Julie: Hi everyone! Thanks for joining today’s webinar: remote mobile collections for corporate investigations. My name is Julie O’Shea, and I’m a product marketing manager here at Cellebrite. Now, I’d like to introduce our speaker today: Ashley Hernandez.
Ashley is vice president of product for enterprise solutions here at Cellebrite. She has worked in digital forensics for over 15 years. She’s taught and certified investigators in digital forensics and security topics, including speaking at many digital forensics conferences throughout the world. Thanks for joining us today, Ashley. If you are ready, I will hand it over to you now so you can get started.
Ashley: Thanks Julie. And thank you for joining us today. Our plan today is to go over a few of the background items and what are the challenges we have today around mobile collections, and then we’re going to move into some of the solutions that we’re going to be able to offer to help solve those challenges.
So we’re going to look at this both from the investigative perspective (from the investigator’s perspective) as well as from the employee’s perspective, and how we can make this process smoother, repeatable and more targeted to get the information that we need right in the way, and the method that we need it in.
So first let’s talk about the challenges of the last couple years. Even before COVID, companies had already started to change the way employees interacted with the collection capabilities. It does definitely vary, depending on if they were trying to collect from employees’ computers, or their mobile devices, or from cloud.
But having folks work in various locations (whether that was at their home office, or still going into headquarters), we knew that there were challenges in being able to get to the data on the devices that the employees had. The devices that were closest to employees have always been the most challenging, because they’re not just in a central location that IT has access to all the time. So this new remote working standard that we’ve really shifted into, and the hybrid working model with maybe people coming in some days, and not others, really has changed how we need to collect from these employees.
In addition to us needing to collect from them in different locations, there’s also different constraints that we see with folks working off of the corporate network. So that may be that they’re on a home connection to the internet with limited bandwidth, or you need to be concerned about how much data is going back and forth if they have to pay for access for that data to be transferred, as well as just the security risk with people not being on always corporate issued devices. They might be on personal devices, or devices that they bring themselves. So those are some of the additional challenges that this new working model has brought to corporations, and even when we’re working with service providers.
Originally we saw a lot of mobile devices issued by corporations as one of the challenges of “how do we acquire from those?” But beyond the corporate issued devices, we’ve seen a lot of shift and increase to BYOD devices, or devices that are provided by the employee or also contains the employee’s personal data, and the mixture of that data on the device, also causes challenges when we sometimes have to have the cooperation of employees to access that data.
So when we started to look at having employees working from home and mixing their data, whether it was on their computer or on their mobile device, it started to become a little bit of a legal issue of, “which of this data do we really need to have access to, and how do we get access to it?”
Now, we know when talking to customers that some of the ways they’ve worked around this is by shipping devices around. Whether that’s the employee’s device, or a collection kit, that might be a combination of software and hardware going to the employee’s location, and all of those have been tricky. Whether that involves trying to walk a custodian over the phone how to set something up, how to plug it in, and sitting with them through the whole process to make sure that it completed correctly, or just trying to convince the employee to hand over their device for a set amount of time, so that they could do the collection: none of those were optimal.
We were seeing that custodians were frustrated because they were willing to cooperate, but they didn’t necessarily want to have to spend hours getting the collection to complete. And we were seeing that the trend was definitely to collect everything on the device, because you really didn’t want to have to do this more than once. It was a burden on both the people who were doing the collection, and the people being collected from.
And the last is really just an increased need to be able to get data off of the employees devices that include mobile phones. So I think historically, we’ve seen things like collecting from email, and collecting from maybe document repositories, but now employees’ devices with messaging apps are also a critical piece of this picture. And so not only do we need to get this data more often, but it’s sometimes some of the most valuable data when we look at employee misconduct discussions, or when we’re looking at eDiscovery claims.
So all of these things are challenging for us, and we need a way to be able to gather the data from the employees with a minimal disruption to their day, but also getting just the data that we need, so that we can respect the privacy of the employees, where it’s important, or where it’s necessary, but make sure that we can access it in a timely manner without too much of an extended burden for these mobile collections on the team itself.
So this is where we’re gonna start to talk about how we’re enhancing our remote collection capabilities to really allow you to treat mobile endpoints more similar to how we treat computer endpoints. So we want to have a single solution, and this is what we’re offering to you, to be able to collect all of the data that’s closest to those employees. So whether it’s their computer, or their mobile device, we want you to be able to reach out and gather that data when you need it and really fit it to what you need for that particular case.
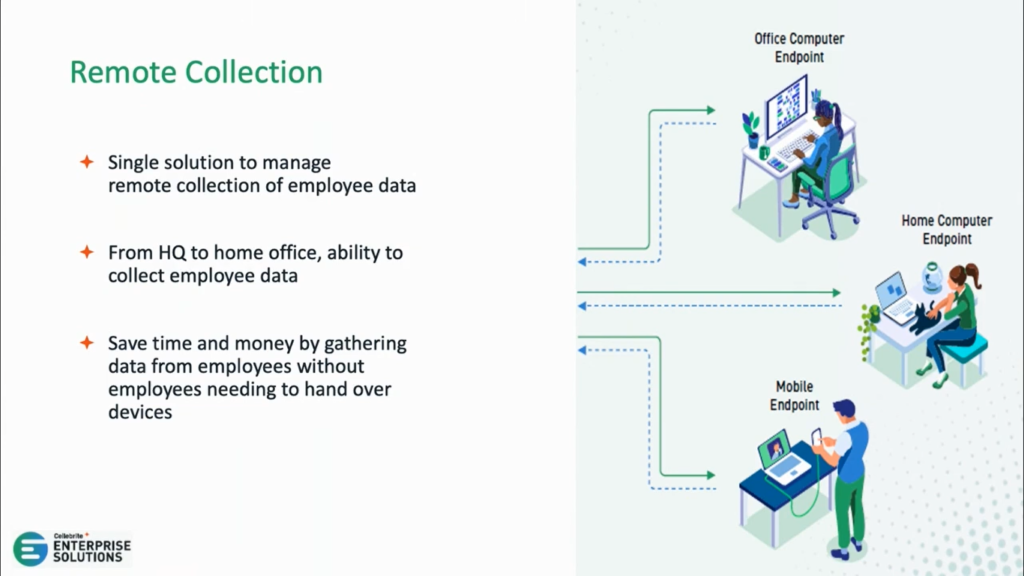
We want you to do this without having to send them any hardware (so no special cables), we want this to be able to be something that is brought together and you’re able to do it from a single interface, both the collection and then bringing that data together, so you can then review it, and without any disruption for the employee where they have to have…give up their device for days at a time or for them to have to sit through and kind of walk through the collection process with a technical specialist.
In addition, we want to provide the ability to give you some flexibility about what you collect. Because this is now going to be a process that is easier on the employee, we want to make sure that you get the choice of, “do you want that full collection, because that’s really what’s needed for a corporate investigation?”
You’re trying to see if there’s something suspicious happening, but you’re not necessarily targeting just one particular piece of evidence or type of evidence. Maybe you want a full collection in that case, and in that case we will give the option to do full collections. Or do you want to just collect specific messages? Or you know you’re going after and looking for pictures. We want to give you options as part of this remote collection capability to really narrow in on what you need.
And this also helps us by skipping data that either might be time consuming to collect. Say, you’re only interested in call logs and you’re looking at some of those records, well you probably then don’t need to spend the time to collect all the videos or pictures. You don’t need employees’ personal information shared with investigators if it’s not relevant.
So in addition to that, we want to make sure that in this instance we are going to be working with the custodian. So we’re not going to install anything on their phone to be able to do these collections, we’re going to involve them each time we want to reach out to them.
So we’re going to walk through in a minute how that process is going to work, but in general, these are four collections where the employee either, because they’ve consented to the collection (they know it’s an eDiscovery matter, for instance where they were part of it and they’re cooperating with us to help you know define the information that is needed), or we are going to reach out to them as part of a matter that we are going to be asking them to do a collection, maybe of their corporate issued device for other matters.
But the custodian would retain possession of the device, and they don’t need to hand over any credentials. So this makes it easier as we start to work with custodians who are going to have more say into what happens with their data, this gives us some flexibility and options to be able to let them know that this is what’s happening at the time of collection.
So this is going to be the general workflow when you have these remote mobile capabilities in your solution. And so, as part of our Cellebrite solutions, we now are going to have a user initiated collection for mobile devices, and it will work like this.
The investigator is going to go online and they’re going to set up a collection job. And in that job, they’re going to specify what they want to collect, from who they want to collect, and where they want to store the information. And then they’re going to have that all packaged into a nice set of settings that they’ll send to the custodian for the custodian to be able to run and complete the collection, and then that software will send the collection back for the investigator.
And so we’re going to walk through what that looks like from the investigator side, as well as from the custodian side. We’ll talk about some of the ways to make this easier both for the investigator and for the custodian.
So let’s start from the investigators workflow first. As you can see, we are inside of our endpoint inspector server that allows us to do collections for computers or for mobile devices.
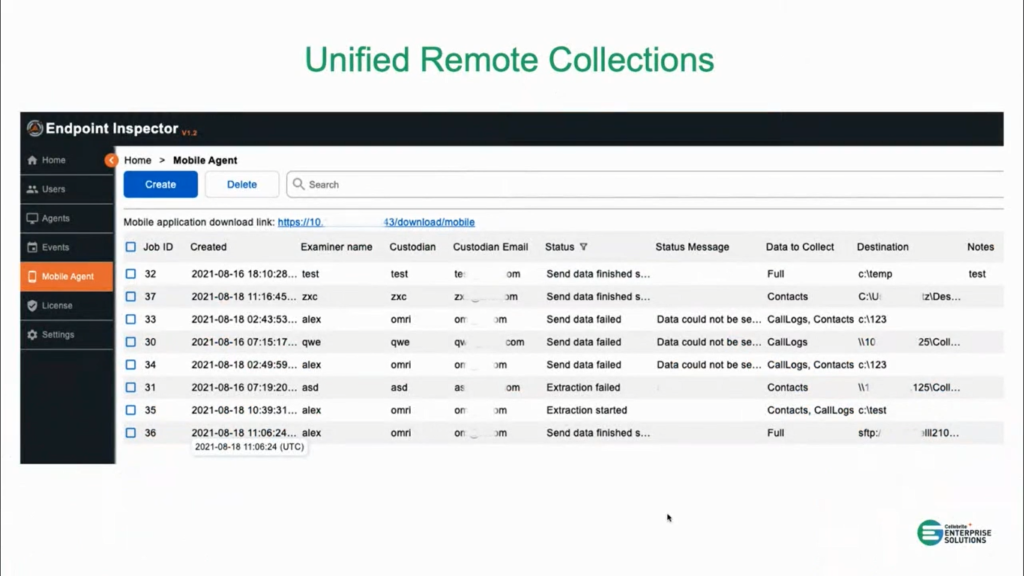
So, for custodian who has both type of devices, you would be able to set up the collection for both of those in this one interface and you’d be able to start moving forward with those collections. But today we’re really going to focus on the mobile collections, and that’s what you’re seeing here.
So here’s a list of jobs that are set up on our sample test data, (as you can see this is test data). And what we are going to do here is be able to see a status of the jobs that are already running, what we collected from them, where we stored that information, if it had any issues or failures, and what happened. But essentially, you’re going to be able to see a status of the mobile jobs you’ve already started, and then you’re going to be able to choose to create a new job.
So when an investigator is creating a new job, they’re going to be able to set up some of the settings that’ll all get packaged in when it goes to the custodian. So this gets set in advance by the investigator, and it is going to be transparent to the custodian: the custodian can’t change these, or modify them, they’re just going to get the application to run to do the collection, and all of this will be embedded inside of it.
So it will set who did the collection (the examiner’s name), as well as a password for the collection output, and what data to collect. We’ll talk about that in one minute. We’re also going to put in the custodian’s name, as well as the email address for where we’re going to send this information to, and finally where we want to send the collected data to. So once the collection is complete, where do we want to send that data?
So when we talk about the data that we want to collect, as we mentioned in the beginning, we want to give you the option to either gather all the data (so that would be the first option), or if you knew you just wanted call logs or you just wanted SMS and MMS, you could really narrow in and just collect specific categories that were of interest.
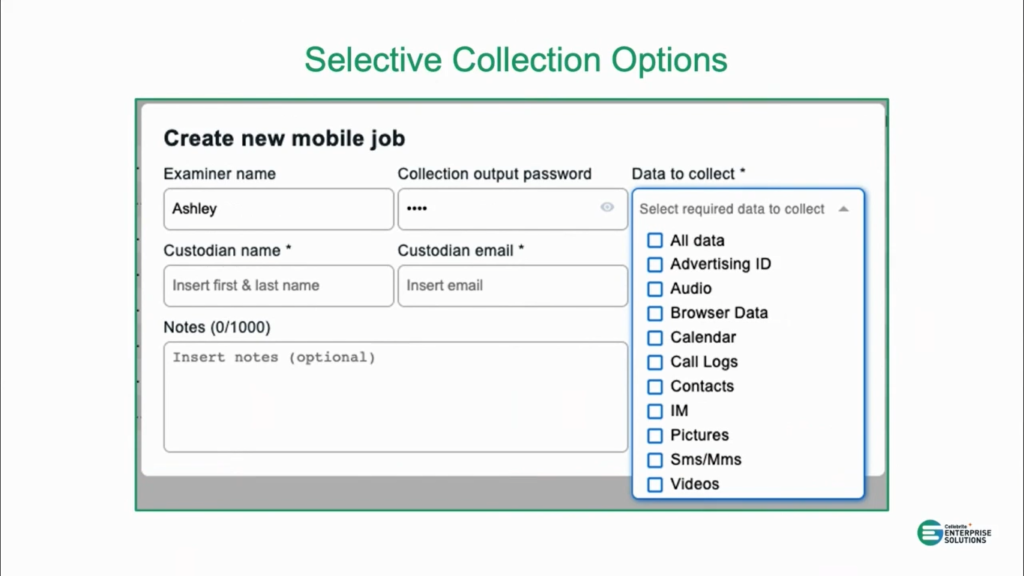
Now, again, before we know that folks were probably tending to do full collection, because it could be difficult to reach back out to an employee and ask them to do a subsequent collection if there was more data that was needed. But we do think that because this process will be easier both on the investigator and the custodian, if you want to be more selective you can really narrow in on these types, so that you’re only gathering the information that you really need. And if you do need to go back to the custodian later (or the employee later), you could do that in a pretty straightforward manner.
But these are the options. If you were to choose all of the options down below, and not choose all data, that’s actually a little less data than all data. So all data is everything that we can get, and then those individual options are subsets of that. And then you can also provide notes about maybe, why you’re doing this collection, or what authorization you got to do that type of collection. So I’m going to take a pause here, and Julie, do we have any questions before moving on to the employee workflow?
Julie: Yes, we’ve had a few good questions come in so far. Let’s touch on a few of them. How about: what type of collection is done, and what format is it stored in?
Ashley: So, the collection is very similar to our advanced logical collection, and it’s going to store it in a standard Cellebrite format. It’s actually going to be temporarily in a .zip, but you’ll be able to add it to any of the Cellebrite tools that you have today to be able to analyze it.
Julie: Great, thanks for elaborating on that. How about: can I collect from multiple phones at the same time?
Ashley: Yea, so if we were to look at this status of what the collections are doing, these are all done independently. So, you set them up, and then you’re able to send the collection information to the individual employees, and you can have as many of those collections running as you want. Since they do actually run the collection on the employees machine, and then they’re going to copy the files back, you’re able to run them all at the same time if you wanted. So if you had 10 different employees you needed to collect from, you could actually collect from all 10 of them at the same time, and you’d be able to get the results back at the same time.
Julie: Great, thanks Ashley. Let’s keep going, and we’ll answer some more at the end of the webinar.
Ashley: All right, sounds great. So, now we’re going to talk about what we’re going to experience from the employees perspective. So, again, we know that right now either the main choices that we hear customers say that they’re using to collect from employees’ mobile devices is: 1) the employee maybe has to hand over their phone, you maybe have to schedule something for it to get to headquarters; or you need to ship something with licenses to the employee and then you have to walk them through the collection.
So we want to bridge that gap with a technical solution designed for people who don’t do mobile phone acquisitions every day. So, we want to make it as smooth as possible for them to complete the collection without having to enter any extra information. So all of that is going to come over to the employee when they get the link to download the collection application, and inside of that application is going to also have the settings for the collection itself. So they won’t have to know which buttons to push or what they’re supposed to do. They’re going to get that all sent to them with an activation code.
So this is what’s going to look like when they run the application. So they’re going to run the application, and they’re going to be asked for an activation code. So that would be created at the time you create the job, and so you can copy that activation code to them and they’ll be able to copy and paste it in to authenticate.
And this is really what ties the collection to the job that you created. So the investigator creates the job, and all the settings with the activation code, and then when the employee launches the application, they enter the activation code and will be able to make sure we have all the settings properly set up for the employee.
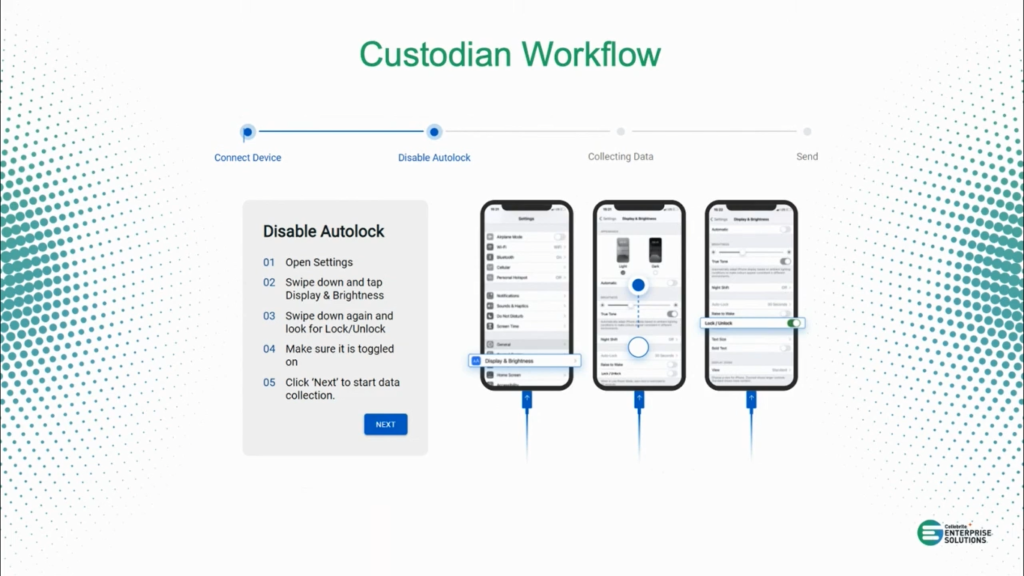
So they’ll enter the activation code, and once it authenticates, it’s going to give them on-screen prompts for how they should complete the collection. So, again, we don’t want to ship them any cables, we want to just use what they have, their regular data cables that they own with their phone. And so it’ll tell them to go ahead and connect their device and once we notice that the device is connected we’ll go ahead and move to some settings that will need to be done on the device itself.
So the first thing that we’re going to need to do is disable the unlock. Again, we don’t want to have to have them sitting there and kind of touching, tapping, wiggling the screen so that it stays on. And so we will show them how to walk through to disable the unlock. In this example it is on an iOS device.
And I know that there are some concerns about folks who have MDMs, and so if you do have MDMs that you’re working with we actually do have a white paper on how to work with MDMs, so if you’d like that afterwards, please just let us know. But in general, we want to move through the settings and we’re going to give them prompts like how to disable the unlock. And then once that’s done, we’re going to start to collect the data.
So at this point they’re going to start to see a progress of the data being collected on the screen. So we’re going to show them what’s being collected, at a very high level here on the screen. And at this point the data is actually being stored. And you will also get a status as the investigator on where it’s at as far as the collection’s going. So they’re running it on their system, but as it’s collecting we can actually see the status of if it started.
And we don’t send that information back and forth too often, but we want to be able to say, “hey, it looks like they’ve plugged in and they’re starting to work on it and they’re not stuck.” If it does have any issues we will also report back if we were able to do the collection, or if there was an error somewhere along the way, so that you would know you might need to reach out to that employee and give them some additional instructions.
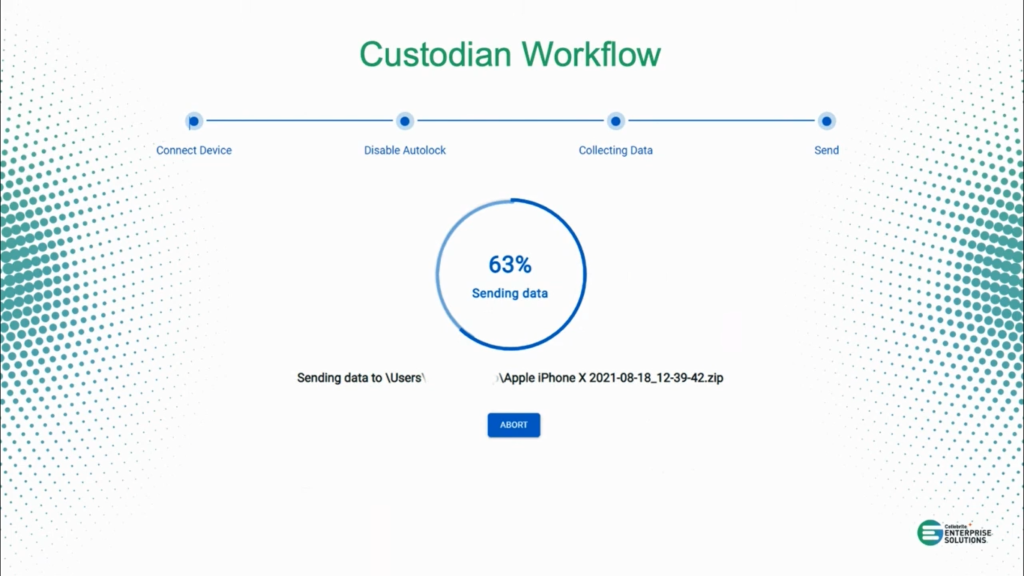
So once the data is collected, then we’re going to send the data back so that the investigator can complete the next phases, whether that’s doing an analysis of the device for corporate investigation, or exporting that information out for legal review. We’ll have a separate step that allows them to take the data and upload it so that it goes back to the investigator.
And at this point, hopefully no investigators had to reach out or or talk to them, they should be able to make it through these steps on their own. But we do have documentation to help them in case there’s anything that comes up that they don’t expect.
So at the very end they will get a successful message. Again, nothing was put on their device so there’s nothing for them to undo, other than knowing that they’ve finished the collection successfully. You would also get a message on the investigator side that would also show that it finished successfully.
All right, so just to summarize, and then I’ll answer a few more questions. The remote mobile collections are new capabilities that we’ve added to our Cellebrite enterprise solutions, and this capability will allow you to acquire a device without having to send the device, or any licensing, or anything separate, to the employees.
We talked at the beginning about how this does provide you more flexible collection options, so you now have the ability to do full collections, or start to narrow in and target on specific features. And also, we covered that there’s nothing that’s getting installed on the mobile phone itself.
And then finally, we went over the guided workflow that we provide for custodians, so that they can independently complete these collections, and have that data sent back for analysis. So with that, Julie, are there any questions that we have on the remote mobile collection?

Julie: Yes. So, how about: where’s the data stored when it’s collected, and can I send it directly to our server?
Ashley: OK, so, the data itself, when the employee is plugged in their phone to their computer, is going to be stored temporarily on their computer. That way we make sure we get the collection completed before we try and do any transfer.
So when it’s stored on the computer, once it’s finished being extracted from the mobile phone, you actually could choose to disconnect the phone at that point. We would have the collection, and then it would continue to upload wherever you set the collection to go.
So in this instance, we have the options currently to allow you to set it to a network share that the employee might have access to, or using something like SFTP to have a secure connection where you’re going to be sending it to. And then as we continue to develop the capabilities, we’ll give you more options for maybe file sharing type applications that you might want to use to upload those collections.
But they will need enough space to be able to store the collection temporarily on their system, and that’s another reason why we do know some folks are choosing to do a more targeted collection first, and then they’ll see if they need to do that kind of full collection.
But also as a note, it doesn’t necessarily have to be the employees machine, there could be a machine that was set up that was just used in that location to do these. Because each time the person logs in to do a collection, they’ll be able to put in their authorization code, and that will tie that employee’s device to the job that was created and the collection that is subsequently created. So, yea, I think that answers that question.
Julie: I think so too. Thanks for clarifying. All right, how about this one: what happens if the collection fails? Can I try to collect from the phone again?
Ashley: OK, so, if during the collection it fails and we get an error, say, they didn’t disable the lock screen, because maybe they weren’t able to, and they didn’t keep it active and so somehow it disrupted the collection, they will be able to restart the process. They could go back and start over the collection again.
So that’s an option. It is going to start from the beginning, it’s not going to pick up from where they left off (at least not in this first version). And then if it actually really can’t upload: so, say, you’ve done the collection, but you weren’t able to get the upload for some reason, maybe it’s too big of a file, you keep losing connection. You can choose to have the custodian choose (or the employee choose) to move the collection to a file share using a different way, or they could put it on a hard drive and ship it back, worst case scenario…old sneaker net!
But ideally, the upload methods that we provided would let you have that work, but if all else fails, once it’s collected it is there for them to be able to move manually if they need to.
Julie: That’s helpful, thank you. And, this is a good one: which phones are supported?
Ashley: So, today we’re showing the iOS devices, and those will be the first that are supported but Android’s coming shortly thereafter. In general we’re going to focus on smartphones, because those are going to be the phones that are most likely used for business purposes.
But if there’s specific phones that your company has, or needs to give access to, please let us know. Either let me know, from the product side, or you can let salesfolks know if there’s specific questions on what we support beyond those two.

And I did have one other question that I saw, which was about the application that we’re sending: is it the same for every employee’s computer? And the application itself that’s going to be running is the same, so the hash would be the same on every employee’s machine that’s going to be running the remote collection capabilities.
So if you were in an environment where you can’t run certain applications unless they’ve been approved, you would be able to approve the application that’s running so that it would run on all of them, because it will have the same hash value. The settings are kind of sent on the side, so it doesn’t affect the running hash. Just wanted to make sure when I saw that one on the list too, that that was covered.
Julie: Great, thanks. That was really helpful. So, I know we have had a few more questions come in that we didn’t get a chance to answer throughout the presentation, but we will reach out to everyone individually after the webinar to answer those. I’ll be sharing those with Ashley.
And just as a reminder, if you would like to get started with our new remote mobile capabilities, you can reach out to our sales team via the sales inquiry URL in your console. And I want to send a big thank you to Ashley for walking us through the really powerful new remote mobile collection capabilities we have, and showing us how those features can really help accelerate your corporate investigations going forward. And thank you all for joining us today, and hope everyone has a great rest of your day.