One of the big focuses in Magnet Forensics‘ Internet Evidence Finder (IEF) v6.3 was adding hashing support for pictures and making it easy for investigators to import hash lists that can be used during searches to alert you of hash matches. We’ve added support for MD5, SHA-1, and the new PhotoDNA. We’ve also added support for Project Vic, an initiative to improve how investigators conduct child exploitation investigations.
Forensic investigators are well aware how common hashing algorithms such as MD5 and SHA-1 help them confirm that their forensic image is an exact copy of the original disk or volume. This assists the investigator with the image’s admissibility into court and helps maintain the integrity of the evidence.Hashing is also used as an investigative tool within the file system to help quickly identify certain known good or bad files. While metadata such as file names can be changed, any two identical files will result in the same hash value. Hash lists can be imported into forensic tools such as EnCase or FTK and then compared with the files on a given system to identify any common matches. This is an excellent technique if the investigator is looking for specific malware, intellectual property, or in child exploitation cases, illicit images.
Law enforcement agencies have been using hashing as an investigative technique for years. Hash databases of known illicit images recovered from cases are often built by agencies to help investigators quickly locate known child exploitation images. Applications/scripts such as C4All and NetClean Analyze assist with locating and categorizing/pre-categorizing (using known hashes) pictures found in a case. Investigators can categorize these illicit pictures into tiers of severity or as non-relevant, but it can be difficult to maintain and/or share these categorizations with other agencies. Project Vic is spearheaded by ICMEC and DHS and is an initiative to create a standardized, shared, central hash database that investigators can use to locate and/or categorize child exploitation images.
New in version 6.3, IEF can be used to hash all the images in a case allowing investigators to identify and categorize pictures which are known to be illicit. This new release allows hash sets to be imported into IEF to be used for identifying images and hashes of recovered pictures can be exported for use in other products. (Additionally, pictures can now be exported to a folder without needing to create a report and keeping filenames intact.)
Investigators can import their own custom hash sets or use sets obtained from other sources such as Project Vic to help speed up analysis of their evidence.
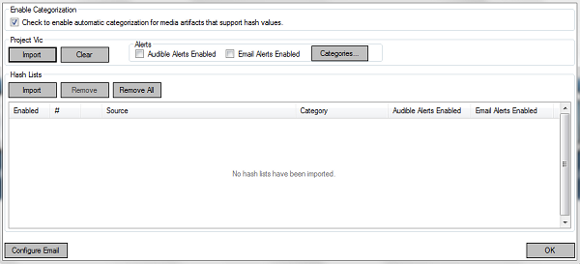
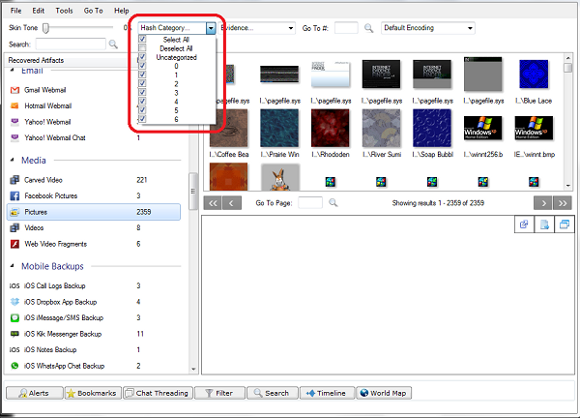
Adding hash sets in 6.3 is simple, just open the Tools menu and select Hash Sets. From here you can choose to import multiple sets either from Project Vic in XML format or any other set in a line separated text format (one hash per line). Each list can be assigned a category by the investigator to indicate/differentiate multiple categories of images. Once the search is complete, results will be displayed in the IEF Report Viewer for analysis. Investigators can choose to filter based on the category of the hashes that were imported into IEF, allowing you to quickly view only images that have been categorized or of a specific category.
Not only does IEF now calculate MD5 and SHA-1 hashes for all pictures in a case, it also incorporates new technology created by Microsoft to combat the spread of child pornography, PhotoDNA. Available for law enforcement customers, PhotoDNA is calculated much like a hash but instead of computing the value for the entire image, the photo is converted into black and white, and broken down into smaller sections. Those sections are then analyzed for gradients or edges identifying similarities between images that might not be exactly the same but share similar characteristics. This assists when comparing images of different sizes or alterations in colour. This technique is similar to how fuzzy hashing is able to distinguish similarities in other files or do*****ents by tools such as ssdeep that wouldn’t otherwise match using traditional hashing algorithms. PhotoDNA is being implemented into all of Microsoft’s cloud technology (OneDrive, Hotmail, Bing) and is also being used by the National Center for Missing & Exploited Children (NCMEC). Facebook and Twitter have licensed the technology for their online services as well.
Go to www.magnetforensics.com/photodnaregistration to request access.
Hashing is a valuable forensic tool for investigators working with large datasets that need to be scaled down and with locating and pre-categorizing child exploitation images. With the addition of picture hashing, the ability to import hash sets and export picture hash values, we hope that these new features in version 6.3 of IEF will help investigators work more quickly and efficiently with their cases and most importantly, combat child exploitation.
This demo video demonstrates how Internet Evidence Finder (IEF) v6.3 can now perform hash analysis for all the pictures in a case. Importing, exporting and categorization are all discussed and how it can improve your searches for known pictures.
To all those working in this extremely important but devastating field, we thank you for the work you do and will continue to do our best to assist you in your investigations through our software.
Please feel free to contact me with any questions/suggestions regarding these new features at jad(at)magnetforensics(dot)com.
All the best,
Jad and the Magnet Team






