan Carvey has developed quite a few other tools, which I will describe on the following pages. Read on to see how to use these tools to make timelines using event logs, prefetch, registry, file times and more.
Using the extracted files to build a timeline
RegRipper is a great tool and it gives a lot of information to the investigator to look through. But what if you don’t know what to look for or just need to see which files and processes have been in use at a particular time?
Of course you can just look at file timestamps, but if you stop here, you will miss out on a lot of information.
Apart from RegRipper, Harlan has developed a system for creating a timeline (normally referred to as TLN format). The system can be described as:
Time|Source|System|User|Description
Which translated means:
Time of event execution|Source of event|System on which the event happened|The user that made the event|A description of the event
There is much more on the subject in the book, so I will not give a detailed explanation here. There are timestamps to be found in numerous places other than just the file’s timestamps. These include – but are not limited to – the times embedded in the prefetch files, the event logs, and the lastwrite time on each individual registry key. These are all timestamps that you can use in your timeline and that we will be using in the remainder of the guide.
The files used in this guide are not exhaustive though. There are timestamps in jumplists and $UsnJrnl – to name a few – that could be useful. But to keep it simple we will only use the files extracted earlier. That way you can always add new timestamps later.
Without further ado, let’s begin building our timeline. I will be using the same image of a Windows 7. Some of the screenshots may differ from each other, but that is because I originally started making this tutorial on a Windows 8, before switching over to a Windows 7 instead.
The following will give you an idea of how to make a timeline. It only covers the basics and is a step by step guide without much description for each step. If you really want to get serious about building timelines you should buy Harlan’s book, which goes into this in much more detail.
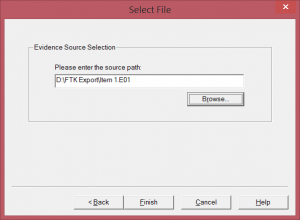
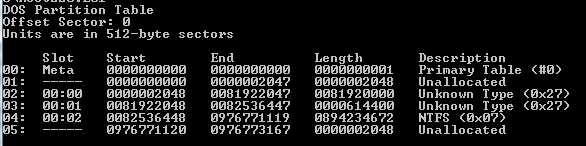
The first thing we need to do is to see what partitions are on the hard drive and extract the timestamps to create a bodyfile.txt. This is done using The Sleuth Kit’s command line tool mmls.exe and fls.exe.
First. Open cmd.exe and navigate to where you downloaded the files earlier. If you followed my instructions you should have all the downloaded files in one folder. This directory will hereafter be referred to as the tools folder.
Type:
mmls -t dos -i ewf [Path to the first e01 file]
Example:
mmls -t dos -i ewt D:\FTK Export\
If you do not use an E01 image or you just want to see what options are available, write mmls and read the help text.
You should end up with the following:
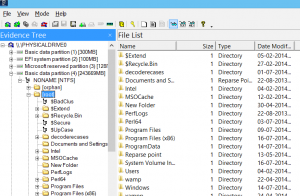
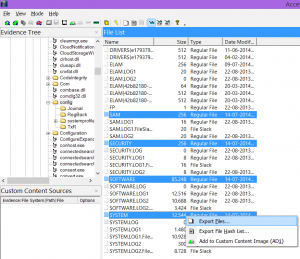
You’ll want the partition on which the Windows installation resides. Look at it in FTK Imager and find out which partition has the Windows and Users folders.
Knowing the offset to your partition, you can build the bodyfile.txt using fls.exe by writing:
fls.exe -i ewf -o [Offset to your partition] -f ntfs -r -p -m [Drive letter you want to assign preceded by a forward slash] [path to image] > bodyfile.txt
Example:
fls -i ewf -o 82536448 -f ntfs -r -p -m c:/ “D:\FTK Export\Item1.E01” > bodyfile.txt
This command will result in a file called bodyfile.txt being created in the directory where fls.exe resides. It is possible to make the output show the times in local times, but this output is in GMT since the tools we will be using later on do not provide this functionality.
Move the bodyfile.txt to your Report directory for easy access later on.
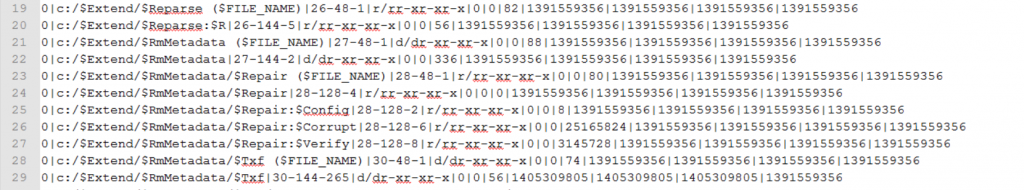
If you open up the bodyfile.txt you will see something like this:
You don’t have to worry about the output now. It is a series of paths, unix timestamps and more. We will have to convert the output into a format we can use to build our timeline (TLN, remember?).
If you know the machine’s name, you should take a note of that (it should be in the auto_rip reports that you generated earlier). This value should be used in the following instead of [Server].
If you do not know the name you can always fire off the following (while in the Tools folder):
rip -r “[path to system hive]” -f system > [path to your report folder]\os.txt
Example:
rip -r “C:\Users\rasmus\Google Drev\hives\system” -f system > D:\FTK export\Reports\os.txt
After the plugin has finished you should open os.txt can look for the text compname. It should look something like this:
—————————————-
compname v.20090727
(System) Gets ComputerName and Hostname values from System hive
ComputerName = WKS26A03
TCP/IP Hostname = WKS26A03
—————————————-
Take a note of the name as you should use this next.
In order to transform bodyfile.txt to a format we can use, you should navigate to the Tools folder and write:
bodyfile.exe -f [path to your bodyfile.txt] -s [Server] > [path to your report folder]\FileEvents_TLN.txt
Example:
bodyfile.exe -f D:\toolsunpacked\bodyfile.txt -s WKS26A03 > “D:\FTK Export\Reports\FileEvents_TLN.txt”
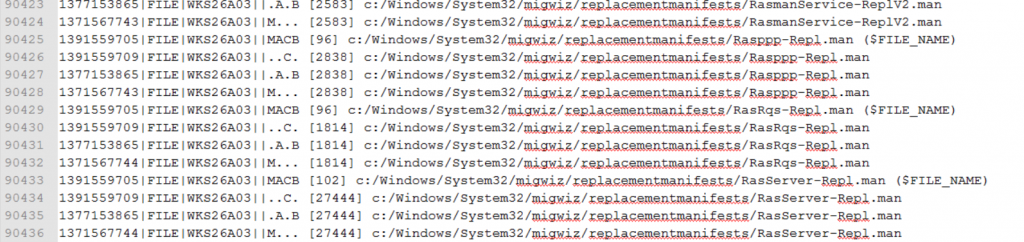
Depending on the size it could take a few seconds. Once finished your FileEvents_TLN.txt should look something like this:
Now this is not the timeline, but if you look closely you see it is formatted in the TLN format. The MACB and ..C. column stands for Modification, Access, Change and Birth. This way you can easily see what has happened to the file.
Now we have all our file timestamps formatted in TLN format. Let’s continue to extract information from the event logs.
Event logs
The following only applies to *.evtx logs which emerged post XP. XP event logs (*.evt) can also be parsed, but you need to process them with a different tool. The process can be found in Harlan’s book, but since I so rarely encounter these I will only show the process which should be used on Vista, Windows 2008, Windows 7 and 8 systems.
There are tools available that will parse the event logs and output these in TLN format. But I find it better to use Microsoft LogParser, which you downloaded earlier (located in the folder “ch7″ within the downloaded file wfa4e.zip).
Open a command prompt and navigate to your Tools folder. Write the following command:
logparser -i:evt -o:csv “Select recordnumber, TO_UTCTIME(timegenerated), eventid, sourcename, computername, sid, strings from [Path to your exported evtx\*.evtx]”” > [Path to your report folder]\EvtxParsed.csv
Example:
logparser -i:evt -o:csv “select recordnumber, to_utctime(timegenerated), eventid, sourcename, computername, sid, strings from “C:\Users\rasmus\Desktop\Exportedhives\winevt\Logs\*.evtx”” > “D:\FTKExport\Reports\EvtxParsed.csv”
And then write:
evtxparse.exe [Path to your EvtxParsed.csv] > [Path to your Report folder]\EventLogsEvents_TLN.txt
Example:
evtxparse.exe D:\FTKExport\Reports\EvtxParsed.csv > “D:\FTK Export\Reports\EventLogsEvents_TLN.txt”
This transforms the content inside EvtxParsed.csv into a nicely formatted TLN format.
This could be a good time to move your non TLN files from your Report folder (bodyfile.txt, EvtxParsed.csv, and perhaps os.txt).
You can specify a single event log to extract records from, for instance system.evtx. But for the sake of completeness I will parse all event logs in the folder. This will result in a lot of data for you to go through. LogParser has a problem with spaces in paths even if it is enclosed in “”. So if you get weird results, try to eliminate any whitespace in your paths.
Prefetch
Next we will focus on the exported Prefetch files (if present on the system you are examining). If the Prefetch folder was empty then just skip this step.
While in the command prompt, navigate to your Tools folder and write the following:
pref.exe -d [Path to your exported prefetch folder] -t -s [Server] > [path to your report folder]\prefetchEvents_TLN.txt
Example:
pref.exe -d C:\Users\rasmus\Desktop\Exportedhives\Prefetch -t -s WKS26A03 > D:\FTKExport\Reports\prefetchEvents_TLN.txt
As you can see, the output is put directly into the TLN format. So there is no need to do anything else with this file.
Registry timeline
Finally we will parse the timestamps from the registry files. I have opted to parse all the registry hives. In a normal examination you will probably want to add each hive individually. Otherwise you can easily lose track of the gigantic timeline you will end up with. But as stated previously I have opted to take them all for the sake of completeness. Then you can allways pick and choose which hives you’ll want to parse.
In order to parse the hives, you must again go to your command prompt and navigate to your Tools folder. You will have to parse each hive individually. But I have the commands here, so you can just adjust the paths and then cut and paste.
The commands are:
System hive:
regtime -m HKLM/System -r [Path to system hive]\system -s [Server] >> [Path to report folder]\regEvents_TLN.txt
NTUser.dat
regtime -m HKEY_USER -r [Path to NTUser.dat]\ntuser.dat -s [Server] -u [User] >> [Path to report folder]\regEvents_TLN.txt
UsrClass.dat
regtime -m HKEY_USER -r [Path to UsrClass.dat]\UsrClass.dat -s [Server] -u [User] >> [Path to report folder]\regEvents_TLN.txt
Software
regtime -m HKLM/Software -r [Path to software hive]\software -s [Server] >> [Path to report folder]\regEvents_TLN.txt
The HKEY_USER, HKLM/Software and HKLM/System shows regtime.exe which hive to parse.
Example
regtime.exe -m HKEY_USER -r C:\Users\wrx15911\Desktop\Exportedhives\ntuser.dat -s WKS26A03 -u wrx15911 >> C:\Users\wrx15911\Desktop\reports\regEvents_TLN.txt
The output is already formatted in the TLN format. So no further parsing is necessary.
Parsing all the TLN reports into a single events_all.txt
We finally have got the data we need. But we have several reports. We could have opted to use the >> operator and parsed all the TLN reports into a single big TLN. But here in the beginning I believe it is better to make individual reports, thus eliminating the risk of you accidentally overwriting a report and having to start over.
Open a command prompt and navigate to your Report folder. Enter the following command:
copy *_TLN.txt events_all.txt
There. You should now have a single file, which contains the contents of all your TLN files.
Single events
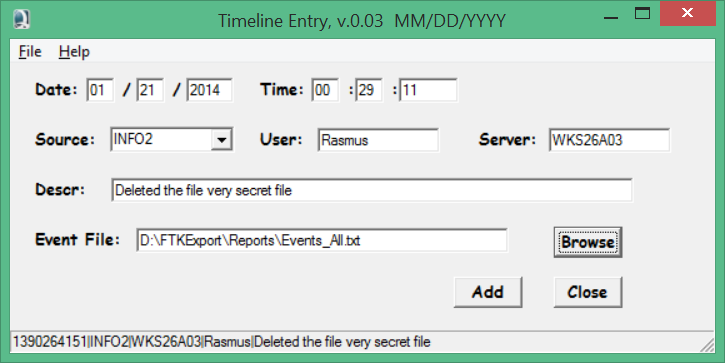
Sometimes you need to have a single event entered, so as to see how it correlates to the other events that have happened on the system. Luckily you can do this easily by using the program tln.exe, which should be in your Tools folder:
Enter the date and time (In UTC), the source of the event (i.e. where it originates. In the image above it is INFO2), a description and the resulting Events_All.txt that you want to add info to.
The above configuration will enter the below text into the timeline:
1390264151|INFO2|WKS26A03|Rasmus|Deleted the file very secret file
This is quite complex. So take a minute to play around with it and don’t read on until you are sure you have understood it all.
Building the actual timeline
When you have all the events parsed into the events_all.txt, you are ready to begin building your timeline.
You do this by again navigating to your Tools folder and writing the command:
parse.exe -f [path to your Events_all.txt] > [Path to your report folder]\TimeLine.txt
Example
parse.exe -f D:\FTKExport\Reports\Events_all.txt > D:\FTKExport\Reports\TimeLine.txt
And you should now have your brand new timeline. Look through it and notice how all the events are grouped according to the time at which they occurred. This is a nice way to see what has happened on the system.
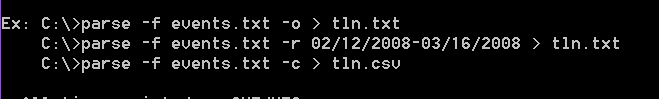
This can be very cumbersome to look through. Fortunately there is an option in parse.exe to parse out all events within a given time frame. There are a few issues though.
The date input syntax according to the help screen is:
Clearly the time format is: MM/DD/YYYY.
However, the error message associated with the dates input is:
I tried to parse it in both formats. I finally figured out that the only accepted format is MM/DD/YYYY.
To parse out events in a given time frame you should go to your Tools folder and type:
parse.exe -f [path to events_all.txt] -r [date in MM/DD/YYYY]-[MM/DD/YYYY] > TimeLineShort.txt
Example:
parse.exe -f D:\FTKExport\Reports\events_all.txt -r 1/12/2013-31/12/2014 D:\FTKExport\Reports\TimeLineShort.txt
This will return all the events that occurred in December 2013. It can still be a lot of events, but at least you will have reduced your data set significantly.
Remember, that even though there can be a LOT of events happening, this isn’t the whole story. As described previously there are many other places to get timestamps from. The JumpLists are one of the more notable.
In conclusion
I have in this guide tried to give you a glimpse into RegRipper and Timeline building. This guide isn’t meant to make you an expert in these subjects. It is just meant to get you started. There are a lot more possibilities and options you can explore.
As I have stated several times throughout this guide, you should buy Harlan’s book if you want to explore RegRipper and timeline building extensively.
Acknowledgments
I would like to thank my colleague, Bárður Christiansen, for proofreading this post prior to the release and for giving ideas for improvements (and for finding some typos in my example queries).
If you have any thoughts on the above or the guide in general, don’t hesitate to post them in the comment.
Hsppy ripping!









What if you want to examine a remote machine. How would you image it?
I would use EnCase with the network ServLet. Run the ServLet on the remote machine and then access it remotely..
Also, I guess, if I was to update the links here, I’d be using https://github.com/keydet89/RegRipper2.8
Thanks. I’ll try and change it. Thanks!
Last night I downloaded auto_rip64, placed the script auto_rip.pl, auto_rip64.exe in the folder with rip.pl and rip.exe, ran this command > auto_rip64.exe -s “c:\Backup\Champlain\Operating System Forensics\Week 1\Jane Dough” -c all
The 16 reports generated did not contain any data from the registry.
There were no errors generated from running the command.
Please let me know if this is a known issue or if I am doing something wrong.
Thanks, Pal
Hi Paul.
I don’t have access to a computer at the moment. But your command looks solid. Only thing I could think of is that you have a spaces in your path.
Try and remove the spaces (replace them with _ or similar) remove the ” and then give it a try.
Let me know how it turns out.
You could also try the -r switch to specify an output directory for your reports.