by Feby Thealma, CEH, CHFI
Digital forensic practitioners run the professional gamut of roles. Once an industry almost solely confined to government and law enforcement, the need for digital forensic incident response, analysis and expertise has expanded from its initial application to include a large swath of corporate needs, including incident response, eDiscovery, insider threat investigations and human resources violations, to name a few. While many digital forensic tools can deal with these ever-growing digital forensic needs on an individual basis, Magnet AXIOM Cyber from Magnet Forensics has emerged as a go-to resource for digital forensic investigators/analysts in their toolbox when dealing with this range of incidents.
The natural first step in the forensic analysis methodology is identification, documentation and collection of your evidence.
When it comes to the corporate need to collect data from remote, off-network sources or cloud-based data, AXIOM Cyber has you covered. Remote data collection in AXIOM Cyber utilizes either a stand-alone client deployed on a remote system by AXIOM Cyber or through third-party tools such as Jamf or Workspace One. Furthermore, analysts can also acquire cloud-based data such as AWS, Azure and from applications such as Microsoft 365, Slack and Teams. In the ever-evolving and growing world of tele-work, these capabilities become vital to the successful investigation and analysis of incidents within the organization.
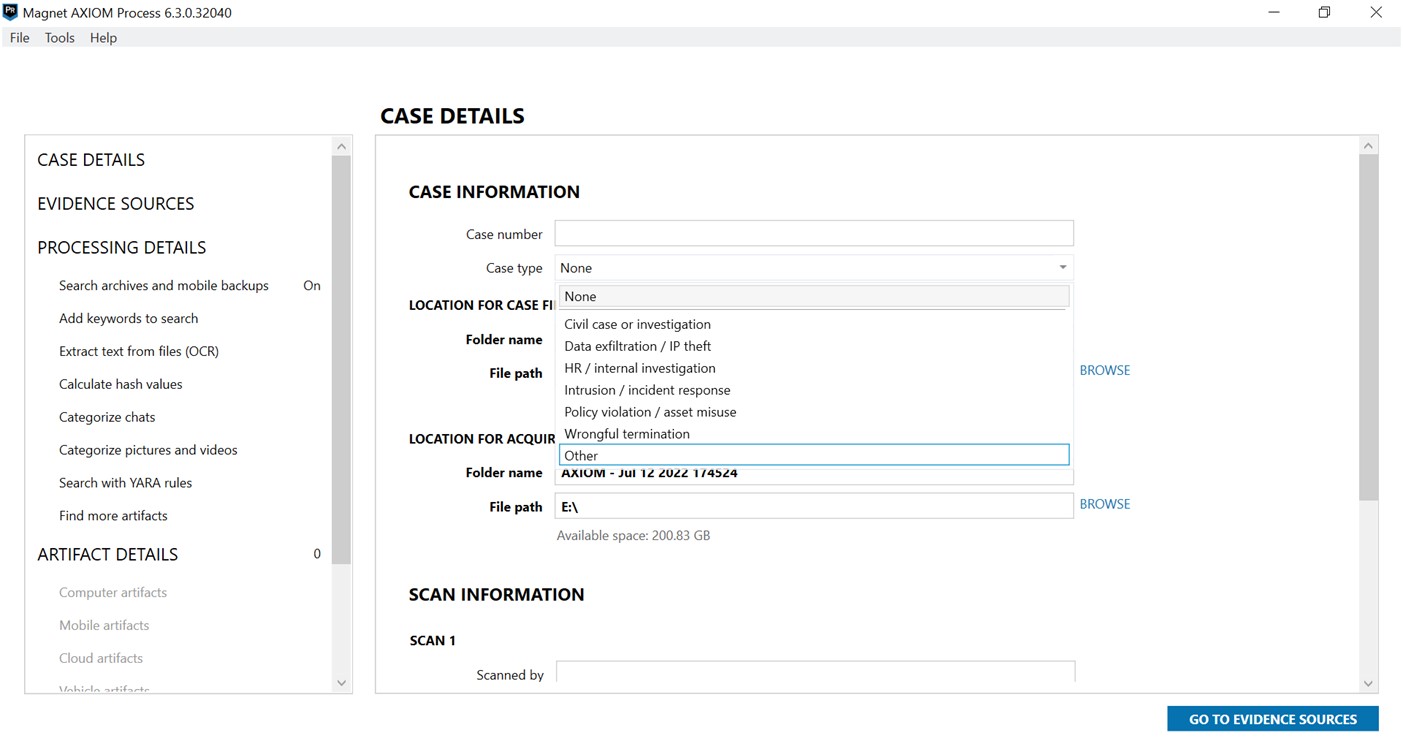
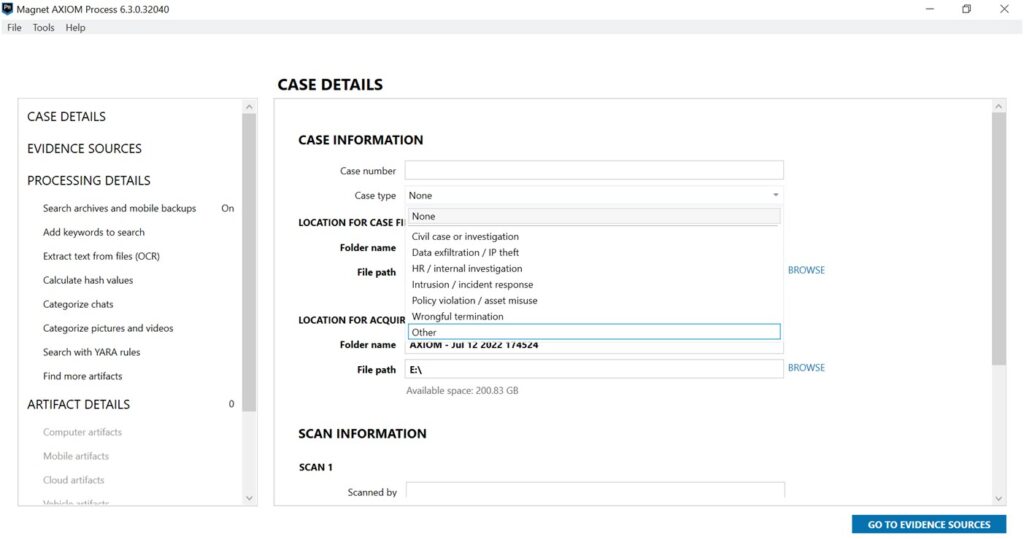
Case Initialization
The case is initialized in the Magnet AXIOM Process utility, which allows for entry of case details and selecting the evidence sources to be analyzed.
Case types such as HR/internal investigation, data exfiltration/IP theft, wrongful termination, incident response and others can be chosen to tag the case under a particular category. From case number, case types to cover logo, Magnet has understood how important case details are to digital forensic practitioners and provide plenty of opportunities to customize these details within AXIOM Cyber.
By initializing the case, it is possible for digital forensic investigators to gather all kinds of evidence from almost any source into one single case file. AXIOM Cyber organizes case files so acquired evidence and analyzed artifacts from computers, cloud storage, IoT, and mobile devices aren’t scattered across the file system.
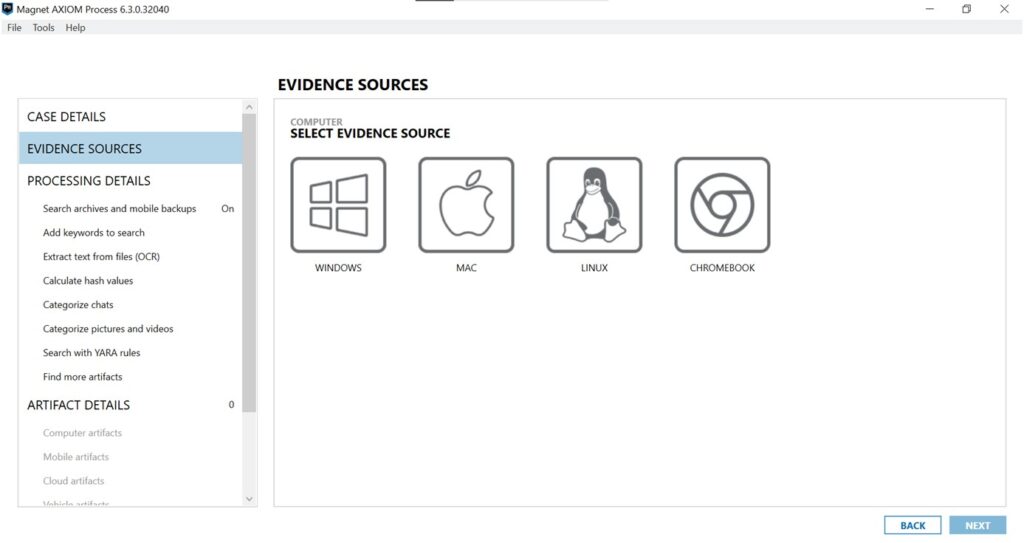
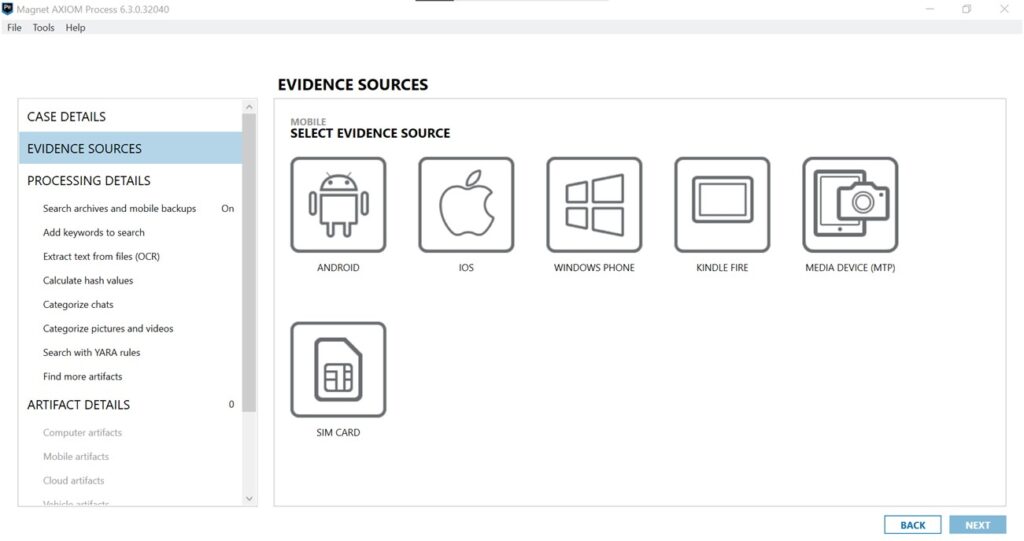
Data Collection & Processing
The computer evidence sources naturally include Windows, Mac & Linux, but also Chromebook.
Mobile offerings are universal, supporting Android, iOS, Windows phone, Kindle Fire, and media devices.
Cloud support is quite extensive for commonly used corporate communications, including Microsoft Teams, Slack, Zoom, and services such as AWS, Google Workspace, Dropbox, Microsoft and Apple, with the appropriate user or admin permissions. AXIOM Cyber is also able to collect social media sources that are available publicly (or with user account information) such as Facebook, Twitter, WhatsApp and many more, as well as service accounts such as Uber and Lyft.
Remote Data Collection
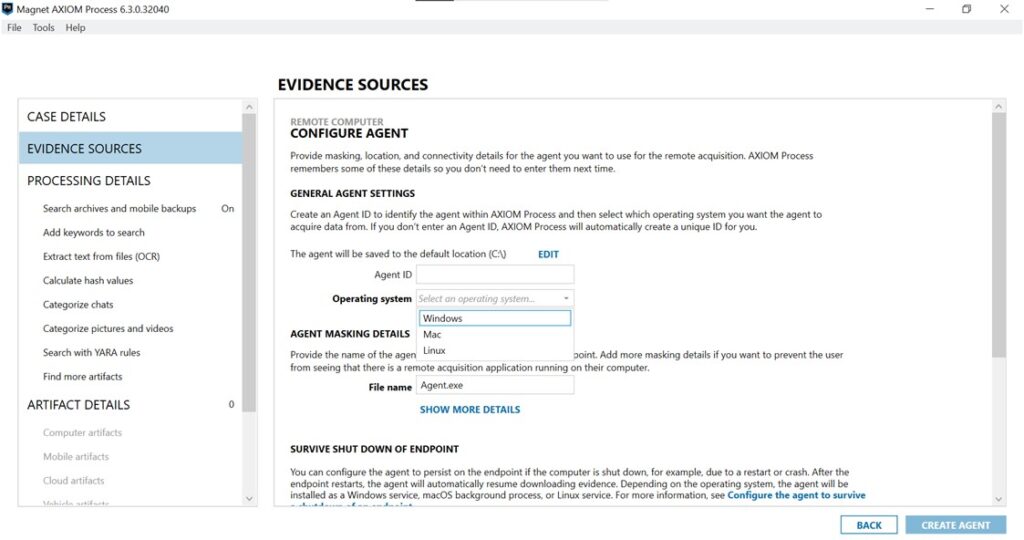
In the past few years, when performing remote data acquisition became crucial in digital forensic investigations, Magnet stayed ahead of the pack with AXIOM Cyber.
The remote collection agents are easy to create and deploy on all of the primary computer operating systems, including Windows, Mac, and Linux. Magnet also provided additional configuration on how the remote agent would behave through a device shutdown. Digital forensic practitioners are also able to see a list of created agents through the Agent Status Dashboard, which mitigates the creation of multiple agents that would have the same purpose or configuration.
When selecting processing options, several notable offerings are present. Key words can frequently be of value in corporate cases, but more notable is the ability to process files using optical character recognition (OCR) as well as YARA rules, which is a versatile and useful tool. While OCR can be used to identify characters in media, YARA rules are very valuable in a corporate setting dealing with a lot of malware cases.
An example of OCR usage is when a screenshot containing text is relevant to the case, AXIOM Cyber is able to surface the screenshot and highlight it to the investigator as potential evidence. AXIOM Cyber includes a set of common YARA rules within the platform, and investigators are also able to add new or specific rules at any time. Both tools in AXIOM Cyber provide speed and efficiency to automatically highlight case-related evidence.
Hash values of all files can be calculated, which can make analysis in an incident response environment with known threats much more streamlined.
This area is where we also would carve for any number of file types including documents, media, encryption & credentials, etc. This list can also be customized for file carving by file header, if known, which is another very useful tool in conducting incident response investigations.
When processing for artifacts, Magnet AXIOM Cyber has not only kept with the workflow that has been part of the Magnet suite of tools since Internet Evidence Finder (IEF), but enhanced, expanded and categorized the artifacts to be searched in a comprehensive list that is frankly too large to share! This list is platform-specific, so it will incorporate mobile applications, computer data, RAM and/or cloud-based data, as appropriate.
From there, we only need to tell AXIOM Process to work its proverbial magic, based upon our case-specific parameters, and the Magnet AXIOM Examine tool is automatically launched, showing our progress and results.
Data Analysis
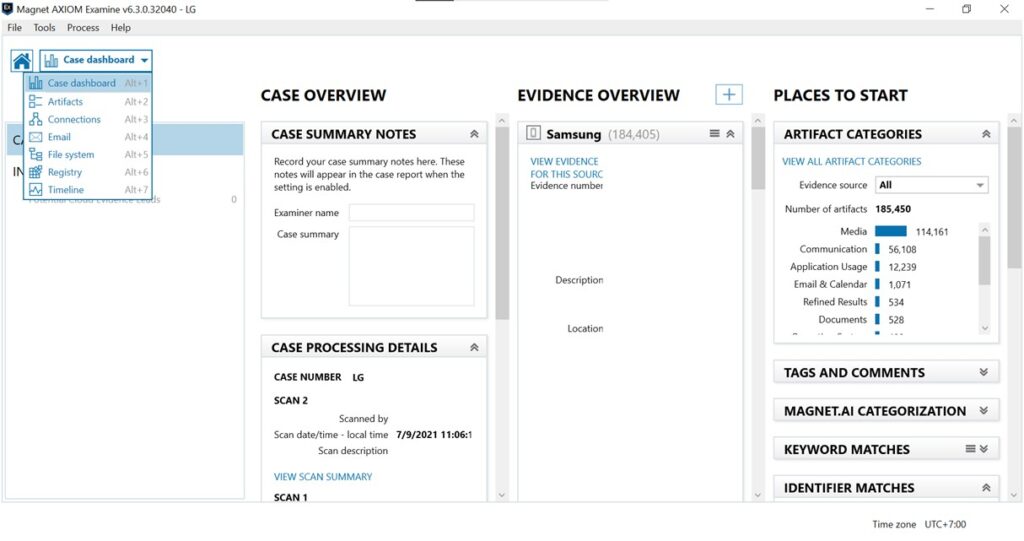
Upon opening AXIOM Examine, we are able to choose from all cases created in AXIOM Process and start or resume an investigation. The case opens with a comprehensive case and evidence overview presented in a dashboard. Digital forensic practitioners can easily review the dashboard to pick up where the case was left off or review which type of artifacts will appear the most in the case.
AXIOM Cyber also provides easy navigation to other necessary interfaces which provide visualization of key data, so that examiners can intuitively interpret, understand, and tell the story of digital evidence such as Artifacts, Connections, Email, File System, Registry, and Timeline. The navigation is accessible through the drop down on the top left-side of the dashboard.
Personally, I love to see this kind of dashboard, where I can prepare the relevant tools for the type of artifacts that are most prominent in the evidence as a starting point for the investigation. As shown in the screenshot sample below, there will be lots of media artifacts that might be important in the case.
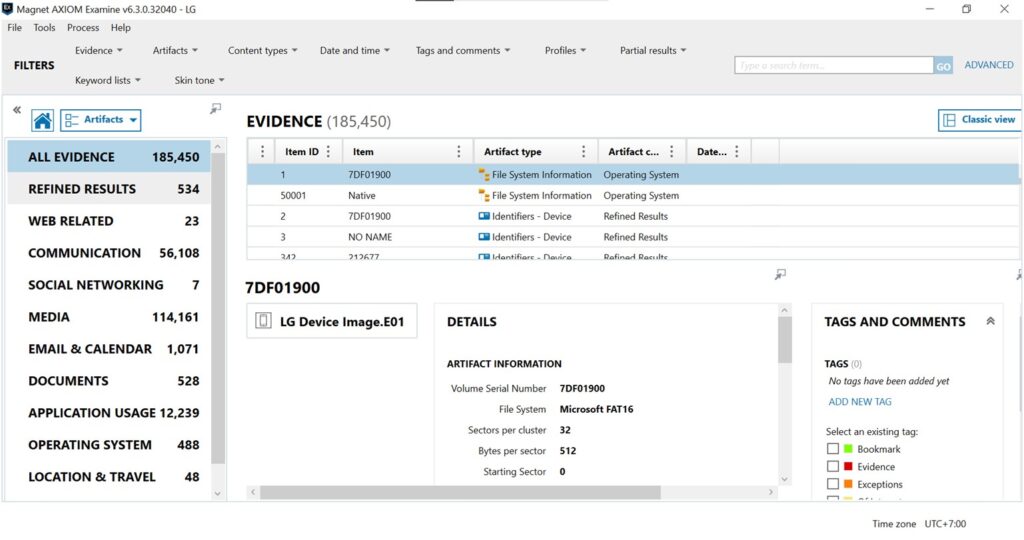
In the Artifacts interface, AXIOM Cyber provides highly customizable filters and layouts that can be utilized to aid an investigation. Digital forensic practitioners often get overwhelmed by the amount of evidence in a single case, but that won’t be a problem with AXIOM Cyber as the filtering system has been tailored to fit multiple investigation flows.
From there, evidence can be selected to analyze by using the Evidence filter. The Artifacts categorization and Content Types filters help find which type of evidence are being analyzed. AXIOM Cyber also covers those who are searching for evidence in a specific or relative date and time or a range of dates and times.
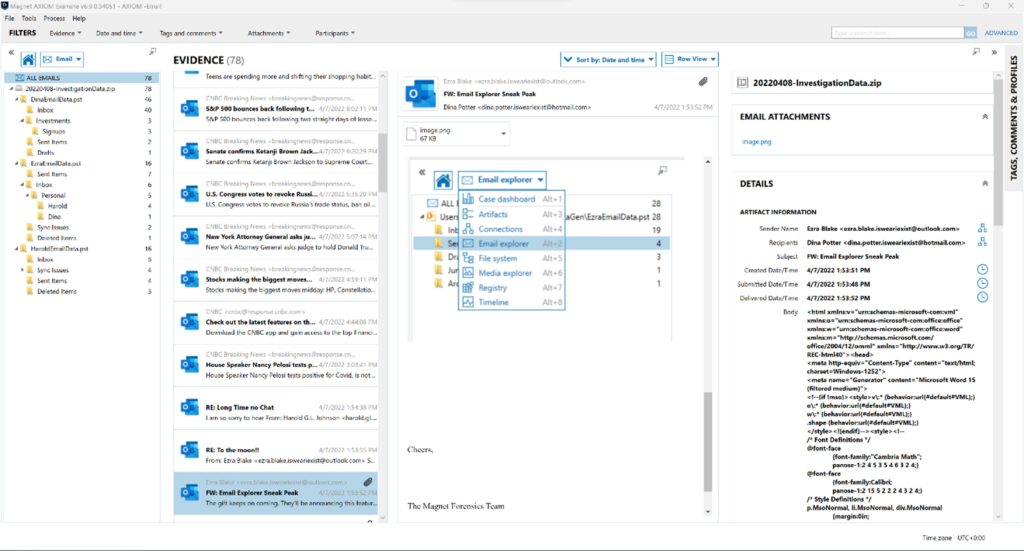
The Email interface helps investigators navigate email related artifacts from Outlook, Cloud Gmail, Cloud IMAP/POP, Cloud Outlook, Cloud Apple Mail, Cloud MBOX, etc. Due to the limitation of sample evidence used in this review, I was unable to test the Email interface. But the error message was very clear, and I was able to understand that the error was encountered because of the sample evidence’s limitation.
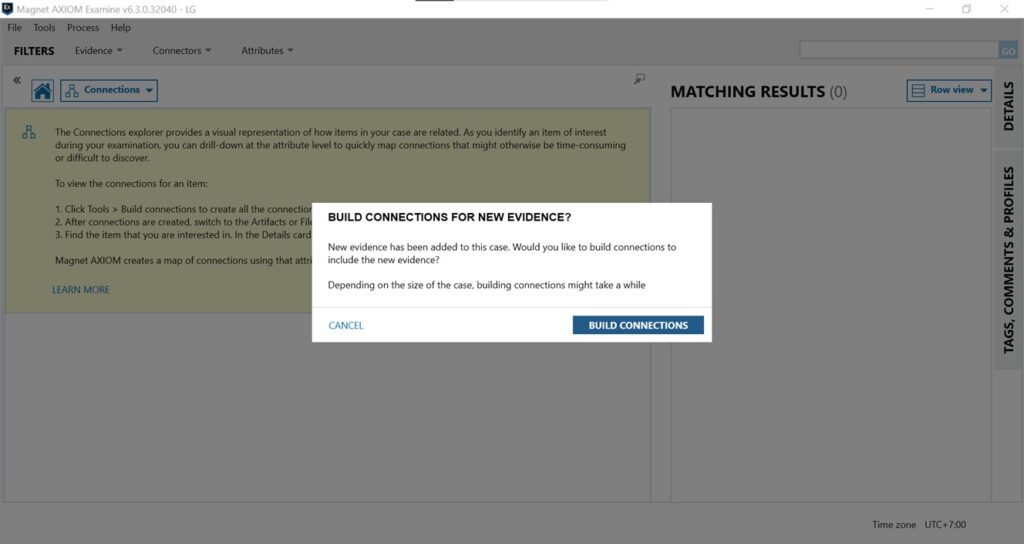
Investigators can see things more clearly by building connections between evidence. AXIOM Cyber helps investigators build connections between evidence that have been marked as a point of interest automatically once the feature is turned on. This feature is especially helpful in cases where multiple sources of evidence are added to the case.
For investigators who prefer to go through the evidence manually or the process is needed in the investigation, AXIOM Cyber also provides the option by simply going to the File System interface. AXIOM Cyber is also built with the capability of analyzing and investigating Registry files, which is a necessity in investigating computer evidence, such as in cases that require the investigator to look at the computer configuration or any traces left in the Registry keys by malware.
Last but not least, AXIOM Cyber is also capable of building Timelines based on every evidence type added to the case. Building a Timeline is a quick process depending on the size of the evidence and the workstation capabilities. Investigators will be able to switch between Years, Months, Weeks, Days, Hours, and even down to Minutes, and any point on the Timeline can be clicked to provide more details on the artifacts with the timestamp. Investigators can choose to go to a specific date or a range of dates of interest by simply clicking on the calendar icon, which helps to speed up time-based incident investigation.
AXIOM Cyber also provides relative time filters, which allows examiner to set an anchor point and filter the timeline to a desired period before and after the anchor. This is very useful in figuring out root cause and the incident chronology once the incident time is determined.
Another point of interest on the Timeline interface is the capability of showing how many different timestamps are available for each artifact and the ease of navigating to the next timestamp if it’s available.
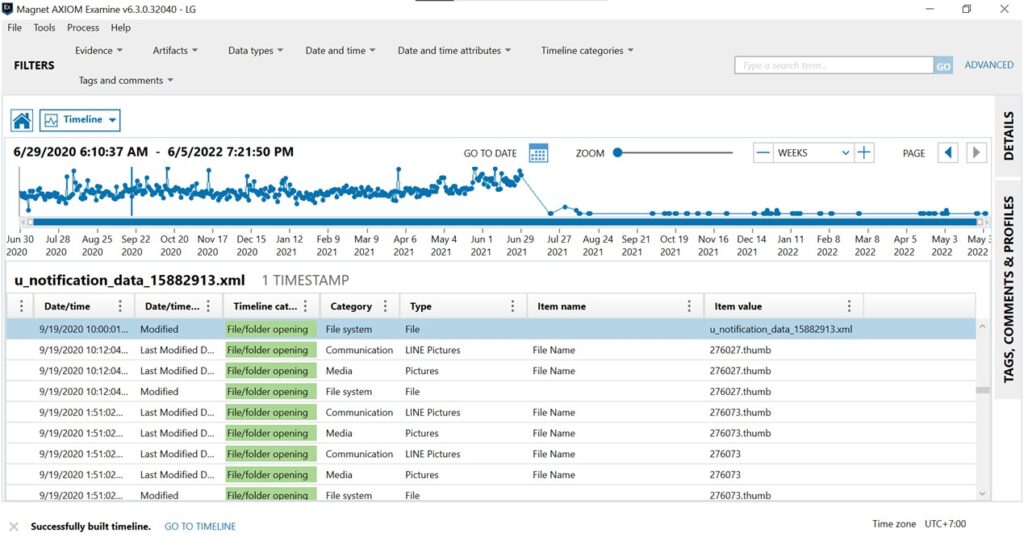
Based on my own experience as an incident investigator who works closer with malware cases than criminal cases, the most helpful feature from AXIOM Cyber is the Timeline feature. With malware cases, it is important to have a complete breakdown of the artifact’s timeline, and the ability to explore the timeline in detail helps get the best insight into what’s happened.
The user interface is also very intuitive, which helps reduce redundancy in an investigation flow. Within the simulation of a real case, I was able to easily navigate through the platform, and the tool worked properly in assisting the investigation by displaying necessary information, both by default and in highly customizable formats. From tool tips to error messages, everything is stated clearly to help investigators navigate through the tool.
For many years, digital forensic tool vendors have tried rather unsuccessfully to create a tool that will potentially cover all investigative bases in one offering. The advancement of mobile technology coupled with the need for cloud-based data acquisition and analysis capability has made it even more difficult for developers to meet current needs and keep up with trends in the technology. By listening to the community and incorporating their very capable and user-friendly interface, Magnet Forensics has taken AXIOM Cyber one step further to help solve digital forensic problems and get answers clearer and faster. Corporate investigators, incident responders and private sector practitioners alike would be very wise to invest in AXIOM Cyber as their go-to analysis resource for computer, mobile and cloud-based evidence. It truly is a one-stop-shop for your digital forensic needs and will continue to advance and grow as the needs of the community evolve.
Feby Thealma is a cyber security expert who specializes in digital forensic investigations from Jakarta, Indonesia. At the age of 20, she has started working in the industry and handled many digital forensic investigations. She always tries to find new challenges and opportunities to learn and grow in cyber security and especially digital forensics.