Binalyze AIR v1.7.40 is now available.
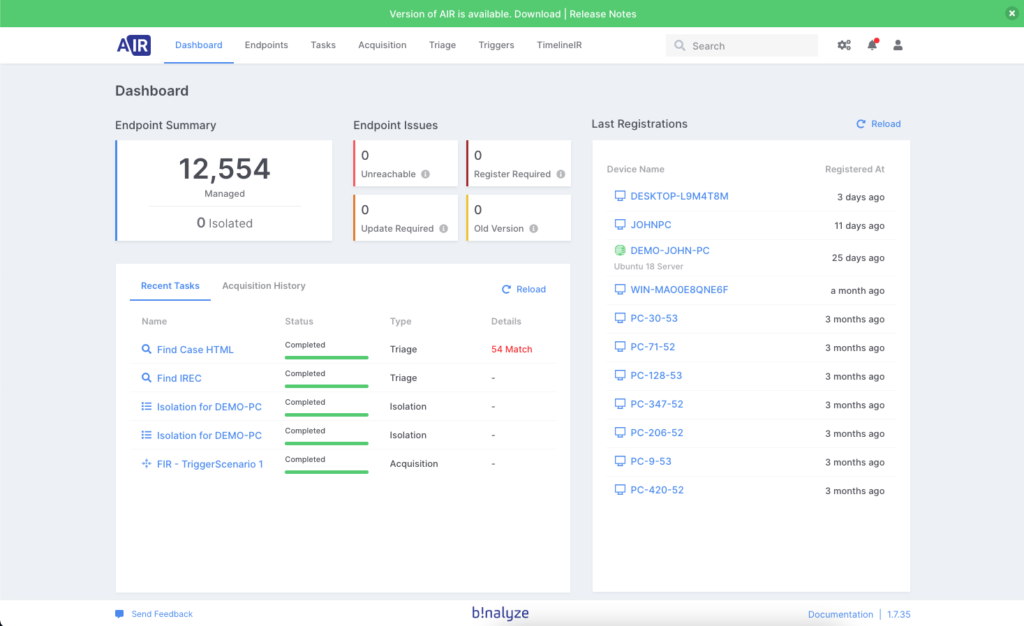
You can update directly from your product (shown below) or download it from the website here.
Product release highlights:
- Continued rollout of Linux support
- Enterprise-grade roles and permissions
- Bulk actions on endpoints
- IBM QRadar integration
Continued rollout of Linux support
After the first release of our Linux version 2.6.0, we are happy to release version 2.6.1 with additional new features parallel to our rock-solid Windows support.
New features
- Binalyze’s Triage support over AIR Console is now available in Linux using the robust industry-standard YARA rules. Both memory and file systems of Linux platforms can be scanned to identify indicators of compromise. Users can also set CPU limits to the triage process to have better control over resources. More will come in the following versions to take automatic actions in the AIR Console when any match is identified during scanning.
- Custom content profiles are now available for Linux platforms to acquire single or multiple files recursively. Shortly we will extend acquisitions to have Cloud uploads in addition to our current SFTP support. Stay tuned.
- We improved deployment automation with a well-crafted shell script to ease the first-time installations.
We would like to thank Hilko Bengen (https://github.com/hillu/) for his invaluable feedback about YARA internals. Hilko Bengen is the author of the famous go-yara (https://github.com/hillu/go-yara) library in the Go community and YARA contributor.
The upcoming version will support the Timeline feature and other automation processes. Stay tuned.
Enterprise-grade roles and permissions
Due to the importance and sensitivity of the data that an enterprise forensics tool, like AIR, collects to protect the network and keep it as safe as possible, it is always a smart move to have user/roles privileges defined. There are 78 privilege variables available in AIR, starting with this release, and more amazingly there is no limit on the number of role creations. Check the video below to see how it is easy.
Bulk actions on endpoints
In the previous versions, you were not able to select multiple endpoints at once and apply an action. Starting with this release, you can choose numerous endpoints and apply any type of task like triage or acquisition. On top of it, you can also tag selected endpoints and create a group. Check the video below:
IBM QRadar integration
QRadar is the one of the most widely used SIEM worldwide. For that reason, we decided to incorporate QRadar integration out-of-box into this product release to make daily DFIR duties more manageable and efficient. As you might already know, AIR can be integrated with any Webhook source but having an out-of-box integration makes things a lot easier.
How to integrate QRadar with AIR?
Integration of AIR with IBM QRadar is possible via a feature called “Custom Actions.”
- When QRadar generates an alert for an incident, it runs a script provided in Custom Actions,
- The properties of the alert, alongside some fixed properties, are then sent to the trigger URL provided in the bash script,
- Upon receiving the URL request, AIR extracts the IP address or Hostname from the URL and automatically assigns an acquisition task to the endpoint in question. The acquisition profile for this task is provided when you create a trigger.
A step-by-step guide on how to integrate QRadar with AIR you can find on this link.
IBM QRadar Security helps security teams accurately detect and prioritize threats across the enterprise. It provides intelligent insights that enable teams to respond quickly to reduce the impact of incidents. With QRadar integration, once you have an alert in your network, AIR automatically starts investigating the endpoint to provide you with the report. Bulletproof digital forensics at any time of the day or night.
The path to better enterprise digital forensics incident response management starts here.







