Republished from the MagnetForensics.com blog by Jad Saliba, Founder & CTO of Magnet Forensics (formerly JADsoftware)
I would like to introduce a new free tool we’ve just released to the forensics community called Dropbox® Decryptor. But first, some background.
Dropbox uses a file named filecache.dbx to store details about files that have been or will be synced to the Dropbox cloud. This file used to be a SQLite database (named filecache.db) and was easily viewed in a SQLite browser. In early 2012 Dropbox released an update that encrypted this file, and hence the new filename “filecache.dbx”.In mid-January of this year, we released IEF Triage v5.8 that added support for decrypting this file on a live system. Support will be added to IEF Standard for decrypting this file on a dead box (or forensic image) in the near future, but for now we wanted to release this free tool to allow you to decrypt these files on your own. The main limitation right now is that it only currently works on files obtained from a Windows XP or Vista system due to how Dropbox does the encryption. We hope to add support for Windows 7 when this capability is put into IEF.
So, on to the tool and how to use it! You’ll need to collect the following items first:
– The filecache.dbx file (located in [root]\Documents and Settings\username\Application Data\Dropbox on XP, or [root]\Users\Jad\AppData\Roaming\Dropbox on Vista)
– The entire Protect folder for that user (located in [root]\Documents and Settings\username\Application Data\Microsoft on XP, or [root]\Users\Jad\AppData\Roaming\Microsoft on Vista)
– A file containing the raw bytes from the Dropbox “Client” value under the “ks” key in the registry/NTUSER.dat file (full path is HKEY_CURRENT_USER\Software\Dropbox\ks)
– And finally, the user’s Windows login password
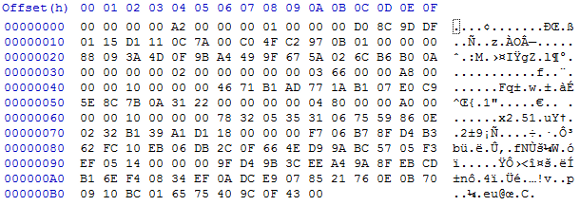
The dbx file and Protect folder are easy to grab, and you can use various registry viewers to pull out the Client value data. The file containing that data should look something like this:
Once you have those items, install and run the Dropbox Decryptor tool and point it at all the respective files or folders:
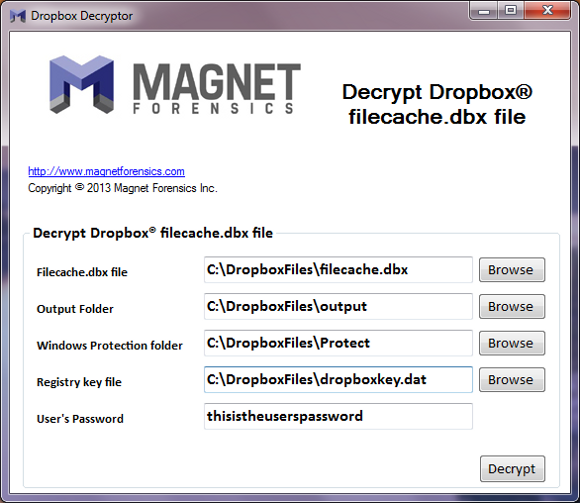
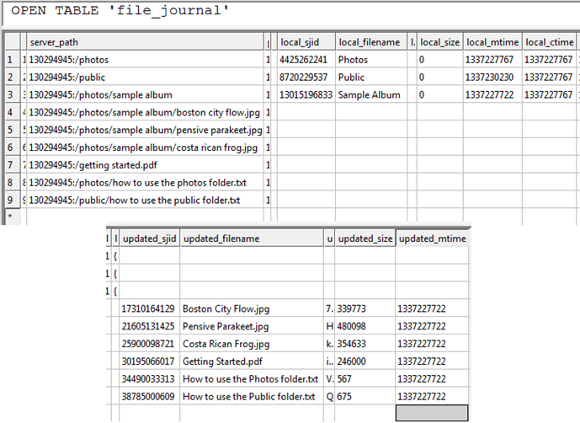
Click ‘Decrypt’ and you’ll get a filecache.db file saved in the output folder you specified which can then be opened by any SQLite browser. The ‘file_journal’ table is the one you’ll be most interested in:
TO REQUEST A DOWNLOAD of Dropbox Decryptor v1:
Please complete the form at: http://info.magnetforensics.com/dropbox-decryptor






