by Chirath De Alwis
Computer forensics is the process of methodically examining computer media (hard disks, diskettes, tapes, etc.) for evidence [1]. When considering computer forensics, registry forensics plays a huge role because of the amount of the data that is stored on the registry and the importance of the stored data. The extraction of this data is therefore highly important when investigating. Due to the limitation of tools that can extract forensically valuable data from registry files, investigators have to extract it manually. Because of the registry file format (.REG), extracting information is a challenging task for investigators. Registry files normally store data under unique values called “Keys”. One challenge that investigators must face is the lack of knowledge about Registry Keys and the data which stored under those Keys. This article provide an overview of registry file acquisition, registry structure and common issues in registry analysis.
Registry File Acquisition
The Windows registry is a central hierarchical database intended to store information that is necessary to configure the system for one or more users, applications or hardware devices [2]. There are four main registry files: System, Software, Security and SAM registry. Each registry file contains different information under keywords. The structure of the Windows registry is similar to file system directories. Registry files are located at the “C:drive/windows/system32/config/” file path. Each registry contains lots of forensically valuable information.
Investigating the Windows registry is quite a difficult task, because in order to investigate it properly, the registry needs to be extracted from the computer. Extraction of the registry file is not just a normal copy and paste function. Since registry files store all the configuration information of the computer, it automatically updates every second. In order to extract Windows registry files from the computer, investigators have to use third-party software such as FTK Imager [3], EnCase Forensic [4] or similar tools. FTK Imager is oneo fthe most widely used tool for this task. Apart from using third-party software, some reasearch has been carried out to demonstrate how to extract registry information from Windows CE memory images [9] and volatile memory (RAM) [10].
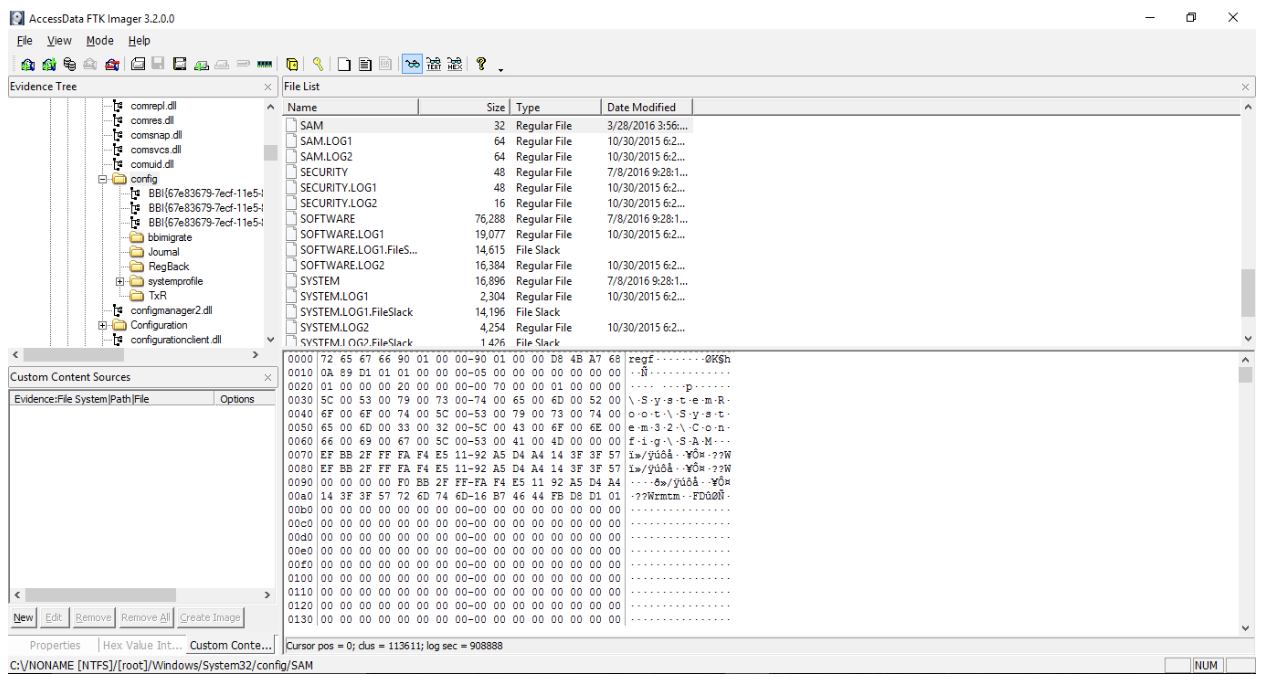
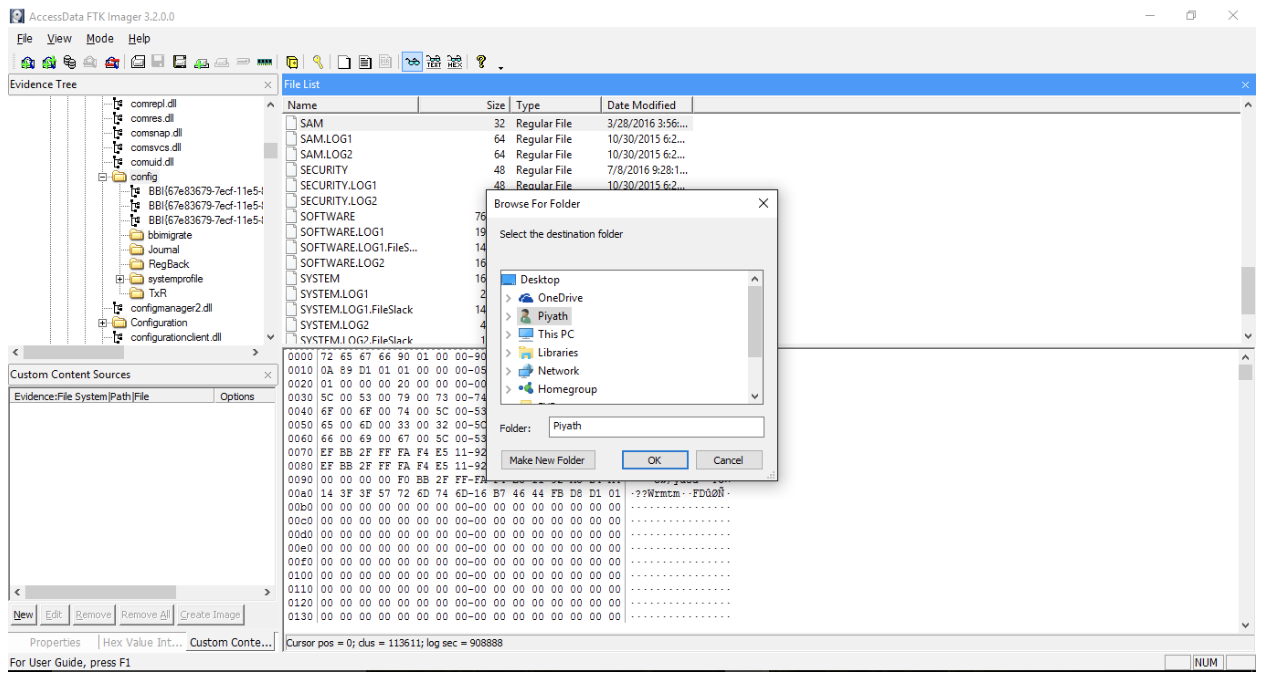
AccessData FTK Imager
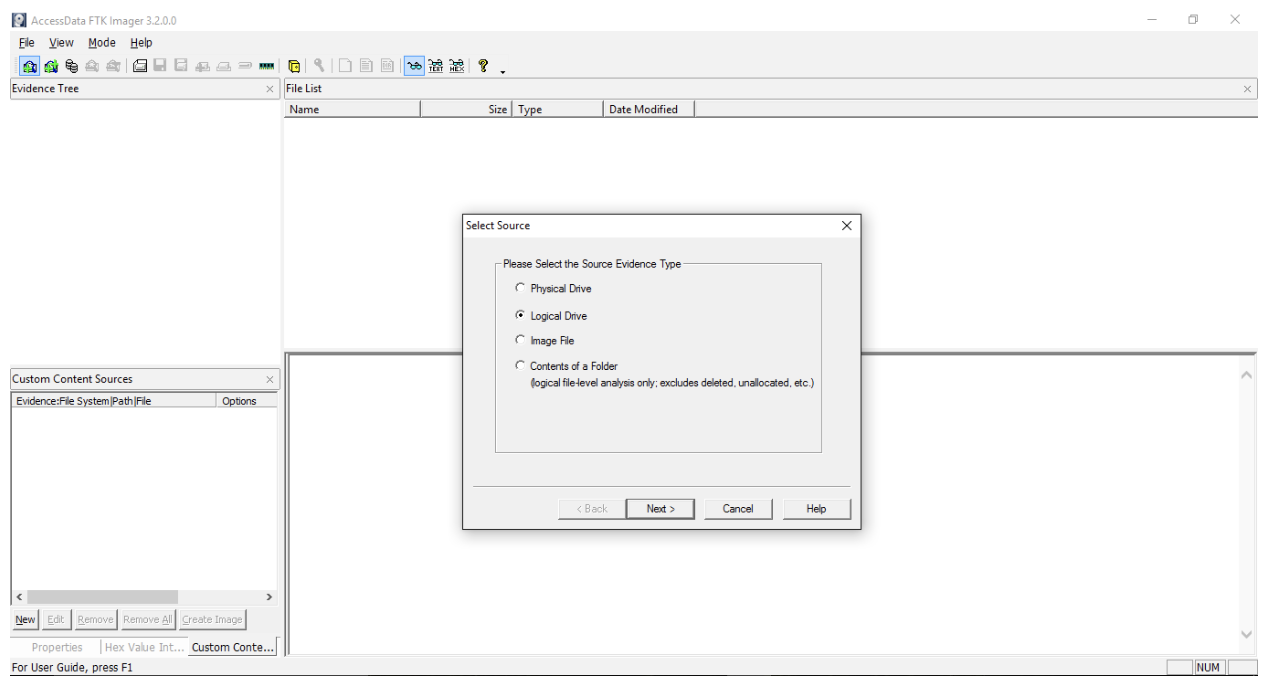
AccessData FTK (Forensic Tool Kit) Imager is the most widely used standalone disk imaging program to extract the Windows registry from computer. Access Data FTK Imager 3.2.0.0 basically scans the hard drive in order to identify various pieces of information. This tool can be used for a variety of processes when extracting the Windows registry. These include:
- Physical Drive – Extract from a hard drive
- Logical Drive – Extract from a partition
- Image File – Extract from an image file
- Contents of a Folder – Logical file-level analysis only: excludes deleted files and unallocated space
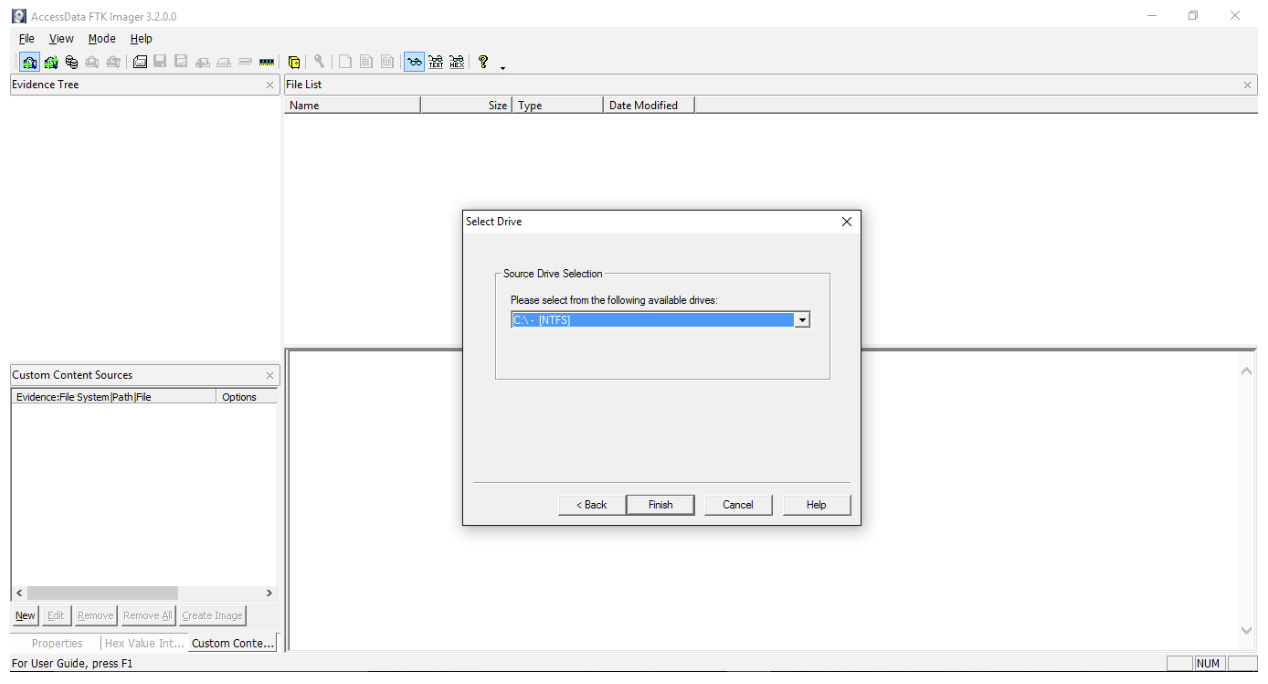
The steps to extract registry files from Access Data FTK Imager 3.2.0.0 are as follows.
Step 1 – Open “Access Data FTK Imager 3.2.0.0”.
Step 2 – Click on “Add Evidence Item” button.
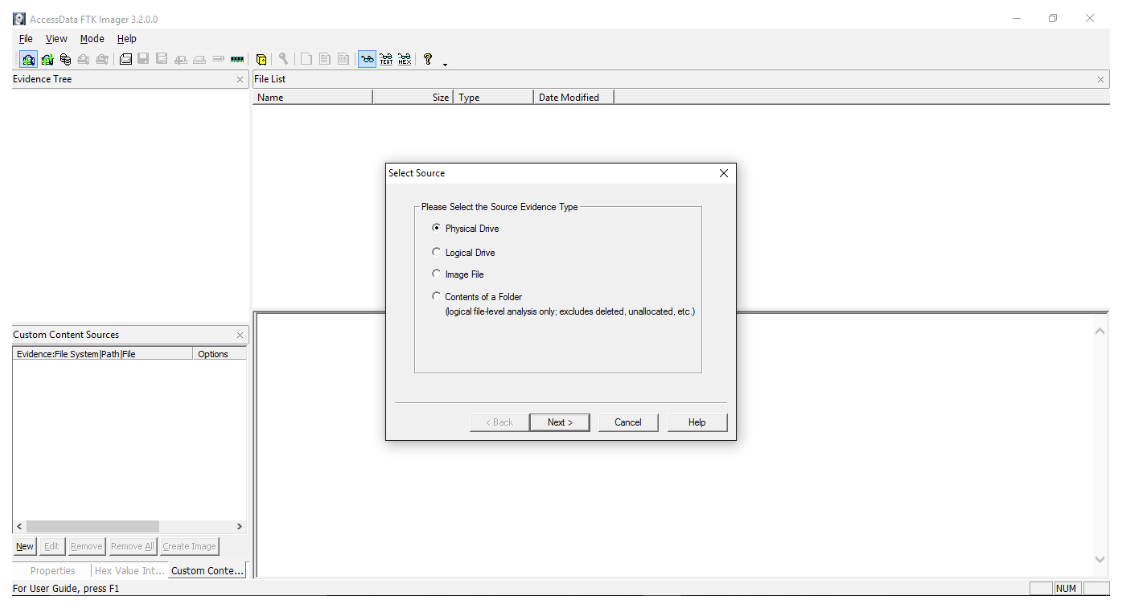
Step 3 – Select “Logical Drive” radio button.
Step 4 – Select source drive.
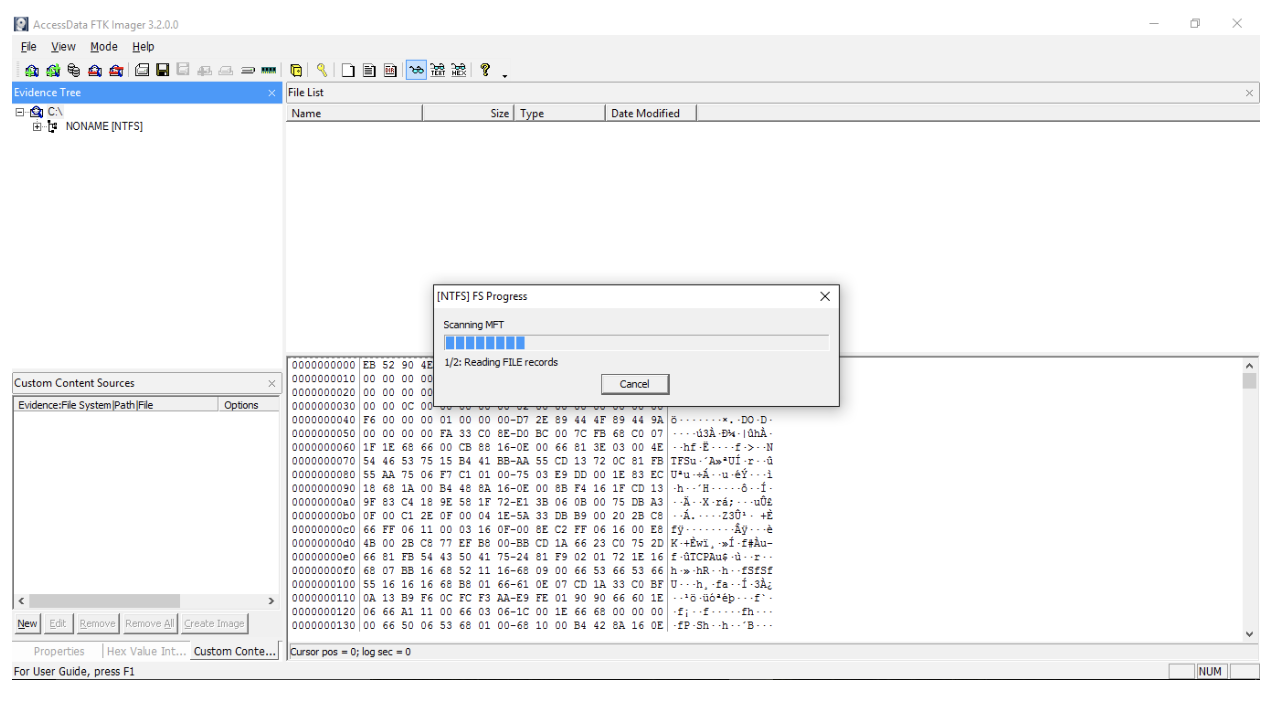
Step 5 – Scan “MFT” by expanding “Evidence Tree”.
Step 6 – Go to windows/system32/config/.
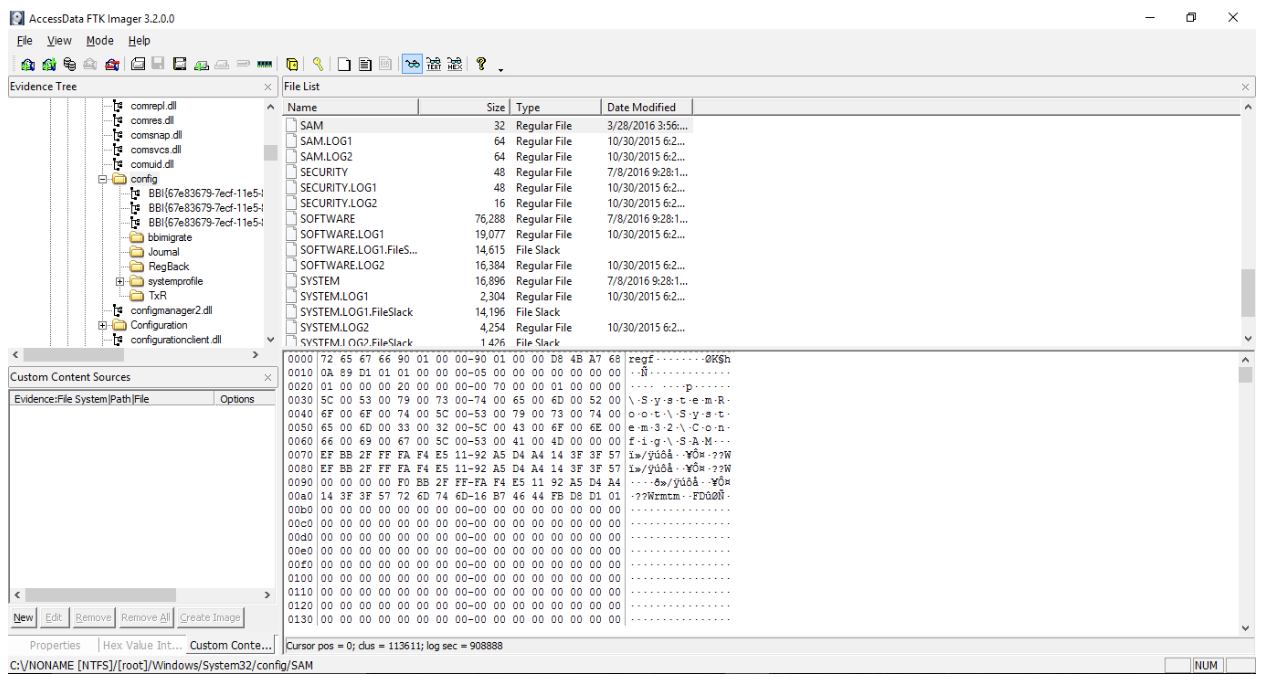
Step 7 – Export registry file by clicking “Export Files” button.
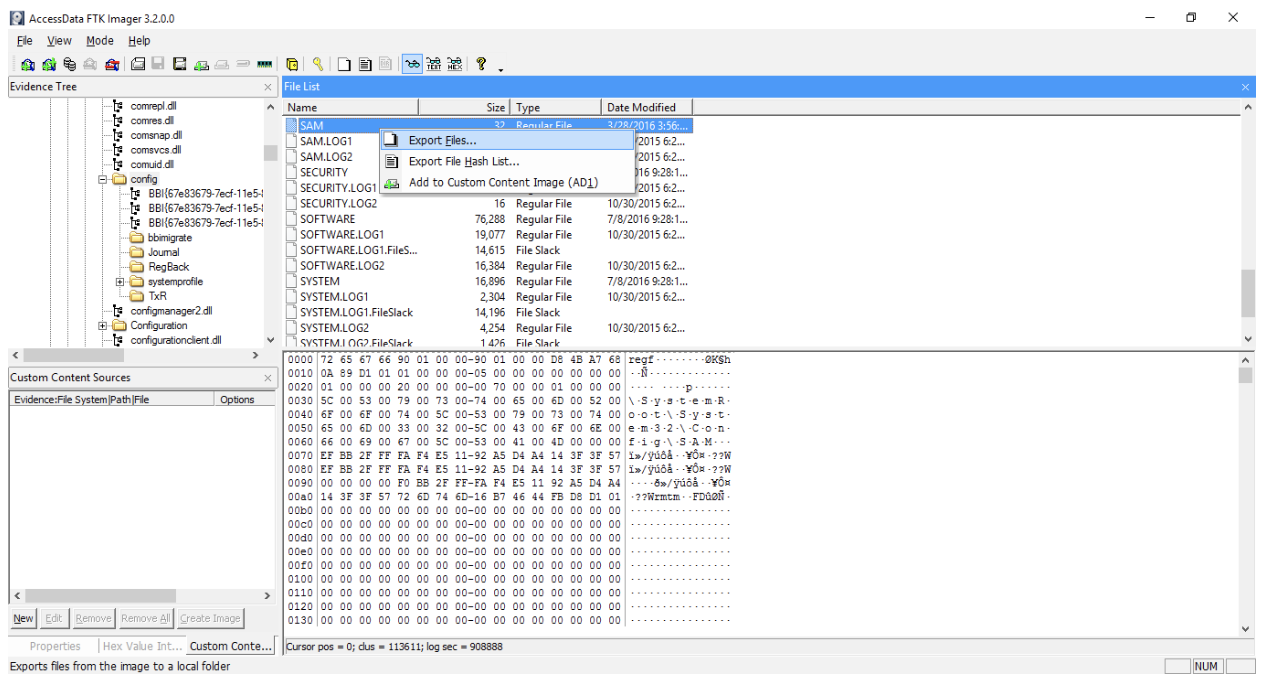
Step 8 – Select the destination folder.
Registry Structure
The structure of the Windows registry is similar to file system directories. Both the Windows registry and the file system are organized in a tree structure [5]. The Windows registry stores all configuration settings as keys [6]. The registry updates its stored configurations according to the changes which are made while hardware and software are being used. In Windows XP, 2000 and 2003 (Windows NT based operating systems) the registry files are stored in the configuration folder located at Windows\System32\Config folder.
As mentioned above, the structure of the Windows registry is similar to Windows folders and files. Each main folder is known as a “Hive”. Hives are made of a combination of sub folders, called “Keys”. These Keys contain Sub Keys with configuration information.
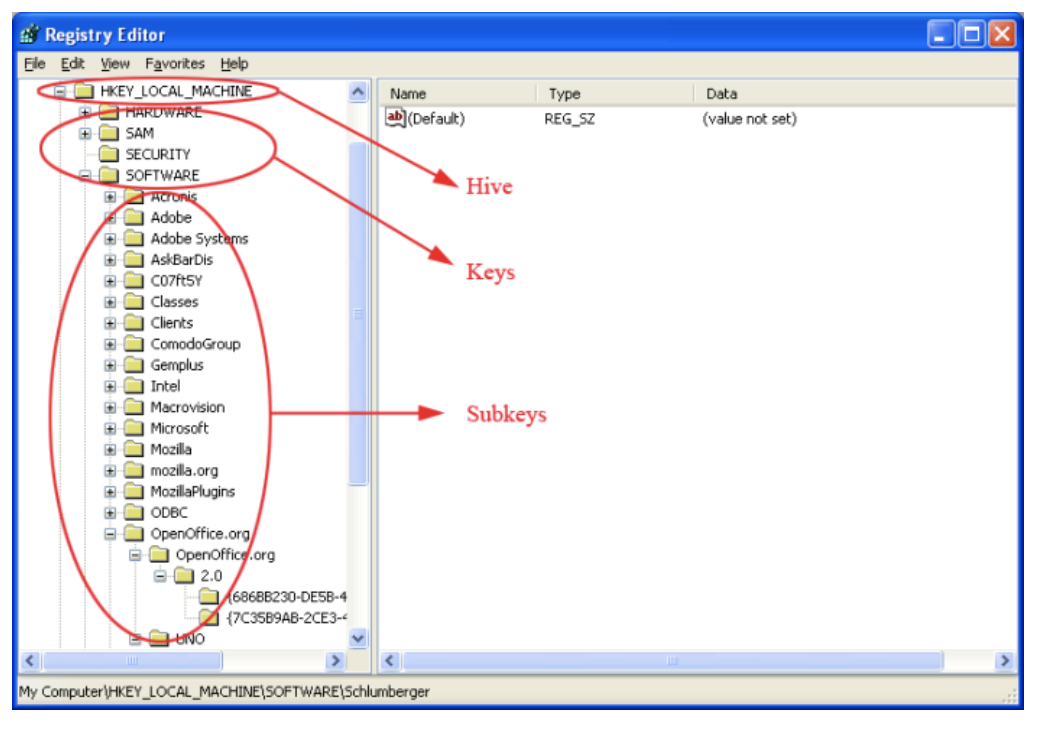
The figure above shows a Registry Editor window of a computer. It shows the internal structure of the registry. A Hive is a logical group of keys, sub keys and values in the registry that has a set of supporting files containing backups of its data [7]. There are five main Hives:
- HKEY_CLASSES_ROOT (HKCR)
- HKEY_USERS (HKU)
- HKEY_CURRENT_USER (HKCU)
- HKEY_LOCAL_MACHINE (HKLM)
- HKEY_CURRENT_CONFIG (HKCC)
Registry Hive and its supporting files are unique to each other. According to Microsoft, the hives and supporting files are [7]:
- HKEY_CURRENT_CONFIG – System, System.alt, System.log, System.sav
- HKEY_CURRENT_USER – Ntuser.dat, Ntuser.dat.log
- HKEY_LOCAL_MACHINE\SAM – Sam, Sam.log, Sam.sav
- HKEY_LOCAL_MACHINE\Security – Security, Security.log, Security.sav
- HKEY_LOCAL_MACHINE\Software – Software, Software.log, Software.sav
- HKEY_LOCAL_MACHINE\System – System, System.alt, System.log, System.sav
- HKEY_USER\.DEFAULT – Default, Default.log, Default.sav
In the HKEY_LOCAL_MACHINE Hive, there are five main Keys. Each Key contains Sub Keys with configuration information. These are:
- HARDWARE
- SAM (Security Accounts Manager)
- SECURITY
- SOFTWARE
- SYSTEM
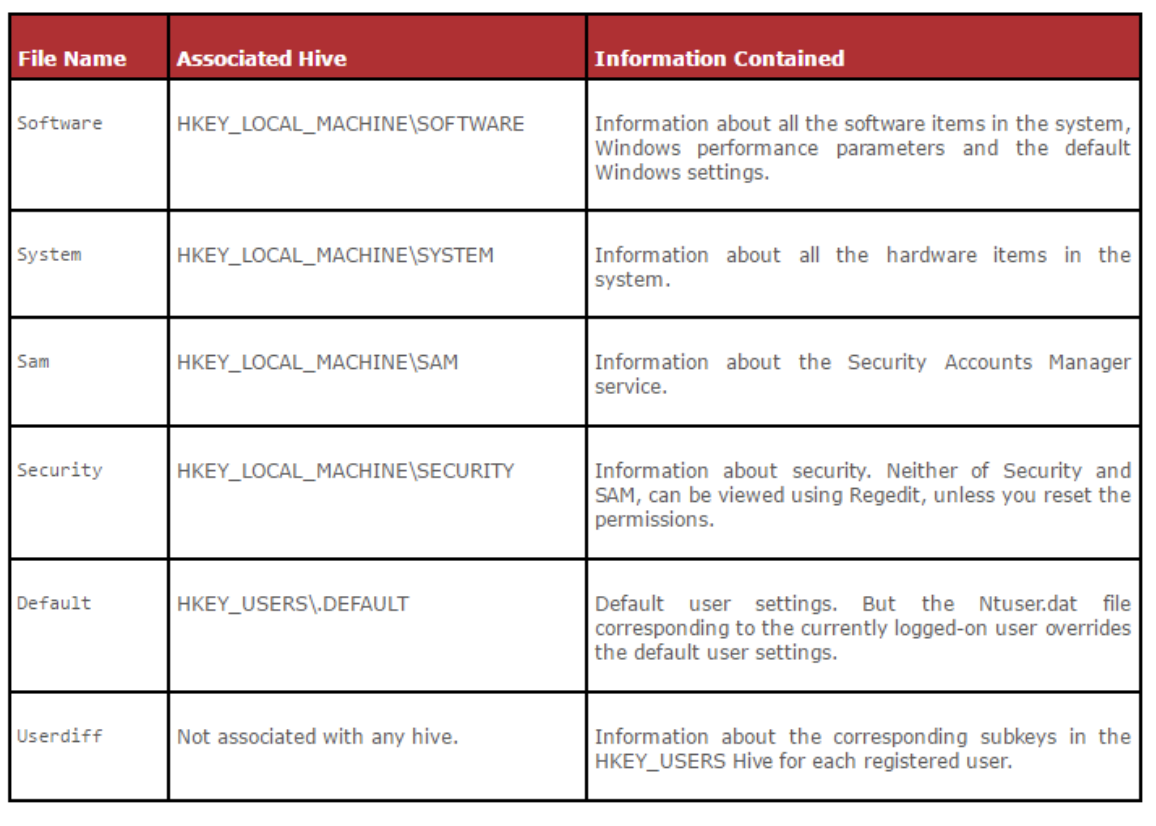
Figure 10 shows the information contained in the Software, System, SAM, Security, Default and Userdiff files and their respective associated file names.
Registry hive files are allocated in 4096-byte blocks starting with a header, or base block, and continuing with a series of hive bin blocks. Each hive bin (HBIN) is typically 4096 bytes [5].
Issues in Registry Analysis
There are few main issues that investigators have to face when analyzing registry files.
- Data Completeness – The amount of information required for the investigation will depend on the type of the investigation. Some investigations require more information than others. Because of this, investigators should ensure that all the data is present and complete. If this is not the case, the investigation may take extra time to complete and therefore be more costly. Missing Data – Missing data reduces the accuracy of the investigation. Missing data can be sorted into three categories of randomness [8]:
- Missing completely at random (MCAR)
- Missing at random (MAR)
- Missing not at random (MNAR)
- Extracting Data – At present there is no technique to view registry files in real time. With the currently available technology, investigators can only take an image of a registry file. The disadvantage of this is investigators cannot collect further information after they have captured the registry file.
- Lack of Knowledge About Keys – Registry files store data with a unique key. Some investigators do not know all the keys which are stored in the registry files. This can lead to missing a lot of information. There are also some instances in which it is not possible to find out about certain keys and stored information.
- Registry File Format – Registry files are stored in the “C:drive/windows/system32/config/” file path and they must be ripped and converted into a readable format before being used in an investigation.
References
- Vacca, J. (2005). Computer Forensics: Computer Crime Scene Investigation. 2nd ed.
- Carvey, H. (2011). Windows Registry Forensics. Burlington: Elsevier Science.
- AccessData. (2019). FTK Imager. [online]. Available at: https://accessdata.com/product-download/ftk-imager-version-4.2.0. [Accessed 20 March 2019].
- Guidence Software. (2019). Encase Forensics. [online]. Available at: https://www.guidancesoftware.com/encase-forensic. [Accessed 21 March 2019].
- D. Morgan, T. (2008). Recovering deleted data from the Windows registry. Science Direct, [online] pp.S35, S36. Available at: http://www.sciencedirect.com [Accessed 20 March 2019].
- Help.comodo.com. (2019). Windows Registry – Overview, Structure, Benefits, Registry Cleaner| Cloud Scanner Version 2.0. [online] Available at: https://help.comodo.com/topic-73-1-147-845-.html [Accessed 23 March 2019].
- Msdn.microsoft.com. (2019). Registry Hives (Windows). [online] Available at: https://msdn.microsoft.com/en-us/library/windows/desktop/ms724877(v=vs.85).aspx [Accessed 20 March 2019].
- Gliklich, R., Dreyer, N. and Leavy, M. (2014). Analysis, Interpretation, and Reporting of Registry Data To Evaluate Outcomes. Agency for Healthcare Research and Quality (US). [online] Available at: http://www.ncbi.nlm.nih.gov/books/NBK208602/ [Accessed 20 March 2019].
- Yang.S, et.la. (2013). A Method on Extracting Registry Information from Windows CE Memory Images. [online]. Available at: https://ieeexplore.ieee.org/document/6835701. [Accessed 25 March 2019].
- Zhang.S, Wang.L, Zhang.L. (2011). Extracting windows registry information from physical memory. [online]. Available at: https://ieeexplore.ieee.org/document/5764089. [Accessed 25 March 2019].
About The Author
 Chirath De Alwis is an information security professional with more than four years’ experience in Information Security domain. He holds BEng (Hons), PGdip and eight professional certifications in cyber security and also reading for his MSc specializing in Cyber Security. Currently, Chirath is involved in vulnerability management, Threat Intelligence, incident handling and digital forensics activities in Sri Lankan cyberspace. You can contact him on chirathdealwis@gmail.com.
Chirath De Alwis is an information security professional with more than four years’ experience in Information Security domain. He holds BEng (Hons), PGdip and eight professional certifications in cyber security and also reading for his MSc specializing in Cyber Security. Currently, Chirath is involved in vulnerability management, Threat Intelligence, incident handling and digital forensics activities in Sri Lankan cyberspace. You can contact him on chirathdealwis@gmail.com.