Apple recently released the newest version of their desktop operating system, Mac OS X Mavericks. As a free update to all supported Apple desktops and laptops, a wide adoption rate was expected, and in fact it was estimated that within the first 24 hours, 5.5% of all Mac laptops and desktops were already running the new operating system. It becomes necessary for a forensic examiner to understand how changes to the file metadata system can be used as a source of new evidence during an investigation. In this article, I would like to cover two significant changes to the metadata generated by OS X Mavericks that, if properly preserved, can be a useful source of evidence.
Files saved from email attachments
There is a convenient feature in OS X Mavericks, which allows you to open a document that has been saved from an email, make a change to that document (applying a signature to a PDF for example), and “Reply” to the original email from within the preview app’s share function.
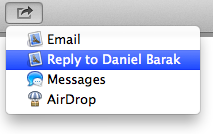
In order to accomplish this function, the operating system must maintain a link between the document resident in the file system and the email from which the document originated. In the case of OS X, the information describing this relationship is stored in the metadata of the saved attachment. Upon examination of a file’s metadata, a forensic investigator could quickly gather useful information about to the origin of the file before it was saved to the file system. For example, if the file was saved from an email message, the additional metadata in OSX Mavericks allows an examiner to identify the mail application used, the email message ID, the sender of the email message and the email subject line.
The following metadata fields are new to OS X Mavericks:
- kMDItemOriginApplicationIdentifier
- The application that the item originated in.
- Example: “com.apple.mail” for the Apple Mail App
- kMDItemOriginMessageID
- The ID number of the message in the Apple Mail App
- Example: “203245”
- kMDItemOriginSenderDisplayName
- The sender display name from the email
- Example: “John Doe”
- kMDItemOriginSenderHandle
- The sender handle from the email, often the same as the display name
- Example: “John Doe”
- kMDItemOriginSubject
- The subject line from the original email
- Example: “RE: Secret Document, DO NOT SAVE”
In the previous version of Mac OS X, Mountain Lion, some of this information was available but it was all encapsulated in one metadata field called kMDItemWhereFroms. The new structure will allow forensic tools to more easily identify the origin of files and more definitively connect a file saved to a computer back to a particular email and sender adding additional context to an otherwise “loose” file.
Files tagged with the new tagging system
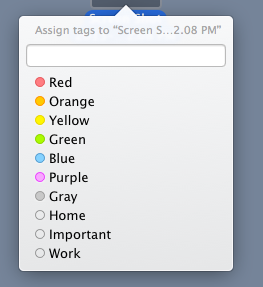
In addition to the new metadata described above, OS X Mavericks also includes a new feature that allows users to organize files in the OS through a tagging system. Right clicking on a file and selecting a “Tag” allows a user to organize files into categories.
By default these are color-based categories but can be modified to represent words. Unlike the color labels in previous versions of Mac OS X, these tags are searchable and their text can be customized. A single file can also have more than one tag associated with it. This tag information is stored in the file metadata under the field kMDItemUserTags. This new user generated metadata can be an important source of context when examining a file because it can indicate how a user chose to categorize a document. Similarly, documents can be searched and grouped by their tags in order to discover potentially related items.
The new metadata generated in Mac OS X Mavericks can be used as a critical tool in a forensic examiner’s belt, subsequently facilitating a better understanding of the context surrounding the creation and classification of a document.
Daniel Barak is the Director of Technology and Digital Forensics at Vdiscovery, a litigation support and electronic discovery service provider in New York City.






