by Laurence D. Lieb, Managing Director, HaystackID.
The subjects we will be covering include:
- Defining When One Should Reasonably Panic
- Reasonable Triage Steps to Take in Order to Identify if There is Only Smoke or an Actual Fire
- The Importance of Defining “Win” Upfront and the Avoidance of Mission Creep
- Definition and Identification of trade secrets
- Improper Misappropriation as Defined By 18 U.S.C. § 1839(5) (A) and (6)(B)
- Restrictive Covenants and Departing Employees
- Evidence Mapping and Preservation
- Reasonable Forensic Analysis Steps
- Special Considerations Regarding Smartphone Based Evidence
- Agreed Orders To Address Privacy Concerns
- Reasonable Attorney-Client Communication Security Measures
- Civil Subpoena for Carrier Call and Text Message Records
In the first section, we will define and lay out reasonable steps one can take in the event smoke has begun to appear which could indicate fire.
In the event smoke signals start to appear in one’s organizations, there are several important triage steps one should take to determine and quantify if a true fire exists.
First, it is important to understand the nature of electronic evidence; electronic evidence is extremely ephemeral in nature.
We will be reviewing in depth the class handout evidence map tool and the method to immediately identify, preserve or have preserved electronic evidence from which smoke has been detected.
Triage Step #1. Identify and Preserve
Electronic evidence is extremely ephemeral in nature: ripe fruit must be picked from the vine and properly preserved before it withers away and dies.
Document and take reasonable steps to identify and preserve, or have preserved, sources of potentially relevant evidence from which smoke signals have been identified.
If a significant amount of smoke is detected, it is time to consult with specialized outside counsel who will recommend an independent third party computer forensic expert.
When working with outside counsel and a computer forensic expert, it is best to think in terms of outside counsel as lead surgeon and the forensic expert as ER doctor.
The ER doctor will run standard tests, which we will review in depth shortly, which can be interpreted and appropriately acted on by one’s specialist physician.
Depending upon the initial test results, one might be given some alka seltzer and sent home, or possibly sent straight to heart surgery.
Triage Step #2. Engagement of Outside Counsel and Computer Forensic Expert
Consider the paradigm of outside counsel as lead surgeon/head physician and third party computer forensic expert as emergency room doctor.
When a patient arrives at the emergency room, standard reasonable tests are run irrespective of, as well as in response to, a patient’s specific complaints.
Similarly, a competent computer forensic expert will perform standard analysis steps to identify “low hanging fruit” indicators of significant problems.
Just as a physician’s interpretation of medical tests might call for the patient to take an antacid and be released, or immediately be directed towards surgery, outside counsel’s interpretation of a computer forensic professional’s analysis results might call for a simple demand letter, or the filing of a temporary injunction request.
Now let us take a look at methods a corporate client might use to work with their outside counsel, to define best outcomes for the current situation and the avoidance of mission creep.
At the outset of any internal investigation, it is very import to define “win” upfront with outside counsel to avoid mission creep.
Here are Plaintiff side and Defendant side definitions of a winning resolution:
Plaintiff Perspective:
Business Protection Achieved: Plaintiff retains all customer relationships, trade secrets, monies, protectable and significant interests, owned by the Plaintiff, which were under threat of theft by former employee, now Defendant.
Defendant Perspective:
Closure Achieved: A clearly defined “No Go” customer list, geographical territory and time frame governing the prohibition, which enables the Plaintiff to move forward and operate freely without fear of further litigation.
Are these “Wins” diametrically opposed or actually a Win-Win?
A significant challenge many companies face is defining their own trade secrets. The DTSA recently enacted into law provides guidance as to what defines a trade secret.
The DTSA was enacted in to law in May 11, 2016 to provide, inter alia, a method and vehicle to address the protection of trade secrets in Federal Court:
(3) the term “trade secret” means all forms and types of financial, business, scientific, technical, economic, or engineering information, including patterns, plans, compilations, program devices, formulas, designs, prototypes, methods, techniques, processes, procedures, programs, or codes, whether tangible or intangible, and whether or how stored, compiled, or memorialized physically, electronically, graphically, photographically, or in writing if—
(A)the owner thereof has taken reasonable measures to keep such information secret; and
(B)the information derives independent economic value, actual or potential, from not being generally known to, and not being readily ascertainable through proper means by, another person who can obtain economic value from the disclosure or use of the information.
Importantly, the DTSA also defines “improper misappropriation”, or theft in plain English, and most critically, what interests cannot be misappropriated by definition by a former employee.
The critical piece here for our purposes is the need to first clearly define one trade’s secrets so that a forensic expert can then more easily identify evidence of inappropriate misappropriation.
U.S. Code 1839(5)(A) pro
(5) the term “misappropriation” means—
(A) acquisition of a trade secret of another by a person who knows or has reason to know that the trade secret was acquired by improper means
(6) the term “improper means”—
(B) does not include reverse engineering, independent derivation, or any other lawful means of acquisition
Now let us examine how evidence mapping and computer forensic analysis can uncover improper misappropriation
USC 1030, otherwise known as the Computer Fraud and Abuse Act, deals with the concept of unauthorized access and intent to cause material harm. In our evidence mapping section of the class, we will provide simple concrete steps to identify what an ex-employee was authorized to access versus what an ex-employee actually did access, and then what actions the ex-employee took after gaining unauthorized access.
When “authorized” becomes “unauthorized” access you must reasonably show the transgressor’s intent to cause material harm or deprive the victim of significant financial value.
For example, evidence that a former employee, notwithstanding their former employer’s reasonable steps taken to protect company information, took steps to access sections of their former employer’s R&D server to which the employee was not officially provided access, created copies of the company’s future prototype drawings, and then deleted the company’s only copies of the prototype drawings could be construed as actionable under 18 USC 1030.
The existence of an enforceable restrictive covenant can improve the chances of achieving a permanent injunction.
Oftentimes restrictive covenants are found to be non-enforceable due to non-compliance with state laws where the employee works versus the state laws where the corporate parent is located.
Review existing restrictive covenants to confirm each covenant complies with state laws and make appropriate revisions.
Here are some basic qualities of an enforceable restrictive covenant. If forensic analysis reveals evidence of “improper misappropriation” of significant trade secrets, a lack of a pre-existing restrictive covenant does not mean a potential plaintiff is without other avenues of potential relief.
Restrictive covenants (as it relates to employment) typically address one or more of three primary areas:
- Non-compete, enjoining the former employee from working for a direct competitor in the same or similar capacity as his/her prior role
- Non-solicitation, precluding the employee to solicit others to depart the organization
- Non-disclosure, preventing the unauthorized release of confidential, proprietary or otherwise protected information
Illinois, for example, considers whether a legitimate business interest exists based on the totality of the facts and circumstances of the individual case. Factors to be considered are:
- The near-permanence of customer relationships
- The employee’s acquisition of confidential information through his employment
- Time and place restrictions Reliable Fire Equipment Co. v. Arredondo, 2011 IL 111871.
If forensic analysis reveals evidence of “improper misappropriation” of significant trade secrets, or the threat thereof, a lack of a pre-existing restrictive covenant does not mean a potential plaintiff is without other avenues of potential relief.
With “Win” defined, now it is time to take steps to identify custodians of evidence potentially relevant to the dispute.
Here Dilbert’s boss and an unethical lackey discuss the absolute wrong approach to addressing one’s duties to preserve evidence.
“…it should be abundantly clear that the duty to preserve means what it says and that a failure to preserve…and to search in the right places…will inevitably result in spoliation.” Pension Committee v. Banc of America Securities (2010 WL 184312 [S.D. N.Y., Jan. 15, 2010]).
The first step is to define and track custodians of evidence potentially relevant to the investigation.
A Custodian of Evidence may be defined as:
- Person or person(s) with direct knowledge and/or control of evidence potentially relevant to the underlying matter.
- IT Custodian: The IT employee(s) of the Plaintiff and/or Defendant’s organization who can identify and help preserve evidence potentially relevant to the underlying matter.
- Individual Custodian: Person or person(s) directly involved in the dispute such as a Defendant former employee suspected of misappropriating trade secrets.
- In complex disputes, the list of Individual Custodians can be expected to evolve.
At the start of an internal investigation and before custodial interviews begin, an “Upjohn Letter” should be provided to the potential subjects of interviews explaining that in-house counsel represents the employer, not the employee, and that the company may choose to, at its sole discretion, reveal the results of employee interviews to a government agency or any other third party.
The underlying case is Upjohn Company v. United States, 449 U.S. 383 (1981)
Interviews may reasonably identify employees’ personal devices and accounts as sources of evidence relevant to a given dispute.
An example Upjohn Letter is provided.
We will now go into detail regarding the tracking of evidence in the handout Evidence map.
A major threat to all litigants is the cost of litigation itself. Identifying and tracking all critical aspects and qualities of a given dispute’s evidence in a single Map can inform and enable one to control and forecast costs. After IT and/or Individual Custodians interviews are complete, Counsel can then pinpoint specific evidence to investigate as the evidence may relate to the Law.
Example: Judges will calculate the financial impact on plaintiff, defendant and third Parties (and the effect on the public at large if an injunction was not applied) to determine if a permanent injunction is called for. Therefore identifying and preserving Accounting records would be important and informative to an injunction.
A True War Story: The IT Custodian interview identified QuickBooks online as the Defendant’s new competing entity’s sole accounting system. Forensic expert was provided with username and password to forensically preserve all financial data, reports and logs possible. An analysis of the QuickBooks accounting records showed that the Defendants had not been doing any business with Plaintiff’s customers or requested restricted geographical region.
At the outset of all investigations, here are the critical dates to identify and track in the provided evidence map:
- Defendant’s last official date of employment at Plaintiff organization
- Defendant’s first official date of employment at new Defendant organization
- Date and time former employee turned in company phone and computer
Forensic analysis of electronic evidence will reveal timelines of human activities performed on computers and phones.
Knowing the last date and time a former employee had control over a computer will allow the computer forensic investigator to efficiently focus in on activities performed by the former employee on the former employee’s last day of control over the computer.
With the need for expedited Preservation, Counsel should schedule interviews with knowledgeable Client IT resources as quickly as possible. These responses also can identify systems still accessible to the former employee, and should therefore be locked down.
All responses should be thoroughly documented in the Evidence Map.
Questions to ask knowledgeable IT Custodians and record in Evidence Map’s “IT QUESTIONS” tab:
- Are USB ports enabled on workstations?
- Are workstations running virtual machines?
- Are hard drives encrypted?
- Is Mobile Device Management Software being used on smartphones?
- What specific business systems and accounts does/did an employee have access to?
- What Email Server is the organization using? An internally managed Microsoft Exchange Server or Office365 in the Cloud?
- Does IT policy allow for employees to export and save email in the form of PST files?
- What Cloud storage services is the organization using such as iCloud, Drobox, Google Drive, OneDrive, SharePoint, QuickBooks Online?
- What are the dates and times on which IT changed all passwords for each internal and cloud based business systems the former employee had access to, and by whom were they changed?
- Has IT identified systems which allow for “User Activity” reporting, which can show user activities such as dates and times of accessing a system, exporting of reports and/or data from system?
Custodial interviews should be scheduled immediately following the initial IT interviews, targeting the known resources whose work / communications intersected with the target of the investigation.
Concurrently, IT interviews can continue with an examination of structured data sources, such as network shares, accounting systems, CRM and ERP platforms, etc.
All responses should be thoroughly documented in the provided Evidence Map.
Based upon the results of individual custodial interviews, client, counsel and forensic expert may plan for preservation of all appropriate sources.
Here are immediate steps in house IT/Legal/or leadership may take to immediately preserve evidence in anticipation of engaging an independent third party computer forensic experts.
Immediate steps to take with laptops:
- Normally power down the device
- IT should seize the device into their keeping
- IT should sequester the device in a secure location specifically designated for devices under a hold
- If deemed necessary or prudent, IT should remove the hard drive (if possible)
Immediate steps to take with mobile devices:
- If the mobile device is powered on and you know the access code, power down the device normally but keep it plugged into a charger and secure it with IT
- If the device is powered on and you do not know the access / unlock code, switch it into airplane mode or put it into a sealed metal container (like a paint can) and secure it with IT
- If the device is powered down already, plug it into a charger to avoid battery loss, and secure it with IT
Immediate steps to take with email and other business system accounts:
- Turn on “litigation hold” capabilities where they exist such as Microsoft’s Office365 and Google’s Business service offer
- Change passwords to all business systems former employee had access to in order to prevent improper misappropriation activities
Resist the temptation to “investigate” electronic evidence as significant spoliation can easily occur.
In the case of departing employee investigations, acting quickly upon devices such as laptops and cell phones is paramount to understanding the nature and gravity of any potential corporate risk. Ideally, the organization will have a standing policy, developed and enforced by IT, Legal, and Risk & Compliance, on how to address the departure of employees of a certain rank (and above), and a plan to extend that policy to anyone in the organization if special circumstances warrant it.
If laptop computers are identified during the custodial interviews and determined to be potentially relevant, a qualified third party forensic investigator will create what is known as a “Physical Forensic Image” of the laptop.
For all internal investigations and theft of trade secret matters, laptop and desktop personal computer hard drives must be imaged in what is known as a “Physical Forensic Image”. A “Physical Forensic Image”:
- Meets the criminal standard of evidence preservation by capturing all possible zeroes and ones on the surface of a given hard drive.
- A unique “Hash” value is calculated, recorded and compared between the original evidence and the resulting “Physical Forensic Image” in order to confirm if a copy is a true forensic copy of the original evidence.
- Allows for recovery of deleted files and other deleted evidence of human activity.
- Requires special “write-blocking” hardware employed by computer forensic experts.
In the event custody and control over one’s evidence is being transferred to outside counsel or a forensic expert, a Chain Of Custody form should be used. Chain of custody in the most basic sense means “control”.
COC documentation creates a written record of when control of and over a specific piece of evidence began and ended. A COC document such as the one provided here should be used for each piece of evidence being transferred from a client to their outside counsel or computer forensic expert.
Now that custodians and their sources of evidence have been identified and preserved, let us discuss reasonable forensic analysis steps one may perform.
We have provided a generic example of a departed employee analysis report in which we uncovered copying of trade secret documents to USB drives. Typically these triage analysis steps cost $3,000.00 per employee being analyzed.
Identification and Reporting of:
- All User Accounts, such as email accounts, existing on computer or smartphone
- All software installed on computer or smartphone
- All external devices connected to a computer, including the dates and times of connection, and the make/model/serial numbers of the connected devices
- Activities of file copying to external devices
- Activities of file copying to unauthorized cloud storage services
- Activities of transmission of files via personal email accounts
- Activities of file deletion
- Activities of recent file access from external devices on work computer
- Estimated Cost: $3,000.00 Per Employee
Now let’s discuss the special threat and considerations smartphones pose to organizations and theft of trade secrets. The smartphones in use today by your clients are oftentimes just as powerful as the laptop computers they are using. Although there is a tendency to ignore smartphones in discovery, such a strategy may be a significant mistake due to the treasure trove of easily recovered evidence they hold.
From a discovery perspective, the best way to deal with smartphones is to simply consider them as one would a big file cabinet.
Smartphones, including iPhones and Android phones, basically have ten different cabinet drawers of information that may be relevant to your matter:
- Contacts
- Call Records
- Voice Messages
- Email and Text Messages
- Documents
- Calendar
- Internet Browsing History
- Songs, Photographs and Movies
- WiFi History
- Social Media (Facebook, Instagram et al)
Some of you may be surprised to discover that only Google or Apple have access to some of your phone’s drawers. Although it is possible to access all of your phone’s drawers by changing all of the locks and keys through a process called “Jailbreaking” or “Rooting”, it is not recommended to do so as this changing of the locks and keys will make one’s phone inherently insecure.
Apple and Google keep highly sensitive information in locked drawers so that malicious applications cannot access the phone owner’s credit card information and passwords. Therefore, it is highly recommended that one not jailbreak or root one’s own phone.
As an example, in iPhone’s Text Messages drawer, Apple stores a file named SMS.db, or short message service database. Through the use of forensic tools, deleted text messages on iPhones and Android phones can be recovered. Phone storage is currently so vast, that it is possible but highly unlikely that deleted messages will ever be overwritten.
Unlike laptop and desktop computer cabinet drawers, which are all unlocked and accessible to the device owner by default, smartphones contain locked drawers with content that is inaccessible to forensic tools unless the device is jailbroken or rooted. Jailbreaking and rooting will violate a device’s license and render the device highly insecure. Therefore, it is important to understand the relative limitations of how much evidence can be recovered from phones versus computers.
We will now discuss alternative locations that smartphone evidence may be recovered from: the device itself, mobile backups on personal computers and mobile backups in the cloud.
Synchronizing an iPhone with a computer using the iTunes application creates an entire backup of that iPhone on the computer running iTunes. Here are the actual file cabinet drawers that one could open to find the iPhone backup.
If an ex-employee created a “Mobile Backup” of their personal iPhone on a company laptop using iTunes, the company will have access to the entire contents of the physical phone itself as of the date the “Mobile Backup” was created.
iTunes file cabinet drawer locations on computers:
- Mac: ~/Library/Application Support/MobileSync/Backup/
- Windows XP: \Documents and Settings\(username)\Application Data\Apple Computer\MobileSync\Backup\
- Windows Vista, Windows 7, Windows 8 & Windows 10: \Users\(username)\AppData\Roaming\Apple Computer\MobileSync\Backup\
An iTunes mobile backup contains basically your entire phone, including previously deleted information:
- Photos
- Contacts
- Calendar
- Internet Browsing History
- Notes
- Call history
- Messages (iMessage and carrier SMS or MMS pictures and videos)
- Voice memos
- Network settings (saved Wi-Fi hotspots, VPN settings, and network preferences)
- Email account passwords
- Wi-Fi passwords and passwords you enter into websites and some apps,
- Map bookmarks, recent searches, and the current location displayed in Maps.
(see http://support.apple.com/kb/ht4946)
Even if your client’s former employee took their personal iPhone and/or iPad with them when they left to work for a competitor, if they synchronized their personal iDevice with your client’s computer, you have access to that iDevice; no subpoena required!
Location-Based Evidence
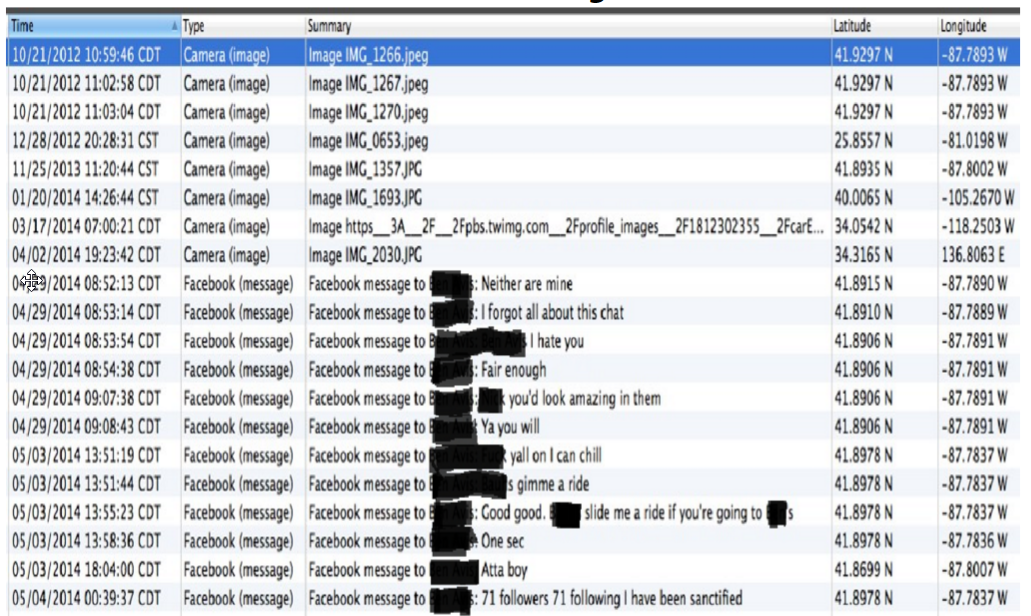
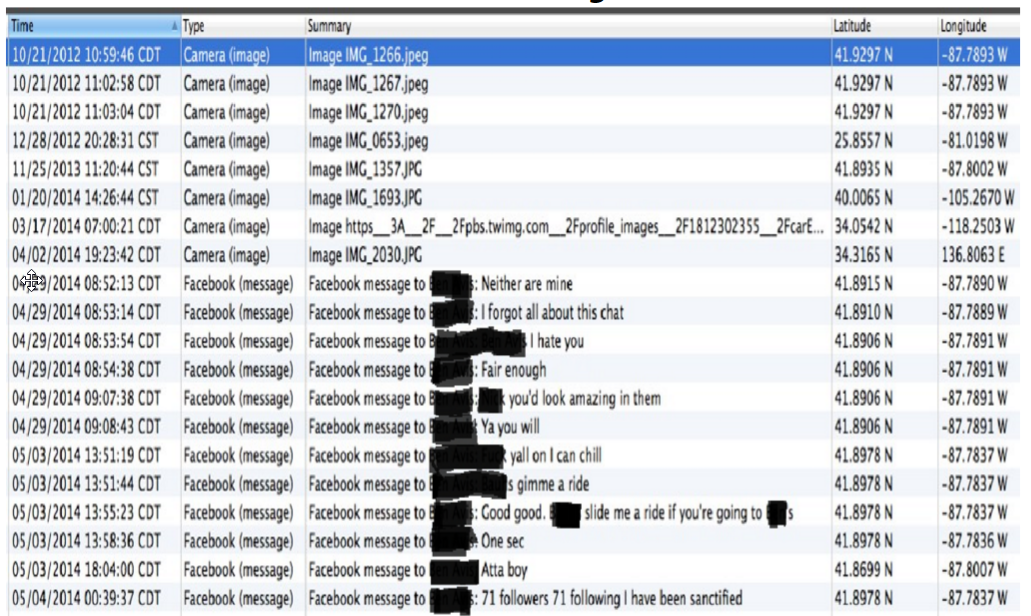
In this example, sample evidence was extracted from an iPhone using Katana Forensics’ Lantern software. Lantern was able to extract times and dates photos were taken and messages were sent, names of photos, the content of the messages and the longitude and latitude of where the person was at the time each photo was taken or message sent.
In one example, investigation of a client’s former employee’s company issued iPhone revealed multiple meetings at their opponent’s headquarters in the months prior to the former employee’s resignation. Signing into a Wifi network creates a time/date/location stamp on a workstation.
Smartphone forensic software automatically sorts all human activity performed on a given smartphone, such as making calls, receiving text messages, sending emails, or taking pictures, in chronological order.
Focusing on critical dates identified in the Evidence Map can be very informative and an efficient, targeted method of analysis.
Now we will review the concept of building and using timelines from acquired electronic evidence.
Although you may have heard of concerns regarding issues related to allowing employees to use their own smartphones at work, or BYOD, I want to alert you to the real threat which I have termed BYOA, or bring your application. One would hope that employees only use company email for work related communication, but we are finding in case after case that this is absolutely not true. Many organizations allow employees to use their own smartphones for work purposes (BYOD). BYOD can present difficulties when content on BYOD phones becomes subject to legal holds. BYOA represents a greater threat than BYOD as most employees will not disclose the use of a non-approved application. Some organizations prevent employees from installing non-corporate approved communication applications on company issued smartphones.
BYOA content is primarily stored as SQLite database files.
- Skype chat messages, incoming and outgoing call records, and file transfers made by a Skype account is stored in a file called “main.db”: C:\Users\*Username*\AppData\Roaming\Skype\main.db
- Kik contacts, messages, and contacts:
For iPhones: /root/var/mobile/Applications/com.kik.chat/Documents/kik.sqlite
For Android: /data/data/kik.android/databases/kikdatabase.db
On a recent engagement, our corporate client received an anonymous tip accusing an employee of viewing obscene materials at work on a company issued iPhone.
From a backup of the company issued iPhone found within the iTunes folder of the company issued laptop, I was able to recover Kik (kik.com) messages included photos of a very private nature. The employee had installed the free Kik communication application himself.
Using my timeline and location tools, I found six instances of inappropriate pictures being sent during work hours on the company issued iPhone while on company property. The employee was reprimanded but not terminated.
From a litigation strategy standpoint, if one wishes a forensic expert to be employed to image and investigate an opponent’s smartphone, inevitably, objections over scope and privacy will be raised. Therefore, it is useful to have an agreed order prepared governing the specificity of which electronic evidence will be searched.
By now it should be clear that significant amounts of evidence about your opponents may be recovered from your own clients’ devices using forensic techniques. In some cases, it may be an effective case strategy to have the court issue an order allowing the examination of an opponent’s smartphone. In these cases, understandable objections will be raised surrounding privacy. To address these objections head-on, it is recommended to put into place an agreed order that limits the focus of investigation to specific targeted evidence based upon key word filters. The sample agreed order handout for the class also includes a process by which the opponent’s counsel may review key word responsive evidence, withhold privilege communications, and only produce key word responsive evidence to the requesting party.
In my Pro Bono practice, I have had seven cases in which my client came to me positive that an opponent “knew” things they could not possibly know. In each case, my client was correct in their assumptions and ultimately I was able to discover exactly how they were being spied upon. Here are three real life examples of spying techniques I have uncovered.
- In one case, my client walked away from her computer while still logged in to Gmail. This enabled the respondent to turn on “autoforwarding” within my client’s email account so that a copy of all emails she sent or received were forwarded to the respondent.
- In a Domestic Violence court case, the respondent had configured my client’s iPhone so that the respondent could log in to trackmyiphone.apple.com and then observe the physical movements of my client.
- In a third case, the respondent had installed key logging software onto my client’s computer, which resulted in every key stroke my client made, including inputting user names and passwords, being sent to the respondent’s computer.
Please now refer to the handout titled “Physical Access Questionnaire” which I created in response to the steady stream of spying cases I have been involved in. I am very proud to say that this tool has been adopted and already put into use at Cook County’s Domestic Violence Courthouse. Using the Questionnaire, the first order of business is to have your client define the actual time period the unfriendly party had physical access to your client and their devices and accounts. As a second step, please have your client list all devices, including cell phones, computers, email accounts and social media accounts they currently own or use that fall under the “Time Period” the unfriendly party enjoyed physical access.
With the Questionnaire completed, one can then move on to curing, and if appropriate preserving for later use, the infection. For example, if you and your client determine that it is possible a former business partner or disgruntled ex-employee did have access to your client and their systems, then it is reasonable and suggested that your client create a brand new email account to be used for attorney-client communication from a computer that the opponent could never have had physical access to. Performing a factory reset of an iPhone or Android phone will render the device free of all possible spyware. However, in appropriate situations, a forensic preservation of the iPhone or Android phone is recommended before completely wiping the device. The market rate for a smartphone forensic preservation is $500.00. One of the handouts is a sample iPhone forensic report for you to review.
From my own experience, shareholder disputes, especially those involving family members, can be highly emotionally charged cases that perhaps would benefit from talk therapy as much as legal counsel. This is just one type of case where our physical access questionnaire should be considered for use at the outset so that your communications with your client are not being read by the opponent.
We will now discuss steps to subpoena phone records from a carrier.
Once a caller’s phone number and carrier are identified, a civil subpoena form and related “Generic Record Request Description” sheet, once responded to, will provide to the requesting attorney:
- Any and all records of incoming and outgoing phone calls and text messages, including the IMEI, ESN, MEID and the IMSI numbers of all calls and text messages made and received, the contents of text messages, and call durations for the telephone numbers ###-###-#### and ###-###-#### from (DATE RANGE START) to the (DATE RANGE END).
- Any and all records of any member accounts held fully or in part under the name RESPONDENT NAME or connected to the phone numbers ###-###-#### and/or ###-###-####, including but not limited to the purchase of new SIM cards, transferring of any numbers associated with the account to new devices, and/or attempts to remove numbers from the account from (DATE RANGE START) to the (DATE RANGE END).
Cell phones have multiple types of unique identifying serial numbers to request and be aware of:
- IMEI Numbers: “International Mobile Equipment Identity” number which is a unique-to-individual-GSM network phones 15 digit number.
- MEID Numbers: “Mobile Equipment Identifier” is 14 digits long and is unique-to-individual CDMA network phones.
- ESN Numbers: “Electronic Serial Number” are unique numbers, which are slowly being phased out in favor of MEID numbers for CDMA network phones.
- MSISDN: “Mobile Station International Subscriber Directory Number”, is a unique number used to identify a mobile phone number internationally.
- IMSI: “International Mobile Subscriber Identity” is a unique number assigned to SIM cards.
- ICCID: “Integrated Circuit Card Identifier” is unique number assigned to SIM cards and used to identify SIM cards internationally.
WhitePages.com Pro Service
Once TrapCall.com unmasks the true phone number, WhitePages.com Pro Service can provide:
- Full name of owner(s)
- Prepaid status: Indication of whether a mobile number is part of a prepaid service plan.
- Carrier: The company providing service to the associated number, including carriers such as Boost, Metro PCS and TracFone.
- Line type: Indicates whether the phone is a landline, mobile, fixed or non-fixed VoIP, premium, toll-free, or voicemail-only service.
- Current Address: Includes the full address associated with this number.
- Personal or commercial line: If phone number is associated to a business
Case Study
A third party in a Domestic Violence case received text messages stating “Let’s kill John Jones” and appearing to have been sent by Tom Smith, but Tom Smith did not send the threatening text messages.
Tom Smith had recently ended a relationship with Frank Williams. However, Frank Williams still had ownership of Tom Smith’s old phone number. A subpoena to Frank William’s carrier revealed that Frank Williams was placing calls and texts on the same day from one single phone but using two different SIM cards. The subpoena response allowed us to connect the unique IMEI number of Frank’s single phone to the two different SIM cards and their related unique IMSI numbers.
The attorney was able to deduce that Frank Williams was in possession of a SIM card to which he had ported Tom Smith’s phone number, and was using that phone number to make calls and the threatening text messages from Frank Williams’ phone. The 3rd party recipient thought the threatening text messages were coming from Tom Smith, but they were in fact coming from Frank Williams’ phone using the SIM card Frank Smith ported Tom Smith’s legacy number to.
The original slides can be downloaded here.
Handouts:
- Chain of Custody Document
- Departing Employee Sample Report
- Draft Order
- Evidence Map
- Generic Phone Record Subpoena
- Generic Record Request Description Sheet
- Physical Access Questionnaire
- Timing Outline
- Sample Upjohn Letter
About the Author
Larry Lieb (CCPA, FEXE, OSFCE, CBE) is Managing Director at Haystack ID. He has worked in computer forensics and electronic discovery since 1998. He is a Michigan PI and has qualified as a computer forensic expert in both Federal and State courts. He is also the 2016 Cook County, Illinois Domestic Violence Legal Clinic Champion of Justice award winner.








Thank you for this article. A question about VoIP calls which often run over a SIP-provider. Reveals a e.g. Basic trapcall.com subscription full technical background information about the IP stream of VoIP calls? Is it possible that the SIP-provider can hide completely behind a marketing term e.g. sipcall or how to find out where the SIP servers are logically located (IP and/or ASN, hoster, proxies)?
R.G. – many thanks for your question. You have exceeded my personal knowledge about VoIP call technology. I received the advice about Trapcall.com from ForensicFocus member “hsco1510” (http://www.linkedin.com/in/ed-merritt-0624672a?trk=hp-identity-name) so I recommend sending Detective Merritt a message directly to answer your question.
Thank you Mr. Lieb, will do you so. By the way I observed that also people out of the Greynet (close to Darknet)
linked your article in their retweets.