Remote acquisition of digital devices is a useful option for modern-day organizations, both commercial and government. The main reasons for this are as follows:
- As entities grow, their IT environments tend to become more complex, distributed, and dispersed.
- Cost-efficiency may not allow organizations to hire trained IT security employees for all the locations.
- Ongoing business processes should not be interrupted; correspondingly, devices cannot be stopped and taken away.
- Sensitivity concerns make it preferable to acquire images in a confidential manner, for both investigations and monitoring.
This is why remote acquisition is a must-have nowadays: it reduces costs, increases transparency, and does not interfere with your workplace climate when it is not needed.
General Outline
Acquiring a remote device image with Belkasoft Evidence Center (BEC) is straightforward. The process looks like this:
- First, you need to deploy an agent to a remote computer. BEC provides you with two deployment options: remote and local.
- Second, you can acquire an image of the PC. In addition, you can collect data from RAM and mobile devices connected to the PC.
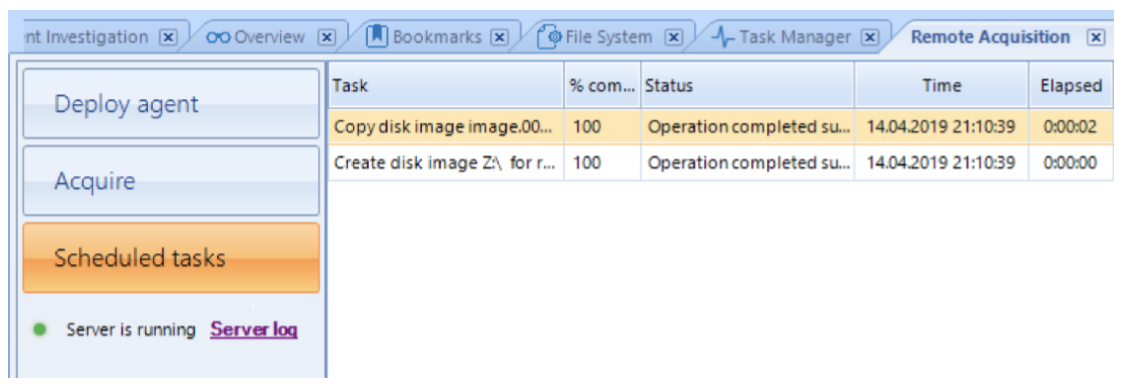
- Third, you can schedule an image to be uploaded to the central storage of your choice at a specified time.
How To
Click on the ‘View’ main menu item.
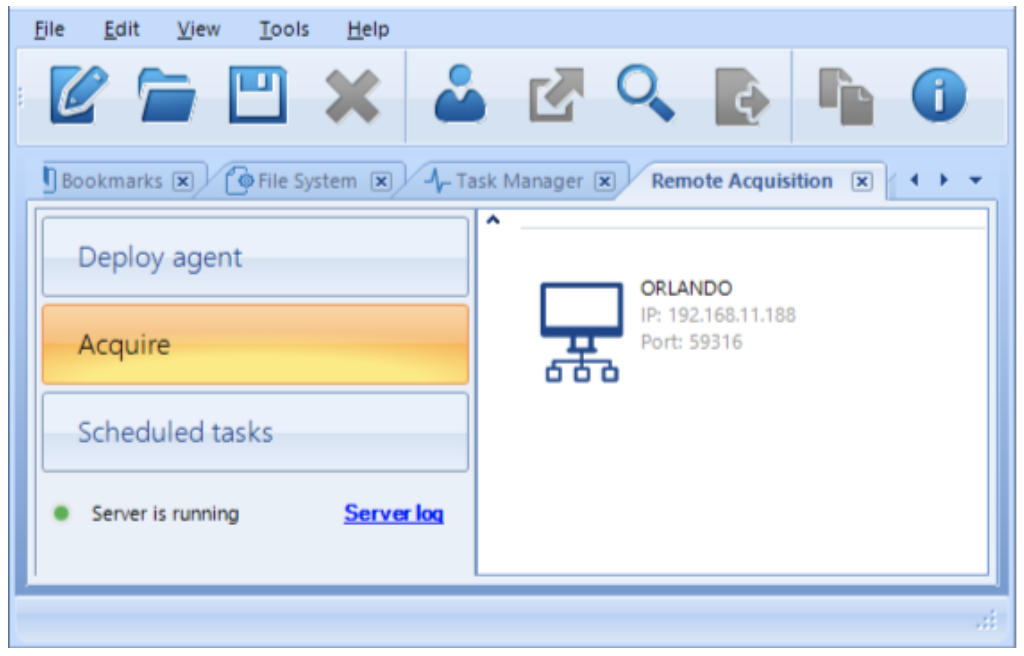
Then click on ‘Remote acquisition’. The following screen will be shown:
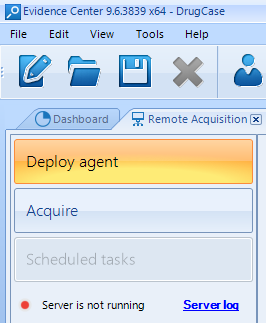
If you have not deployed the agent, do so using the ‘Deploy agent’ button.
Once you have clicked ‘Deploy agent’, there will be two kinds of agent deployment with Belkasoft Evidence Center:
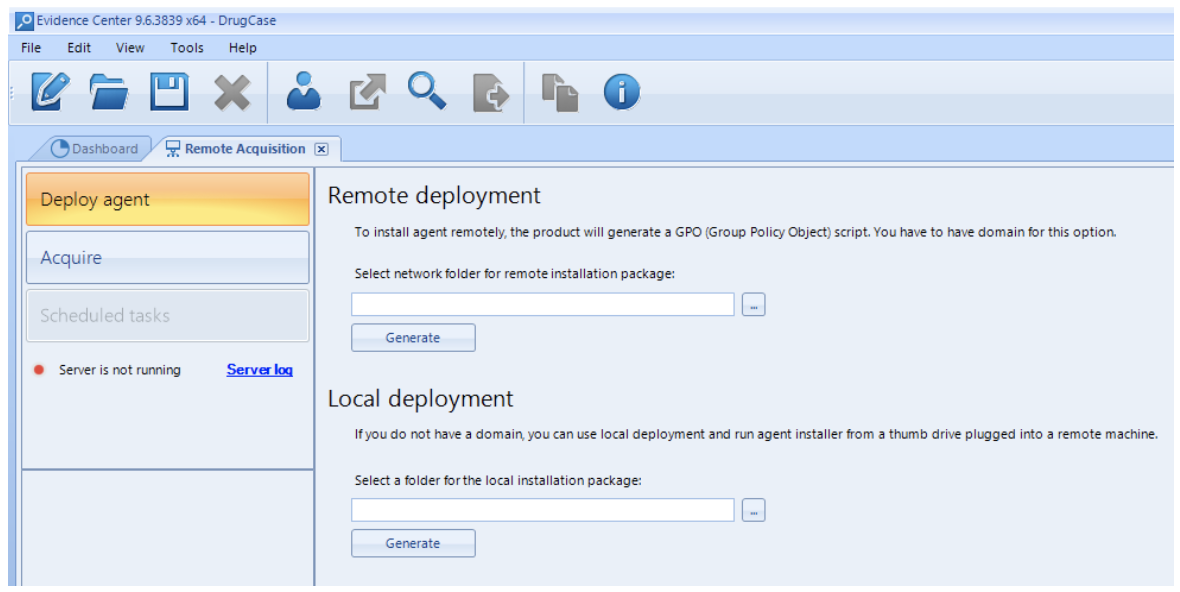
You may opt for ‘Remote deployment’ if you have a Windows domain that includes both your main computer and the remote one. In this case you need to select a network folder on the upper ‘Generate’ button. BEC will create a script which can be run to deploy your agent.
Otherwise, if you have no available Windows domain, your option is ‘Local deployment’. You need to choose a folder on your own computer and click on the second ‘Generate’ button in this case. As a result, a set of files will be generated which should be passed to the computer of interest via network folders, a thumb drive, etc. After that, the agent executable file should be run on such a computer.
After you complete the previous stage, you can launch the process of acquisition by clicking on ‘Acquire’ and selecting one of the available agents from the list on the right.
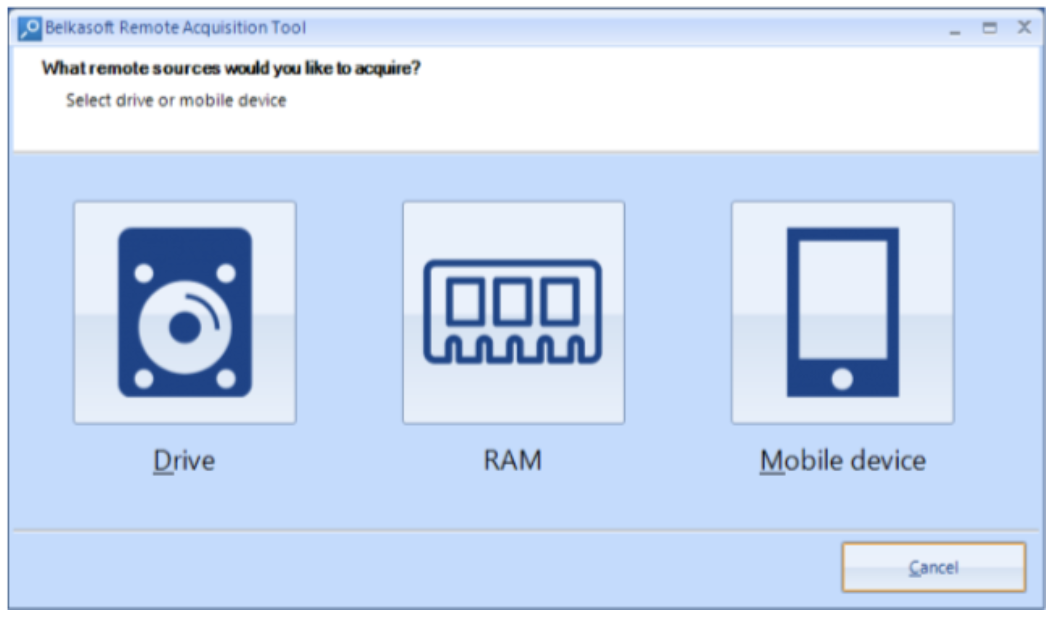
Images of hard drives, mobile devices, and RAM can be acquired:
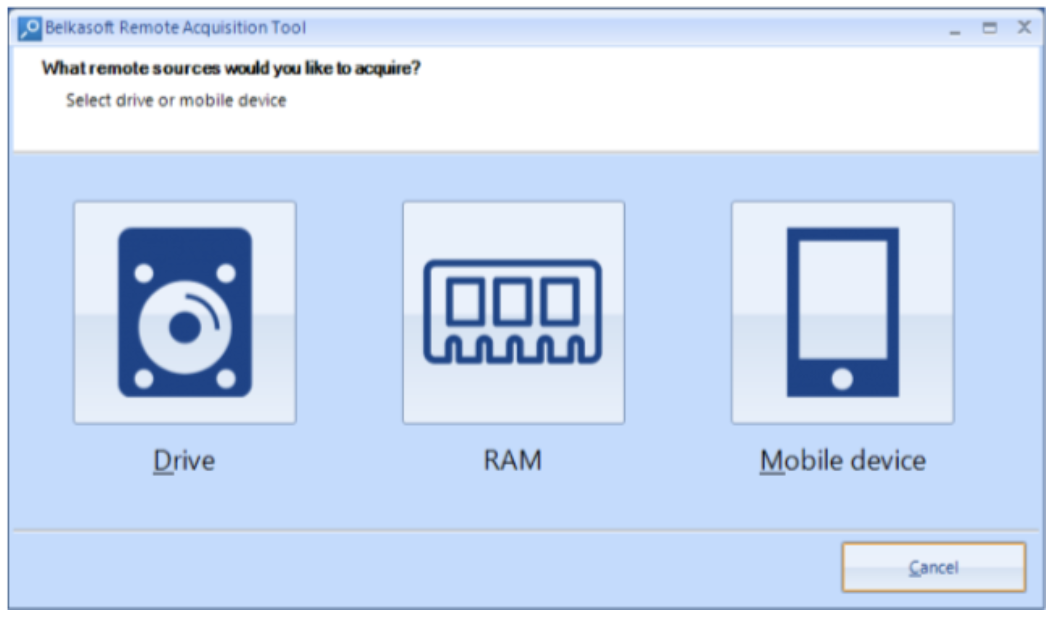
Please remember that hard drives and RAM can be acquired unattended, while mobile devices need to be connected to a computer; it is also necessary to unlock them and follow the standard route such as ‘trust this device’, ‘enable developer mode’, etc.
Let us assume that you would like to acquire a hard drive image. Once you have clicked on the ‘Drive’ button, you will see the following screen with a range of options:
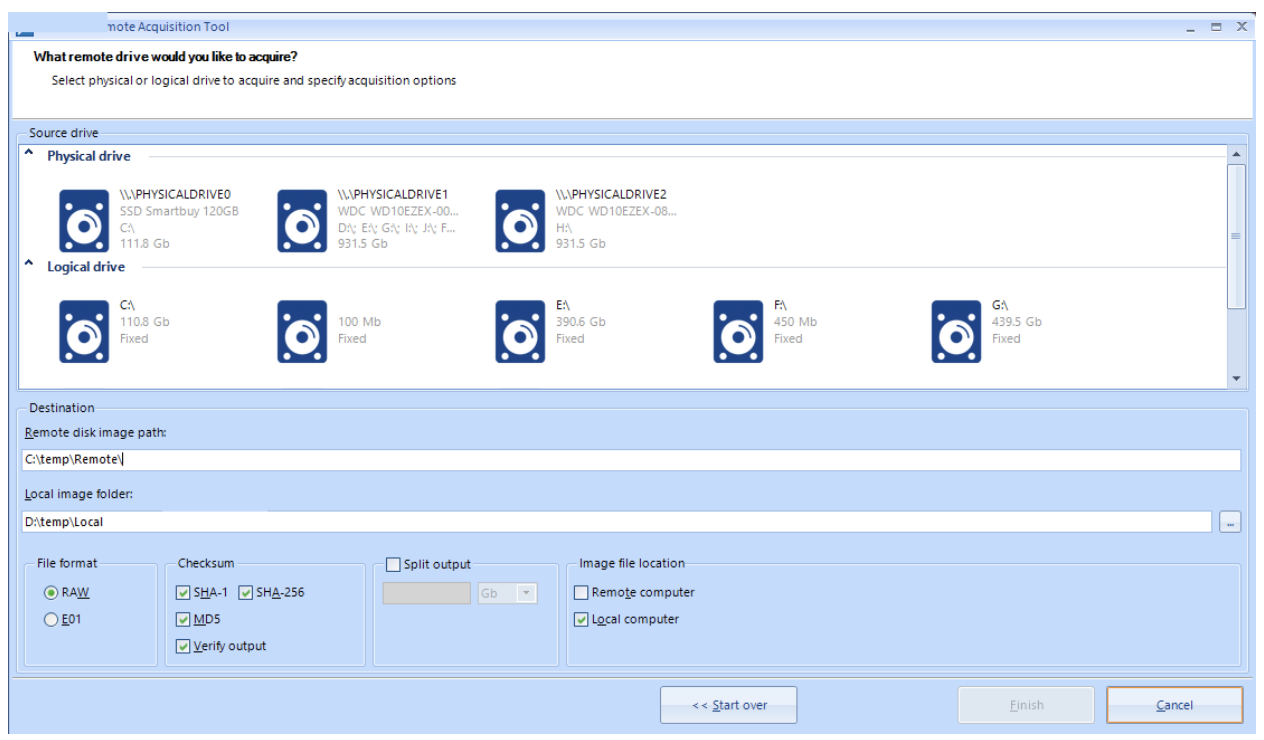
- ‘Source drive’. Here you can choose a physical drive or a logical one (of course, they mean remote drives connected to the computer of interest).
- ‘Destination’. You can select a location for the acquired image on both a remote computer and your local one.
- ‘File format’, ‘Checksum’ and ‘Split output’ output work the same as for a drive acquisition.
You can schedule your image for uploading. We recommend scheduling it for nighttime, especially if you would like to upload several images at once or just one big image, otherwise your (and your colleagues’) connection quality may degrade.
Conclusion
Belkasoft Evidence Center makes it easier and more cost effective to acquire digital images of remote devices. An agent is required to be deployed on a remote machine. Hard and removable drives, and memory of a running Windows machine can be acquired. A unique feature of remote acquisition of mobile devices is supported. Uploaded images can be then analyzed with BEC on a central machine.
The acquisition process is short and transparent. Using BEC, organizations with different structures, varying resources, and dispersed locations can get access to the data they need.
If you would like to try the remote acquisition, download BEC at belkasoft.com/get. The trial allows you to deploy one agent with full features.