Today, digital forensic investigators must be adept at extracting evidence from an array of devices, each with unique structures, operating systems, storage capabilities, and security features. A case involving a desktop computer, for example, may require an understanding of operating systems, file systems, and data recovery techniques. Conversely, a case involving a smartphone may call for expertise in mobile operating systems, encryption, GPS technologies, and app data extraction. In network or cloud-based investigations, understanding data transmission, network protocols, cloud architectures, and multi-tenancy environments becomes critical. Thus, the device or system at the center of the investigation often shapes the strategy and methodologies employed by the investigators.
In this article, we will delve into the various types of digital forensics. We will explore the obstacles investigators face when extracting information from different types of devices, as well as the rich and varied types of evidence these devices can yield. Finally, we will discuss the increasingly recognized necessity of a holistic approach in digital forensic investigations, where multiple devices and techniques often come into play. This holistic strategy not only increases the effectiveness of investigations but also allows for a more adaptable, versatile approach in a world where technology is ceaselessly evolving.
Types of Devices
Digital forensics is not a one-size-fits-all discipline; it branches out into several areas, each addressing a specific kind of device or system. Below we’ll take a look at some of the key types.
1. Computers and Laptops: The first stage in computer forensics involves the preservation of data, carried out by creating a forensic image of the system’s storage devices. This process is typically conducted using a write-blocking device to ensure data integrity. The forensic image is then analyzed for files (both existing and deleted), browsing history, metadata (including timestamps and file ownership), system logs, and email correspondence. These elements can provide crucial evidence regarding the use, ownership, and purpose of the device.
Challenges in computer forensics primarily stem from encryption and anti-forensic techniques. Modern computers often utilize full-disk encryption, which can prevent investigators from accessing the data without the correct encryption key.
Encryption is a critical tool for protecting personal or commercially sensitive data. It is a cornerstone of electronic security technologies, used by businesses, governments and individuals … in some forms it may hamper digital investigations.
UK Parliament Office of Science and Technology
Anti-forensic techniques, such as data wiping, data hiding, and obfuscation, can also be employed to complicate the investigation. Tools and strategies such as file carving, keyword searching, and hash comparison can help overcome these challenges.
2. Smartphones and Tablets: Mobile device forensics can yield a wide array of evidence, including call logs, SMS/MMS messages, app data, GPS location data, browsing history, and multimedia files. The extraction methods range from manual examination to logical and physical extraction using forensic tools like Cellebrite UFED, Oxygen Forensics, and XRY. Physical extraction provides a bit-by-bit copy of the entire memory, potentially recovering deleted items and hidden data, whereas logical extraction retrieves files through the device’s operating system, providing a structured view of the data.
Smartphones and tablets pose unique challenges due to their wide range of operating systems (iOS, Android, etc.), numerous device models, and rapidly updating software. Also, advanced security measures like encryption, biometric locks, and secure containers pose hurdles for investigators. Cloud data associated with these devices, while a potential evidence source, adds another layer of complexity, often requiring legal measures to access.
3. Network Devices and Servers: Network forensics focuses on monitoring and analyzing network traffic. Investigators can capture network packets in real-time or from saved logs, using tools like Wireshark or tcpdump. Analyzing these packets can reveal suspicious activities, data exfiltration, or malicious network anomalies. Network devices also store log files, providing a record of network events, while servers may contain user data, website logs, and databases.
Tracking and attributing network activities to specific individuals can be challenging due to network address translation (NAT), proxies, VPNs, or anonymizing networks like Tor. Another challenge is dealing with the high volume of data and isolating relevant information. Furthermore, evidence might be distributed across multiple devices in the network, requiring synchronized investigation.
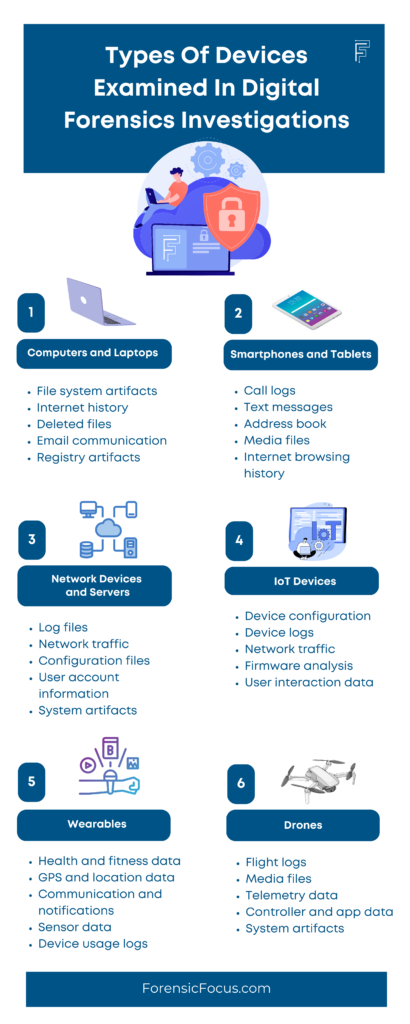
4. IoT Devices: IoT devices can hold sensor data, network logs, and user profile information, all of which can serve as potential evidence. Depending on the device, this might include data like temperature readings, video footage, audio recordings, or GPS data.
The forensics process for IoT devices is relatively new and challenging due to the sheer variety of devices, each with unique operating systems, data formats, and storage capabilities. They often lack built-in data preservation mechanisms, and many do not store data locally long-term, instead transmitting it to a paired device or cloud service. This necessitates extraction from multiple sources and potentially dealing with real-time data capture.
5. Wearables: Wearables can hold valuable digital evidence such as user profile and activity data, GPS data, heart rate, or even sleep patterns. The forensic process relies on syncing the device with a forensic workstation and extracting data using specialized tools or direct memory access, if supported.
However, wearables present unique challenges for digital forensics due to the variety of manufacturers, each with proprietary operating systems and data formats. They often sync data to a companion app on a smartphone, or cloud storage, resulting in the data being constantly overwritten and updated, making historical data difficult to recover. Additionally, many wearables encrypt stored data, which poses an additional challenge to extraction.
6. Drones: Drones can offer telemetry data, flight logs, videos and photos, and controller input commands. The memory chips in drones and associated controllers can be forensically imaged and analyzed for this data, which can reveal the drone’s flight path, altitude, speed, and movements. Some drones also come with integrated or attachable cameras that can capture high-quality videos and photos, potentially used as evidence.
Parties in litigation seeking to prove wrongdoing often find important evidence, clues and traces by analysing activities stored on drones, including flight routes and their creation and landing locations as well as photos the drone has taken, whom has operated it, the controller ID and metadata.
DIGITPOL
Drones present significant challenges in digital forensics due to their proprietary nature. Understanding the specific drone’s data structure, storage system, and transmission protocol requires specialized knowledge and tools. Privacy concerns related to drone operations and their surveillance capabilities add to the legal and ethical complexities.
7. Vehicles: Modern vehicles come equipped with numerous onboard computers known as Electronic Control Units (ECUs), responsible for various functions like engine control, navigation, communications, and more. A subset of these, Event Data Recorders (EDRs), can provide information about vehicle speed, brake usage, airbag deployment, seatbelt use, and other crucial event data before, during, and after a crash.
Vehicle forensics involves specialized tools to interface with these ECUs through the onboard diagnostics (OBD) port and other connections, and interpret the extracted data. The proprietary nature of these vehicle systems and the multitude of manufacturers and models significantly complicates the process. Also, many vehicle systems encrypt their communications for security purposes, which can pose a challenge for forensic extraction.
8. Medical Devices: Medical devices such as pacemakers, insulin pumps, and various health monitors can provide patient health data, usage logs, and configuration information. The forensic process often involves using proprietary software provided by the manufacturer or specialized hardware interfaces to extract this data.
However, the field of medical device forensics is fraught with challenges. Many devices employ encryption to protect patient data, requiring specialized knowledge or manufacturer cooperation to decrypt. Also, given the sensitivity of health data, there are significant legal and ethical considerations surrounding its extraction and use.
9. CCTVs: Closed-circuit television systems can provide video footage, access logs, and configuration data. Typically, forensic experts acquire data by extracting the hard drive from the Digital Video Recorder (DVR) associated with the CCTV system and making a forensic copy.
CCTV systems present a unique set of challenges. For instance, video data is often recorded over on a loop, making older data harder to retrieve. Advanced techniques might be needed to recover deleted or overwritten footage. Furthermore, processing and analyzing video footage can be time-consuming, especially in high-resolution systems where the data sizes can be enormous.
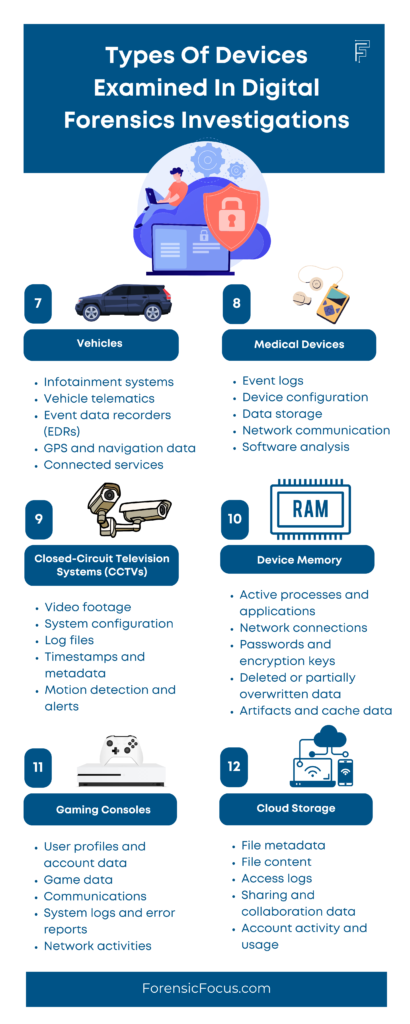
10. Device Memory: Device memory, or RAM, holds a wealth of volatile data, including running processes, network connections, login sessions, and even fragments of user data. Live system forensics can be performed to capture this volatile data, often involving careful order of volatility-based evidence collection and the use of specialized tools like Volatility or Rekall to create memory dumps.
Memory forensics is a highly specialized field, requiring expertise to correctly interpret the data structures and remnants of activity within a memory dump. The volatile nature of RAM means that valuable evidence can be lost if not captured quickly and properly. Furthermore, some areas of device memory may be protected or encrypted, posing additional challenges for investigators.
RAM is a very useful and extremely fragile thing. Any interaction with the system, even the smallest one, can lead to irreversible consequences. For this reason, one of the most important challenges in memory analysis is data preservation.
Packt
11. Gaming Consoles: Gaming console forensics is an increasingly relevant aspect of digital forensic science, given the rise of internet-connected gaming platforms like PlayStation, Xbox, and Nintendo Switch. These consoles often harbor a wealth of personal user information, making them viable sources of digital evidence. Data stored on a gaming console can include user profiles, chat logs, friends lists, saved game data, screenshots, and even credit card information. Furthermore, consoles are often used to browse the web or connect to social media, which may leave additional trails of digital evidence. With the growing utilization of cloud services, additional user-specific data can often be recovered from linked accounts and external servers.
However, the process of extracting this information is not without its challenges. Different consoles have distinct operating systems and proprietary hardware, which require specialized tools and techniques for forensic analysis. Data encryption is commonly employed in newer consoles, adding another layer of complexity. Furthermore, there is the issue of volatile data – information which can be lost or changed if the console is turned off or restarted. As with any form of digital forensics, maintaining a chain of custody and ensuring that evidence is not unintentionally altered during the investigation process is critical. Consequently, gaming console forensics is a field that requires both a high degree of technical skill and a thorough understanding of legal considerations.
12. Cloud Storage: Cloud storage forensics is a significant facet of digital forensics that focuses on retrieving and analyzing data stored in cloud-based services like Google Drive, Dropbox, or iCloud. This type of forensics can reveal a vast array of valuable information such as file activity records, user activity logs, and metadata related to created, accessed, or modified files. The analysis can further uncover deleted files, previous file versions, or even trace shared files between accounts. Given the extensive use of cloud storage solutions, such information can prove crucial in diverse investigations ranging from corporate espionage to personal disputes or criminal cases.
Despite the potential for rich data extraction, cloud storage forensics also presents unique challenges. Privacy laws and differing regulations across countries can complicate the process of obtaining required legal permissions to access cloud data. In addition, the decentralized nature of cloud storage, which often involves data redundancy and distribution across multiple servers possibly in different geographical locations, can complicate data recovery. Encryption used by cloud providers presents another hurdle, as it can make direct data acquisition difficult. Lastly, the volatile nature of cloud data, where files can be easily modified or deleted, also creates the need for timely and methodical investigations to preserve and recover valuable evidence. As such, cloud storage forensics demands a nuanced understanding of technology, law, and international relations, making it a complex yet vital domain within digital forensics.
Developing A Holistic Approach
With the varied types of devices and systems involved in digital forensic investigations, a singular approach often proves insufficient. A more encompassing, holistic approach is necessary to conduct an effective and thorough investigation. This involves considering all the digital devices and systems relevant to the case and understanding how data from each device contributes to the overall picture.
The advantage of a holistic approach is that it enables investigators to piece together disparate bits of evidence into a cohesive story. For instance, network logs may indicate a cyber intrusion, computer data may reveal unauthorized activities, mobile data could provide proof of communications related to the crime, and cloud data might store relevant documents or files.
In an era where digital devices are intertwined with our daily lives, investigations that take into account the full range of these devices are far more likely to provide a comprehensive understanding of the activities in question. This not only enhances the robustness of the investigation but also increases the admissibility and weight of the evidence in court proceedings.
Throughout this article, we’ve examined the different types of digital forensics, highlighted the challenges inherent in extracting information from different types of devices, and explored the myriad types of evidence that can be derived from each device. We’ve seen that each type of device offers its own unique challenges and rewards, necessitating a diverse skill set and a deep understanding of a range of technologies.
Some of the major technical challenges, associated with digital forensics are encryption, a huge volume of data, and incompatibility among diverse forensic tools.
IntechOpen
This has led us to the understanding that a singular approach to digital forensics is often insufficient. Multiple devices and techniques are often used in investigations, necessitating a holistic approach that considers all the digital aspects of an individual or entity’s activities. It is not enough to merely examine a computer or a mobile device in isolation – in many cases, these devices are interconnected, and the activities on one may impact or inform the activities on another.
















Very informative and well written.