Syria McCullough: Hi, my name is Syria McCullough, and today I will be giving a presentation on our paper called: Another Brick in the Wall: An Exploratory Analysis of Digital Forensics Programs in the United States.
So, first here’s a little bit of information about the authors. As I mentioned, my name is Syria McCullough. I’m a graduate student at the University of New Haven, and my major is Cyber Security and Networks. I have a bachelor’s degree from the university in Biology and Forensic Science. Stella Abudu, she’s also a graduate student in Cybersecurity Networks and she holds a bachelor’s degree in Clinical Psychology. Ebere Onwubuariri, she recently completed her graduate degree in Cyber Security and Networks and holds a degree from the university in Computer Science. And lastly, we have Dr. Baggili, he’s the founding director of the Connecticut Institute of Technology at the University of New Haven, and he leads our research team on campus.
So on today’s agenda, we’re going to go through the introduction and introduce the purpose of this paper, the methodology, the discussion, the conclusion, and the future work.
So in this slide, we’re going to talk about the purpose of this paper and this quote wraps it up perfectly. It reads: The diversity and abundance of emerging programs in the U.S. related to cybersecurity and digital forensics makes it imperative to conduct a meta-analysis of the state of curricula to gain deeper insight into their similarities and differences. That just means that in response to the growing digital forensics market, universities are implementing digital forensics at their academic institutions. However, not all of these digital forensics programs are sufficiently preparing students to apply digital forensics concepts in the field upon graduation.
So there have been numerous studies on digital forensic standards and curriculum. However, to the best of our knowledge, there haven’t been any studies that examined the current digital forensics courses offered across the nation.
So our work provides a primary analysis on 70 academic institutions and 97 degree programs in the U.S. related to digital forensics. Our work also explores courses taught in universities with the NSA Centers of Academic Excellence designation. Those with an accreditation from the Forensic Science Education Programs Accreditation Commission, and those with the Centers of Digital Forensics Academic Excellence designation, as well as those that do not hold any of these designations or accreditations.
And lastly, our work presents necessary updates to academia, to explore both adequacies and deficiencies in digital forensics curriculum.
And now for our methodology. All universities were chosen based on online searches. So much of those will be made by prospective students looking to go into digital forensics. As I mentioned, 97 degree programs in the U.S. were chosen. And to create our data set, we used seven knowledge domains that were outlined by the Department of Defense Cyber Crime Center. And these are also the knowledge domains that the CDFAE designation uses to create their course curriculum. And the CDFAE, as I mentioned, is the Centers of Digital Forensics Academic Excellence.
In addition, 15 courses were chosen and they were chosen based on their importance in the digital forensics field today. And lastly data was gathered from universities that have digital forensics degree programs or those which had digital forensics courses offered as part of other cyber related degrees. And some of these degrees were Digital Forensics, Cyber Information Technology and Criminal Justice.
And here we have the courses that we used to create the data set, as I mentioned, the seven knowledge domains. Those are Investigative Processes, Lab and Forensic Operations, Legal and Ethics, Network Forensics, Program and Software Forensics, Quality Assurance, Control and Management and Storage Media.
And on the right, these are the remaining courses that we analyzed. Here are the 15 courses and we’ll see them again in the results section.
So first, before we get into the results section, I would like to discuss some of the limitations of our work. Of course, it was done through manual analysis. So we need to account for human error. However, some of the course catalogs had vague descriptions. And as you can see in the next slide, we had to classify these courses as not specified. Additionally, some of the courses could be offered at universities, however the course catalogs are not kept up to date and prospective students, as well as us, could not see that. And also teachers can deviate from the course catalogs and they could teach more or less than what’s available in the course description online.
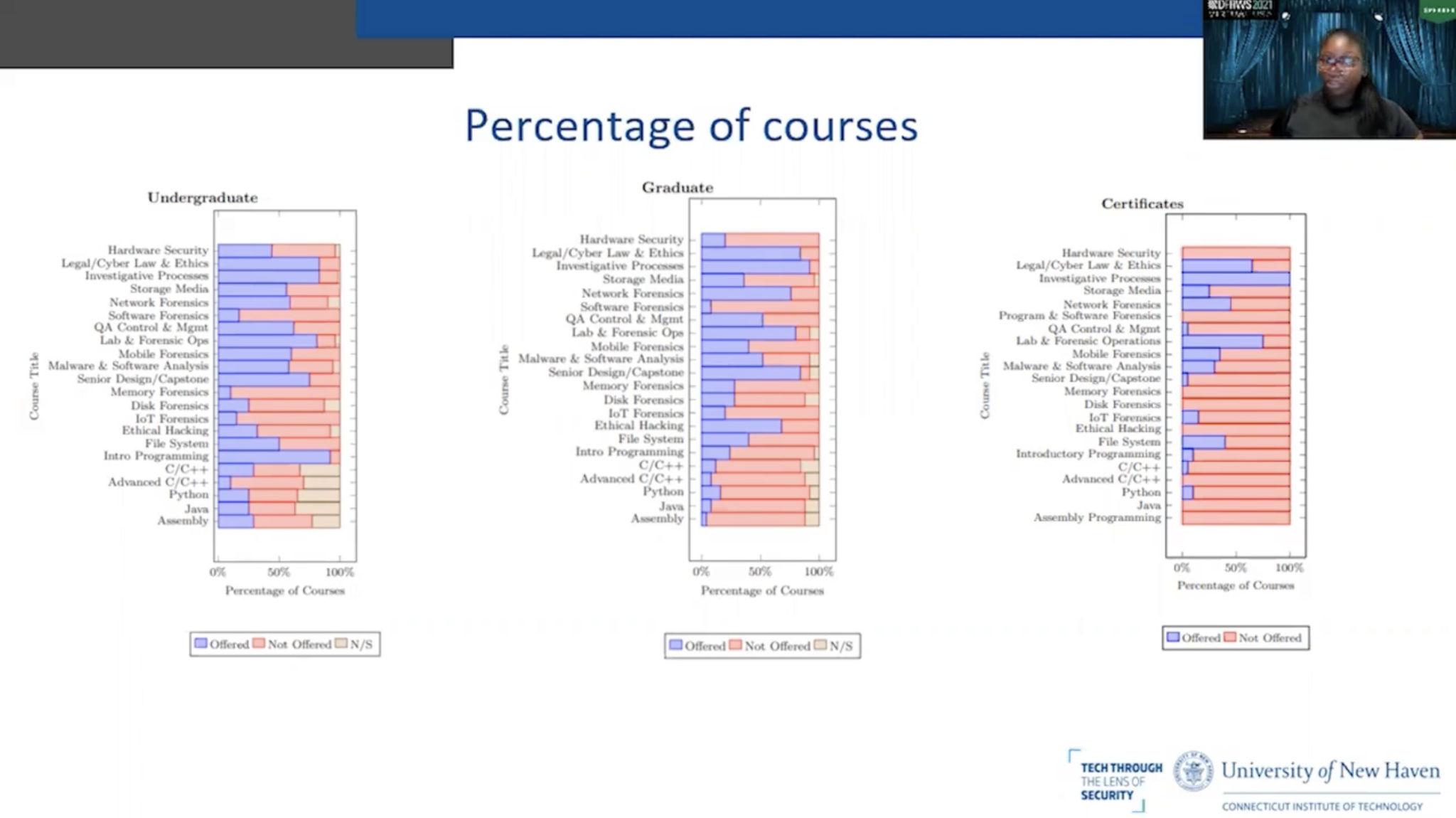
So here are the charts for the undergraduate and graduate degrees that we looked at as well as some of the certificate programs. As you can see, the blue stands for the percentage of courses that are offered, the red are the percentage of courses that are not offered. And again, the beige are the percentage of courses that are not selected, which just means that the course description was unclear. Also, we are comparing the degree types to degree types. So we’re comparing undergraduate degrees to other undergraduate degrees. We’re not comparing the undergraduate to graduate because the average credit hours are different for each. The average credit hours for the undergraduate degrees were 120 while the graduate degrees were 34 and the certificates were around 16 to 17 credit hours.
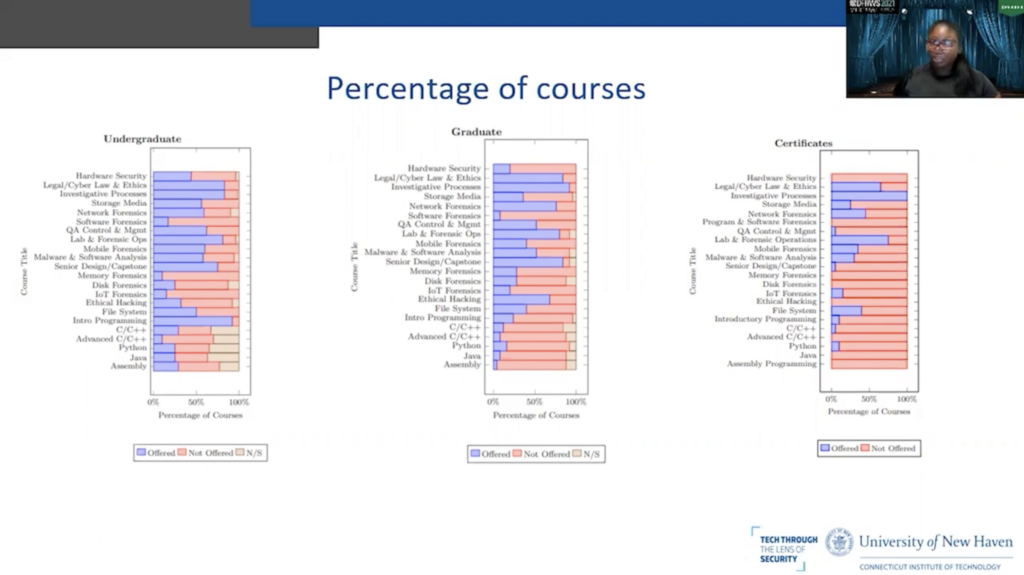
So the major takeaway from each chart are the courses that are offered the most and the courses that are offered the least. So I’ll quickly go through the findings so we can discuss. For the undergraduate degrees, the courses that are offered the most were an Introductory Programming course and Investigative Processes course, Legal/Cyber Law and Ethics, Lab and Forensics Operations and a Senior Design or a Capstone.
The courses that were offered the least are Memory Forensics, Advanced C/C ++, IOT Forensics, Program and Software Forensics and Disk Forensics.
Similarly, for the graduate degrees, the courses that are offered the most are Investigative Processes, Legal/Cyber Law and Ethics, Senior Design or a Capstone, in this case it would be a thesis project, Lab and Forensics Operations course and Network Forensics.
The courses that are offered the least are Assembly Programming, Java, Advanced C/C++ and Program and Software Forensics.
And in the certificate chart, you can see that the top courses are Investigative Processes, Lab and Forensic Operations and Legal/Cyber Law and Ethics. Again, you can see that there’s a high percentage of courses that are not offered. Again, that’s due to the fact that certificates are only around 16 to 17 credit hours and the courses that are not offered at all for these programs are Hardware Security, Program and Software Forensics, Memory Forensics, Disk Forensics, Ethical Hacking, Advanced C/C ++, Assembly Programming and Java.
So after looking at the courses that are offered the most and the courses that are offered the least, we saw that some of the technical courses that are needed in digital forensics were not offered in many of the universities. For example, only 10% of the undergraduate degrees offered a Memory Forensics course, only 33% at the graduate degrees and not at any of the certificate programs.
So these courses should update to include Memory Forensics because memory forensics is needed so students can learn how to analyze dynamic and volatile memory and in order to have a complete digital forensics investigation. Students should be able to analyze a computer that was left powered on at a crime scene and have the skills to retrieve that volatile data that will be lost once the machine is turned off. So courses such as Memory Forensics should be taught in digital forensics education programs before students enter the workforce.
Also 85% of universities did not offer an IOT forensics course. That should not be the case with the abundant amount of IOT devices that we have today. Students should be able to obtain digital evidence from numerous devices, especially since standard digital forensics methods and tools do not work on these newer IOT devices. Students should be introduced to it during their education in a lab setting.
And lastly, of course, Program and Software Forensics was not offered in 83% of the degree programs. And a course like this can expose students to another branch of digital forensics involving software patents and copyrights and malware analysis.
So before we move on to the next slide, after looking at those results, we’ve grouped 18 of the 22 courses for the undergraduate degrees into three respective categories. Those categories being security courses, forensics courses, and programming courses. We looked at the percentage that they were offered and we found that security courses were offered the most at 58% followed by forensics courses at 38. And 2% behind that are the programming courses at 36%. And this shows that the universities are on the right path because security and forensics courses should be offered more than programming courses, especially since this field is always updating and students need these courses for their curriculum, and we feel that they should be weighted a little bit more than the programming courses.
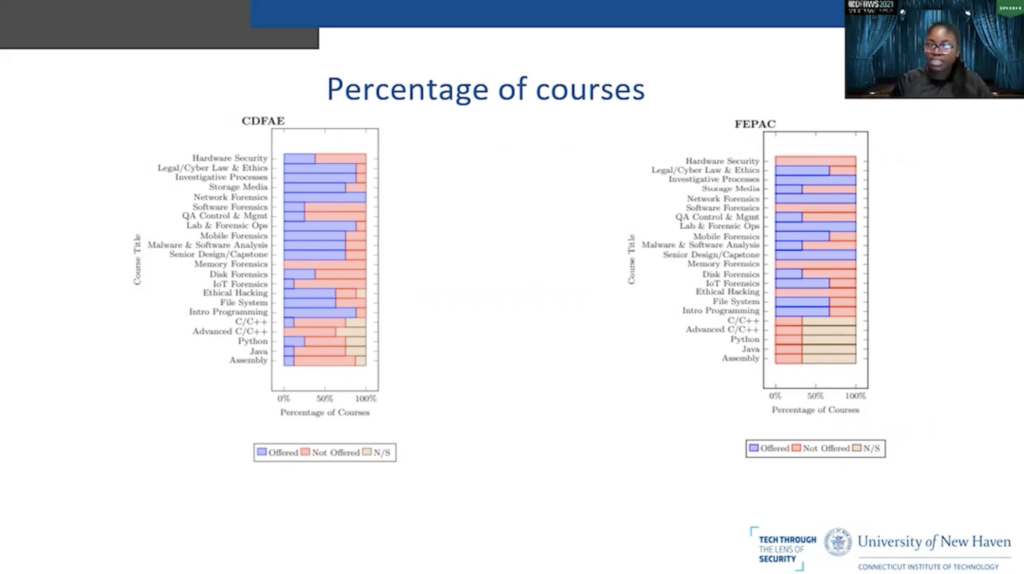
So the last slide was an overview of the undergraduate and graduate degrees and the certificate programs that we reviewed for this paper. In this slide, we pulled out those with the CDFAE designation and a FEPAC accreditation to compare the two.
So first looking at the left, the CDFAE designation, as we mentioned, stands for Centers of Digital Forensics Academic Excellence. The CDFAE designation’s goal is to have a well-rounded digital forensics curriculum. One that will equip students with the knowledge and skills needed to become digital forensics professionals.
So I found that the top courses offered for the CDFAE designation are Network Forensics, Lab and Forensics Operations, Investigative Processes, Legal/Cyber Law and Ethics, Introductory Programming, Storage Media, Mobile Forensics, Malware and Software Analysis and a Senior Design or a Capstone. And this is in line with the seven knowledge domains that we mentioned earlier. And the courses that are offered the least are Memory Forensics and Advanced C/C ++, both at 0% across the board for the CDFAE designated universities.
And then you have C/C++ programming, Java, Assembly Programming, and IOT Forensics, all at a low offering percentage of around 12%.
Next, we can take a look at the chart on the right for the FEPAC accreditation. So the goal of this accreditation is to enhance the quality of forensic science education. So this accreditation is for forensic science degrees, however, they do accredit computer science degrees with the forensic science concentration. And currently there are only three universities that hold the FEPAC accreditation for digital forensics or digital evidence. Since there are only three universities that hold this accreditation that can attest to why there’s a higher percentage of courses that are not offered, especially compared to the CDFAE designation. But we’ll take a look at the courses that are offered the most.
So for the FEPAC at a hundred percent, they offer a Senior Design or a Capstone, a Network Forensics course, Investigative Processes and a Lab and Forensics Operations course. The courses that are not offered across all of the universities are Hardware Security Program and Software Forensics, Memory Forensics, Ethical Hacking, C/C++, Advanced C/C++, Python, Java and Assembly Programming.
That being said, we put both of these charts next to each other to highlight the fact that when students are looking for a degree program, especially a digital forensics degree, they should look further than the accreditation and onto the course catalog and the plan of study. The requirements for the FEPAC accreditation for a computer science degree or their forensic science concentration are covered in all of the degrees. More topics should be covered for students graduating with this accreditation. FEPAC needs to expand their requirements and their digital forensics curriculum to include more of these relevant topics. Because additionally, that could cut down on the time that it takes for graduates to become proficient investigators.
On the other hand the CDFAE designated schools, as we said, are focused on providing the knowledge and skills students will need in the field. And that is reflected in the percentage of courses that are offered across the course catalogs. 11 of the 22 courses we reviewed were offered over 50% of the time. Of course, improvements could be made. The CDFAE universities could start incorporating a Memory Forensics course or an Advanced C/C++ Programming course. And of course, increase the frequency of the 22 courses within their course catalogs. However, compared to the FEPAC accreditation, CDFAE, designated schools are more likely to provide the necessary skills needed to pursue a career in digital forensics.
So for our last chart, we compared the private versus the public academic institutions for the undergraduate degrees. We tried to see if the private or the public institutions had a higher percentage of offered courses. However they seem to follow the same overall trends. And we didn’t find a significant variation between the two. So here are a few points that we’re going to discuss quickly.
So as we mentioned, digital forensics courses vary from university to university, which shows that there’s a lack of standardization in digital forensics education. Standardization could solve some of the problems that the digital forensics industry is facing today. This lack of curriculum standards increases the difficulty in creating digital forensics programs, and then indirectly affects other challenges such as finding qualified faculty, setting up lab exercises and deciding which equipment and tools to include.
So the next point is the integration of modernized security and forensic courses. As we said, students should be updated during their education on important digital forensics topics. And we didn’t know that for the undergraduate degrees, the courses that were not offered the most or weren’t in 80% of the course catalogs were Memory Forensics, IOT Forensics and Program, and Software Forensics. Also for graduate courses, the courses that were not offered 80% or more were Program and Software Forensics, Assembly Programming, Hardware Security, IOT Forensics, Advanced C/C++ and Java.
And lastly, we noticed that there was no uniformity in which colleges within a university offered digital forensics and related degrees. So that means that we found that digital forensics courses were being offered in the College of Engineering at some universities while others, it was offered in the College of Business or the College of Arts and Sciences. Digital forensics expands multiple industries, however having the same degree title offered at different colleges and departments across universities can attest to the disorganized state of digital forensics education today.
And to conclude, we found that Investigative Processes, Lab and Forensic Operations and Legal/Cyber Law and Ethics courses appeared in most of the course catalogs. The courses that were offered the most were pretty uniform across the board and the courses that were offered the least varied a little bit more. So most of the universities did not offer a Memory Forensics or an IOT Forensics course. And of course you have the courses that were near the median, such as Hardware Security, that should be offered a little bit more frequently within the course catalogs. We looked at the public and private institutions for the undergraduate degree, and we really did not find a significant variation between the two academic institutions.
Overall, we felt that universities need to take a deeper technical approach to digital forensics education. A lot of the process, a lot of the courses were introductory in nature. So these programs should include more in-depth analysis on important topics.
And that leads into our last bullet point, which is that future work should explore conducting surveys and interviews to explore the similarities and differences between what is actually taught and what’s available in the course catalogs. As we mentioned earlier, teachers can deviate from the course catalogs and that should be explored further so we can get accurate data on these digital forensics programs.
Thank you. I hope you enjoyed this short presentation. We would like to acknowledge Courtney Hassenfeldt, Sahara Fathelbab, Muna Abdelrazeq and Tiffanie Edwards. Thank you for your insightful feedback and your visions and your overall support.
And the last slide is our contact information. If you would like to ask any questions on something that wasn’t included in this presentation or an upcoming Q and A session, please feel free to contact us. As I said, my name is Syria McCullough and that’s my email. And of course that’s the email of my advisor, Dr. Baggili. Thank you and thank you for listening.