This article is a recap of some of the main highlights from Techno Security TX 2018, which took place in San Antonio, Texas from the 17th-19th September.
The conference had four tracks: forensics; information security; audit / risk management; and investigations, along with sponsor demos. Forensic Focus attended the forensics and investigations tracks during the event.
Monday September 17th
Magnet Forensics’ Jessica Hyde opened the conference with a discussion on the proliferation of devices. With 20 billion connected devices projected to be online by 2020, this is a growing concern in the industry. And considering that the results of our latest survey show that data triage is one of the biggest challenges investigators face, it’s certainly a topic that requires attention. Hyde also mentioned the importance of verification and validation in the industry.
Validation and verification are particularly important in machine learning within #digitalforensics. We need to make sure we're capturing what we actually want to see. – @B1N2H3X at #TechnoSecurityTX
— Forensic Focus (@ForensicFocus) September 17, 2018
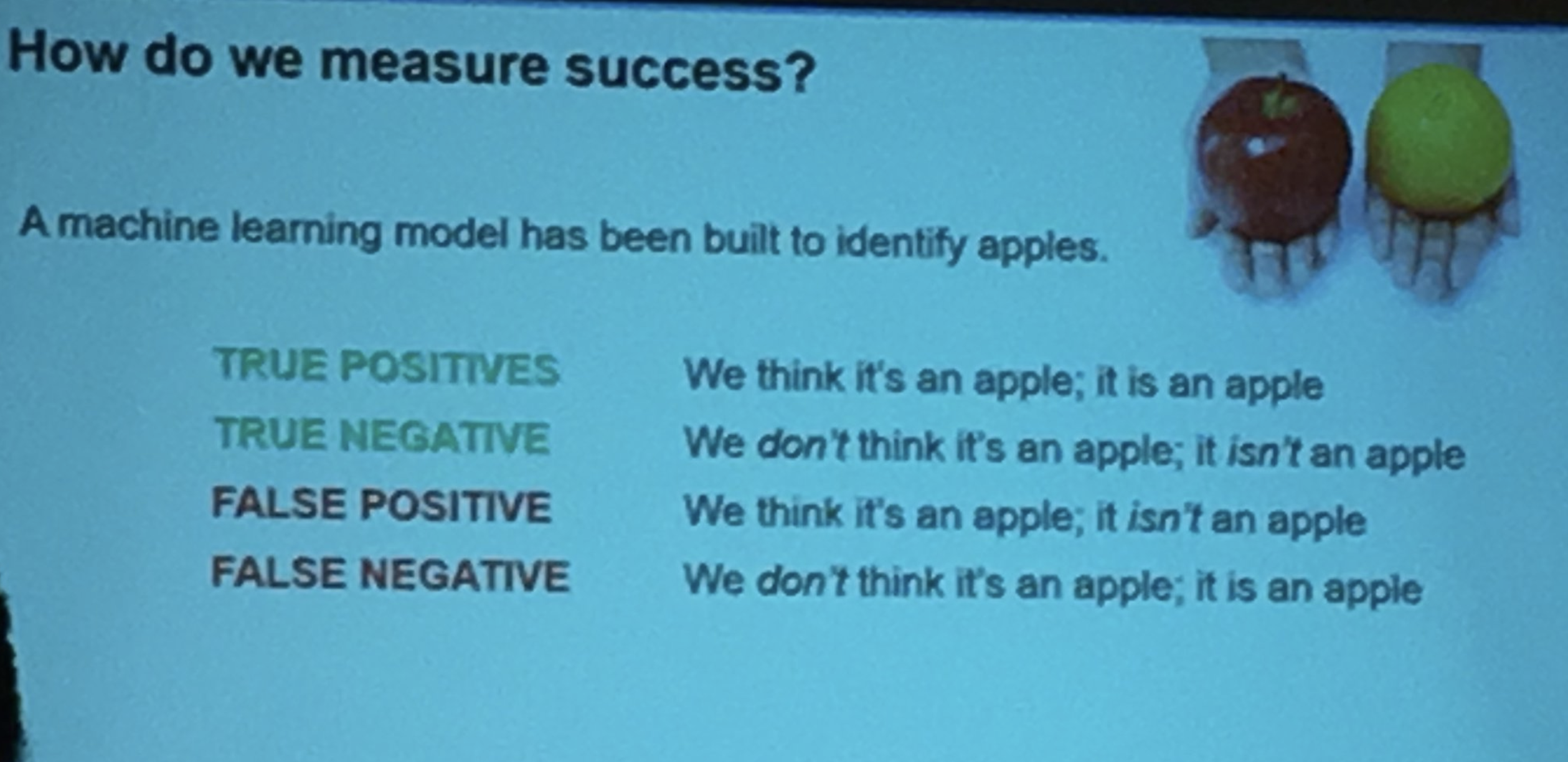
But how do we measure success in machine learning? This handy slide was a useful reference point.
For anyone who’s still not sure about the potential applications of machine learning, some of those featured in this talk included identifying things that fell outside the norm, for example finding unique patterns in network activity which may help you to find a bot or intrusion.
Presenters from Digital Intelligence then took to the stage to talk about the forensic analysis of cloud storage. Increasing amounts of personal and professional data are stored in the cloud, with options such as iCloud, Dropbox and Box.com growing in popularity. The reliability of dates and times was one common challenge encountered when forensically analysing cloud accounts, but we also learned some of the positive applications of cloud forensics.
Goals of cloud analysis:
– determine if the user has cloud accounts
– find out if files are being downloaded
– work out whether files are being synced
– understand what file activity you're looking at: accessed, changed, deleted
– recover relevant data. #TechnoSecurityTX— Forensic Focus (@ForensicFocus) September 17, 2018
Retired FBI agent Matteo Valles then spoke about how every industry is affected by theft of trade secrets, and how many stakeholders don’t take this area seriously enough. Sometimes people don’t even realise their companies have trade secrets, but they all do; it simply means whatever information you don’t want your competitors to have. This could be anything from new machine learning algorithms to your customer list. Other examples of trade secrets include software, source codes, research & development data, product specs, prototypes, future products, marketing plans, recipes, algorithms, merger & acquisition plans, customer lists, pricing info, suppliers & vendors, and formulas. As you can see, the area covers a multitude of subjects! And with instances of FBI cases concerning trade secrets having increased 100% since 2009, it’s very important to make this a priority for your business.
What is a trade secret? Info a company keeps secret to maintain an advantage. Three elements:
– Has actual / potential economic value
– Not generally known to the public
– Company takes reasonable steps to protect it. #TechnoSecurityTX— Forensic Focus (@ForensicFocus) September 17, 2018
Nick Drehel, the VP of Training at AccessData, ran a session demonstrating how their Quin-C tool can help accelerate investigations using collaborative methods. Quin-C speeds up data processing and analysis time and has a flexible, customisable user interface that aids investigators particularly in larger cases.
Tuesday September 18th
Abdul Hassan’s talk on counter terror analysis using social media was as popular at this chapter as it was in Myrtle Beach; if you get a chance to see it, it’s well worth going along. Hassan’s vast experience in the industry makes this a fascinating delve beneath the surface of counter terror investigations.
ADF’s Richard Frawley spoke about best practices for on-scene investigations, which can be hampered by non-technical investigators who may not understand how to best preserve digital evidence. Triage once again came up as a challenge:
Digital forensics is constantly evolving, and we need to get to the evidence faster. 90% of cases can be solved with 10% of data; not all cases are 'deep dive' worthy. #TechnoSecurityTX
— Forensic Focus (@ForensicFocus) September 18, 2018
Jamie McQuaid from Magnet Forensics showed attendees how AXIOM can be used in fraud investigations. Now that fraud, like most other industries, has gone digital, it can be harder to trace what’s been happening and ultimately end with a conviction. One of the main ways investigators find the details they need is by uncovering a hard drive or storage device that was previously unknown to their client; but knowing where to look and what to look for is paramount.
At 10.30am a panel discussion was held on the topic of women in cyber security and digital forensics. This was a fascinating discussion in which five women talked about their experiences in the industry, how to address the challenges faced, and how to encourage the next generation.
Some of the excellent advice given included:
- Always get a mentor – and not just a mentor, but multiple mentors, because they’ll help you to get out of your own head and figure out the right path.
- If you can’t achieve something, have a plan B, plan C, plan D, and keep going until you reach something you can do.
- If you don’t wake up jazzed in the morning about where you’re going [in life], then it’s time to move on.
- Find yourself, where you belong, what works for you, and go with it. Be honest with yourself.
- Remember that it’s OK to ask for mentorship, and it’s OK to offer it.
This marks the second recent discussion about women giving back in DFIR, after the Women In Forensics lunch which Forensic Focus co-hosted with Magnet Forensics at DFRWS in Rhode Island. It’s heartening to see this trend towards inclusion in the industry, and that so many people are enthusiastic about finding out how they can give back and help the next generation. Jessica Hyde wrote an excellent article back in July detailing some of the practical ways in which you can help.
In the afternoon Jamie McQuaid took to the stage again to discuss mobile device investigations and how to look for data on the mobile devices of the future. One of the main issues he pointed out was the number of investigators who don’t understand what their tools are doing, so are stumped by new updates to operating systems or apps.
It is important to separate acquisition problems and analysis problems, but this can be challenging especially in mobile forensic investigations. #TechnoSecurityTX
— Forensic Focus (@ForensicFocus) September 18, 2018
McQuaid also pointed out that not all images are created equal. It is very important to understand what is included in the image you’re currently acquiring; both app-level and device-level encryption will have a significant impact, but things like this are overlooked surprisingly often. He also highlighted the importance of not being dependent on one single tool but instead having a number of different options in your arsenal, since no one tool can possibly keep up with all the device and application updates that are constantly being released.
Encryption was the number one challenge mentioned by respondents to our survey, and it’s partly due to a lack of knowledge about encryption techniques that people miss out on data they might otherwise have been able to acquire.
There are two different types of application-based encryption you may encounter:
(1) Encrypted databases & files, where the whole file is encrypted, and it can’t be opened with typical tools prior to decryption. (2) Encrypted content, which is a little more forgiving.
When an app says ‘end-to-end encryption’ they usually mean ‘encryption in transit’; there will often still be unencrypted data on the device. It is always worth double checking this when conducting your investigations, because you may be able to acquire more data than you’d thought.
Following on from this, Joe Sylve discussed the importance of snapshots in APFS investigations, which can be viewed as a webinar here if you missed it. Amber Schroader from Paraben then spoke about smartphone processing and the kinds of app data investigators should be able to find.
Wednesday September 19th
In another talk that was previously given at Myrtle Beach, Mark Spencer showed what happens when a high stakes failure occurs in digital forensics. Again, this is a presentation not to be missed: the scale and scope of the investigation in question is fascinating, and its effects far-reaching!
Meanwhile we learned about what data can be gleaned from Alexa and other voice-based assistants, which collect much more data than the average user probably realises. Jason Hale followed this with a talk about USB device forensics and how we can improve this area.
Traditionally #DFIR investigators have looked at disparate parts of Windows system to identify whether a USB device has been connected. Data extracted include things like serial number, description and connection times. #TechnoSecurityTX
— Forensic Focus (@ForensicFocus) September 19, 2018
Chuck Easttom kicked off the afternoon sessions by discussing dark web markets and how to investigate them. This took the audience on a whistle-stop tour through some of the most nefarious sites around and gave a brief overview of how it might be possible to catch their owners. He also discussed some ways for investigators to keep themselves safe whilst working on dark web cases.
If you're investigating on the dark web, make sure you use either a VM or a different physical machine; ideally both. #TechnoSecurityTX
— Forensic Focus (@ForensicFocus) September 19, 2018
The final session of the conference looked at G Suite products and how much data can be found on these. Essentially it depends on the level of product bought; G Suite Basic only goes back six months, whereas the more advanced options store data for much longer. However it is still possible to acquire a fair amount of data even from G Suite Basic accounts:
Using the Google API, on G Suite Basic you can get data such as last login time, size of data in account, number of docs viewed, number of docs trashed, and more. So if you come across a Basic account in investigations, don't just assume you can't find anything. #TechnoSecurityTX
— Forensic Focus (@ForensicFocus) September 19, 2018
If you do need to look at G Suite data in an investigation, Google’s online API explorer may be helpful.
The next chapter of Techno Security will take place in San Diego, CA from the 11th-13th March 2019. Next year’s Texas event will once again be held in San Antonio from the 30th September-2nd October, and the South Carolina chapter will be right in between these two, in Myrtle Beach from the 2nd-5th June. Find out more, submit your papers and register to attend on the conference website.