Feby Thealma, CEH, CHFI, Head of Blue Team at Protergo, reviews Binalyze AIR version 4.3. There have since been two further releases.
Even with the shift back to office-based work, the importance of remote acquisition capabilities in Digital Forensics and Incident Response (DFIR) cannot be overstated. In situations where physical access to data sources is impractical, restricted, or impossible, it ensures that digital investigations can proceed unimpeded. While many DFIR tools now offer remote evidence gathering, Binalyze AIR stands apart with its enhanced capabilities. It is especially useful in settings where investigators are inundated with high volumes of assets and cases within tight timeframes. The platform not only enables an automated DFIR response to triggers from the most common alert systems, but also integrates asset management and allows investigators to proactively engage in threat hunting at the same time.
Asset Management
Binalyze AIR is designed to accommodate the needs of investigators managing a substantial number of assets. For example, it offers an ideal solution for those working with or within Security Operation Centers (SOCs), enabling investigators to efficiently manage and continuously work with the assets registered in the platform.
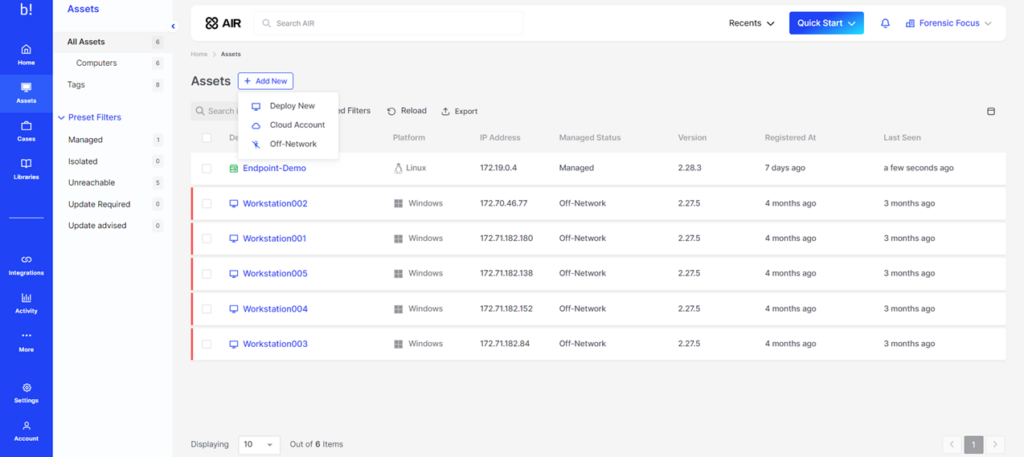
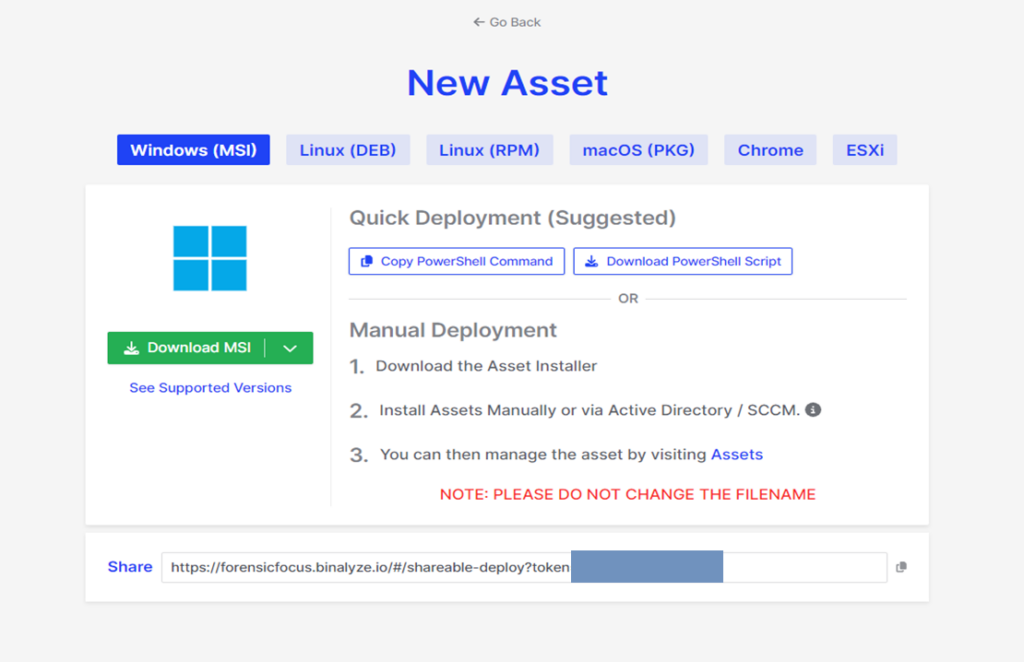
Registration of new assets into Binalyze AIR is very straightforward. The instructions are clear, and assets can be easily shared with other personnel through link sharing. Furthermore, the integration of Chrome and ESXi support is a significant feature, complementing the platform’s support for widely used operating systems like Windows, Linux, macOS, and IBM AIX. This feature is particularly useful in environments where SOC clients or corporations use a diverse range of operating systems.
Binalyze AIR also offers the functionality to incorporate off-network assets, enhancing its asset management and DFIR capabilities. AIR allows for task execution in the form of acquisition and triage on these assets and facilitates the retrieval of results back to the platform for analysis and reporting. There will always be limitations to continuous management due to the off-network nature of these assets but there will always be cases where the responder will need to deal with assets that have been removed from networks.
The simplicity of integrating Binalyze AIR is a major advantage, especially given the challenges of collaborating with various asset owners across a company and the potential difficulty in guiding them through a complex integration process.
Another positive we found is the fact that Binalyze AIR allows us to give tags to each asset and even provides a feature of auto-tagging. The tags can be fully customizable according to the user’s necessity. This feature gives proper identification and adds to filtering capabilities in managing all the assets registered. Imagine working with over a hundred registered assets and needing to be able to perform triage or acquisition on a specific business unit’s assets without the tagging and filtering feature – it would take hundreds of hours to identify the correct assets and ensure that none of the assets are left behind or skipped.
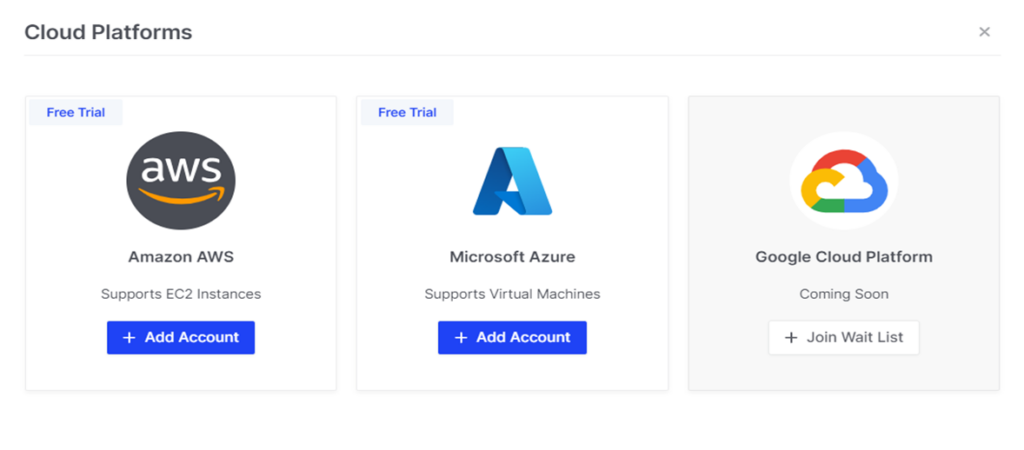
The capability to integrate with popular cloud services such as Amazon AWS and Microsoft Azure is very much welcome, particularly during the widespread transition of many businesses to cloud-based solutions. The only thing that Binalyze AIR needs to improve in this area is to enable integration with more cloud service providers from major players to niche ones.
Finally, before looking closer at the product’s current capabilities, I was pleased to see an on-screen notification of the upcoming integration of Google Cloud Platform assets (see screenshot below). Not only is this good news for practitioners who need this feature, but it also demonstrates a commitment to proactive communication and user-friendly design – always welcome in a forensic product!
DFIR Capabilities
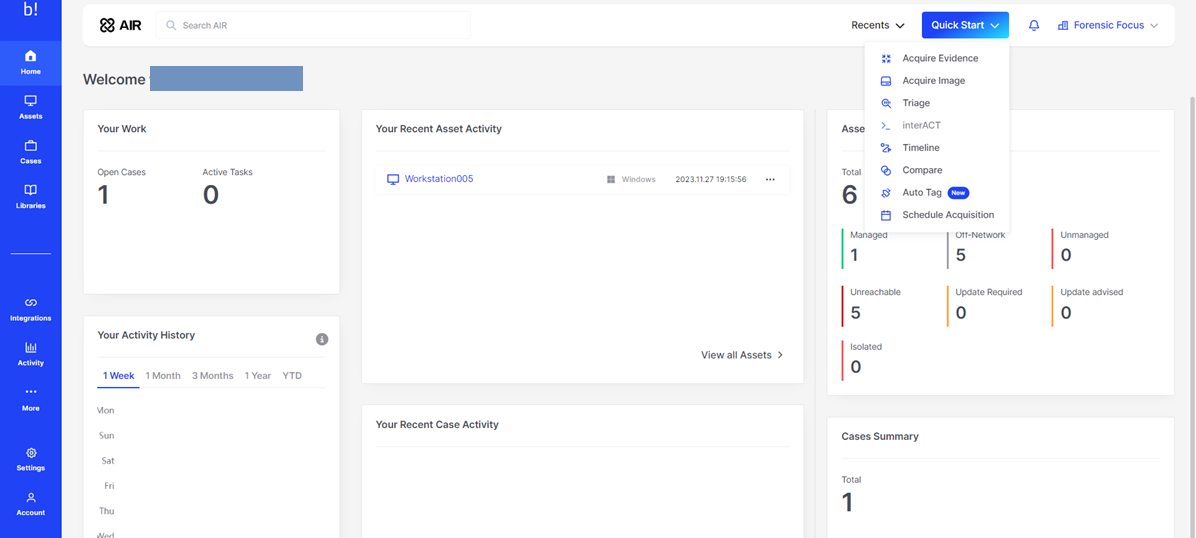
Binalyze AIR is, first and foremost, a digital forensic and incident response platform. Landing on the dashboard, the most eye-catching option here is the option to Quick Start. Clicking this button immediately shows us all the features and capabilities offered by Binalyze AIR.
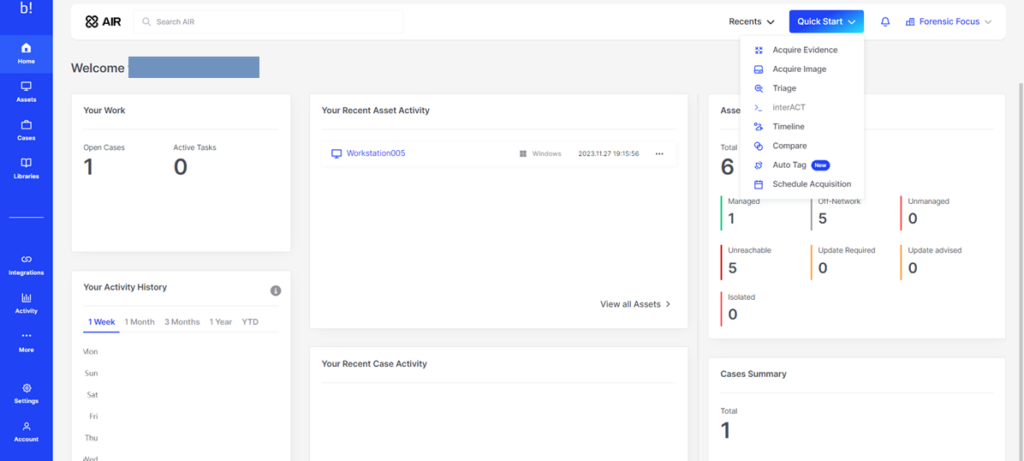
Acquiring evidence and images and creating timelines are standard functions in many DFIR tools. However, Binalyze AIR sets itself apart with its user-friendly, all-in-one approach, which includes features like scheduled acquisition. This is particularly beneficial for investigators who previously had to work overnight, waiting to start acquisition late in the day to minimize performance impact on the asset owner’s operations. Binalyze AIR’s scheduling capability significantly enhances convenience and efficiency in such scenarios.
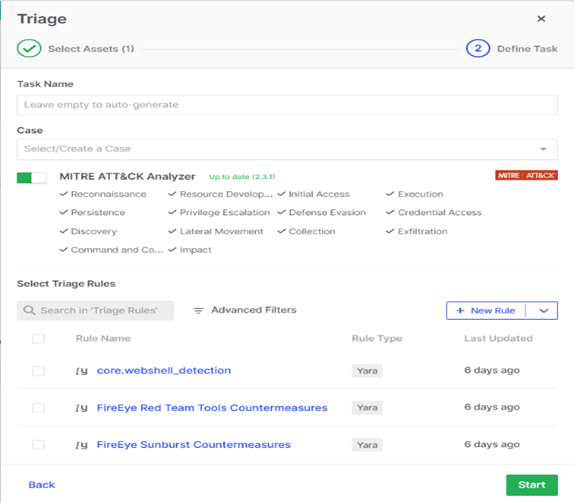
Triage is another interesting feature Binalyze AIR has to offer. Performing Triage on an asset lets you map suspicious processes or artifacts into a MITRE ATT&CK matrix, which gives you a complete insight into the incident or malicious artifacts. Additionally, Binalyze AIR allows you to perform Yara, SIGMA, and osquery scanning, and you can even add your own rules to scan for anomalies. This feature definitely helps in performing proactive threat hunting, allowing for the early detection of threats even before incidents or alarms are triggered.
Compare makes it easy for investigators to see what’s different between recently acquired evidence and previously acquired evidence. This feature offers rapid, non-intrusive artifact analysis. Utilizing a lightweight 5MB Baseline Acquisition, results are typically delivered in just 5 seconds. This targeted analysis focuses on critical system areas, including Autostarts, Installed Applications, Services, Firewall Rules, Hosts File, and Kernel Modules/Drivers—all seamlessly managed and viewed within the Console. This feature offers rapid, non-intrusive artifact analysis. However, to use this feature properly, investigators will have to perform frequent acquisitions periodically to ensure that there’s another image to compare the latest acquired evidence to.
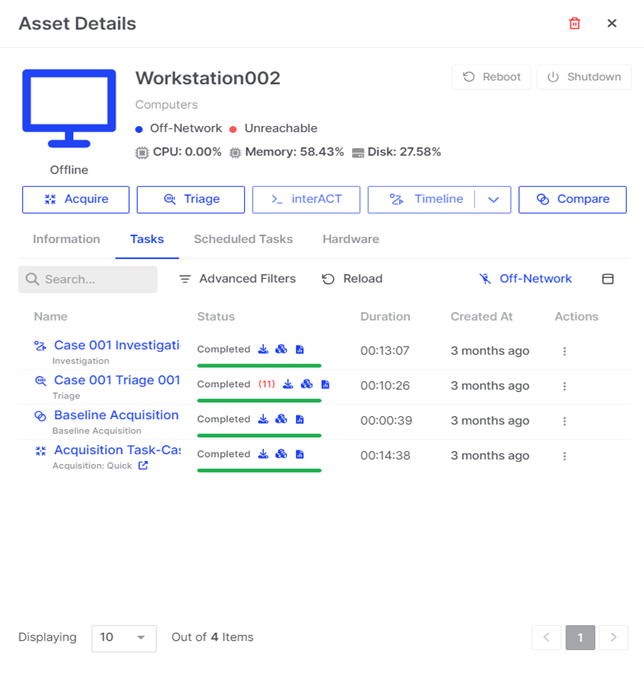
Aside from all the digital forensic capabilities mentioned above, Binalyze AIR also helps satisfy the need to mitigate a compromise on an asset. Through the dashboard, we can mitigate the incident by performing isolate, reboot, and/or shutting down of the asset, which is sometimes found lacking in asset protection tools.
The best part of all the DFIR capabilities provided in the platform is the capability to connect directly to the asset using Binalyze’s interACT module and to send out a standardized command set for Windows, macOS, and Linux in a secure cross-platform remote shell session. On top of that, everything in the platform is properly logged, hashed, and timestamped as we, digital forensic practitioners, know how much it means to have evidentially sound, complete, and proper logging on everything the users touch.
Investigation Hub
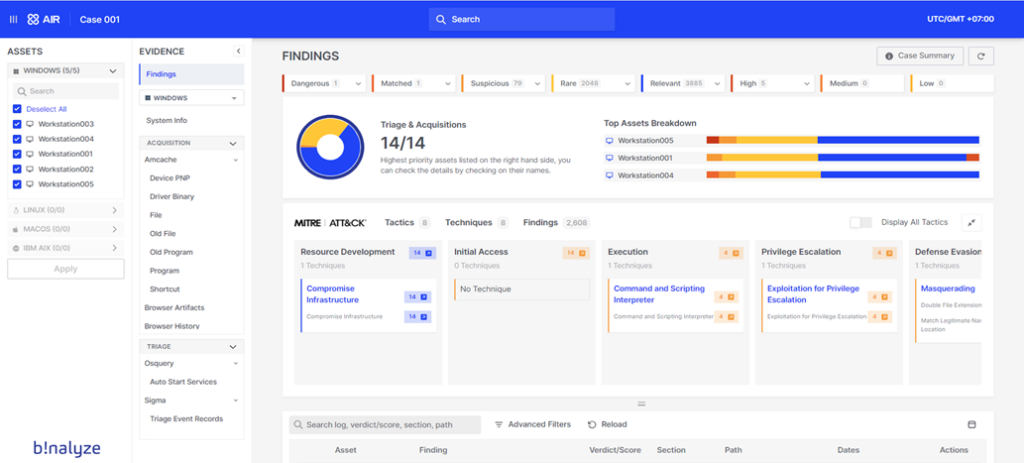
One of my favorite areas of the platform is the Investigation Hub. It’s here that Binalyze demonstrates that they understand the pain of investigators having to deal with multiple pieces of evidence. Typically, managing evidence from four or five devices can be feasible, but as the number of devices increases the task becomes significantly more difficult and time-consuming and the Investigation Hub helps to bypass that challenge.
When essential tasks performed on each piece of evidence are complete, such as acquisition and triage, investigators can promptly access the analysis results for all evidence in the case through the Investigation Hub. This not only accelerates the investigation process but also assists investigators in identifying which pieces of evidence are most critical or relevant to the case, thereby enhancing the efficiency and effectiveness of their work. Not to mention that the Investigation Hub also provides links back to each asset or evidence or endpoint’s individual report to provide more information in detail that can be easily navigated through.
In some investigations, I find myself wondering which piece of evidence I should start with. However, the Investigation Hub’s landing page simplifies this decision-making process. By presenting a clear breakdown of the top assets, it becomes straightforward to identify an initial focal point or ‘foothold’ for the investigation, streamlining the starting phase. Including the MITRE ATT&CK in the mapping of indicators of compromise (IOCs) was a smart move from Binalyze AIR to enable investigators to start off their investigation at an even quicker pace.
This Investigation Hub also provides a quick, clear, and comprehensive draft executive report, which is sometimes requested in the middle of investigations. Investigators can show the stakeholders the dashboard to provide a quick, concise explanation of the temporary findings and reports.
Another point to love in the Investigation Hub is the global search bar that can be used to search for specific terms across all assets in the case. This hastens the investigation by being able to correlate multiple assets at once through searching for specific items and/or terms.
Finally, some of the bigger benefits of the Investigation Hub include the emphasis on collaboration, offering restricted logins for team members to view, bookmark findings, and add notes. Users can also efficiently export the entire report, facilitating seamless sharing with colleagues or stakeholders for review.The capability to provide investigators with quick and seamless reporting is always appreciated, even more so when the format of the document is laid out beautifully. The January 2024 release, version 4.5, also offers the capability to automatically generate and customize reports with a company logo and other personalized attributes that companies and SOC clients might appreciate.
Integrations
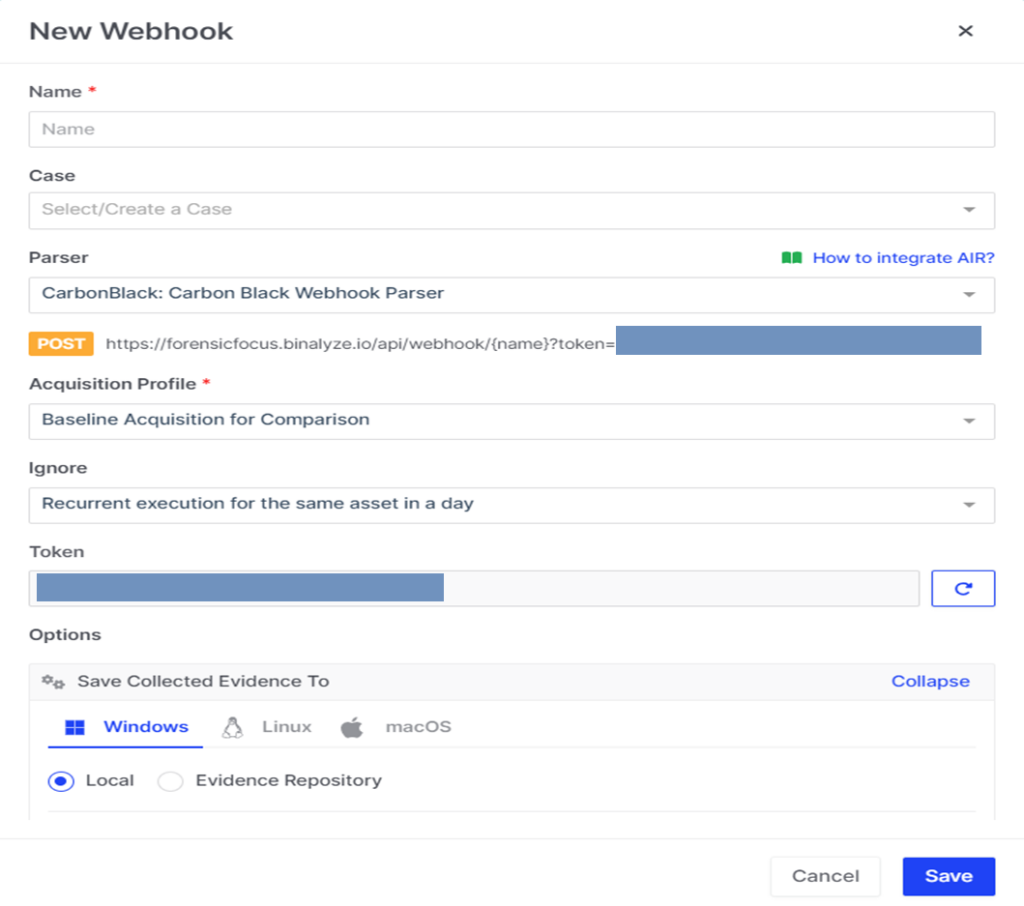
Binalyze AIR also provides investigators with the capabilities to integrate the platform with their own workspaces or SOCs via API, Webhooks, or directly to Cloud Platforms. Integrating Binalyze AIR enables investigators to automate DFIR tasks, as soon as a certain trigger or alarm is seen on the integrated workspaces or SOCs. Such integration capabilities demonstrate Binalyze AIR’s clear direction and understanding of its role in enhancing Blue Teaming within the broader cyber security landscape.
Closing Thoughts
With my experience in SOC-based investigations, I personally found Binalyze AIR’s features and approaches very useful. In a typical SOC setting for a single client, managing over twenty assets is common. Multiply this by the number of clients, and the challenge escalates to overseeing and understanding a vast array of assets, ensuring they are well-connected and updated. Beyond passive monitoring, it’s crucial to actively secure each asset through proactive hunting. This responsibility, while essential, can become increasingly demanding (and, at times, seemingly endless).
Each button is equipped with tooltips to aid investigators, and where tooltips aren’t available, detailed documentation is readily accessible within the platform’s menus. Overall, Binalyze AIR stands out as a comprehensive solution for managing connected assets, conducting active hunting, and executing rapid but thorough DFIR, particularly in SOC environments.