by Michelle Oh, HancomGMD
With an ever-increasing range of features and dramatically increased storage capacity, digital devices have become essential to our daily life. Their ability to store vast amounts of data means that these devices have proliferated and are now found in every household. They therefore prove to be a source of crucial information that acts as evidence in digital forensic investigations.
With the expansion of 5G technology, we expect a new chapter in mobile development, and this will bring huge innovation for new technologies such as infrastructure, city management, autonomous vehicles, and connectivity for the consumer mobile internet. And this explosive growth of digital data will lead all investigators to face highly demanding challenges.
This article covers HancomGMD’s data extraction solution ‘MD-NEXT’. It focuses on how investigators can practically use MD-NEXT for both logical and physical data extractions.
Following the step-by-step instructions below will show you the mobile data extraction sequence. It is a simple but useful tutorial for investigators who are looking for a tool which addresses all their their mobile forensic investigation needs.
I. Data Acquisition Sequence Method – Physical Extraction
Tested device – Samsung Galaxy S7 (SM-G935F)
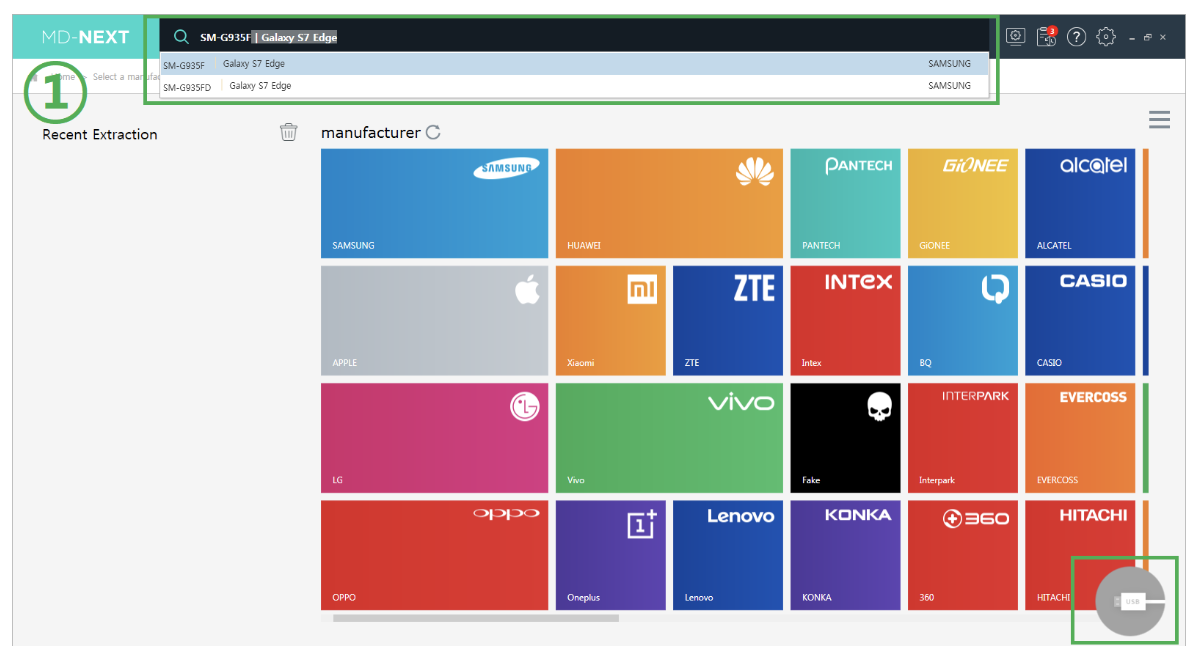
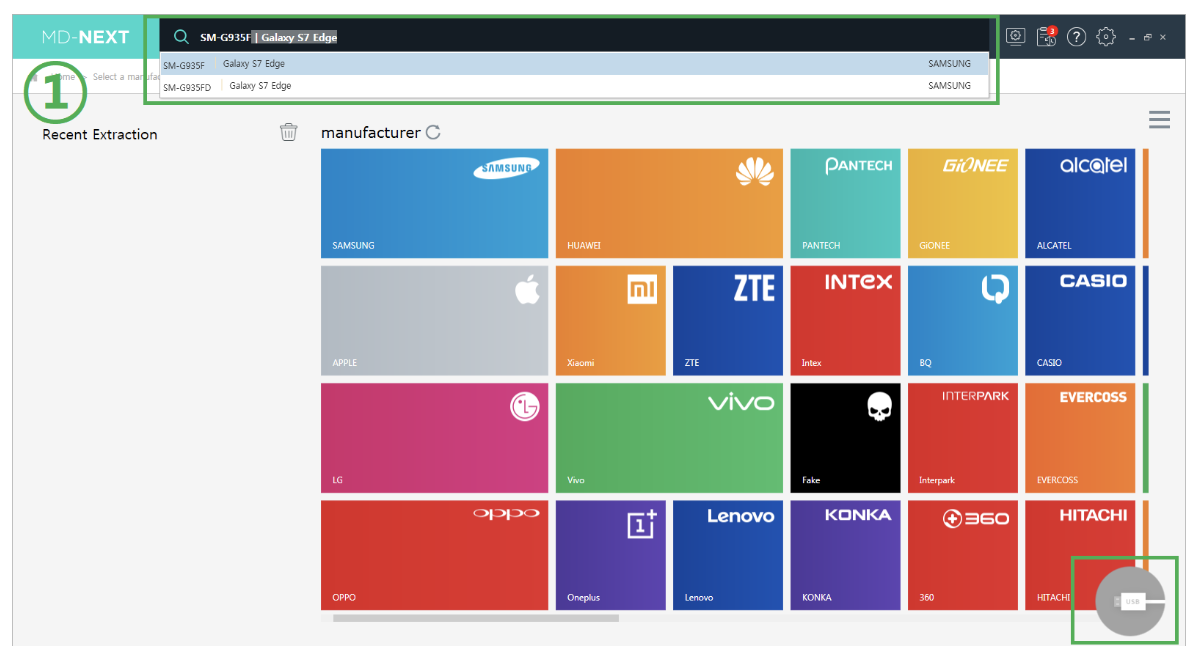
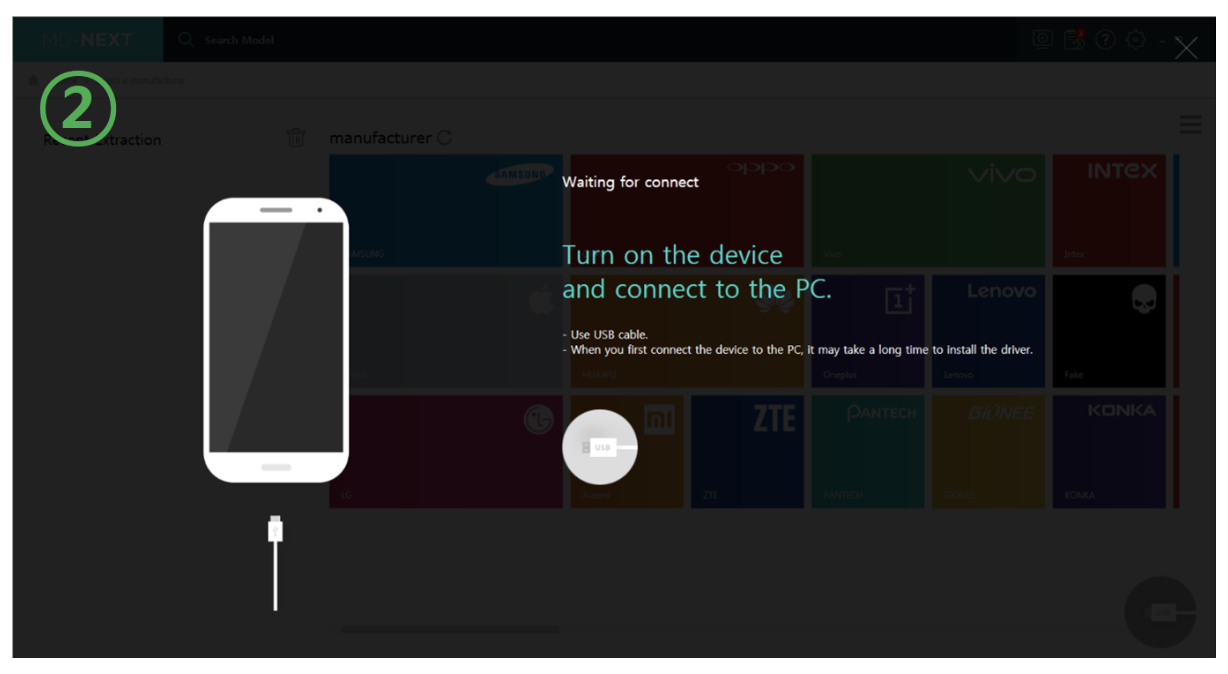
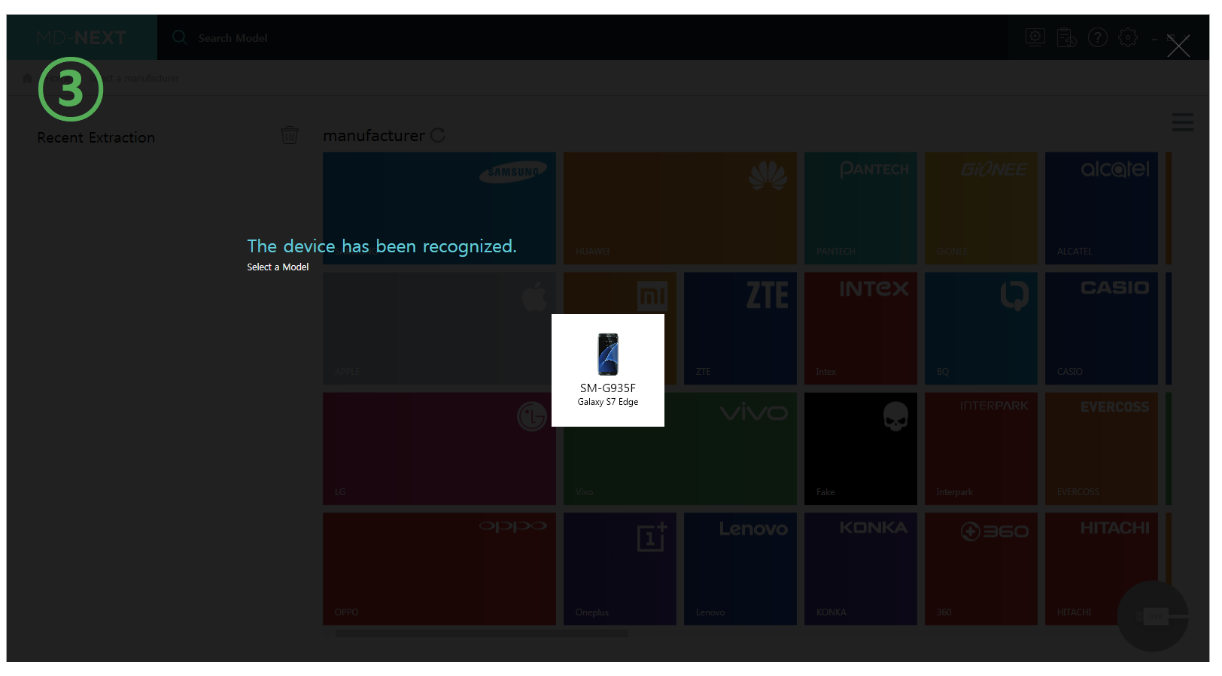
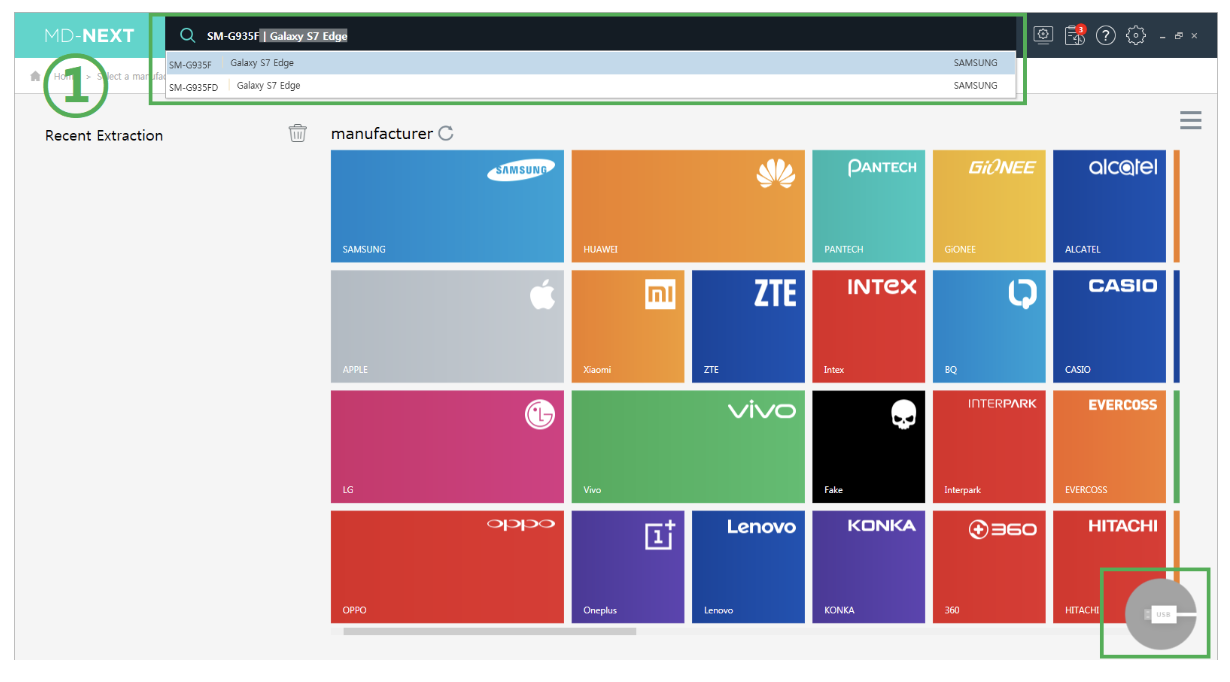
Step 1: Connecting the Device and Finding the Model
MD-NEXT provides a user-friendly and intuitive interface, to help you to easily find and select the device model. After the device has connected, click the cable icon on the bottom right of the screen and MD-NEXT will automatically detect the model.
MD-NEXT supports more than 15,000 smartphone devices from around the world, including over 500 models from Chinese manufacturers (Huawei / Xiaomi / Oppo / Vivo, etc.) It also supports the extraction of IoT devices, AI speakers, smart TVs, drones and vehicle systems.
Advanced Physical Extraction Features:
- Bootloader, Fastboot, MTK, QEDL, Custom Image, rooted Android, iOS physical, ADB Pro, DL, JTAG, Chip-off, SD card, USIM, removable media
- JTAG pin map viewer and connection scanning with AP
- Drone SD card extraction: DJI Phantom, Maverik series / Parrot / Pix Hawk
- AI speaker chip-off extraction: Amazon Echo, Kakao Mini, Naver Clova
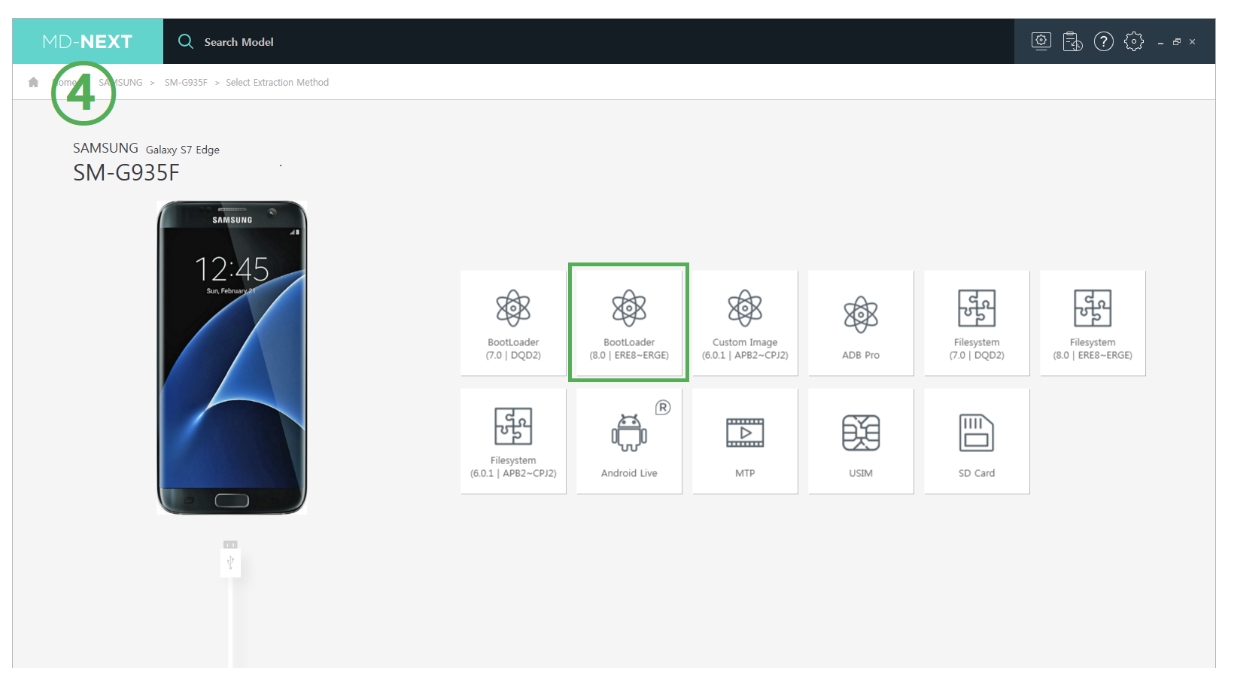
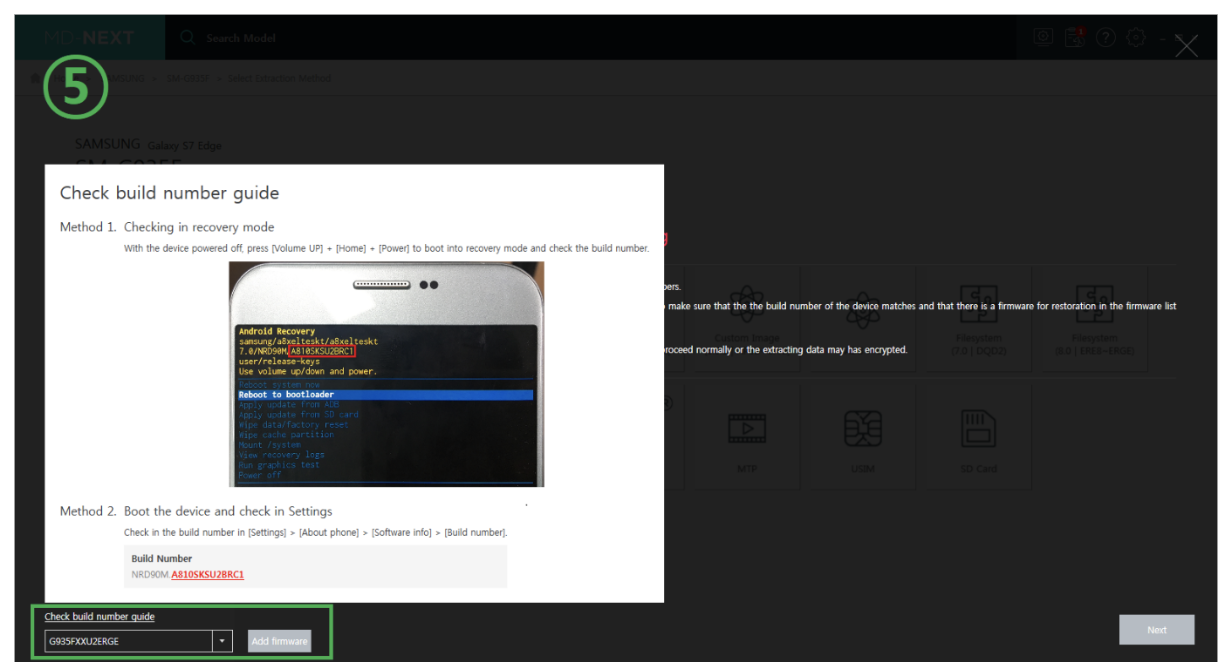
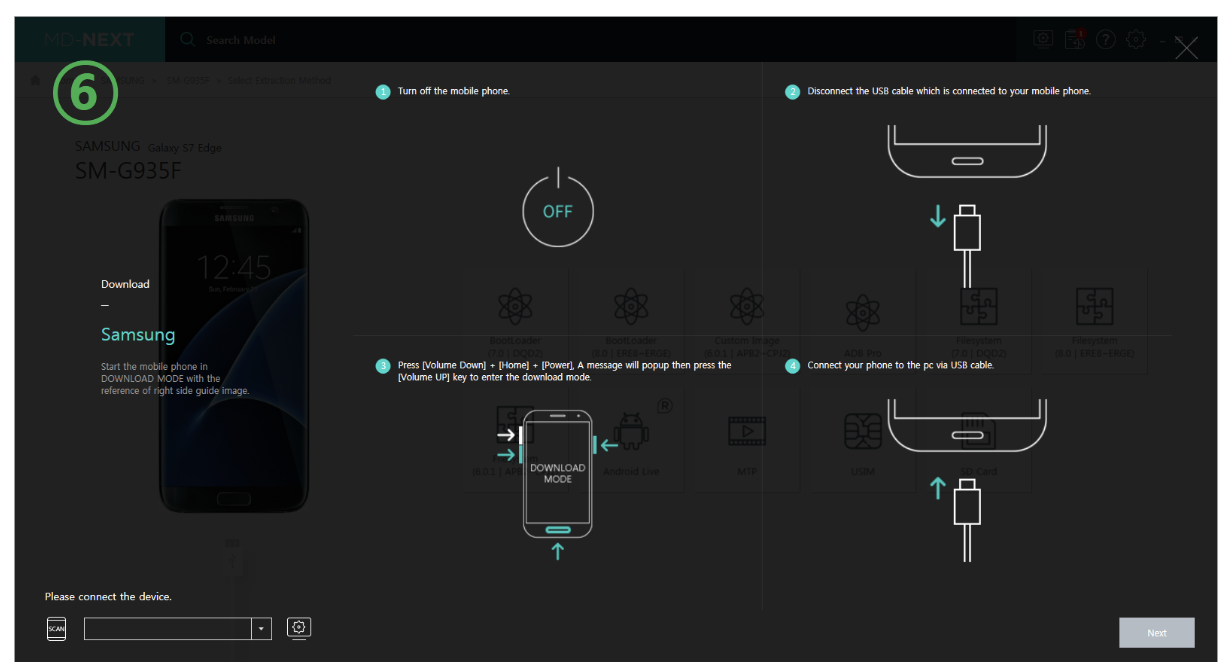
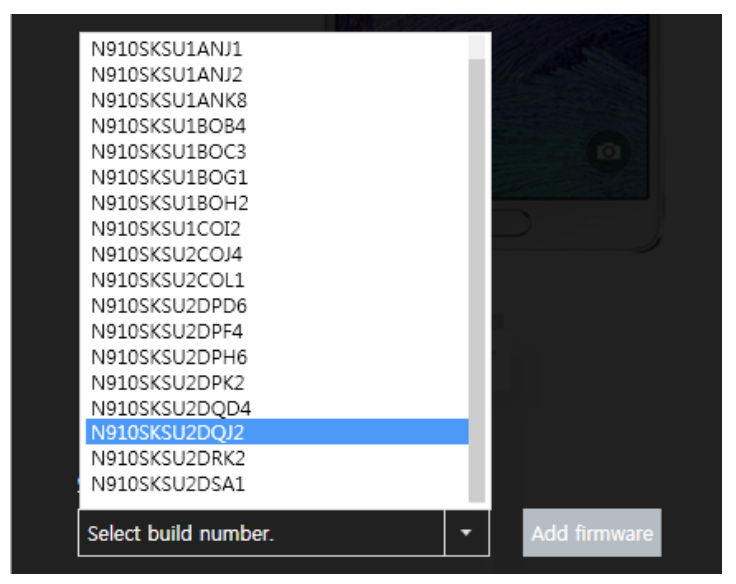
Step 2: Extraction Method
In the screenshot below you can see the available extraction methods for the model we have selected. Both logical and physical extractions are available. Selecting ‘BootLoader’ lets you extract all the mobile data including filesystem, user data, cache and so on. Then select the build number which matches your phone. A set of simple instructions will lead you to the download of the customized firmware.
MD-NEXT comes with an intuitive graphical user guide for each extraction method.
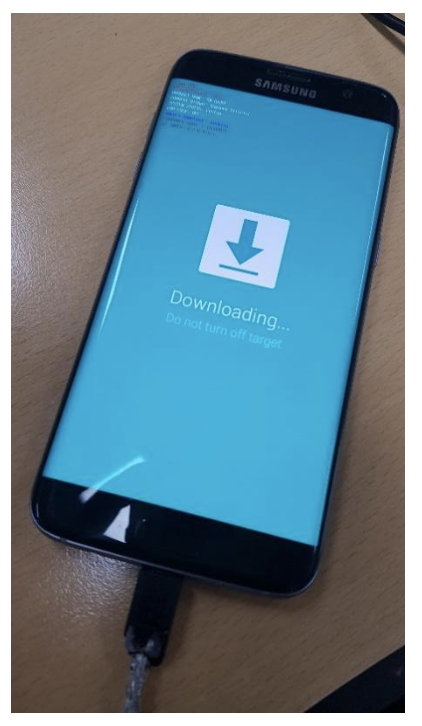
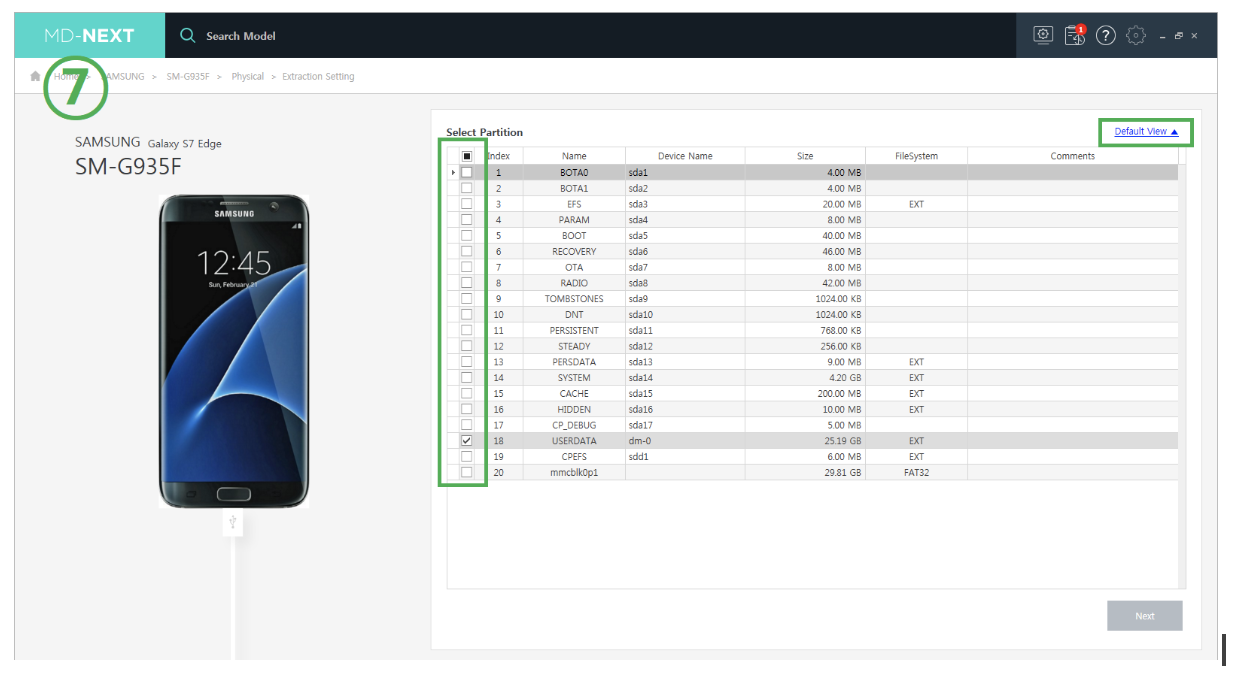
Step 3: Selecting the Data Partition
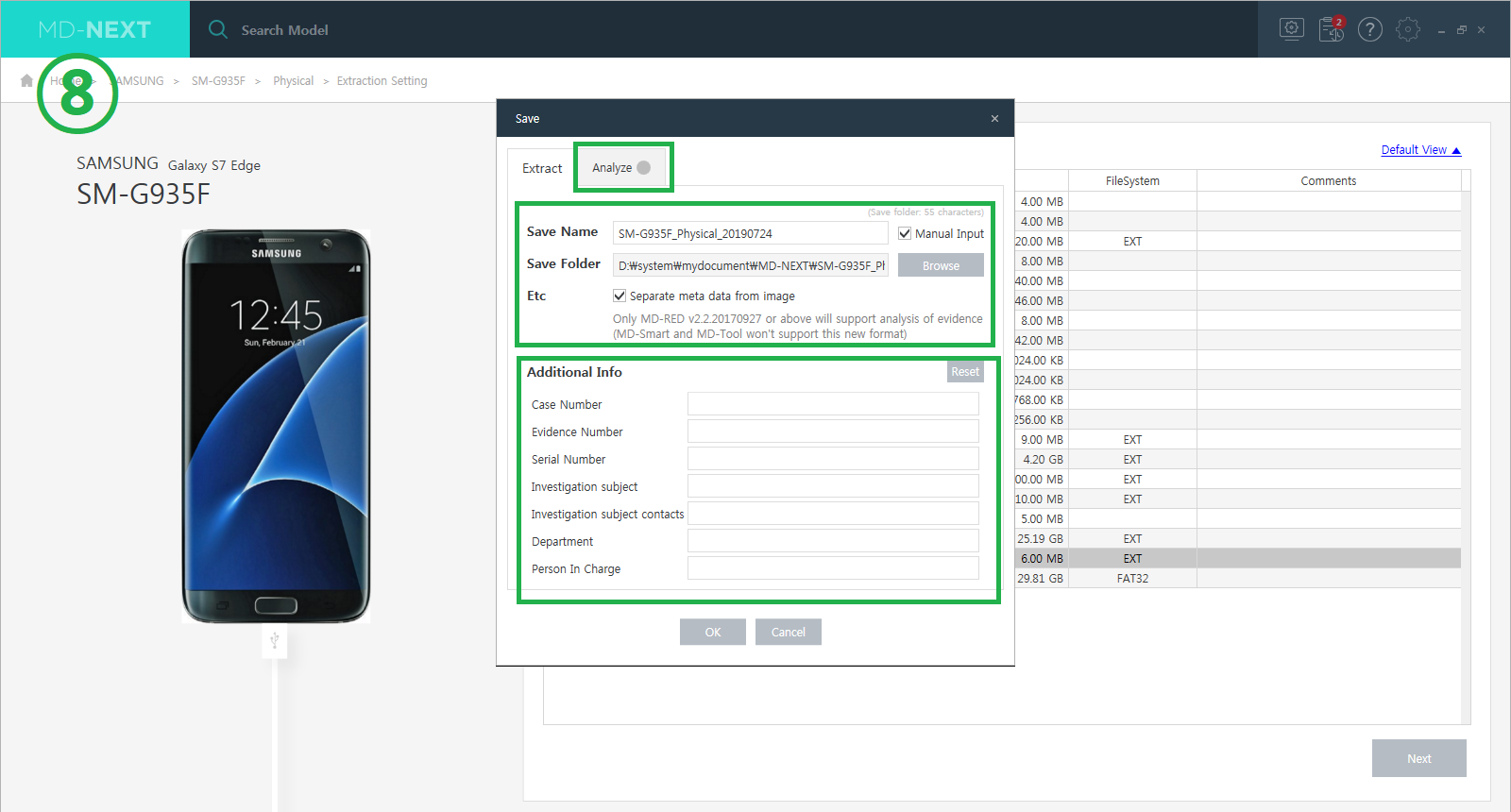
When the device enters “Download Mode”, MD-NEXT recognizes and shows the file system to be extracted, and the user can easily expand the partition. You can then schedule the extracted data to be analyzed by MD-RED.
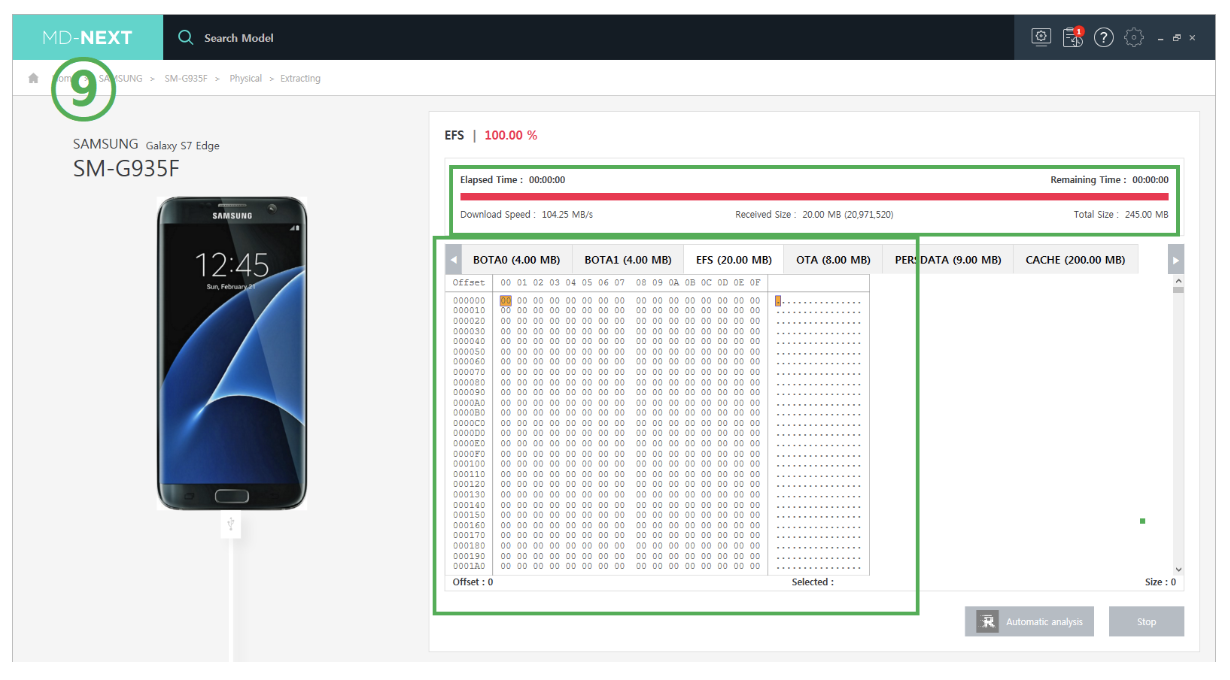
MD-NEXT displays the specific extraction process with a useful menu which shows an extraction progress bar, as well as time and hex data by partition.
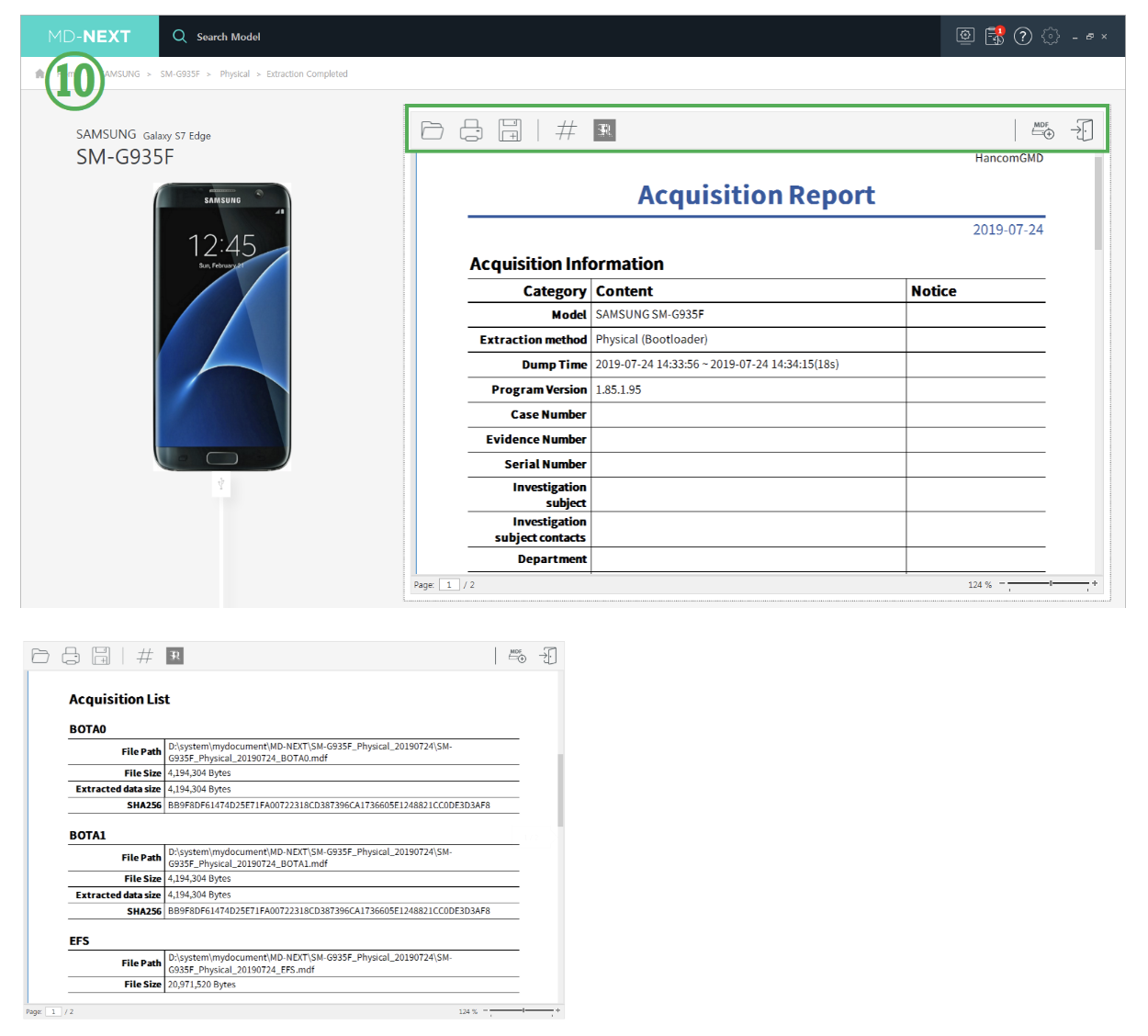
Step 4: Exporting the Acquisition Report
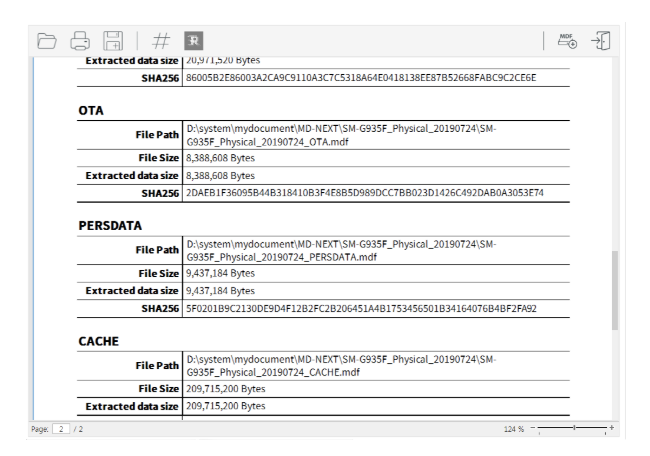
After the extraction sequence is completed, the user can generate an ‘Acquisition Report’. This contains detailed information of extracted partition: file path, file size, size of extracted data, and so on. All of the extracted data is guaranteed with the hash value.
Data preview and save function:
- Preview extraction data
- Hex viewer, data viewer
- An image dump can be saved as ‘MDF’ and standard binary file format
- Pre-defined extraction file name
- Sound alarm for extraction status change
Specific reporting function for integrity:
- Extraction information: hash value, time, method and file name
- Supports report formats such as PDF, Excel and HTML
- Supports ‘Extracted File List’ generation with a hash value of each file
- Supports ‘Witness Document’ generation
- Regeneration of ‘Extraction Reports’
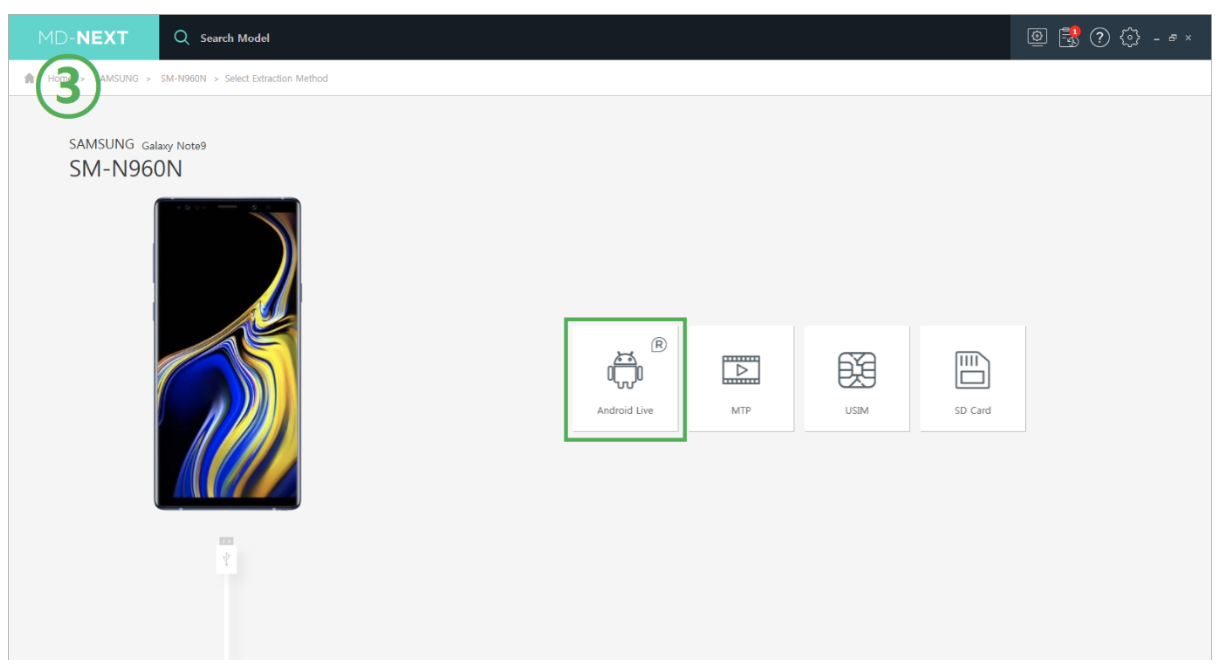
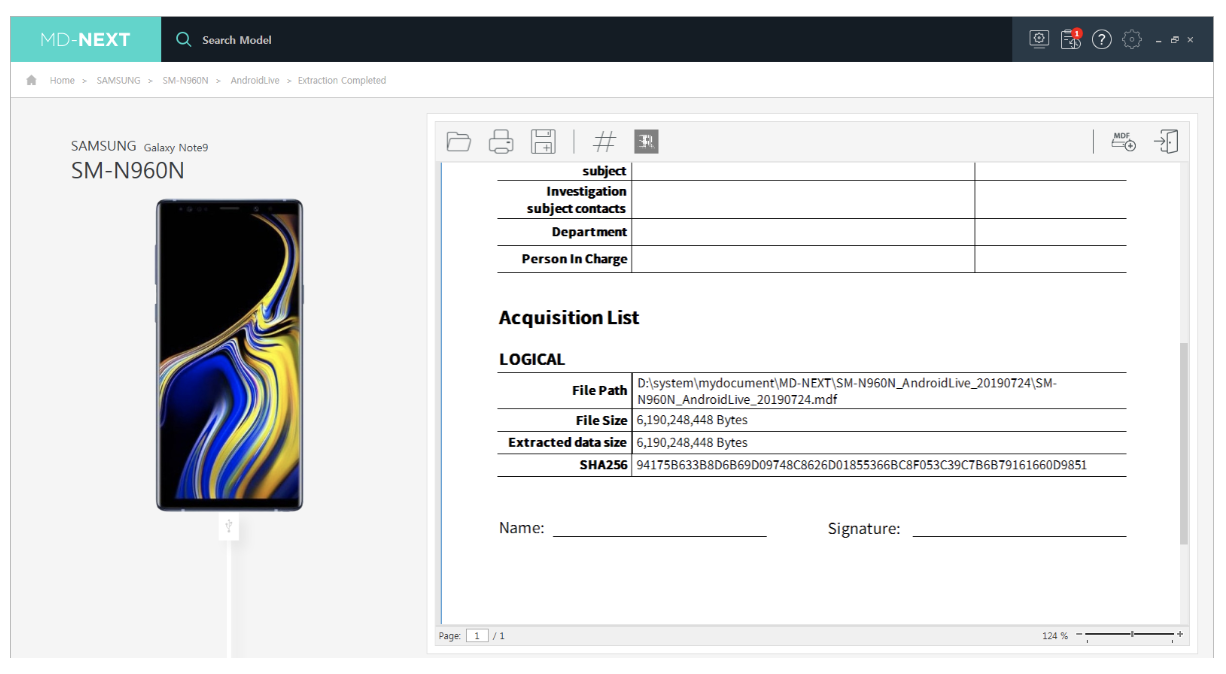
II Data Acquisition Sequence Method – Logical ‘Android Live Extraction’
Tested device – Samsung Galaxy Note 9 (SM-N960N)
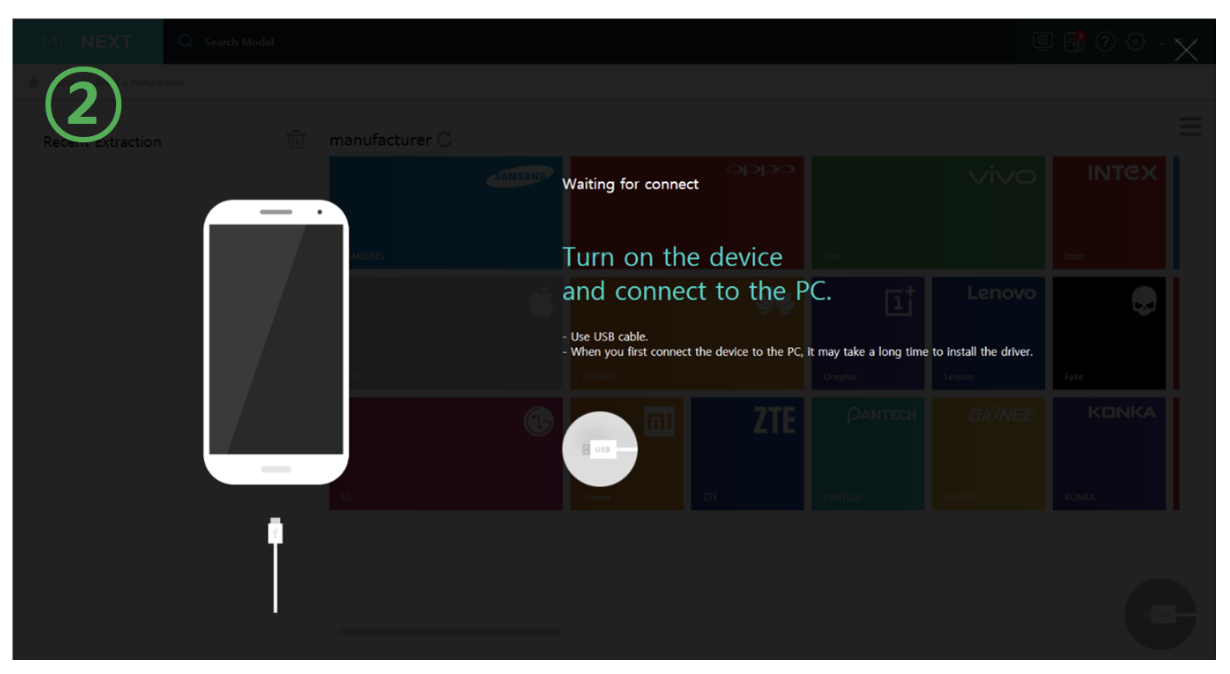
Step 1: Device Connection and Logical Live Extraction
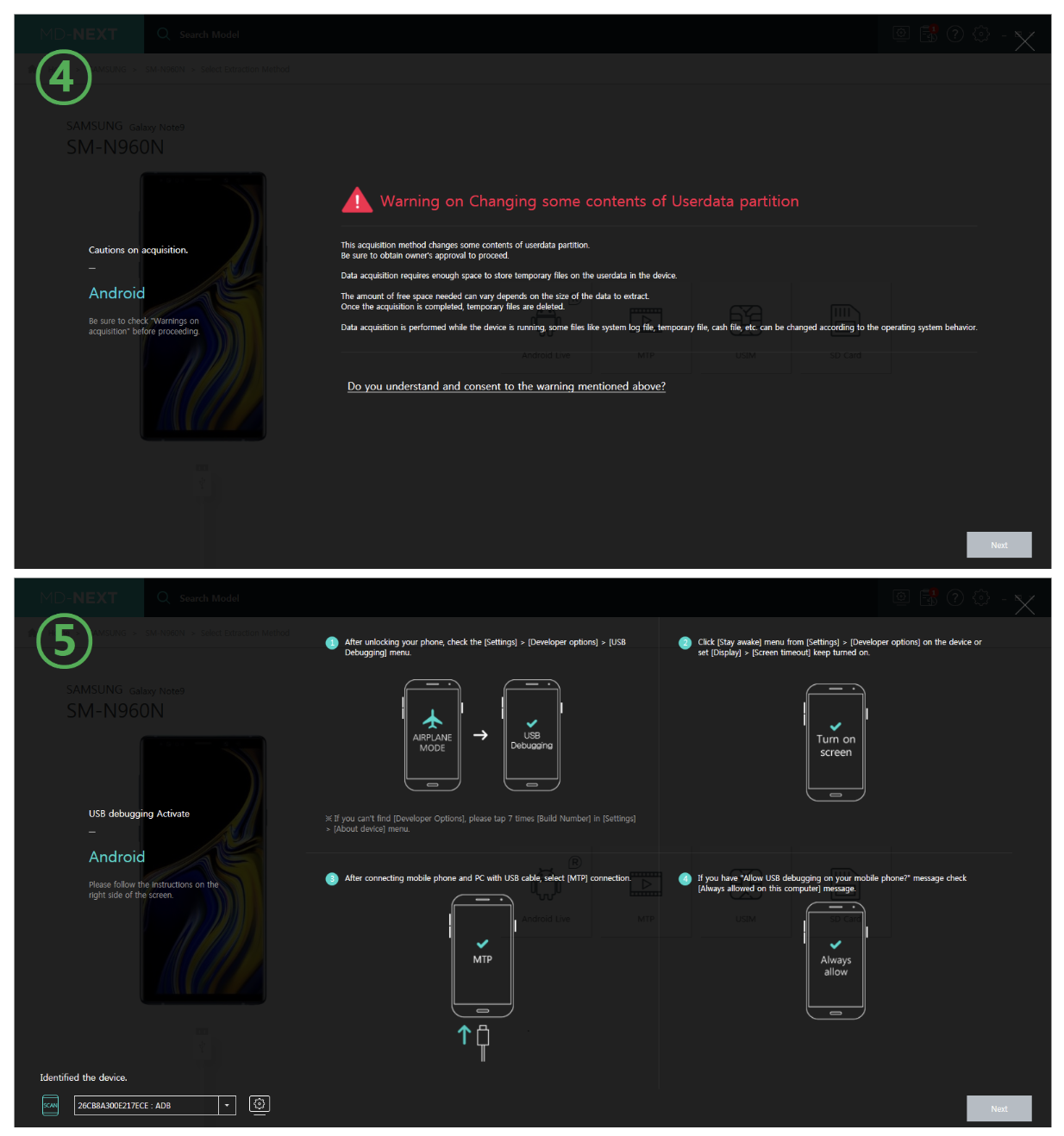
Android Live Extraction is a method of extracting the key active files from an Android Phone. After the device is connected, set up the phone as shown in the guide. MD-NEXT will automatically recognize the device.
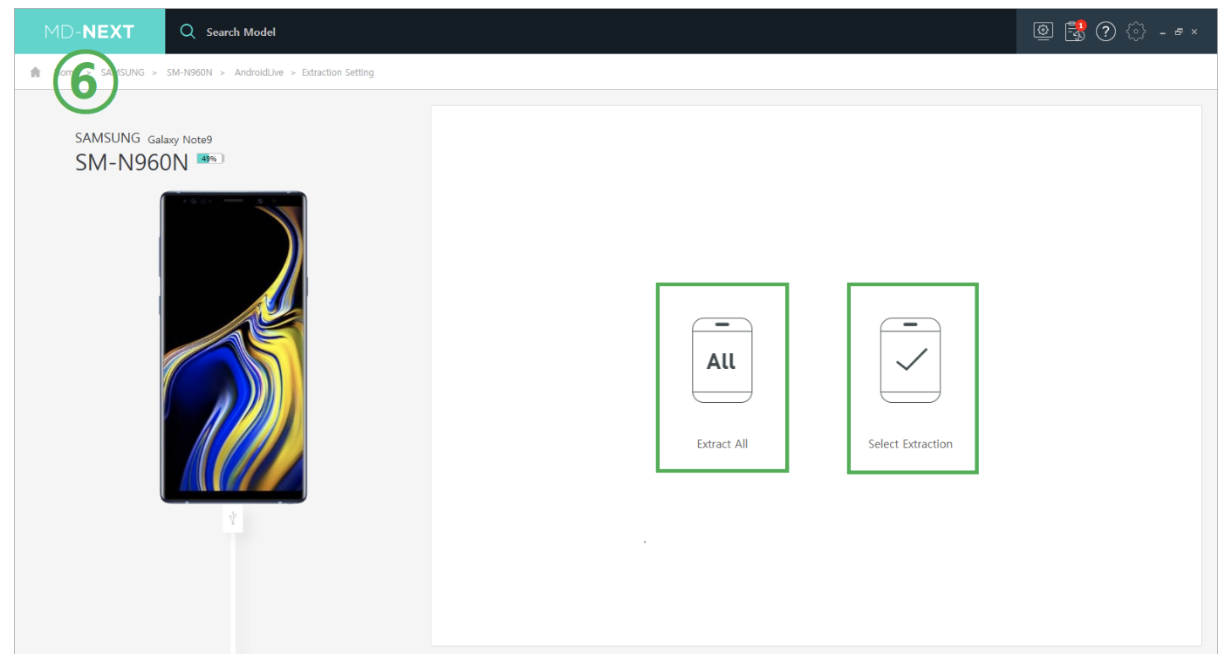
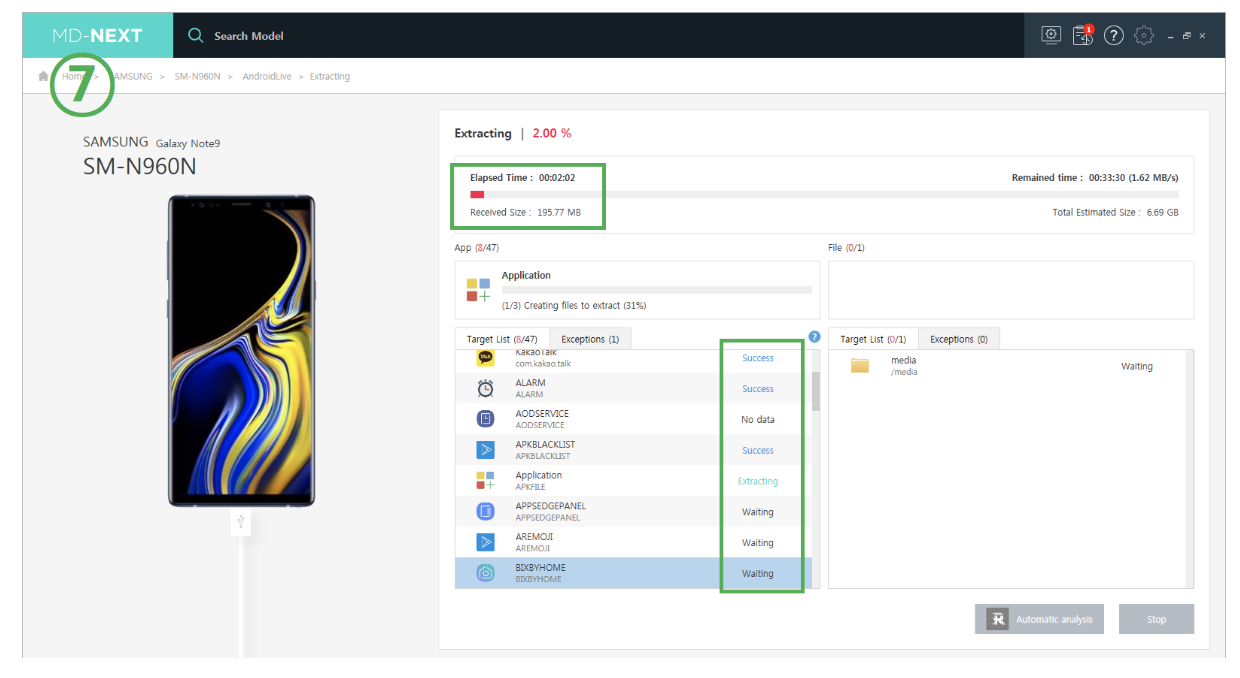
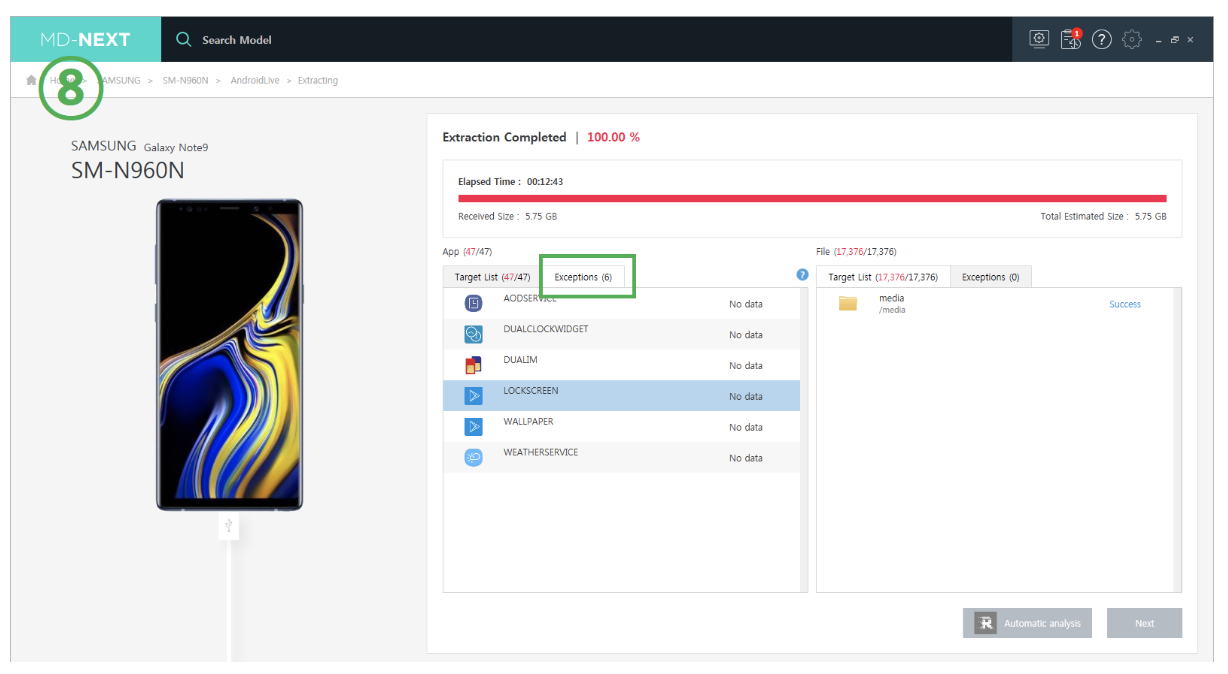
Step 2: Data Extraction
You can then select the range of data for extraction. MD-NEXT will then start to acquire data from the device. You can check the extraction time and the status for each app on the ‘Extracting’ screen.
Selective extraction for privacy protection:
- Supports selection of partition, file, category and app
- Supports selection of file system physical extraction
- Supports selection of all logical extraction methods
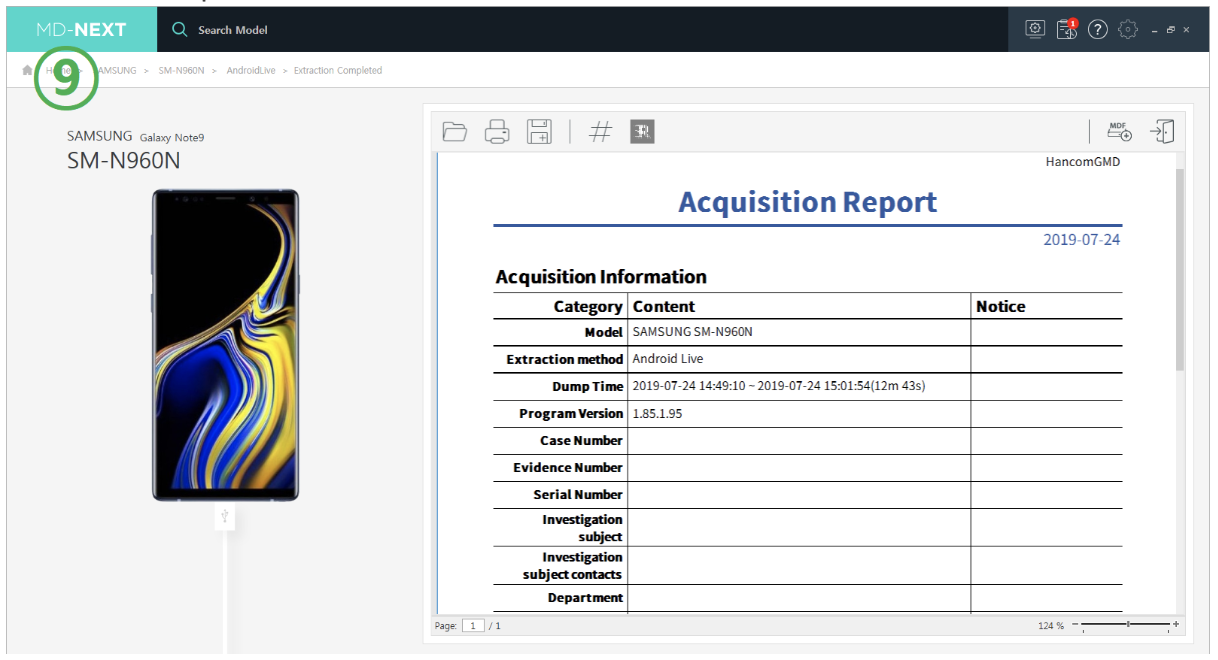
Step 3: Exporting the Acquisition Report
The acquisition report contains useful information such as hash value, time, extraction method, and file name. The report can be formatted as PDF, Excel, or HTML.
If you want to learn more about MD-NEXT, please visit our website or send an email to sales@hancomgmd.com