Atola Technology has announced a major update to Insight Forensic. All existing customers can freely download and install the new 4.2 software.
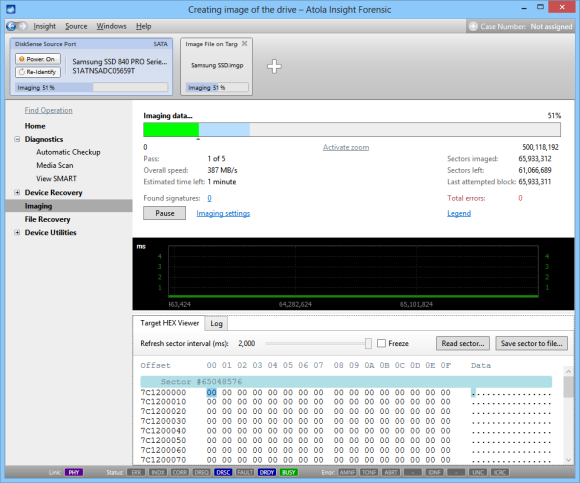
Having been asked many times by forensic experts to allow the creation of image files on target devices attached directly to an Atola DiskSense unit, this facility is now available.Image Files on Target Media
You can take a big HDD, attach it to DiskSense unit and image to the HDD creating as many image files as drive capacity allows.
Improved Performance
Insight Forensic got an overhaul of its performance. As a result almost all long-lasting operations as well as File Recovery user experience were sped up much. See the latest 4.2 benchmark.
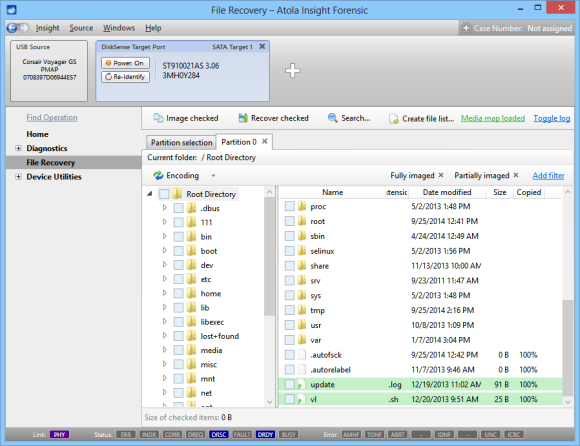
File Recovery UI
Now you can easily create file list where all cluster/sector numbers added for files. Insight 4.2 writes file list in a more compact and optimized CSV-formatted file.
File Recovery got lots of other improvements:
• New cumulative filters
• Improved look and feel
• USB device browsing and recovery performance improved up to 4 times
• ext4 partition browsing and recovery performance improved up to 3 times
• Added keyboard shortcuts and improved keyboard navigation
Other Insight Forensic 4.2 improvements, new features, bug fixes are described in the release change log: http://atola.com/products/insight/changelog.html






