UPCOMING WEBINAR – Unique Exploits And Solutions In XRY & XRY Pro
REGISTER NOW HERE
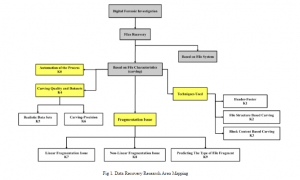
Successful investigations rely on fast and precise data recovery – there’s no two ways about it. And with most reported crimes nowadays having a digital footprint, it’s more important than ever to have the right tools and skills