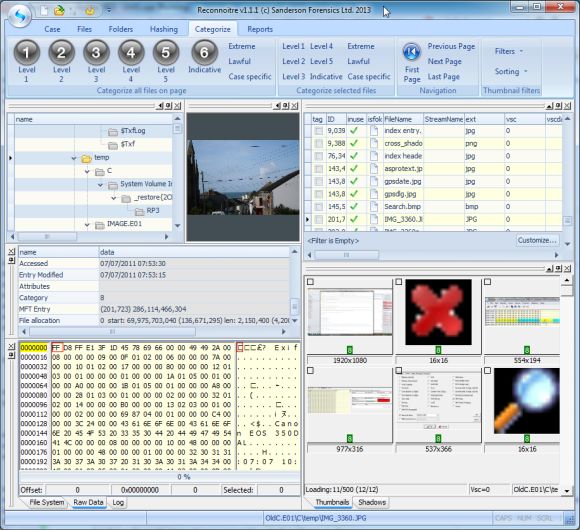
Sanderson Forensics are pleased to announce an update to our most recent software tool Reconnoitre.
Reconnoitre allows the forensic investigator to quickly and easily investigate images containing volume shadow copies, without the need to run VSSAdmin.
This latest version adds facilities that include querying a C4P hash server, import a .c4p export file and identify files that exist only in volume shadow copies.We have what seems to be an unusual policy in the forensic world rather than give our customers what we think they want, we are listening to them and trying to give them what they have asked for.
So when some of our first Reconnoitre users said “Could you get Reconnoitre to identify graphics files in volume shadow copies that have been identified by C4P as ‘somewhere in this SVI file’?”, “can Reconnoitre do a hash comparison using a C4P hash server?”, “could you add graphic file categorisation features” or “can you see just those files in shadow copies that are not present in the live files?” – we listened.
The latest version of Reconnoitre does all these things and there are plenty more enhancements planned.
You can get more information and download a demo at the link below:
http://sandersonforensics.com/forum/content.php?168-Reconnoitre
and there are some short support videos highlighting some of these features at this link:
http://sandersonforensics.com/forum/content.php?174-Reconnoitre-support-videos
This is what some of our users are saying about Reconnoitre:
• It looks as if it is going to solve that huge problem no one else seemed to want to tackle except in small segmented ways
• the UI looks like it was designed by someone who doesn’t hate his customers
• it’s flipping amazing
• paid for itself on the first job
• this is exactly the tool that we have been looking for that has been missing for our investigations
Reconnoitre – VSC processing made easy.