Hello, and welcome to this presentation on enhancing traditional forensic investigations using IoT traces from smart buildings. We will look at how IoT devices and the traces generated can be useful to provide additional insight in classical forensic investigations. We will also discuss which main challenges are presented by the analysis of these devices and propose a method to approach them.
IoT devices can broadly be divided in industrial IoT devices and Smart Home IoT devices. We’ll focus on Smart Home IoT devices, which are an ever-growing market composed by multiple segments: Security Systems, Smart “Things”, and Smart Assistants, which often interact with each other directly or through cloud services. IoT devices can be direct targets, due to reduced security implementations and access to sensitive data. At the same time, they can be digital witnesses as extended data is collected by these devices about their surroundings and the interaction with the users in order to provide the needed functionality. We’ll focus on this aspect.
So why collecting this data? Data collected by these devices can be useful in traditional investigations in multiple ways. It can help reconstruct the sequence of events either by logging presence of people directly or indirectly by recording environmental conditions. A sudden change in temperature might indicate the beginning of the house fire, a sudden drop in temperature, detected by radiator valve, may allow investigator to pinpoint a break-in time, as we can see in the image above. Some devices may also record images and sounds useful for identification of persons, as recently happened in Germany, where audio from a Alexa device was used in a trial. They can also contain hints about authentication information or other devices that may expand the investigation perimeter.
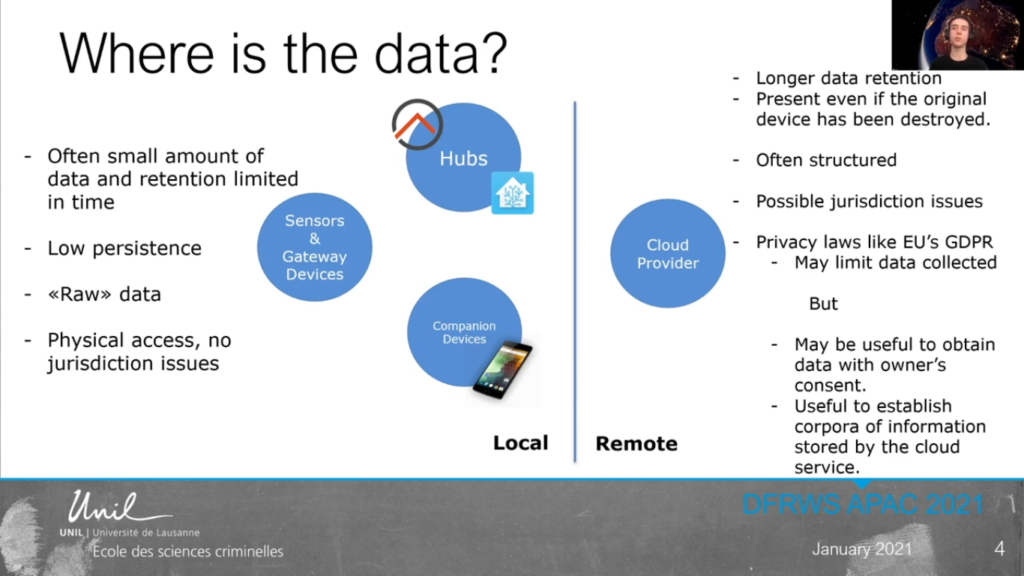
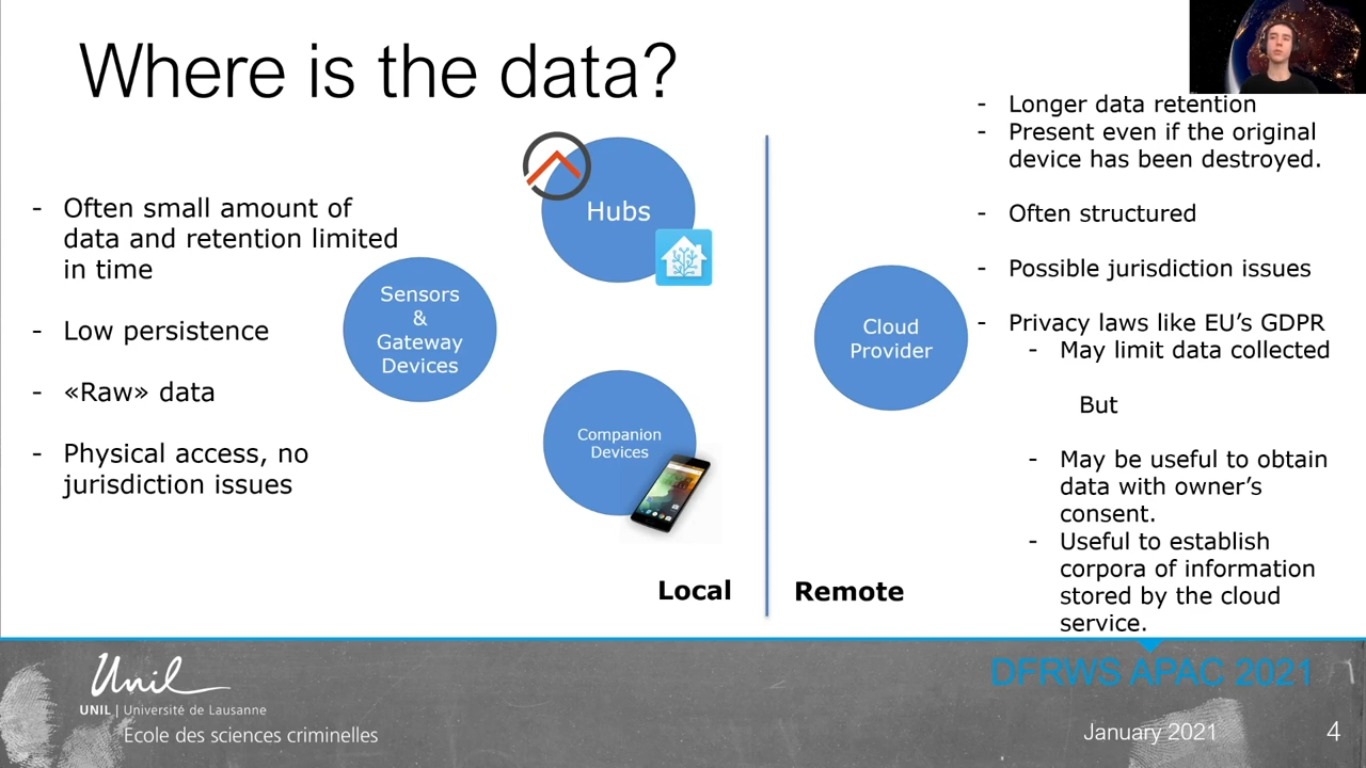
So where is the data we’re interested in? We can find it in multiple locations each with different challenges. Locally, we can find directly the data on the sensors or the gateway devices such as a camera or a Smarter System. We can find it on hubs or aggregators used to centralize with device management, such as Home Assistant or open HEB or on smartphones with companion apps installed. Remotely, we can find it on the servers of a device vendor.
Data stored locally on the device and sensors is often limited in retention time due to limited storage space and is often not persistent. Additionally, it is raw data which needs additional interpretation to appreciate its meaning. Remotely stored data has often better retention, and it’s better structured. However, generally it incurs jurisdiction issues, as well as issues due to privacy laws like GDPR. These same laws, however, can sometimes be useful to obtain data when consent of the owner is present. They can also be useful to establish a corpora of information during the study of new device in the controlled environment.
Smart Hubs can particularly be interesting to analyze. We can see in this example that it’s pretty easy to detect the presence of a person at home and even in a particular room as highlighted by the changes in the light switch or Valeant iOS devices. Finally, multiple chain engines are linked to IoT analysis. Detection of the pertinent device or traces is among the first steps of a forensic process. IoT devices was a particular challenge in this aspect, as many times, they are hidden or may be mistaken for traditional objects, such as the case here with the challis light switch or a heater radiator valve. Additionally acquisition of IoT devices is often challenging and requires a very technical approach. Access to data on cloud services is generally met with constraints due to jurisdiction, and can thus be a long process.
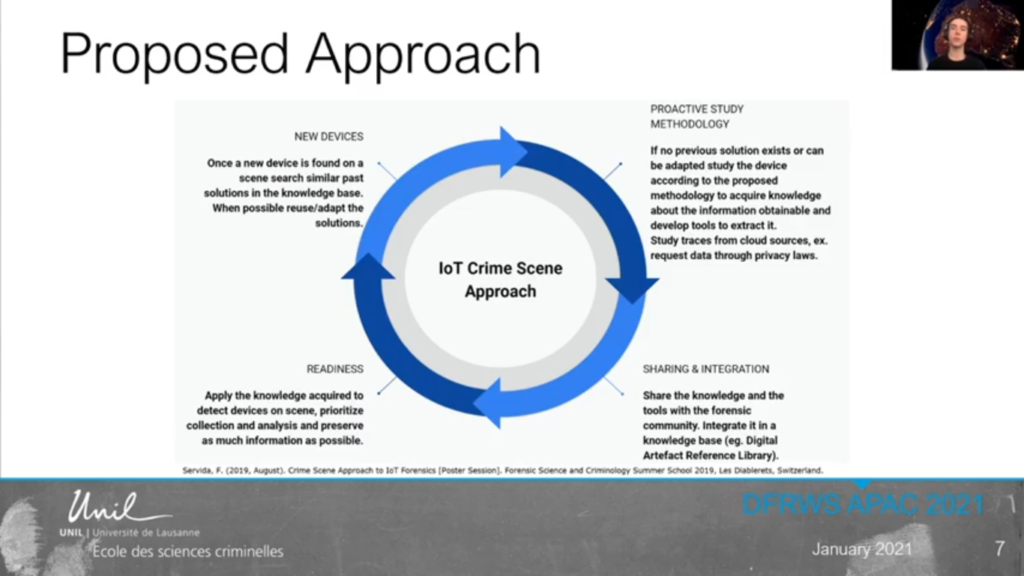
Finally, even when the data is obtained, the meaning is not always clear and understanding these traces may require extensive experimentations. In light of the value of these traces and the challenges in obtaining and exploiting them, we propose a multi-step approach to the IoT investigation on crime scenes. Upon discovery of a new device of interest on the scene, a study in a controlled environment is proposed to assess which traces are obtainable from a device itself, the companion apps, and eventually cloud sources and establish the investigative value of these traces.
This data is then fed in a shared knowledge base shared by forensic practitioner and researchers alike. We have a final step: the data is used to train investigator on most common IoT devices, sensibilised [inaudible] postural usefulness. And upon investigation of the crime scene, this data will help the investigator prioritize which object to collect based on the forensic value of the traces they can expect to recover from a device. That will be all, thank you for your attention and get in touch if you have any questions.